Every financial business moves money, but very few truly understand the risk hidden inside each transaction. You might screen users at onboarding, yet risky funds can still flow through your platform later on. That is where most compliance problems begin. A single high risk transaction can expose you to sanctions, investigations, frozen accounts, or even lost partners.
This is exactly why KYT exists. Know Your Transaction helps you see, explain, and manage transaction risk in real time, long before it turns into a costly compliance failure.
The Meaning of KYT
KYT, which stands for Know Your Transaction, is the systematic process of monitoring, analyzing, and assessing financial transactions to detect suspicious activity and financial crime risks.
In simple terms, KYT focuses on what the money is actually doing, rather than just looking at who the customer is.
This definition applies widely across traditional finance, modern fintech, and cryptocurrency. However, it becomes especially critical in blockchain-based systems where transactions move globally at lightning speed.
What Is KYT (Know Your Transaction)?
Know Your Transaction is a core, non-negotiable part of modern compliance and risk management. It refers to the ongoing monitoring of transactions to identify suspicious behavior, illicit fund flows, or regulatory risks.
Unlike simple one-time checks, KYT is a continuous effort. It looks at transactions as they happen and evaluates them based on multiple signals, such as the total amount, frequency, counterparties involved, behavior patterns, and risk exposure.
KYT vs Transaction Monitoring: Are They the Same?
You will often see the terms KYT and transaction monitoring used together, but they are not exactly the same thing.
Transaction monitoring is a broad term that describes any system that observes transactions.
KYT, however, is more specific and risk-focused. It adds context and interpretation to transaction data.
Think of it this way:
- Transaction Monitoring: Shows what activity is happening
- KYT: Explains whether that activity is risky and why
Ultimately, KYT is the engine that turns raw transaction data into clear compliance decisions.
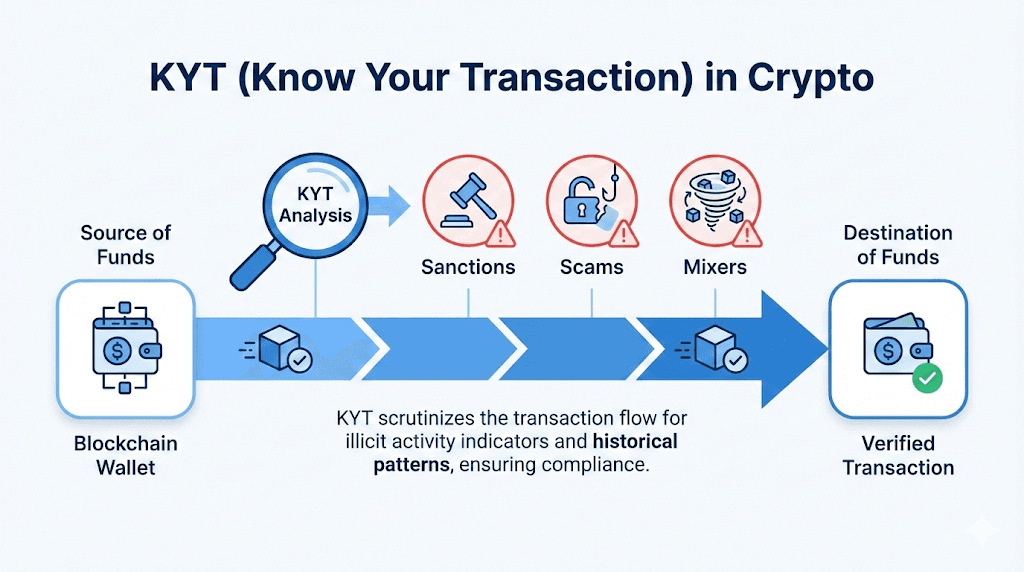
KYT in Crypto: Why It Often Starts With Wallet Risk
In the world of cryptocurrency, KYT usually begins by examining wallets and addresses. Because there are no real names or traditional bank accounts recorded on-chain, risk must be intelligently inferred from a user's behavior, their risk exposure, and their transaction history. That is why KYT in crypto heavily focuses on tracing the initial source of funds and tracking their final destination. It also involves carefully reviewing a wallet's past interaction history and scanning for any exposure to high-risk entities. This wallet-centric approach makes KYT an absolutely essential tool for crypto exchanges, digital wallets, DeFi apps, NFT platforms, and blockchain payment providers.
