Background
On March 17, 2023, Paraspace (now Parallel Finance), an NFT lending platform, suffered a critical attack due to a vulnerability in its price oracle. Paraspace allows users to deposit NFTs and ERC-20 tokens as collateral to borrow ERC-20 tokens, enabling returns on NFTs without selling them.
A key feature of ParaSpace is ApeStaking, which auto-compounds APE rewards. Users staking APE receive cAPE tokens, a cToken representation of APE, which can be used as collateral to borrow assets like USDC and WETH. Depositing cAPE tokens grants pcAPE shares, whose collateral value is calculated by multiplying the pcAPE amount by its rebasingIndex.
The rebasingIndex is derived from the total pooled APE balance and total shares, as shown in the following code snippets:
function _scaledBalanceOf(address user, uint256 rebasingIndex)
internal
view
returns (uint256)
{
return super.scaledBalanceOf(user).rayMul(rebasingIndex);
}
function lastRebasingIndex() internal view override returns (uint256) {
return ICApe(_underlyingAsset).getPooledApeByShares(WadRayMath.RAY);
}
function getPooledApeByShares(uint256 sharesAmount)
public
view
returns (uint256)
{
uint256 totalShares = _getTotalShares();
if (totalShares == 0) {
return 0;
} else {
return
sharesAmount.mul(_getTotalPooledApeBalance()).div(totalShares);
}
}
function _getTotalPooledApeBalance()
internal
view
override
returns (uint256)
{
(uint256 stakedAmount, ) = apeStaking.addressPosition(address(this));
uint256 rewardAmount = apeStaking.pendingRewards(
APE_COIN_POOL_ID,
address(this),
0
);
return stakedAmount + rewardAmount + bufferBalance;
}The _getTotalPooledApeBalance() function sums the staked APE tokens, pending rewards, and a buffer balance from the ApeCoinStaking contract.
Vulnerability Analysis
The vulnerability lies in the manipulation of the rebasingIndex, which artificially inflates the collateral value of cAPE tokens. Specifically, the depositApeCoin() function in the ApeCoinStaking contract increases the stakedAmount for a position. An attacker can exploit this by depositing APE tokens into the cAPE position, inflating the output of _getTotalPooledApeBalance() and thus the rebasingIndex.
function depositApeCoin(uint256 _amount, address _recipient) public {
if (_amount < MIN_DEPOSIT) revert DepositMoreThanOneAPE();
updatePool(APECOIN_POOL_ID);
Position storage position = addressPosition[_recipient];
_deposit(APECOIN_POOL_ID, position, _amount);
apeCoin.transferFrom(msg.sender, address(this), _amount);
emit Deposit(msg.sender, _amount, _recipient);
}
function _deposit(uint256 _poolId, Position storage _position, uint256 _amount) private {
Pool storage pool = pools[_poolId];
_position.stakedAmount += _amount;
pool.stakedAmount += _amount.toUint96();
_position.rewardsDebt += (_amount * pool.accumulatedRewardsPerShare).toInt256();
}This design flaw allows the attacker to inflate the collateral value by depositing APE tokens through depositApeCoin() with cAPE as the recipient.
Attack Analysis
The attacker exploited this vulnerability using a flash loan attack in five key steps:
- Obtained a flash loan of approximately 47,352 wstETH and supplied about 46,018 wstETH to borrow cAPE via multiple contracts.
- Deposited roughly 12,880,000 cAPE tokens as collateral.
- Traded approximately 1,205 wstETH for about 492,124 APE tokens and withdrew 1,839,999 cAPE to APE tokens.
- Deposited 2,332,214 APE tokens into the cAPE position by calling
ApeCoinStaking.depositApeCoin(), increasing the protocol’s stakedAmount from 851,662 to 3,183,876 (a 373% increase). - Leveraged the inflated collateral to borrow large amounts of assets such as USDC and WETH for profit.
This manipulation of the pcAPE price via flash loans exploited the use of spot prices in the oracle calculation.
