This guide explains what DeFi compliance means in 2026, why it is now a technical requirement, and how protocols can build a step-by-step compliance framework to unlock institutional capital and avoid regulatory shutdown.
The world of decentralized finance (DeFi) has reached a major crossroads. For years, the industry followed a simple rule: "code is law." This meant that as long as a smart contract worked, it didn’t need to follow the rules of traditional banks. However, throughout 2024 and into 2025, this began to change. Global regulators have moved from just watching the market to actively enforcing laws. Today, DeFi compliance is no longer just an idea. It is a requirement for any project that wants to survive and attract large-scale investment.
From "Code is Law" to "Compliant by Design"
The End of the "Grey Area"
This shift is happening because governments worldwide are working together to oversee crypto. The Financial Action Task Force (FATF) has updated its global rules. Under the FATF framework, certain DeFi creators and participants may qualify as "Virtual Asset Service Providers" (VASPs), particularly those who maintain control or influence over the protocol.
Enforcement timelines vary significantly by jurisdiction, but the direction is clear: projects with identifiable governance entities should plan for AML and "Know Your Customer" (KYC) obligations equivalent to those applied to traditional financial companies.
At the same time, the European Union has launched its Markets in Crypto-Assets (MiCA) regulation, which is a major step toward standardized oversight of crypto-asset service providers. Fully decentralized protocols with no identifiable issuer or intermediary currently fall outside MiCA’s direct scope.
However, protocols with identifiable governance bodies, foundations, or token issuers are already subject to MiCA’s CASP (Crypto-Asset Service Provider) licensing and transparency requirements, with the EU Commission mandated to propose further DeFi-specific rules. In the United States, the U.S. Treasury continues to warn that being "decentralized" does not give a project a free pass to ignore the Bank Secrecy Act or international sanctions.
The Real Risks of Ignoring the Rules
If a DeFi project ignores these changes, it faces more than just legal fines. The actual risks to the protocol include:
-
Losing Access to Funds: Large institutional investors and professional traders will not put money into "dark" pools that cannot prove their funds are clean.
-
Protocol Freezing: If regulators take action against a project’s developers or its DAO members, the entire protocol could stop growing or be abandoned by its users.
-
Sanction Problems: Without proper screening, a protocol might accidentally help criminal groups, such as the Lazarus Group, move money. This can lead to the project’s tokens being banned by major exchanges and stablecoin providers.
A Security-First Approach
At BlockSec, we believe the strongest DeFi projects are those that treat compliance as part of their overall security. Just like a code bug can drain a treasury, a lack of compliance can cut a protocol off from the rest of the financial world. The leaders of the next wave of DeFi will be the ones who build legal transparency directly into their technology.
Barriers to Achieving DeFi Compliance: Solving the Decentralization Paradox
Building a protocol that meets global standards is difficult because DeFi was originally designed to be anonymous and permissionless. To achieve a high level of DeFi compliance, developers must solve specific technical "bottlenecks" that traditional banks never have to worry about. At BlockSec, we categorize these hurdles into three main areas: privacy, code immutability, and cross-chain tracking.
1. The Privacy vs. Transparency Conflict
The biggest challenge is the conflict between user privacy and the need for oversight. Most DeFi users value their privacy and do not want to upload sensitive personal documents to a public blockchain. However, the FATF has made it clear that Virtual Asset Service Providers (VASPs) must be able to identify and prevent illegal money transfers. This creates a difficult question of how to prove a user is clean without revealing their real-world name or location to everyone on the network.
Many projects are now turning to Zero-Knowledge Proofs (ZKP) and Decentralized Identity (DID) standards. This technology allows a user to prove a statement is true—such as "I am not on a sanctions list"—without sharing their underlying personal data.
