A Decade of USDT: Opportunity and Risk
It has been a decade since Tether launched USDT in 2014, the world's first mainstream USD-pegged stablecoin. Now, the landscape is immense: stablecoin transaction volume hit $27.6 trillion in 2024. The total market cap is projected to exceed $250 billion in 2025, with annual transactions reaching $36.3 trillion—surpassing the combined volume of Visa and Mastercard. With price stability tied to fiat or other reserve assets, stablecoins are widely used in cross-border trade, treasury management, and consumer payments. However, USDT’s anonymity has also made it a preferred tool for illicit finance. In 2025, the “Xinkangjia” fraud scandal revealed how USDT was misused for fund collection and laundering, resulting in massive investor losses. This article examines how criminals exploit USDT across blockchains and highlights defense strategies for businesses and users.
USDT Across Major Blockchains
USDT is issued on multiple chains, making it easy for criminals to move funds cross-chain and avoid detection:
-
Tron (TRC-20): $75.8B supply; low fees, high volume—favored for micro laundering.
-
Ethereum (ERC-20): $79B supply; integrated into DeFi—used to mask “fake investment” transactions.
-
BNB Chain (BEP-20): $7.4B supply; tight exchange integration—key laundering route.
-
Solana (SPL): $2.3B supply; fast confirmations—shortens laundering cycles.
-
Polygon (ERC-20): $1.4B supply; scaling layer—often disperses large illegal transfers.
This multi-chain distribution increases tracing difficulty. BlockSec’s Phalcon Compliance and MetaSleuth provide full coverage of major EVM chains and 20+ cross-chain bridges, offering real-time detection and forensics.
Six Emerging Criminal Tactics with USDT
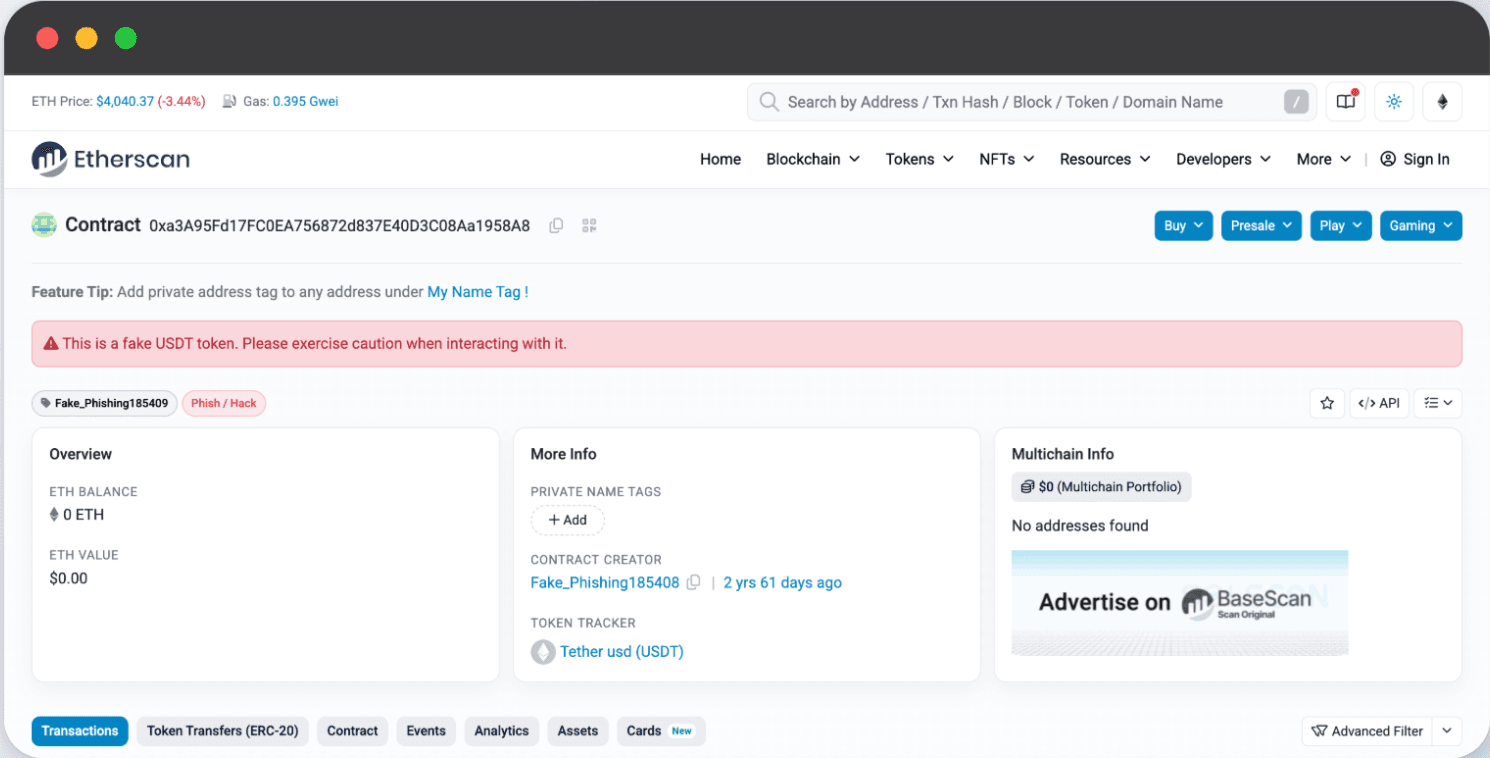
- Fake USDT
Criminals forge fake tokens or falsify transaction records to scam users:
-
“Discounted” OTC deals at 5–10% below market
-
Fake transfer screenshots tricking users into paying fiat upfront
-
Malicious wallet apps with “fake USDT balances”
➡️ Fake tokens can be flagged instantly using tools like BlockSec’s MetaSuites browser plugin and a risk-labeled address database (hundreds of millions of entries).
 2. "Black" USDT
2. "Black" USDT
Funds from fraud, gambling, trafficking, or terrorism finance laundered via:
-
“Score-running” platforms using mule accounts
-
DeFi mixers through lending & liquidity protocols
-
Cross-border OTC trades into exchanges
