The recent Bybit incident has garnered widespread attention. According to Bybit's report conducted by third parties, the incident occurred because the hacker breached a Safe developer's machine, altered the data Bybit signers intended to sign during transaction initiation, and ultimately executed a malicious upgrade transaction. The incident resulted in nearly $1.5 billion in asset losses. In fact, similar attacks occurred twice last year, including Radiant (loss of approximately $58 million) and the Indian exchange WazirX hack (loss exceeding $200 million), both caused by signing malicious transactions via Safe wallets.
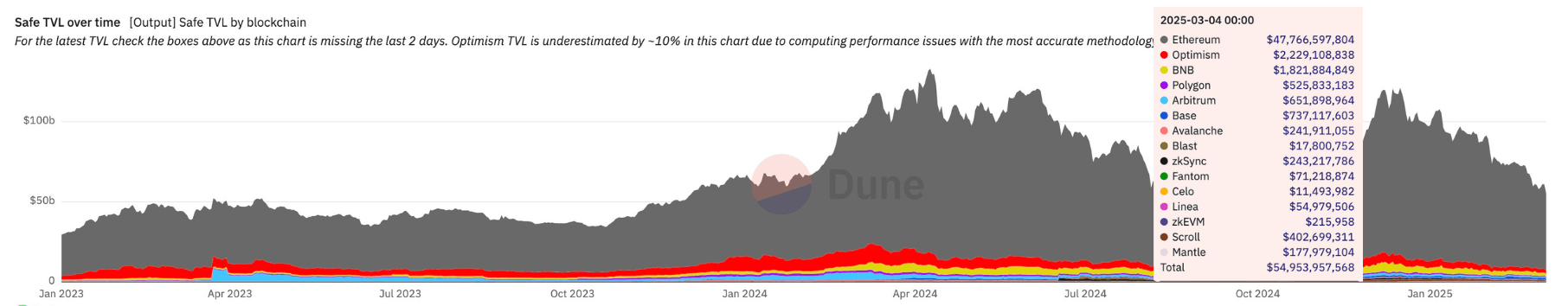
The latest data (March 4) from Dune reveals that over 39.14 million Safe wallets have been deployed in total, managing assets valued at $54.9 billion. To meet user demand and strengthen risk control throughout the lifecycle of using Safe wallets, BlockSec has launched the Safe{Wallet} Monitor. This solution offers users comprehensive visibility into transaction details, risk assessments, and transaction simulations, helping to safeguard assets and prevent potential losses.
Risks of Safe{Wallet} Transaction Signing
- Prime Attack Targets: Safe wallets typically manage large assets, making them prime targets for hackers. For instance, the Bybit incident was a meticulously planned attack, with the hacker deploying and testing malicious contracts two days in advance.
- Extended Security Chain: The security chain involved in the entire operation is very long. Users need to trust Safe's smart contracts, the official website/app, the front and back end, their own computers, browsers, and finally the wallet used for signing. However, attackers can target either Safe or individual signers. A single compromised link—such as tricking a user into signing an upgrade transaction disguised as a normal transfer—can result in devastating consequences.
- Hardware Wallet Limitations: Most hardware wallets cannot interpret Safe transactions. If users are misled by the Safe interface, they are unable to perform cross-verification while signing with a hardware wallet. Coupled with signers' inherent trust in prior approvals, this kind of "blind signing" can easily lead to serious oversights and security incidents.