2. Immutable Code vs. Constantly Changing Laws
In DeFi, many believe that "Code is Law," and smart contracts are usually permanent once they are deployed. However, global laws and sanctions lists, like the OFAC SDN List, change almost every week. If a smart contract is set in stone, it cannot easily be updated to block a newly sanctioned wallet. This creates a massive legal risk for developers and the community. To fix this, teams are moving toward modular contract designs. By embedding compliance hooks, a protocol can check an external data feed before any transaction is finalized. If a wallet is flagged as high-risk, the smart contract can automatically reject the transaction in real-time.
3. The Complexity of Cross-Chain "Hops" and Mixers
Protocols must also deal with the complexity of cross-chain "hops" and mixers. Criminals often try to hide their tracks by moving money across different blockchains using bridges or privacy tools like Tornado Cash. According to our 2025 Crypto Crime Report, hackers are increasingly using sophisticated cross-chain maneuvers to bypass basic security filters.
This means effective compliance now requires deep forensics that scan a wallet's history across multiple networks. This is where Phalcon Security provides a vital advantage. By using "time-of-check" monitoring, protocols can inspect a transaction in the "mempool"—the waiting area before a block is confirmed—to stop illicit funds before they ever enter a liquidity pool.

Why Technical Security and Compliance are Inseparable
At BlockSec, we have seen that a protocol's greatest threat isn't always a bug in the code; it can also be a lack of oversight. If a protocol becomes a haven for money laundering, it risks being isolated from the rest of the financial world. Stablecoin issuers like Circle (USDC) or Tether can freeze assets linked to illegal activity, which could drain a protocol's liquidity overnight.
By treating DeFi compliance as a technical "guardrail" rather than a legal burden, developers can build more resilient systems. Integrating these checks directly into the code ensures that the protocol remains permissionless for honest users while staying "off-limits" for bad actors.
Why DeFi Compliance is a Critical Frontier
Implementing DeFi compliance presents unique challenges that traditional financial systems never had to face. The friction between privacy-preserving blockchain technology and "Know Your Customer" (KYC) mandates creates a complex environment for developers.
-
The Myth of the "Middleman": In traditional finance, banks act as gatekeepers. In DeFi, smart contracts automate these functions, leading to a "responsibility vacuum" that regulators are now moving to fill.
-
Pseudonymity vs. Accountability: Balancing user privacy with the need to prevent illicit fund flows is the central tension of modern Web3 development.
-
Regulatory Fragmentation: From the EU’s MiCA to evolving SEC frameworks in the US, DeFi projects must navigate a patchwork of global rules that are often in flux.
A Strategic Roadmap to Achieving DeFi Compliance
Navigating DeFi compliance is not just about following rules. It is about building a protocol that is "institutional-grade." To move from a risky, anonymous platform to a trusted financial ecosystem, developers should follow a structured, technical roadmap. By treating compliance as a core feature—much like security—projects can protect their users and ensure long-term growth.
Step 1: Regulatory Mapping and Perimeter Defense
Before writing code, you must identify your legal "perimeter." This means understanding which jurisdictions your users come from and how international standards apply to your specific protocol.
-
VASP Identification: Determine if your protocol falls under the definition of a Virtual Asset Service Provider (VASP) as defined by the FATF.
-
Regional Compliance: Research regional laws, such as the EU’s MiCA, to see if you need specific licenses or data-reporting mechanisms.
Step 2: Privacy-Preserving Identity Layers
Traditional KYC, collecting IDs and storing them in a database, is a major security risk for DeFi projects. Instead, use "Privacy-First" verification.
-
Zero-Knowledge Proofs (ZKP): Use ZK-technology to verify that a user is not on a sanctions list without actually holding their personal data.
-
Decentralized Identifiers (DID): Allow users to own their identity credentials. Your protocol simply checks a "credential" on-chain to confirm compliance before allowing a trade. This satisfies W3C standards for Decentralized Identifiers while keeping user data private.
Step 3: Real-Time Screening and Risk Prevention
Waiting for a transaction to finish before checking it is a dangerous strategy. Once illicit funds enter your liquidity pool, the pool is "poisoned." Proactive screening is required to stop bad actors at the door.
