In the rapidly evolving world of decentralized finance (DeFi), the threat of cyberattacks looms large, jeopardizing the security and integrity of digital assets and transactions. Front-running, a tactic traditionally viewed with apprehension due to its potential for abuse, involves preemptively executing trades based on prior knowledge of pending transactions, often to the detriment of regular users. However, when this technique is repurposed by cybersecurity experts, it can morph into a powerful defensive tool against such threats.
In this article, we will introduce BlockSec Phalcon, a cutting-edge platform that transforms front-running from a predatory tactic into a protective strategy. But before we delve into the specifics of Phalcon, let's first understand what front-running is and how it typically functions in the cryptocurrency sector.
Introduction to Front-Running
What is Front-Running?
Front-running is a trading activity where individuals or systems use pre-knowledge of upcoming transactions to execute advantageous trades before those transactions are processed.
In decentralized finance (DeFi), this involves actors detecting pending transactions in the blockchain's mempool and quickly placing their own transactions with higher gas fees to ensure they are processed first, thus gaining a financial edge. This is often carried out by front-running bots programmed to scan the mempool for such opportunities, or by miners who can prioritize their transactions in the block they are validating.
How Does Front Running Work in Crypto?
The sequence of front-running in cryptocurrency markets typically unfolds as follows:
- Pending Orders: Traders queue orders to buy or sell cryptocurrencies.
- Advance Knowledge: Bots or other parties detect these pending transactions in the mempool.
- Front Running Execution: The front runner places a transaction with a higher gas fee to get processed first.
- Profit Realization: The front runner profits from the price changes caused by the original large transaction.
From Threat to Defense: Repurposing Front-Running in DeFi
Front-running, while often creating unfair advantages and negative impacts in decentralized finance (DeFi), can paradoxically serve as a powerful tool for good when wielded by responsible parties. Traditionally, front-running leads to market inefficiencies, higher transaction costs, and potential price manipulations, posing significant challenges for ordinary users. However, when used by defenders of the blockchain ecosystem, such as cybersecurity firms, this technique can transform into an effective defensive strategy.
A prime example of this positive application is BlockSec, a well-known blockchain security company. By employing front-running tactics as part of their crypto hack monitoring and blocking system Phalcon, it has been able to proactively intercept and block numerous malicious activities.
Over the past two years, their innovative approach has successfully thwarted multiple attack attempts, securing assets valued at over $15 million. This showcases how front-running, typically viewed as detrimental, can be repurposed to protect and preserve the integrity of blockchain networks when used responsibly.
BlockSec Phalcon: Leveraging Front-Running for DeFi Protocol Security
What is BlockSec Phalcon?
BlockSec Phalcon is an innovative platform specifically designed to monitor and block hacking attempts in real time. It helps users and protocol operators detect suspicious transactions, receive instant alerts, and take automatic actions to prevent or minimize damage. This system is vital for preventing hacker attacks on DeFi protocols, thereby maintaining the security and trustworthiness of blockchain applications.
Applications of BlockSec Phalcon
How Phalcon Uses Front-Running to Prevent Attacks
Phalcon's detection engine scans every mempool and on-chain transaction for malicious transactions, proposals, and contracts, among other potential threats.
It detects transactions into three risk levels: Attack, Suspicious, and Regular, complemented by user-defined trigger rules. When a transaction meets both the specified risk levels and trigger rules, a predefined response action is automatically initiated.
When initiating response actions (i.e. blocking transactions), Phalcon employs an exclusive bidding strategy to speed up our blocking transactions, thereby frontrunning the attack transactions.
Why Can Phalcon Successfully Execute Front-Running?
- Precise Detection in the Mempool: Phalcon accurately identifies malicious transactions in the mempool. This allows Phalcon to front-run and block the attack even before it occurs, keeping potential losses to zero.
- Exclusive Bidding Strategy: Phalcon strategically bids higher gas fees to ensure its transactions are processed before those of attackers, securing priority in execution.