Why KYT Matters and Who Needs It
KYT is not just a regulatory checkbox; it is a highly practical tool for protecting your business. There are three main reasons why KYT matters so much. First, for regulatory compliance, Anti-Money Laundering (AML) and Counter-Terrorist Financing (CTF) regulations require financial institutions to closely monitor transactions and report suspicious activity. KYT provides the necessary structure to reliably meet these legal obligations. Second, for risk prevention, issues like fraud, money laundering, and sanctions exposure almost always appear at the transaction level. KYT helps you catch these risks early before they escalate. Third, it builds trust and reputation. Partners, banks, and regulators all expect strong transaction controls, and weak KYT can easily lead to frozen accounts, lost licenses, or permanent reputational damage.
Because of these risks, KYT is relevant for a massive range of businesses. It is required for traditional banks, financial institutions, fintech startups, and payment platforms. In the digital asset space, crypto exchanges, custodians, and wallet providers must rely on it. It is also vital for DeFi protocols, infrastructure developers, stablecoin issuers, and fiat on-ramp services. Simply put, if your product moves money, KYT must be part of your risk defense surface.
KYT vs KYC vs KYB: The Simple Differences
These three compliance concepts serve different roles.
| Term | Meaning | Focus | When It Happens |
|---|---|---|---|
| KYC | Know Your Customer | Identity verification of individuals | Onboarding |
| KYB | Know Your Business | Verification of companies | Onboarding |
| KYT | Know Your Transaction | Monitoring transaction behavior | Continuous |
Example:
- KYC: Confirms the identity of a new user
- KYT: Detects suspicious transactions after the user begins operating
How KYT Works: Step by Step
A modern KYT system typically follows a structured workflow.
Step 1: Collect Transaction Signals
The very first step is collecting transaction signals and data. This includes gathering the transaction amount, frequency, asset type, blockchain network, processing time, velocity, and the sender and receiver addresses. It also pulls in related metadata depending on the specific platform. In crypto, all of this data comes directly from the public blockchain and specialized analytics tools
Step 2: Screen Counterparties and Exposure
The second step is screening counterparties and measuring exposure. The system actively evaluates whether the wallets or entities involved are linked to global sanctions lists, known scams, fraud, major hacks, or exploits. It also checks for the use of privacy mixers and any ties to high-risk jurisdictions.
This step answers the critical question:
Who is this transaction interacting with?
Step 3: Detect Patterns and Assign a Risk Score
The third step focuses on detecting patterns and assigning a concrete risk score. Because KYT is not just about looking at single transactions in isolation, it actively looks for broader behavioral patterns. It uses a mix of rules-based detection, deep behavioral analysis, and machine learning models to handle risk scoring and tiering. The primary goal here is to assign a clear risk level and carefully explain the reasons behind that specific score.
Step 4: Alert, Review, and Report
The final step is to alert, review, and report. When the risk score exceeds an acceptable threshold, the KYT system immediately triggers alerts. Compliance teams can then review the transaction, investigate its context, and confidently decide whether to allow, block, or escalate the transfer. If necessary, they can also file regulatory reports. A strong, well-designed KYT process will automatically keep a full audit trail of all these steps.

Key KYT Red Flags to Watch For
Running an effective KYT program relies heavily on recognizing common risk signals. There are several major red flags that compliance teams must watch for. These include users structuring transactions into smaller amounts to avoid legal reporting thresholds, or the rapid movement of funds across multiple wallets to hide a money trail. Any interaction with sanctioned addresses, blacklisted addresses, or exposure to hacked and stolen funds is incredibly dangerous. Teams must also flag the use of cryptocurrency mixers or obfuscation services, as well as sudden, unexplained spikes in transaction volume. Finally, new wallets showing unusually high-value activity and patterns of cross-chain bridge abuse should trigger immediate reviews. While these signals do not automatically mean a crime has happened, they absolutely require immediate attention and investigation.
