As a kind of self-protection, protocol providers will always pause the protocol and freeze assets in the event of an emergency. However, it exposes the funds of liquidity providers (LPs) to significant uncertainty and risk.
For example, the Euler Finance flash loan attack in March of this year led several protocols to freeze their liquidity pools, including Balancer, Angle Protocol, and Yield Protocol. The assets affected were worth approximately ten billion dollars. In the case of the recent Aave V2 incident, the directly affected asset value amounted to 2.5 billion dollars.
However, facing the uncertain handling methods following protocol pauses and pool freezes, liquidity providers have another option: using BlockSec Phalcon to withdraw funds before the protocol initiates a pause transaction!
BlockSec's attack monitoring and automated blocking system BlockSec Phalcon, along with Cobo's on-chain digital asset management solution Cobo Argus, fulfills this demand by providing LPs with a comprehensive "auto-withdrawal strategy". It can identify potential liquidity pool freezes and promptly trigger a bot to withdraw funds even before the DeFi protocol's pause transaction is executed.
Aave Protocol Pause Recap
On November 5th, the leading DeFi protocol Aave received a serious vulnerability report from white-hat hackers. The protocol was paused as an emergency measure, and user assets were frozen. According to data from DefiLlama, Aave has a total value locked (TVL) exceeding $5 billion. Specifically, the affected Aave V2 accounts for nearly half of this amount, standing at $2.5 billion. The protocol pause means that digital assets worth $2.5 billion were frozen.
According to media reports, the undisclosed vulnerabilities in Aave V2 could reappear in over 30 forked projects!
Here's the official statement from Aave:
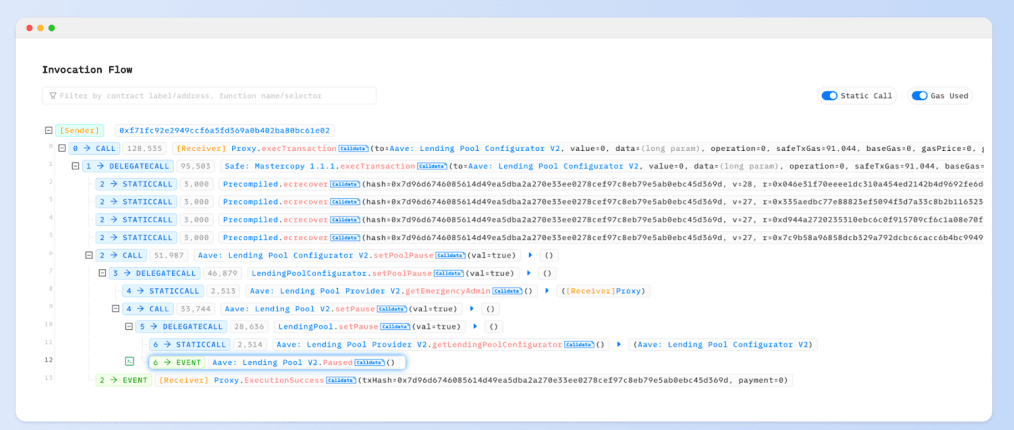
Use Phalcon Explorer to dive into the transaction:
For leading DeFi protocols like Aave, we believe that after the vulnerabilities are patched, user funds will remain safe and the protocol will continue to operate.
However, in the Web3 world, there are always unforeseen circumstances. In the past two years, there have been extreme cases where users were unable to withdraw their funds for months after the protocols froze their liquidity pools, as seen with PolyNetwork and CoinWind. Such protocol pauses not only greatly affect the efficient utilization of LPs' funds but also pose significant risks to the security of their funds.
Regardless of the varying credit ratings of protocols, the various reasons for protocol pause, and different handling methods after protocol pause, having timely access to information and the choice to withdraw funds should be the right of every liquidity provider!
How can LPs Respond?
The attack monitoring and blocking platform BlockSec Phalcon launched by BlockSec, together with Cobo Argus launched by Cobo, will tackle this issue effectively for liquidity providers.