➡️ For businesses like exchanges and payment providers, accepting Black USDT can lead to frozen assets, license revocation, massive fines, and even criminal charges. Phalcon Compliance detects risky inflows via address scoring, fund tracing, and AI-driven anomaly detection—blocking illicit deposits before they contaminate platforms.
- Stolen USDT
Techniques evolve from phishing to:
-
Plugin hijacks stealing wallet keys
-
Smart contract exploits draining protocols (e.g., $120M theft in 2024)
-
Supply chain hacks injecting backdoors in SDKs (as seen in the high-profile Bybit incident)
-
Malicious upgrades exploiting new features like EIP-7702 (used in attacks on SeedifyFund and Griffin_AI)
➡️ BlockSec’s Phalcon Security stops live attacks, while Phalcon Compliance blacklists attacker-linked addresses to prevent laundering. Over $20M in assets have been rescued via BlockSec white-hat interventions.
- USDT Laundering
Modern laundering = multi-chain hops + DeFi nesting:
-
Split funds into 10–20 “intermediate wallets”
-
Criminals use cross-chain bridges + DeFi loops (borrow–stake–swap)
-
Cash out via offshore exchanges
➡️ Phalcon Compliance reconstructs cross-chain fund graphs, detecting “looping patterns” and providing FATF-aligned compliance reports.
- USDT “Score-Running” Platforms
Mule platforms recruit individuals (students, unemployed) with “work from home” ads:
-
Users bind personal bank cards
-
Receive illicit USDT → transfer fiat to criminal accounts
-
Users earn 1–3% commission
➡️ Phalcon Compliance detects abnormal “multi-account fund pooling” and “high-frequency micro transfers,” pinpointing mule networks.
- USDT Ponzi Schemes
Scammers disguise USDT investments as “low-risk, high-return” with:
-
Fake personas (influencers, “investment gurus”)
-
Multi-level referrals with membership fees (1,000–10,000 USDT)
-
Collapse when inflows dry up—operators disappear with all funds
➡️ Users must stay alert: "Guaranteed returns" is a major red flag.
Conclusion
USDT has become a double-edged sword in the crypto economy. While it enables efficient cross-border payments, its misuse by illicit actors—through fake tokens, laundering schemes, and fraud networks—poses serious risks to financial integrity. Combating these threats requires advanced compliance tools and real-time intelligence. BlockSec’s Phalcon Compliance and MetaSleuth empower businesses to detect, trace, and block illicit USDT flows, enabling exchanges, payment providers, and institutions to stay compliant and safeguard users.
Take Action
🚀 Strengthen your compliance today.
👉 Book a Demo and learn how BlockSec can help you stop illicit USDT flows and build long-term trust with regulators and customers.




