Since BlockSec’s debut in 2021, we have long maintained that code auditing alone cannot solve Web3 security issues. Therefore, we have been investing in exploring new paradigms for Web3 security. Thus we created Phalcon, the world's first crypto hack-blocking system.
Before the launch of Phalcon, the system had been running internally for 2 years, successfully blocking over 20 hacks, and rescuing more than 20 million USD worth of assets, including $3.8 million for Saddle Finance, $2.4 million for Platypus, $5 million for ParaSpace, and more.
Over the past four days, we have proudly shared the extraordinary success stories of our system Phalcon. Today let's dive into the industry's most important block, the one that rescued a staggering $5,000,000.
How We Blocked the Attack Against Paraspace
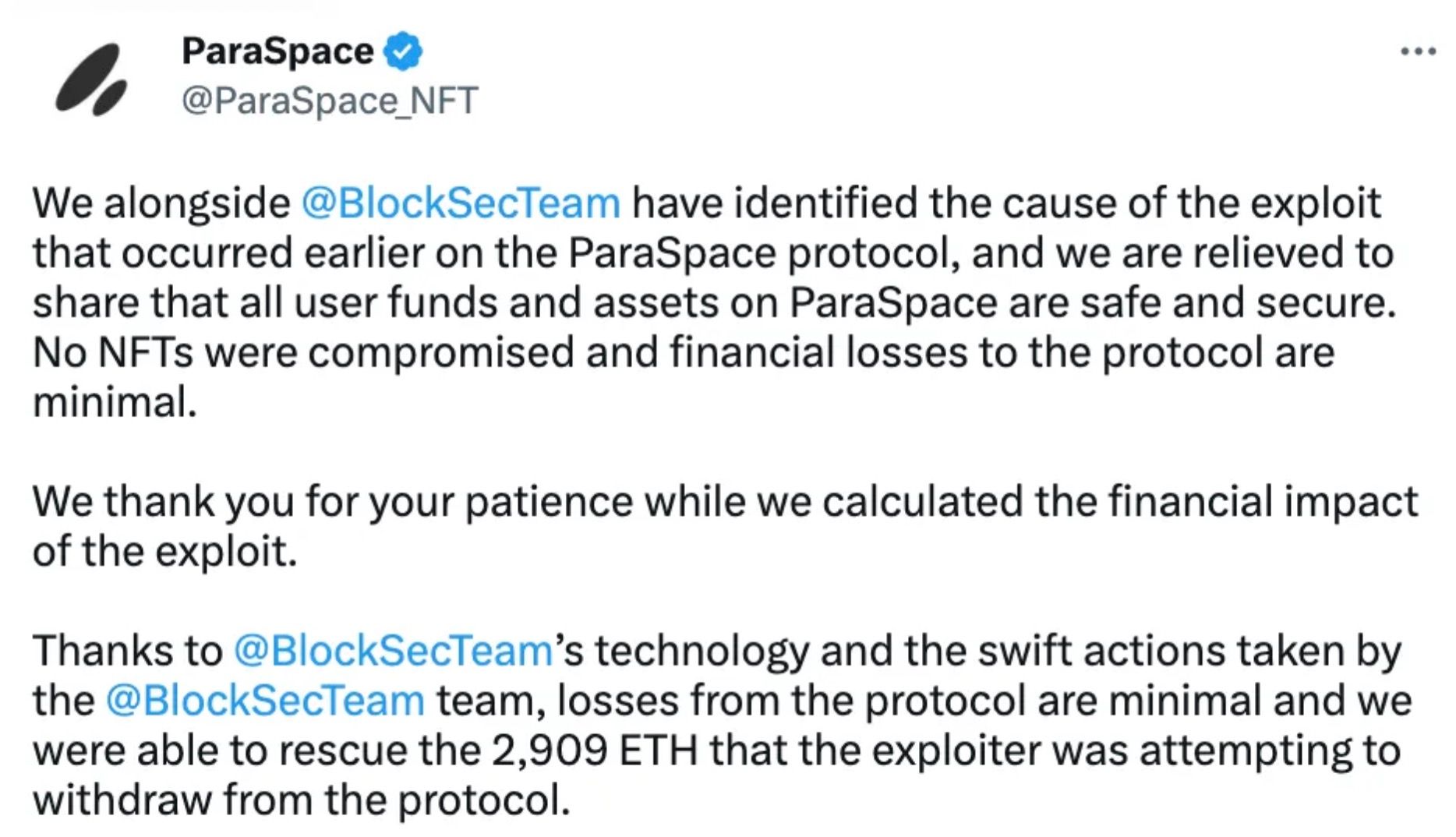
In March 2023, Paraspace was attacked. Luckily, we managed a rescue in the nick of time, recovering all losses: over 2900 Ether.
