Since BlockSec’s debut in 2021, we have long maintained that code auditing alone cannot solve Web3 security issues. Therefore, we have been investing in exploring new paradigms for Web3 security. Thus we created Phalcon, the world's first crypto hack-blocking system.
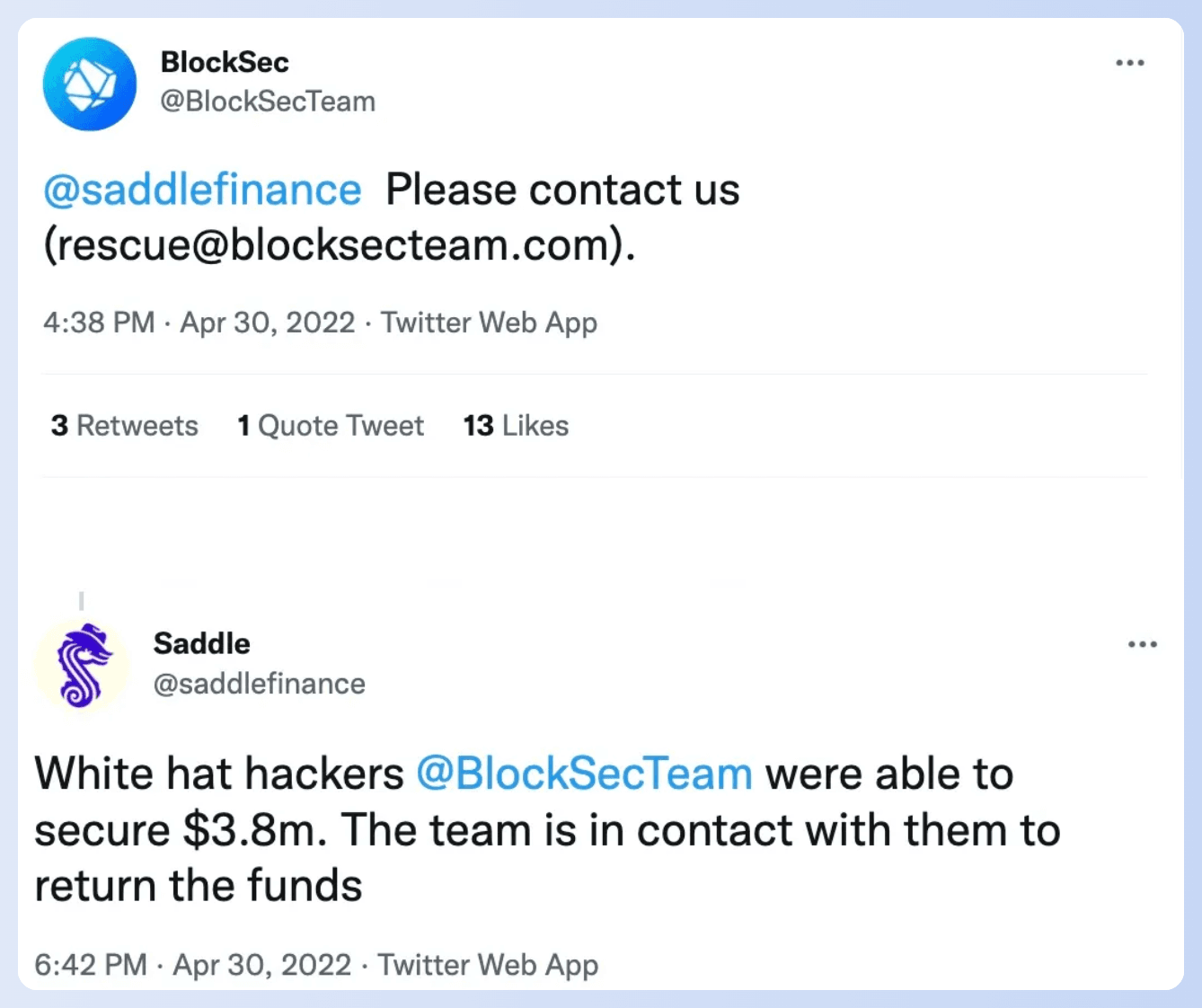
Before the launch of Phalcon, the system had been running internally for 2 years, successfully blocking over 20 hacks, and rescuing more than 20 million USD worth of assets, including $3.8 million for Saddle Finance, $2.4 million for Platypus, $5 million for ParaSpace, and more.
In this series of articles, we will present representative successful stories of our system Phalcon. Today let's take a look at the industry's first influential blocking that rescued $3,800,000.
How We Blocked the Attack Against Saddle Finance
On April 30th, 2022, Saddle Finance was targeted by an attacker. In total, 4,900 Ether were at risk during the attack. Fortunately, we were able to successfully secure 1,360 Ether, which was worth $3.8 million at that time.
The root cause analysis of the vulnerability and the way to launch the attack can be found in our previous report.