Can Phalcon Front-Running Occur on Layer 2 Networks?
Layer 2 networks do not have a mempool, so Phalcon cannot detect an attack transaction during the mempool stage and block it before the transaction is confirmed on the chain.
However, Phalcon is still highly valuable for Layer 2 protocols. That's because in most cases, hackers don't launch a single attack; instead, they execute multiple attacks across various chains in a short period. When the first attack transaction is recorded on the blockchain, Phalcon can detect it immediately. If an L2 protocol employs Phalcon, the system can promptly alert the team and automatically pause the protocol, limiting losses to just the initial attack.
Can Phalcon Front-Run Transactions in a Private Mempool?
Phalcon cannot detect transactions within a private mempool because these transactions are undetectable until they are executed on the blockchain.
Despite this limitation, Phalcon is highly effective once an attack is executed, as it can immediately detect the attack, alert the protocol team, and initiate a blocking transaction. This capability is crucial, especially since over 90% of attacks involve multiple transactions, allowing Phalcon to play a pivotal role in preventing further losses after the first attack is detected.
Furthermore, BlockSec is actively collaborating with private mempool providers who meet compliance requirements to enhance our ability to detect and block attack transactions, further strengthening our defensive capabilities.
How to Configure Front-Running in the Phalcon System
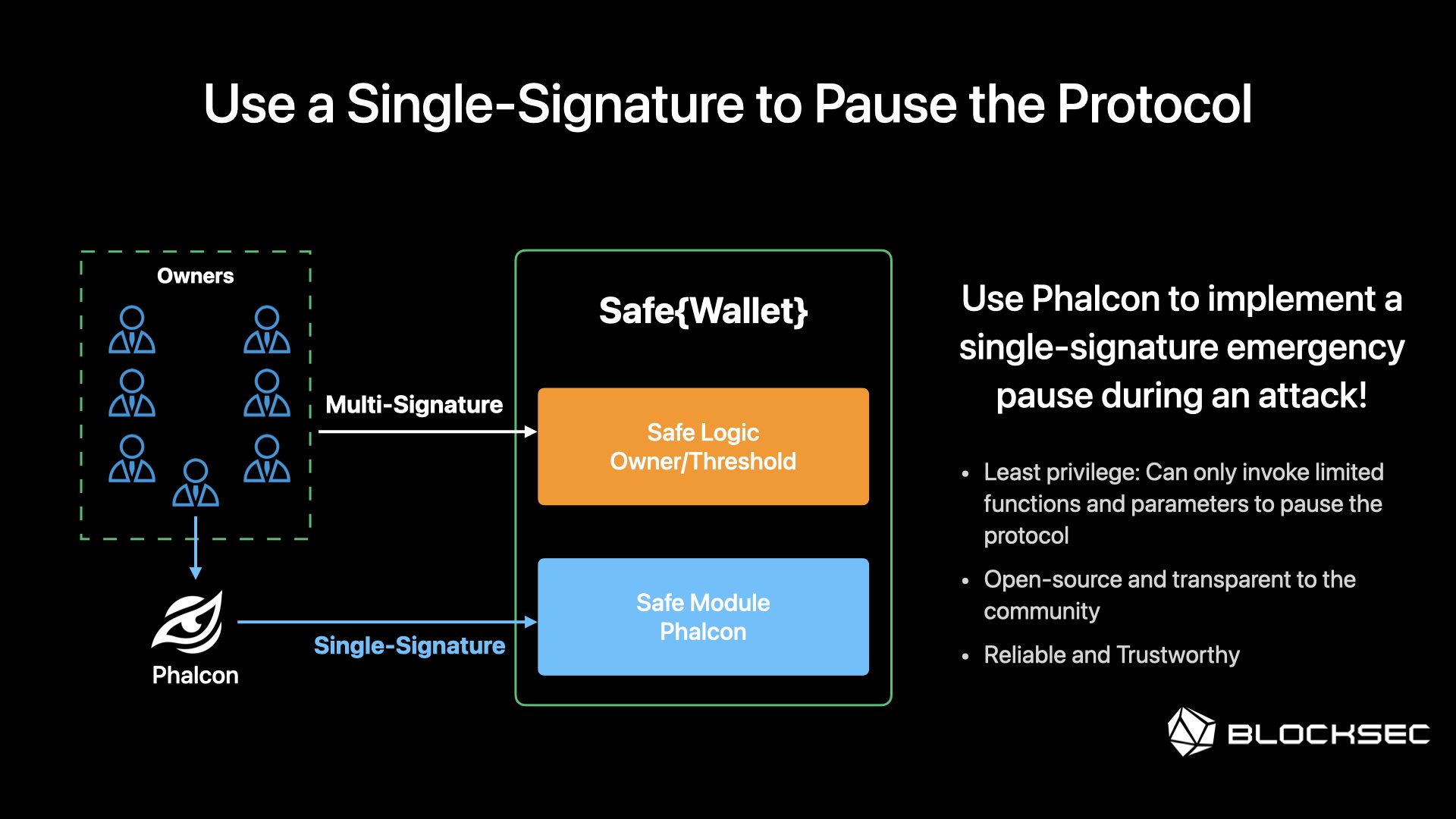
Phalcon's main approach to frontrunning involves automatically initiating a pre-signed pause transaction once the system detects an attack transaction. There are generally two types of contract pauses: via EOA wallet and multi-sig wallet.
-
EOA Wallet: Users need to use their EOAs to pre-sign the blocking transactions and upload them to Phalcon.
-
Multi-sig Wallet: Multi-sig wallets typically require multiple signatories. However, Phalcon offers a streamlined alternative with a custom module for Safe{Wallet}. This module circumvents the usual multi-signature process, allowing an EOA, designated by the user, to autonomously sign the blocking transaction. We've already crafted the module code. Users simply need to integrate the module into their Safe{Wallet} by adding its address. The module can be configured to only pause selected contracts or execute specific functions, providing precise control with no additional risk exposure.
