自 BlockSec 于 2021 年首次亮相以来,我们一直认为代码审计本身无法解决 Web3 安全问题。因此,我们一直在投入探索 Web3 安全的新范式。因此,我们创建了**Phalcon**,这是世界上第一个加密货币黑客拦截系统。
在 Phalcon 推出之前,该系统已在内部运行了 2 年,成功阻止了 20 多次黑客攻击,并挽救了价值超过 2000 万美元的资产,其中包括为 Saddle Finance 挽回的 380 万美元,为 Platypus 挽回的 240 万美元,为 ParaSpace 挽回的 500 万美元,以及更多。
在本系列文章中,我们将展示我们系统 Phalcon 的代表性成功案例。今天,让我们来看看行业首个挽回 380 万美元的重要拦截案例。
我们是如何阻止针对 Saddle Finance 的攻击的
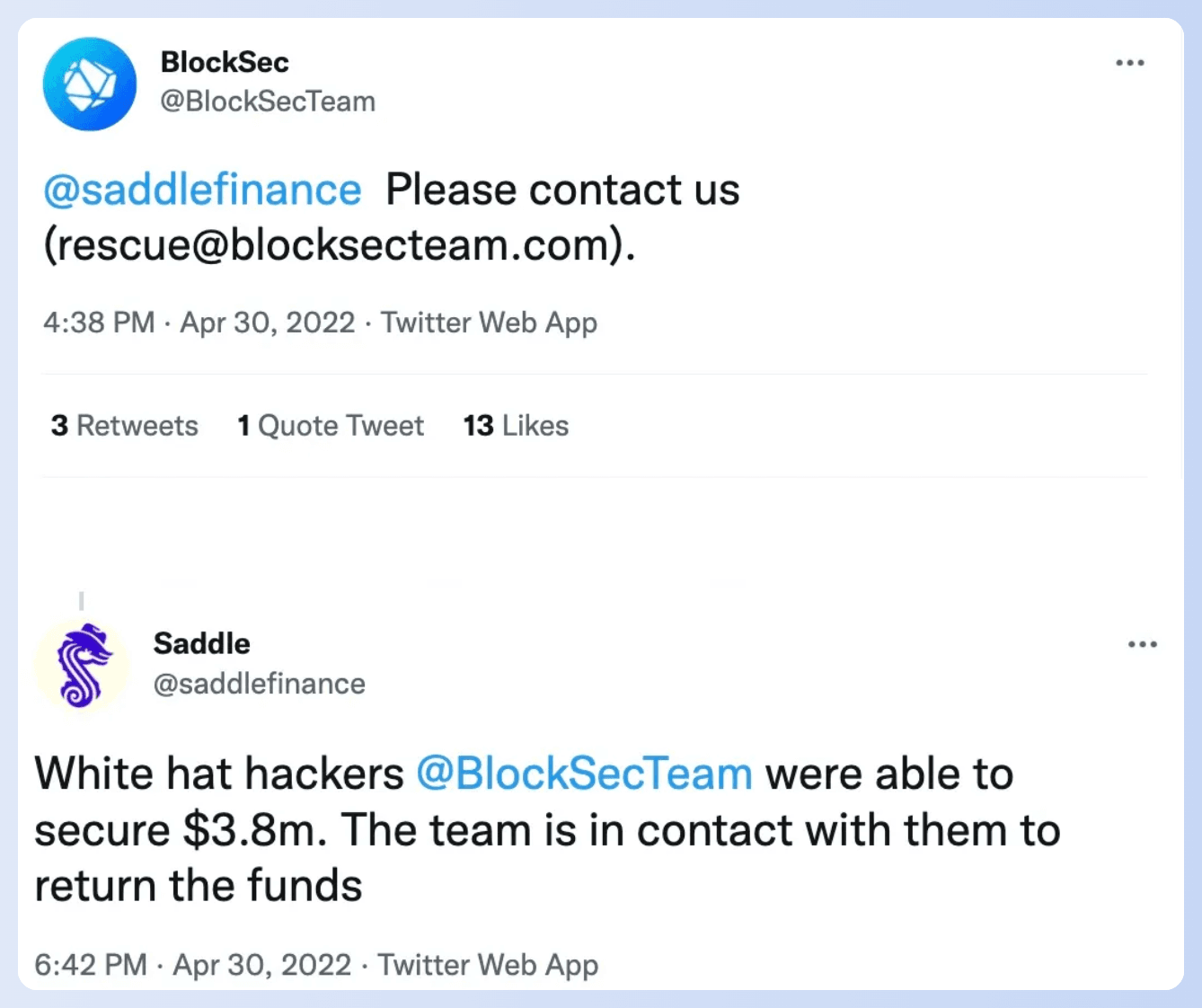
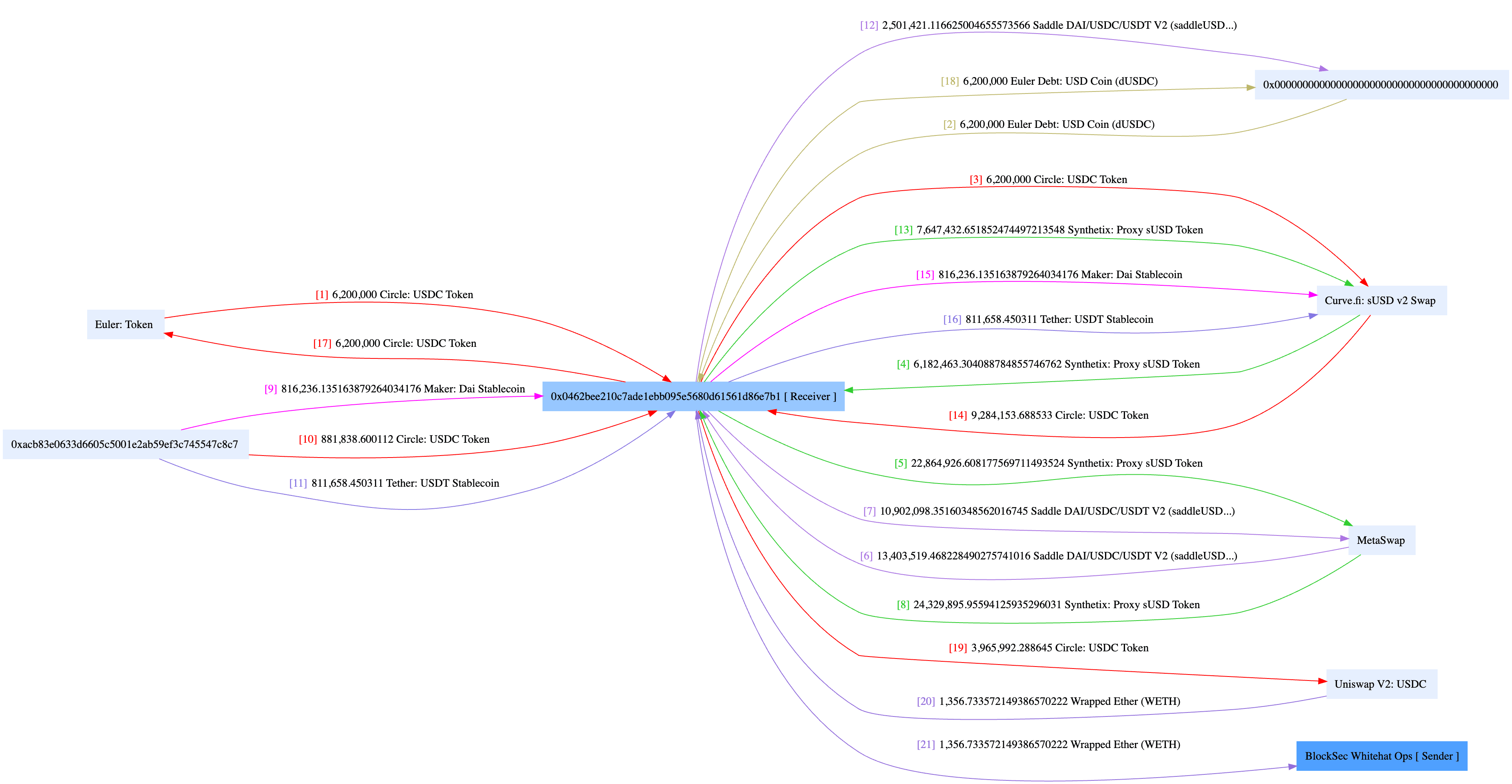
2022 年 4 月 30 日,Saddle Finance 遭到攻击者攻击。总共有 4900 个以太坊面临风险。幸运的是,我们成功地保住了 1360 个以太坊,当时价值 380 万美元。
有关漏洞的根本原因分析以及发起攻击的方式可以在我们之前的报告中找到。
攻击者在每次尝试中都遵循了相同的模式。首先,他们创建了一个攻击合约,然后调用已部署合约的函数 0xaf8271f7 来发起攻击。总共有三次攻击尝试;第一次成功了,而第二次由于 gas 不足在区块 14684432 失败。因此,攻击者发起了第三次尝试。