Summary
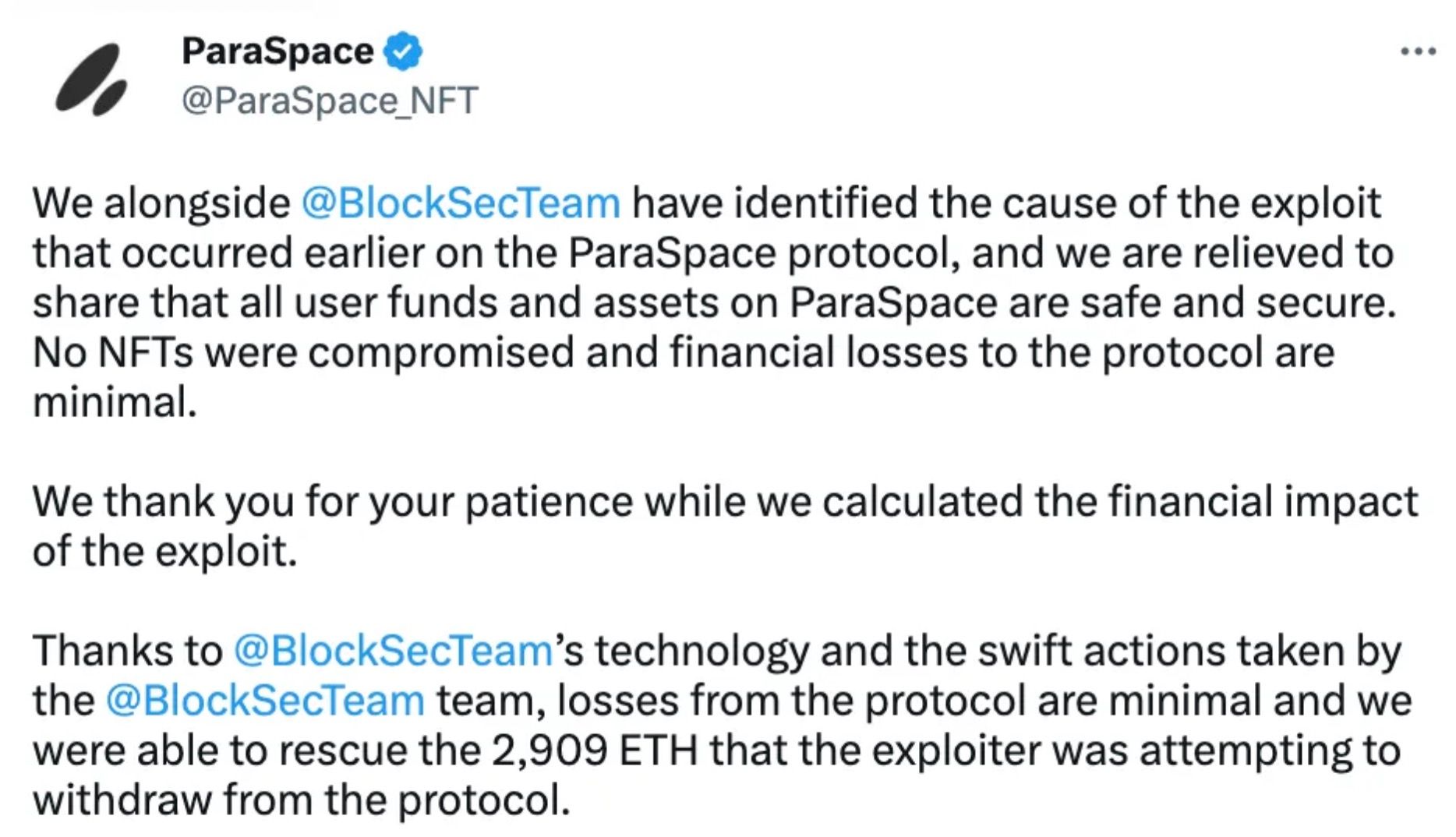
The ParaSpace incident underscores the risks of oracle manipulation and flash loan attacks in DeFi protocols. It highlights the critical need for robust, manipulation-resistant price oracles and continuous security monitoring beyond pre-launch audits.
BlockSec’s Phalcon Security system demonstrated the value of active threat detection and prevention by automatically blocking the attack and protecting user assets. This incident serves as a reminder for DeFi protocols to implement comprehensive security measures, including smart contract audits, infrastructure audits, and real-time monitoring.
For more insights on DeFi security incidents and best practices, explore our Security Incident Library and consider our Smart Contract Audit and Infrastructure Audit services.
Read other articles in this series:
- Lead-In: Top Ten "Awesome" Security Incidents in 2023
- #1: Harvesting MEV Bots by Exploiting Vulnerabilities in Flashbots Relay
- #2: Euler Finance Incident: The Largest Hack of 2023
- #3: KyberSwap Incident: Masterful Exploitation of Rounding Errors
- #4: Curve Incident: Compiler Error Produces Faulty Bytecode
- #5: Platypus Finance: Surviving Three Attacks
- #6: Hundred Finance Incident: Precision-Related Exploits
- #8: SushiSwap Incident: A Clumsy Rescue Attempt
- #9: MEV Bot 0xd61492: From Predator to Prey
- #10: ThirdWeb Incident: Incompatibility Between Trusted Modules
Best Security Auditor for Web3
Validate design, code, and business logic before launch




