On January 5, an attacker made a malicious proposal to LootDAO to drain 477 Ether (worth 1.2 million USD) from the project if the proposal could be passed. Phalcon detected the proposal and then immediately notified the Loot community. The community took action to vote against the proposal and then made a new one to move the funds to a secure wallet to prevent further loss. With the help of Phalcon’s precise attack detection capabilities, 1.2 million USD was saved.
Main Timeline
-
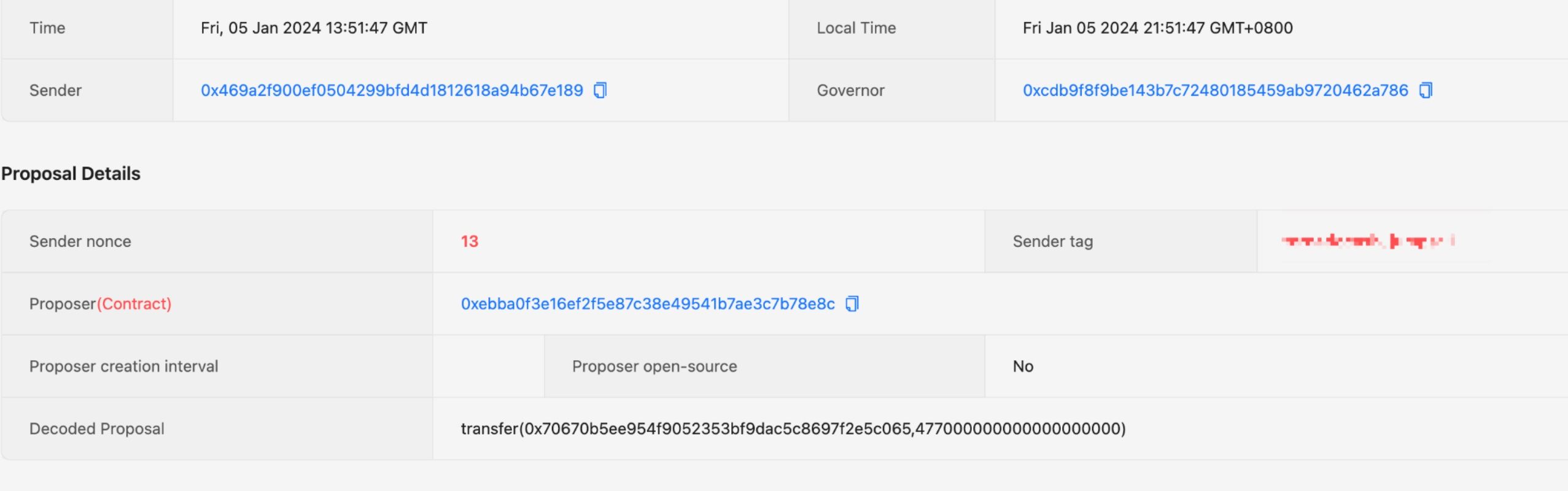
2024-01-05 13:51:47 (UTC) Phalcon detected that an attacker with the address 0x469a2f900ef0504299bfd4d1812618a94b67e189 made a proposal to drain the 477 Ether in LootDAO. We attempted to contact the project through various channels.
-
2024-01-05 14:48:00 (UTC) We decided to post an alert on Twitter since the alert could make the Loot community aware of this threat and to vote against the malicious proposal.
-
2024-01-05 15:42:00 (UTC) A war room was created with BlockSec and core contributors of the Loot project. Measures were devised to mitigate the current and further threats.
-
2024-01-10 05:02:35 (UTC) The malicious proposal did not pass, and the hack was blocked.
Details
Our Phalcon system actively monitors transactions and reports malicious ones. Customers of Phalcon can also configure automatic actions to respond to malicious transactions. Please take a look at our articles (Link1 | Link2 | Link3) on how our system can save millions in user assets.