In this article, we will reveal an insider story of the rescue without giving you any complicated tech details.
Paraspace is a top NFT lending protocol on Ethereum. For any lending protocol, ensuring collateral value is higher than lent funds is key. Many attacks on lending protocol manipulate the collateral value, and this attack on Paraspace was no exception.
On March 17, 2023, the attacker deployed the attack contract and completed the setup. He made three unsuccessful attacks from 3:51:23 UTC to 4:36:23 UTC.
Post-analysis revealed the attacker's main failure was due to the 'Gas Limit' not being enough to execute this "complex" attack. During the three failed attacks, the attacker was gradually increasing the gas limit, and by the third attempt, they were very close to success. (Gas Limit: 6,721,975 -> 9,000,000 -> 13,000,000)
Luckily for us, the three failed transactions used up the funds he had prepared for the attack. Now he needed to find some more funds to continue the attack. That gave us some time.
We detected the attack when the attacker sent the first tx, even though the tx failed. At 5:47:11 UTC on March 17, 2023, our rescue contract was ready. We immediately sent the rescue transaction and successfully saved 2906 Ether.
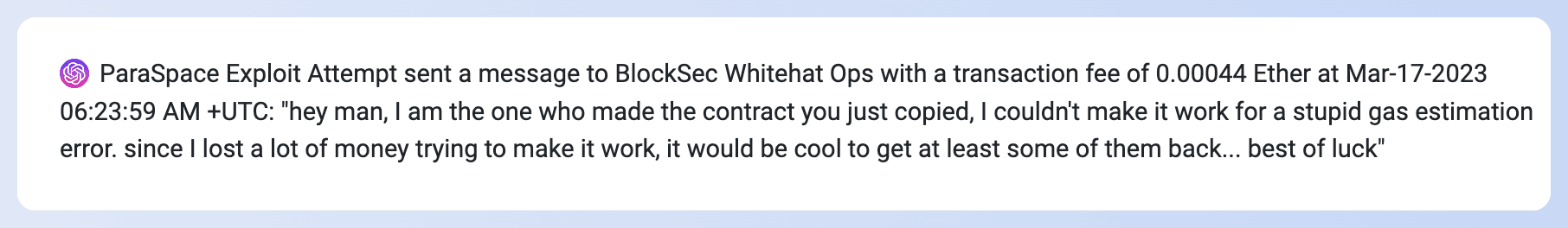
The following image shows after failing to steal the funds, the hacker left an on-chain message that asked our team to return some of the gas fees expended for the hack.
If the attacker had given one more try ahead of us, he would have stolen the money. It was Phalcon that played a pivotal role in securing our victory in the battle with the attacker. That was the victory of justice!
How to Access the Service
- Phalcon is a SaaS platform. You can log in to our website to explore features, view pricing, and subscribe directly.
- You can also book a demo to learn more about Phalcon and receive expert security advice.
Let Phalcon build a defense line for your protocol. It doesn't require much work on the protocol side and would never bring in additional risk. It's just like a shield providing an additional layer of safety. Book a demo now!
See More Success Stories of Phalcon
- Blocked HomeCoin Attack: Industry's First Successful Blocking Story
- Blocked Saddle Finance Attack: Industry's First Influential Blocking to Rescue $3,800,000
- Blocked TransitSwap Attack: Industry's First "Hacking Back" to Rescue $300,000
- Blocked Platypus Attack: Industry's First Counter-Exploitation of a Hacker's Contract
- Blocked Loot Attack: How Phalcon Saved $1.2M from Malicious Proposal
About Phalcon
Phalcon is an attack monitoring and automated blocking platform launched by BlockSec. The platform is capable of accurately identifying attacks and automatically blocking them. Phalcon aims to provide comprehensive post-launch security protection for Web3 projects, including continuous monitoring, attack blocking, and emergency response, safeguarding on-chain assets for protocol providers, LPs, and DAO organization participants.
To date, Phalcon has successfully blocked over 20 hacker attacks, rescuing more than $20 million in assets. Even in the early customer stage, Phalcon gained recognition and a grant from the top DeFi protocol Compound and established an attack-blocking platform for it.
Website: https://blocksec.com/phalcon
Twitter: @Phalcon_xyz
Telegram: https://t.me/BlockSecTeam