The following is the operation path:
👉 Step 1: Monitor
Liquidity providers register as users on the BlockSec Phalcon platform, choose protocols on which they have deposited assets (such as Aave) to enable monitoring, and set up alerts and trigger conditions (BlockSec Phalcon offers one-click default configurations).
BlockSec Phalcon offers multiple monitoring templates for key variables, sensitive events, token amounts, token prices, and more. Taking the Aave incident as an example, the project team can set the "key variable" of the protocol to Pause, which then outputs a "sensitive event" labeled as Paused.
With prior setup on BlockSec Phalcon, the intelligence can be captured as early as the transactions are still in the mempool stage and immediately trigger pre-set response mechanisms to withdraw funds promptly.
👉 Step 2: Trigger
Create a "Withdrawal Bot" on the Cobo Argus platform and set the trigger condition to BlockSec Phalcon's designated webhook. This enables the "Withdraw Bot" to be activated based on intelligence instructions from BlockSec Phalcon.
👉 Step 3: Withdraw
Deploy targeted "withdrawal contracts" based on LPs' specific needs, which include single withdrawals, batch withdrawals, and executing withdrawal operations based on pre-set trading strategies, to name a few (BlockSec Phalcon can provide technical services).
In short, when BlockSec Phalcon detects a transaction (behavior) of the "Pause" category, it immediately triggers an alert and sends it to the Cobo Argus system. Based on the pre-set withdrawal logic, BlockSec Phalcon will automatically withdraw funds and deposit them into LPs' secure multi-sig wallets.
Maximize fund withdrawals for liquidity providers within a single block time!
Safeguarding Funds Throughout the Entire Process
It's important to emphasize that we always put user asset security as a top priority and adhere to decentralized governance principles, making sure we never cross the line. This philosophy is also thoroughly implemented in the design of BlockSec Phalcon.
We suggest liquidity providers utilize a multi-signature scheme to manage assets. Leveraging Cobo Argus' on-chain role-based access controls, BlockSec Phalcon helps liquidity providers withdraw funds promptly and securely while ensuring LPs retain complete control over the approval.
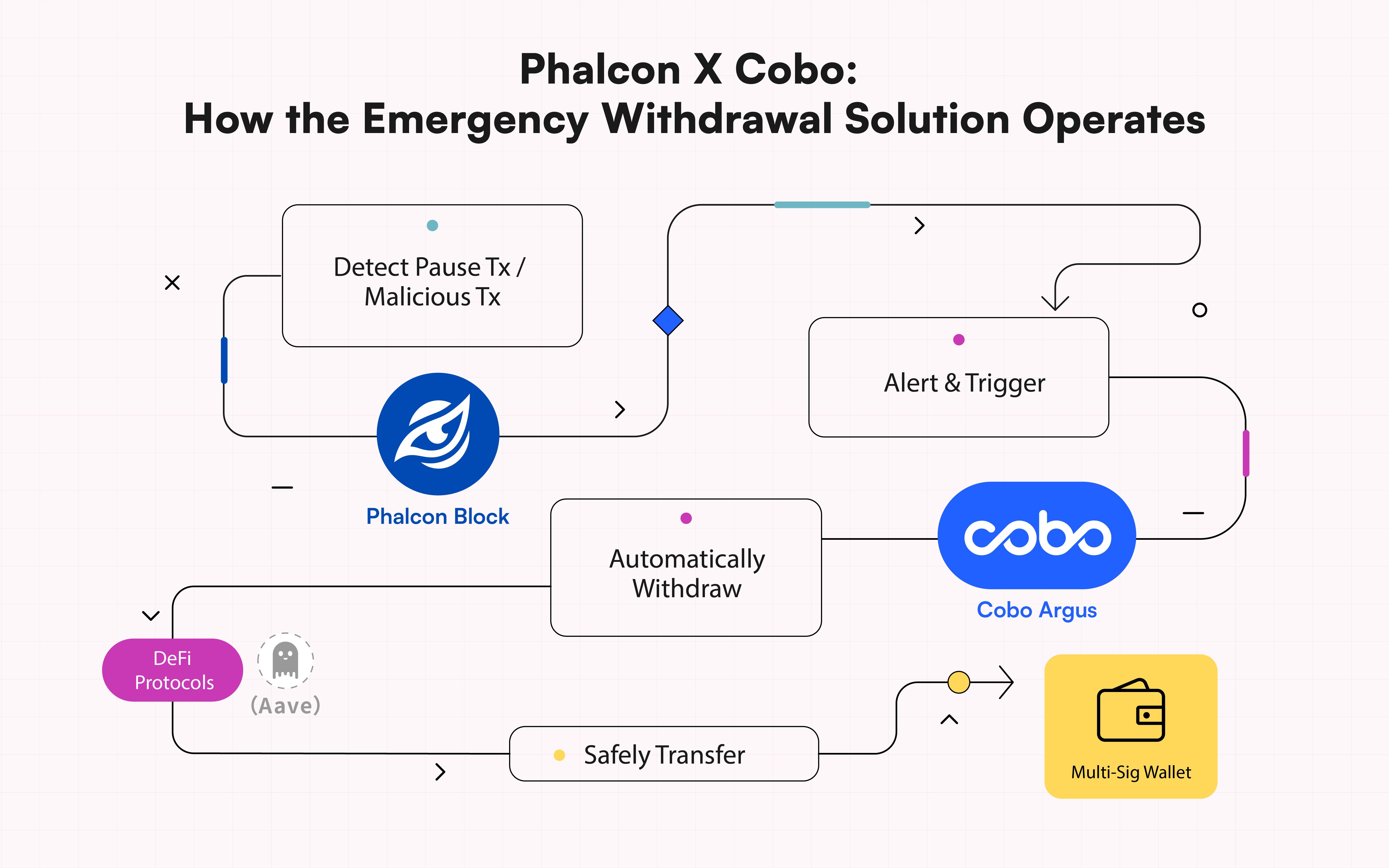