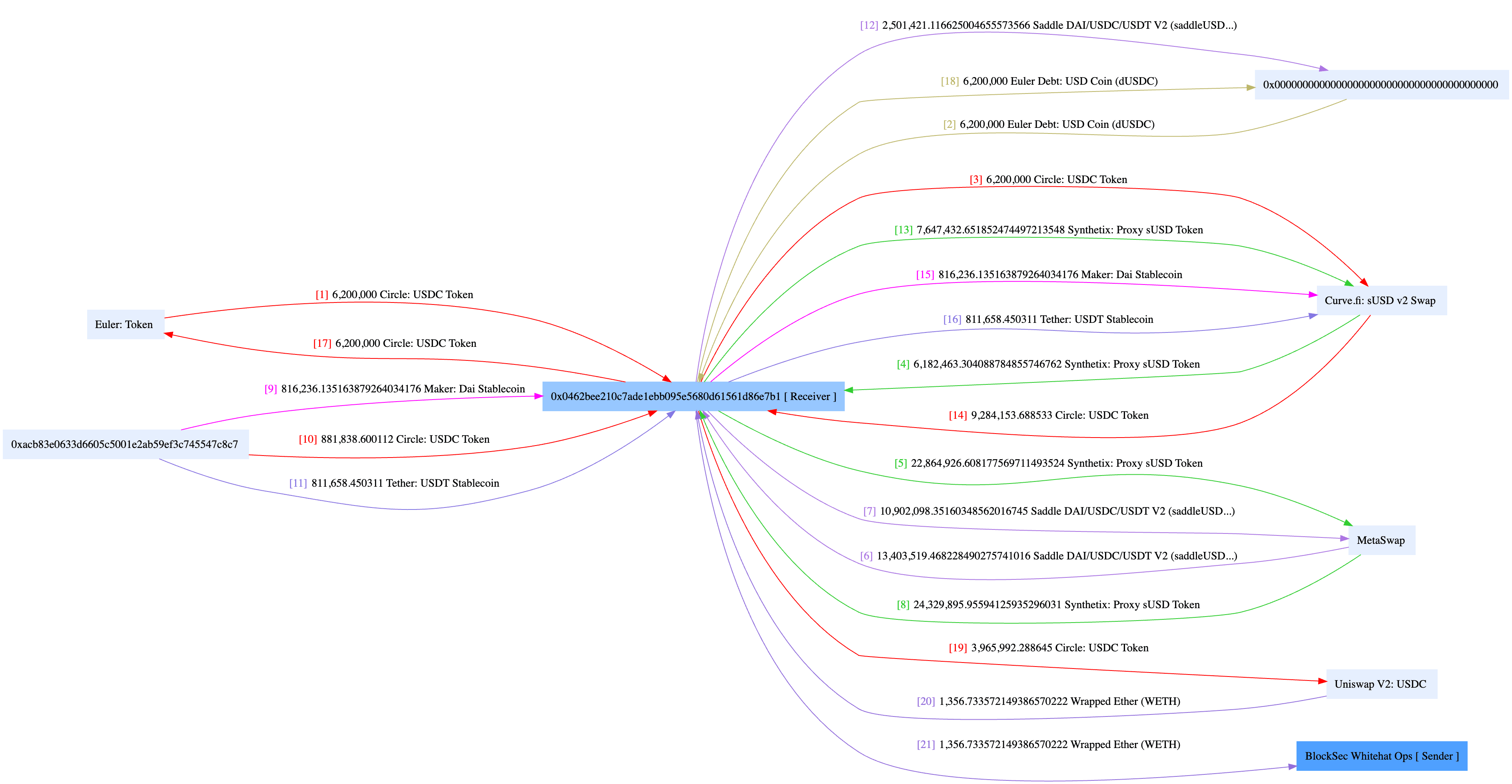
The attacker followed the same pattern for each attempt. First, they created an attack contract and then invoked the function 0xaf8271f7 of the deployed contract to launch the attack. In total, the attacker made three attempts; the first one was successful, while the second one failed at block 14684432 due to an out-of-gas issue. Consequently, the attacker launched a third attempt.
At that time, our system was still a bit green when the first attempt slipped through, but it was ready and waiting for the second one. Just in the nick of time, it spotted the failed transaction, put on its superhero cape, and successfully sent a rescue transaction at block 14684434 to stymie the subsequent attempt. And just like that, the attacker's third attempt was thwarted, leaving them with far less loot than they'd hoped for.
Not perfect, but it certainly marked a milestone as the industry's first influential blocking action to proactively fend off ongoing threats. This triumph reinforced our confidence and motivated us to pursue even greater progress. The experience, particularly the setbacks, shed light on areas for improvement and guided us in refining our system. Fear not, for a more sophisticated and powerful system is just around the corner!
How to Access the Service
- Phalcon is a SaaS platform. You can log in to our website to explore features, view pricing, and subscribe directly.
- You can also book a demo to learn more about Phalcon and receive expert security advice.
See More Success Stories of Phalcon
- Blocked HomeCoin Attack: Industry's First Successful Blocking Story
- Blocked Saddle Finance Attack: Industry's First Influential Blocking to Rescue $3,800,000
- Blocked TransitSwap Attack: Industry's First "Hacking Back" to Rescue $300,000
- Blocked Platypus Attack: Industry's First Counter-Exploitation of a Hacker's Contract
- Blocked Loot Attack: How Phalcon Saved $1.2M from Malicious Proposal
About Phalcon
Phalcon is an attack monitoring and automated blocking platform launched by BlockSec. The platform is capable of accurately identifying attacks and automatically blocking them. Phalcon aims to provide comprehensive post-launch security protection for Web3 projects, including continuous monitoring, attack blocking, and emergency response, safeguarding on-chain assets for protocol providers, LPs, and DAO organization participants.
To date, Phalcon has successfully blocked over 20 hacker attacks, rescuing more than $20 million in assets. Even in the early customer stage, Phalcon gained recognition and a grant from the top DeFi protocol Compound and established an attack-blocking platform for it.
Website: https://blocksec.com/phalcon
Twitter: @Phalcon_xyz
Telegram: https://t.me/BlockSecTeam