Since BlockSec's debut in 2021, we have long maintained that code auditing alone cannot solve all Web3 security issues. Therefore, we have been investing in exploring new paradigms for Web3 security. Thus we created Phalcon, the world's first crypto hack-blocking system.
Before the launch of Phalcon, the system had been running internally for 2 years, successfully blocking over 20 hacks, and rescuing more than 20 million USD worth of assets, including $3.8M for Saddle Finance, $2.4M for Platypus, $5M for ParaSpace, and more.
In this series of articles, we will present representative stories of our system Phalcon. In sharing these cases, we aim to do more than validate the effectiveness of our system. We also want to demonstrate the transformative effect of proactive defense measures.
In the face of threats, we are not powerless. Together, we can usher in a new era of Web3 security.
Breaking Down: A Comprehensive Overview






About Phalcon
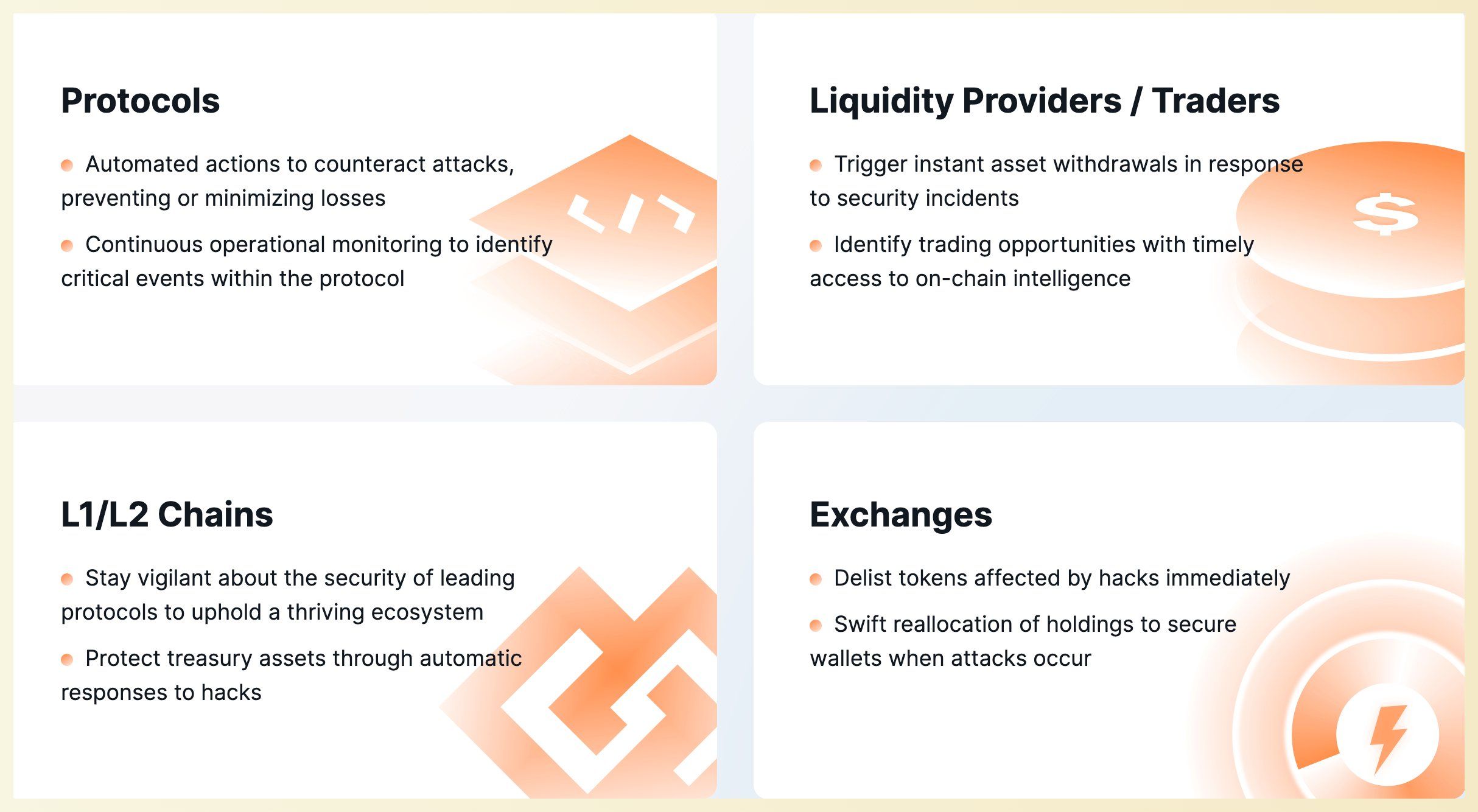
Phalcon is a security platform developed by BlockSec to monitor and block hacks. The system detects suspicious transactions, instantly alerts users, and takes automated actions in response.
Phalcon is a SaaS platform where users can directly log in through our official website to view different pricing plans and features, and subscribe immediately (supporting both credit card and crypto payments). For any questions, feel free to book a demo with our security experts who will address your concerns.
Support Tool: Phalcon Explorer
Phalcon Explorer is a support tool for the Phalcon platform. This powerful transaction explorer is designed for the DeFi community. It provides comprehensive data on call flows, balance changes, and transaction fund flows, as well as supports transaction simulation. This helps developers, security researchers, and traders to more intuitively understand transactions.



