Security at a Glance 👀
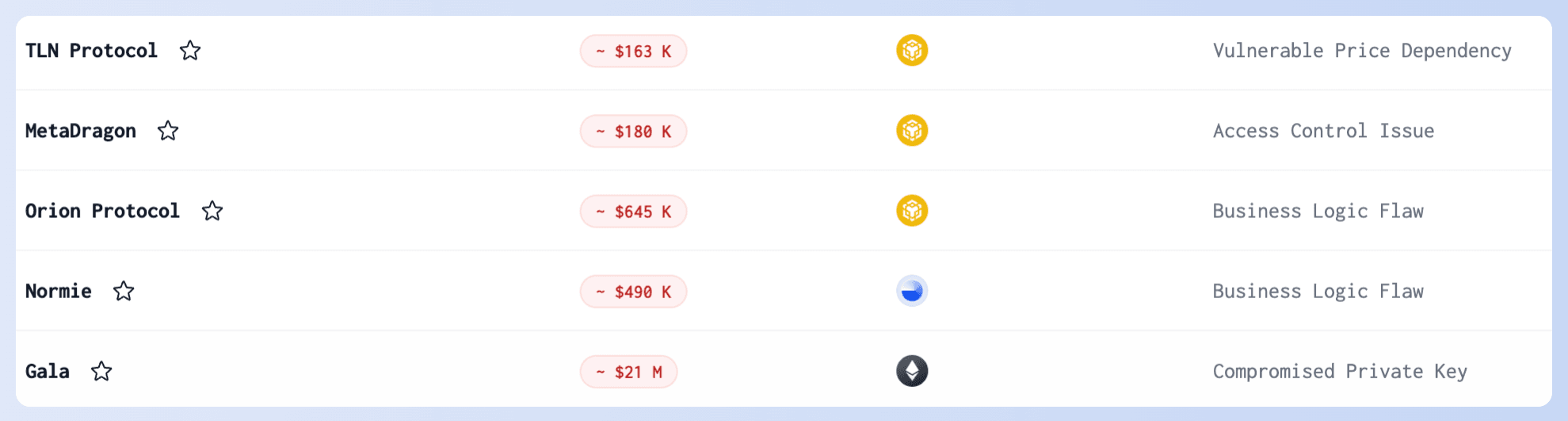
DeFi Exploits
- Gala Game
On May 20, the private key of a Gala administrator was stolen, and the attacker minted 5 billion GALA tokens, exchanging them for $21M worth of tokens on the blockchain. Subsequent to this, an official report from Gala indicated that the breach involved a third-party contractor and that internal procedures have since been rectified, including the removal of unauthorized users. Following an investigation into internal leads, the attacker's identity was confirmed, and the stolen assets were fully returned.
Official report: Gala News
For project teams, establishing a necessary monitoring system for privileged operations is crucial. Inadequate management of private keys poses severe risks of internal and external attacks gaining admin privileges or access to private keys. In this example, employing Phalcon could have helped avoid losses.
- Sonne Finance Incident
On May 14, Sonne Finance on Optimism was exploited, resulting in a loss exceeding $20 million. The root cause was a precision loss in Compound V2. Although the Sonne team was aware of this issue and planned to add liquidity during market deployment to avoid the issue, the attacker exploited a flaw. Multiple scheduled transactions in the timelock were left for anyone to execute, and the attacker executed the market deployment without adding liquidity, completing the exploit.
If the Sonne had used Phalcon, they would have detected the attack sooner and limited the loss to $3 million instead of $20 million. Learn more
- TCH
On May 17, TSC was attacked on the BSC network, suffering losses exceeding $11K due to a signature replay issue. Developers should be aware of at least three types of Signature Malleability:
Due to the characteristics of ECDSA, if (r, s, v) is valid, then (r, secp256k1n-s, 55-v) is also valid, as Ethereum’s ecrecover allows both. To address this, the OpenZeppelin signature library restricts s to be less than secp256k1n/2+1. (OpenZeppelin Contracts)
Regarding the value of v, 0 and 27 mean the same, as do 1 and 28, with 27 being a coding standard. Some libraries convert 0 and 1 to 27 and 28 before verification, but OpenZeppelin currently only supports 27 and 28.
OpenZeppelin previously supported two types of byte signatures, one with v as a separate byte following s, and another with v in the high order of s. (Malleable Signatures)
- TonUP
A project on the TON chain, TonUP, announced that its staking contract was hacked, planning to allocate funds to buy back 307,264 tokens to compensate users. As new ecosystems bring new opportunities, they also come with the threat of hacks.
🫡 The attack transactions, root causes, and PoC of major attacks in May are all recorded in our Security Incidents list for your review.
Phishing
- Pink Drainer
The Pink Drainer announced its closure, claiming to have made enough and planning to retire. However, exiting the scene might not be as straightforward as they anticipate.
- Whale's Address Poisoning Attack
On May 3, a whale suffered an address poisoning attack, losing 1,155 WBTC worth around $70 million. Fortunately, the attacker returned the funds after persistent community efforts. Phishing attacks involve social engineering and can target even the most DeFi experts. Stay vigilant!
Legal Action
On May 15, the U.S. Department of Justice announced the arrest of two brothers for attacking the Ethereum blockchain and stealing $25 million in cryptocurrency. These attackers exploited vulnerabilities in the Flashbot Relay to attack MEV bots. This was a highly sophisticated attack, and our in-depth analysis is available here.
Read the DOJ's press release here.
Blog Article
Phalcon Virtual Experience Journey
😎 Ready for a LIFE-AND-DEATH battle against hackers?
We invite you to participate in the "Phalcon Virtual Experience Journey" for FREE.
Battle against hackers, confront REAL on-chain attacks, and use our automated attack-blocking platform Phalcon to save millions in assets! Are you ready to be a hero?
MetaSuites now supports Solana!
MetaSuites 5.0 Major Upgrade introduces support for Solana, adds cross-site local labels, and enhances DeBank, Arkham, and Merlin Scan! Click here to learn more.
🎉🎉🎉
We are absolutely delighted to share that our esteemed partner, DeFiHackLabs, has been awarded a 35,000 USDT grant from GCC. This funding will serve as their initial operational capital, supporting their relentless efforts in the Web3 security field and nurturing more talent.
Congratulations to DeFiHackLabs on this well-deserved recognition and here's to more groundbreaking achievements together! 👏