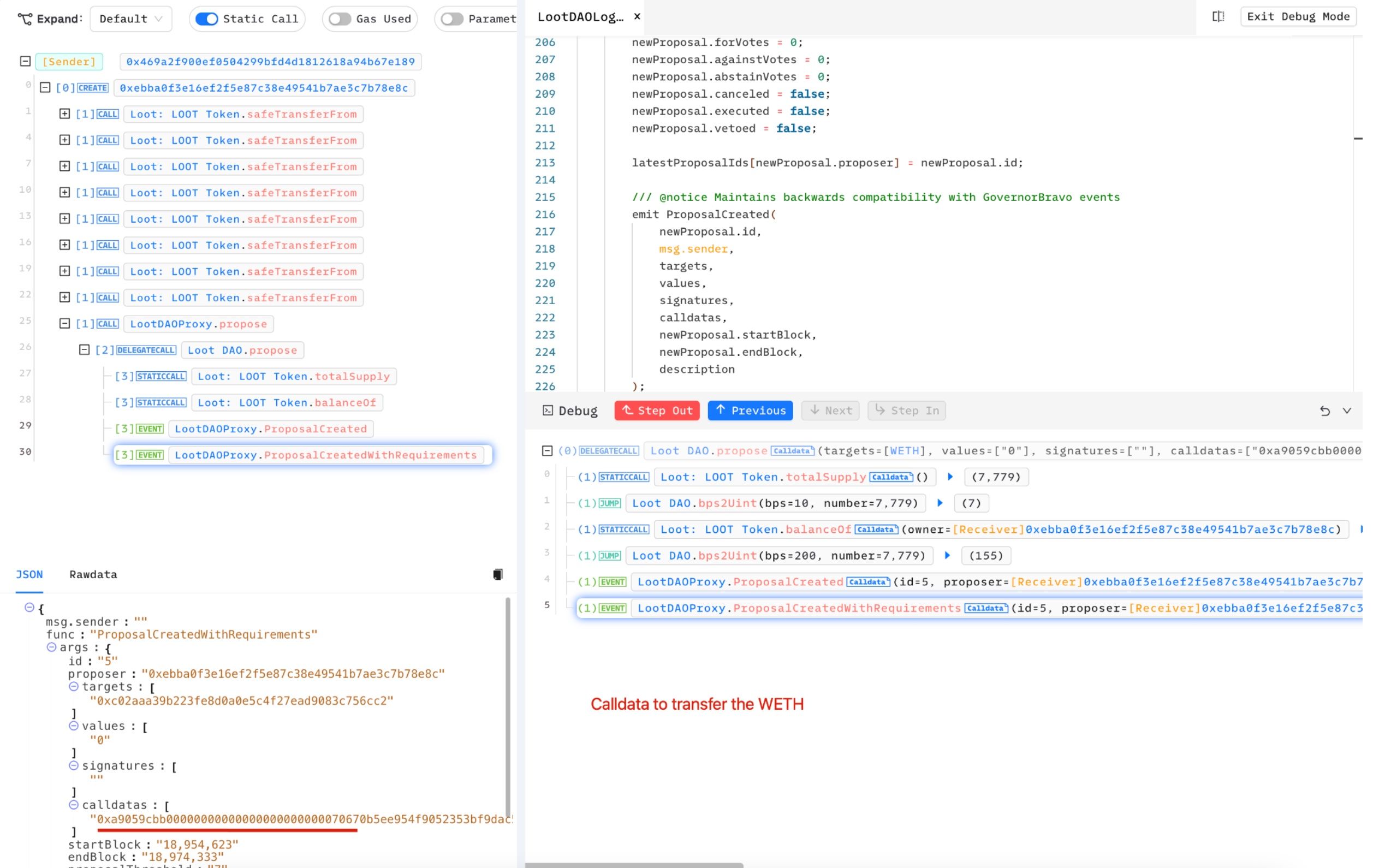
The Attack Transaction
On January 5, our system reported an attack transaction, which was a proposal submitted to the Loot project. If the proposal passed, it would have directly transferred the 477 Ether from the LootDAOExecutor contract (0x8cFDF9E9f7EA8c0871025318407A6f1Fbc5d5a18) to the address 0x70670b5ee954f9052353bf9dac5c8697f2e5c065. To make this proposal pass, there had to be at least 155 votes for it, and the number of votes for had to be larger than the number of votes against.
The Vulnerability in the Contract
We further found that there were issues in the LootDAO smart contract. Specifically, the count of the vote is based on the number of tokens held by the user, and there is no lock on the tokens that have been voted.
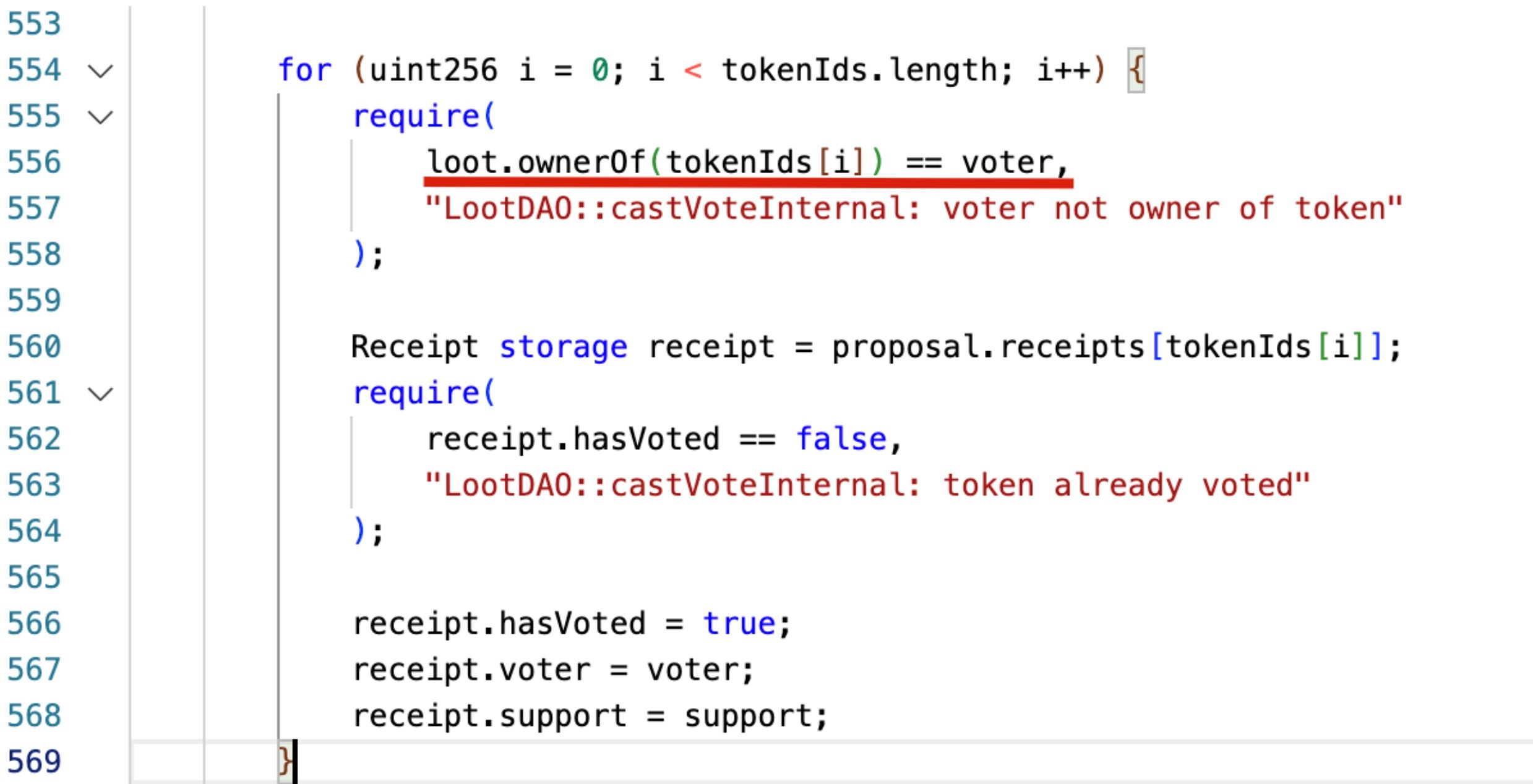
In this case, the attacker could borrow Loot from NFTX, perform the vote, return it to NFTX, and then borrow other Loot again. Since there is no lock on the Loot that has been used to vote, the attacker could do this in one transaction (in the last minute before the end of the voting period).
How to Mitigate
To mitigate the issue, the direct way was to make the proposal fail. Due to the issue in the contract, the community needed to ensure that there was no liquidity in NFTX so that the attacker could not borrow a large number of Loot to vote. However, the attacker could collude with other holders to make the proposal pass. Thus, the best strategy was to ask Loot holders to vote as soon as possible.
However, the attacker could create new malicious proposals again. To defend against this, the community decided to make a new proposal to move the funds in LootDAOExecutor to a secure wallet.
Thanks to the community's efforts, the attacker did not get enough votes to make the proposal pass, and the 477 Ether in the contract was saved. Also, the proposal to move the funds to a secure wallet is ongoing.
Summary