当时,当第一次尝试溜走时,我们的系统还很稚嫩,但它已经准备就绪,正在等待第二次尝试。就在关键时刻,它发现了失败的交易,披上了超级英雄披风,并在区块 14684434 发送了一笔救援交易来阻止后续的尝试。就这样,攻击者的第三次尝试被挫败了,他们获得的赃物远远少于预期的。
虽然并不完美,但它无疑标志着一个里程碑,是行业首个主动抵御持续威胁的重要拦截行动。这一胜利增强了我们的信心,并激励我们追求更大的进步。这次经历,特别是其中的挫折,揭示了需要改进的领域,并指导我们完善我们的系统。别担心,一个更复杂、更强大的系统即将到来!
如何访问服务
查看更多 Phalcon 的成功案例
- 阻止 HomeCoin 攻击:行业首个成功拦截案例
- 阻止 Saddle Finance 攻击:行业首个挽回 380 万美元的重要拦截案例
- 阻止 TransitSwap 攻击:行业首个“黑客反击”挽回 30 万美元案例
- 阻止 Platypus 攻击:行业首个针对黑客合约的反利用案例
- 阻止 Loot 攻击:Phalcon 如何从恶意提案中挽救 120 万美元
关于 Phalcon
Phalcon 是 BlockSec 推出的攻击监控和自动化拦截平台。该平台能够准确识别攻击并自动进行拦截。Phalcon 旨在为 Web3 项目提供全面的上线后安全保护,包括持续监控、攻击拦截和应急响应,从而保护协议提供商、LP 和 DAO 组织参与者的链上资产。
迄今为止,Phalcon 已成功拦截了 20 多次黑客攻击,挽回了超过 2000 万美元的资产。即使在早期客户阶段,Phalcon 也获得了顶级 DeFi 协议 Compound 的认可和资助,并为其建立了一个攻击拦截平台。
网站:https://blocksec.com/phalcon
Twitter:@Phalcon_xyz
Telegram:https://t.me/BlockSecTeam