For example, in this case, once BlockSec Phalcon is granted the 'Withdraw' permission, it helps liquidity providers withdraw their funds at the earliest opportunity before protocol pauses. With Cobo Argus's on-chain role-based access controls, BlockSec Phalcon does not have any other operational authority, ensuring the withdrawn funds are safely held in LPs' original multisig wallets at the code level.
More than Safeguarding Funds
The joint solution supported by BlockSec Phalcon and Cobo Argus is not limited to emergency withdrawals during protocol pauses. It is designed to handle various risky scenarios. For instance, when a protocol is under hacker attack, it can help LPs promptly and securely transfer their assets.
We believe that by collaborating with outstanding partners to develop reliable security products, we can effectively protect investors' funds from threats and turn Web3 into an opportunity-rich, safe, and prosperous new world.
About BlockSec Phalcon
BlockSec Phalcon is an attack monitoring and automated blocking platform launched by BlockSec, a leading Web3 security company. The platform is capable of accurately identifying attacks and automatically blocking them. BlockSec Phalcon aims to provide comprehensive post-launch security protection for Web3 projects, including continuous monitoring, attack blocking, and emergency response, safeguarding on-chain assets for protocol providers, LPs, and DAO organization participants.
To date, BlockSec Phalcon has successfully blocked over 20 hacker attacks, rescuing more than $14 million in assets. Even in the early customer stage, BlockSec Phalcon gained recognition and a grant from the top DeFi protocol Compound and constructed an attack-blocking platform for it.
Website: https://blocksec.com/phalcon
Twitter: @Phalcon_xyz
About Cobo Argus
Cobo Argus is an institutional-grade on-chain digital asset management solution. Built on top of Safe{Wallet} (previously Gnosis Safe), Cobo Argus provides unparalleled security, workflow efficiency, and risk management for interacting with DeFi protocols. Cobo Argus offers a comprehensive suite of powerful features including multi-signature security, on-chain role-based access controls, granular permissions at function and parameter levels, advanced DeFi bots, single-signature authorizations, automated risk monitoring, and more. Cobo Argus supports all open-source DeFi protocols on compatible blockchains.
Website: https://www.cobo.com/
Twitter: @Cobo_Global