Safe{Wallet} Monitor
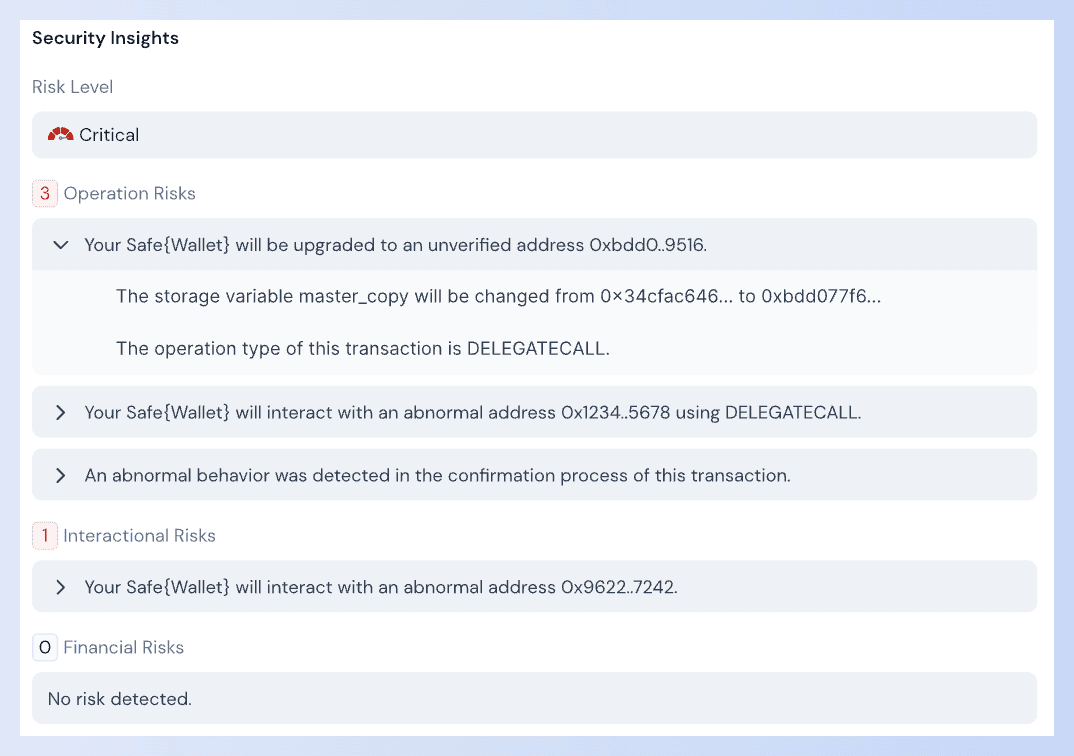
BlockSec's Safe{Wallet} Monitor tracks the entire transaction signing process in real-time, displays transaction details, identifies risks, simulates outcomes, and offers the following features:
- Alerts Risks Before Execution: Our system provides continuous monitoring across all stages of Safe wallet transactions, including initiation, signing, and execution. If a risky transaction is detected, users are alerted before the signing process is completed and prior to the transaction being broadcast.
- Detailed Transaction Insights: Our system intercepts complex transactions and translates them into clear, human-readable explanations, enabling informed decision-making and eliminating blind signing risks.
- Risk Analysis & Execution Simulation: Our system analyzes each transaction's related risks and simulates transaction outcomes before they're executed, to prevent signing unwanted transactions.
- Multi-Channel Verification: Alerts can be sent to both signers and non-signers for additional verification, providing an extra pair of eyes and ensuring thorough cross-checking.
- Whitelist Mechanism: Users can restrict interactions to specific contracts. The system instantly detects configuration changes and responds.
- Automated Response: Automatically triggers a pre-set response mechanism to block attacks upon detecting harmful transactions.
Book a Demo
Any individual or institution using a Safe wallet, especially those managing large assets such as exchanges, protocols, L1/L2 chains, investment institutions, and investors, may face the risk of funds being stolen.
We invite you to book a demo to learn how the Safe{Wallet} Monitor can help you prevent potential risks and protect your assets.
BlockSec Phalcon: Threats Monitoring and Prevention
Safe{Wallet} Monitor is an essential module of Phalcon. Phalcon is a security monitoring and blocking platform launched by BlockSec, providing comprehensive post-launch security protection for protocols, helping liquidity providers, DAOs, fund managers, etc., safeguard their assets. In addition to Safe{Wallet} Monitor, Phalcon also covers:
- Real-time monitoring of attack transactions
- Real-time monitoring of operational, interaction, and financial risks
- Flexible monitoring of token amounts/price, key variables, sensitive events, and function invocation
- Custom monitoring solutions by security experts
- Automated responses with multi-signature wallets
- Emergency response SOP and War Room services
- Root cause analysis
- Audits of fixed smart contract codes
- ...
Conclusion
In the crypto world, security is not optional—it is foundational. BlockSec's Safe{Wallet} Monitor builds multiple defense layers to ensure every Safe{Wallet} transaction withstands unforeseen risks, safeguarding your assets.