We are glad that our Phalcon product saved assets for the community again, following the success stories of multiple projects.
However, if protocols could adopt the Phalcon system in the first place, they would receive real-time alerts and, more importantly, take automatic actions to protect the protocols, as we have discussed in the Radiant, Gamma, and Telecoin cases.
Partner with BlockSec for Full-Stack Security
In the realm of DeFi, security is multi-faceted and ever-evolving. By collaborating with BlockSec and incorporating Phalcon into your protocol, you unlock a suite of full-stack security services that cater to all your security needs.
Here's how you benefit.
-
Expert Code Audits: BlockSec's top-tier code auditing services provide ongoing review as your protocol evolves, ensuring security keeps pace with development.
-
Tailored Security Rules: Using what we learn from our detailed audits, we set up Phalcon with security rules made just for your protocol. This means better protection without the need to deal with different companies for different services, saving you both time and money.
-
Swift Vulnerability Response: With BlockSec's expertise in identifying root causes, we can rapidly pinpoint vulnerabilities and establish a dedicated war room for immediate and effective mitigation.
Choosing BlockSec means opting for a robust, integrated security solution. You're not just getting a tool; you're gaining a partner dedicated to safeguarding your protocol's integrity and your users' assets every step of the way.
Contact us: [email protected] for more information.
See More Success Stories of Phalcon
- Blocked Paraspace Attack: Industry's Most Important Block that Rescued $5,000,000
- Blocked HomeCoin Attack: Industry's First Successful Blocking Story
- Blocked Saddle Finance Attack: Industry's First Influential Blocking to Rescue $3,800,000
- Blocked TransitSwap Attack: Industry's First "Hacking Back" to Rescue $300,000
- Blocked Platypus Attack: Industry's First Counter-Exploitation of a Hacker's Contract