How Can Users Subscribe to Phalcon?
For detailed pricing information on Phalcon, interested users can log in to the Phalcon official website where various feature options and their associated costs are listed. Phalcon operates as a SaaS (Software as a Service) platform. Subscriptions can be made directly through the Phalcon system after users log in.
For those who have questions or need more details about what Phalcon offers, it is possible to book a demo with BlockSec Phalcon's security experts who will address security concerns and demonstrate the platform's capabilities.
Additionally, there is an opportunity to experience Phalcon's functionality through the Phalcon Virtual Experience Journey.
This interactive game allows participants to see how Phalcon effectively blocks an attack transaction. Upon completion of the journey, participants will receive a coupon that enables them to try Phalcon for 7 days at a special introductory price of $9, a significant discount from the regular price of $4,600 per month. This trial offers a practical opportunity to evaluate Phalcon's protective capabilities in a real-world scenario.
Conclusion
In the dynamic and ever-evolving landscape of decentralized finance (DeFi), the necessity for robust security measures cannot be overstated. BlockSec's Phalcon emerges not just as a solution, but as a proactive sentinel designed to safeguard digital assets against the sophisticated threats posed by hackers. By transforming the usually detrimental tactic of front-running into a defensive mechanism, Phalcon sets a new standard in blockchain security.
The growth of blockchain technology underscores the increasing complexity and sophistication of the digital threat landscape. As such, the DeFi ecosystem must continually evolve its security strategies to protect against innovative forms of cyberattacks. The integration of advanced monitoring tools and strategic defenses is essential for maintaining the integrity and trust of digital finance platforms. This holistic approach to security is vital for supporting the sustainable growth and adoption of blockchain technologies in our digital economies.