KYT Challenges and How to Solve Them
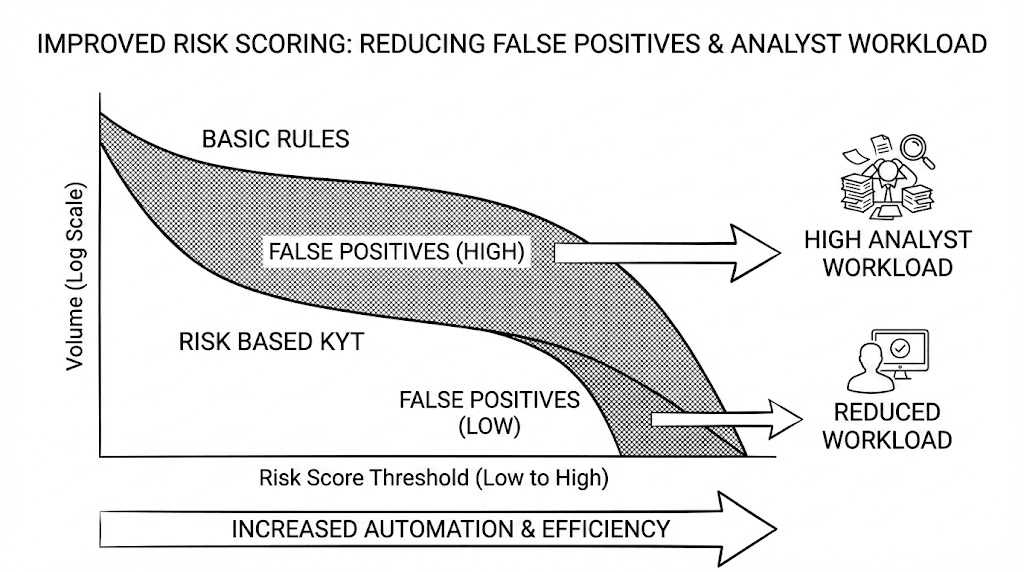
False Positives
Strict rules can generate excessive alerts.
Solution:
Use risk-based scoring and contextual analysis instead of binary rules.
Data Coverage and Cross-Chain Complexity
Crypto assets move across multiple chains.
Solution:
Adopt tools supporting:
- Multi-chain analytics
- Comprehensive labeling databases
Operational Bottlenecks
Manual review processes are slow and expensive.
Solution:
- Automation
- Risk tiering
- Structured case management
What to Look For in a KYT Tool
Not all KYT tools on the market are created equal, so choosing the right one is vital. A modern solution must offer broad blockchain and asset coverage, as well as real-time transaction screening. Furthermore, it needs to provide easily explainable risk indicators—not just a mysterious number score—alongside configurable risk thresholds. Ensure the tool includes built-in case management, detailed audit logs, API access for smooth integration, and strong support for generating required regulatory reporting. Above all, your KYT tool should actually help you make confident decisions, rather than just generating endless alerts.
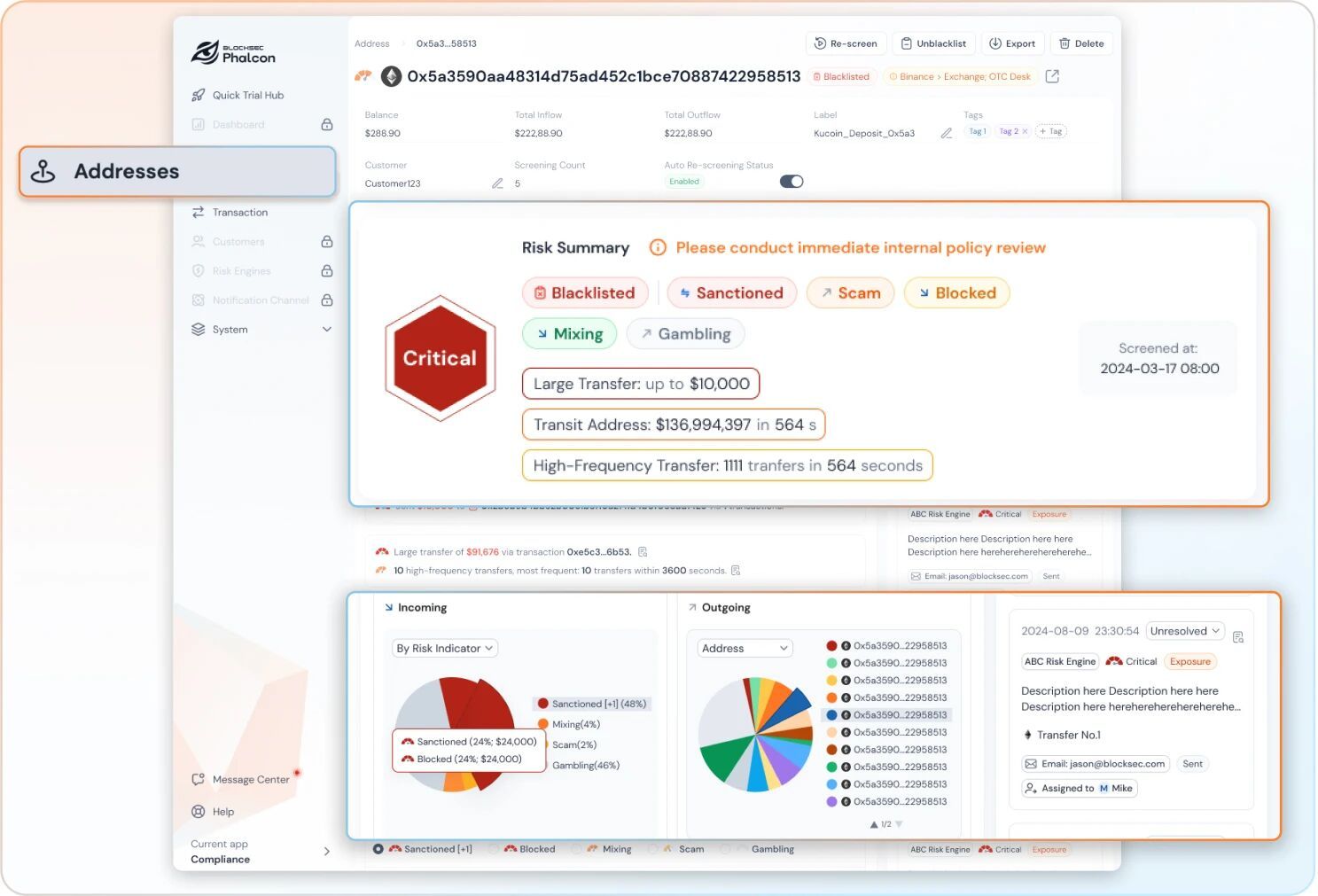
Where Phalcon Compliance Fits
Phalcon Compliance is designed for crypto environments where speed and clarity matter.
It helps teams screen wallets and transactions in real time, understand why a transaction is risky, and build an auditable compliance workflow.
Instead of relying on a single risk score, Phalcon Compliance provides detailed risk context such as exposure paths, behavioral indicators, and historical patterns. This allows teams to confidently decide whether to allow, review, or restrict a transaction.
A Quick KYT Best Practices Checklist
When you are designing or improving your KYT process, keeping a few best practices in mind will keep you on track. Always define clear risk policies and logical thresholds for your platform. It is highly recommended to segment your users and transactions by their specific risk tiers. Your program should harmoniously combine automated rules, intelligent scoring, and careful human review. Always maintain full, transparent audit trails for all your decisions. Additionally, remember to regularly tune your models and rules to stay ahead of new threats, and routinely test your KYT coverage on key fund flows, such as deposits and withdrawals. Good KYT is an iterative process; it naturally improves as your own understanding of risk improves over time.
Conclusion
KYT is no longer optional for businesses that move money. Understanding the KYT definition is the first step toward building a safer and more compliant transaction flow.
By monitoring transactions continuously and interpreting risk signals in context, KYT helps you protect your platform, your users, and your reputation.
If you operate in crypto or fintech and need clearer visibility into transaction risk, a modern KYT solution like Phalcon Compliance can help you move from reactive alerts to confident decisions.
Book a demo with our security experts to see how Phalcon can automate your compliance workflow.
FAQ: KYT Definition and Common Questions
What does KYT stand for?
KYT stands for Know Your Transaction. It refers to monitoring and analyzing transactions to detect financial crime risks.
Is KYT required by law?
Yes. In many jurisdictions, KYT is effectively required under AML and CTF obligations, even if not always named explicitly.
How is KYT different in crypto?
Crypto KYT focuses more on wallet behavior, on chain exposure, and transaction patterns rather than personal identity.
What data is needed for KYT?
Typical data includes transaction details, counterparty information, behavioral patterns, and external risk intelligence.
How do you reduce false positives in KYT?
By using risk based scoring, contextual analysis, and feedback loops instead of static rules alone.