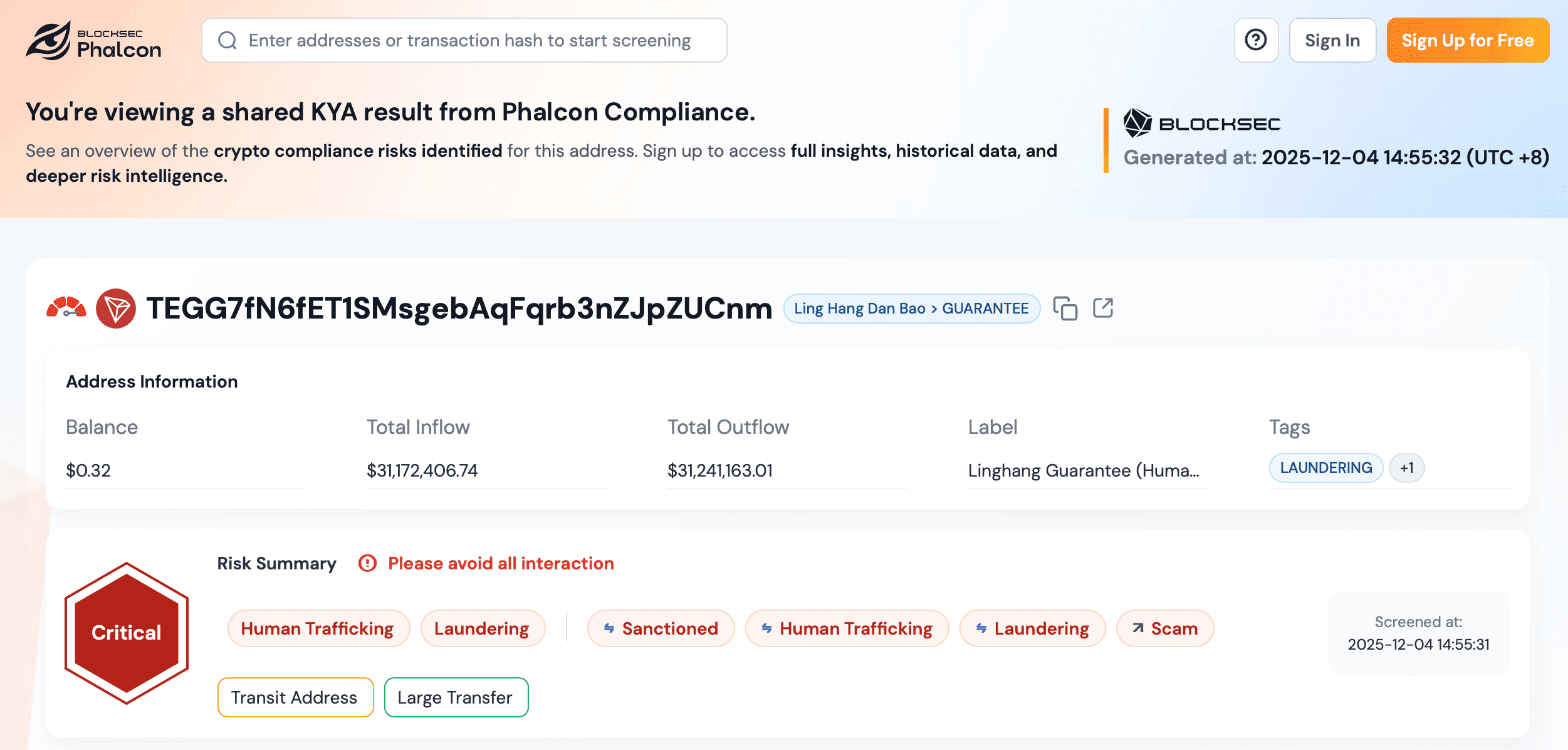
This is where Phalcon Compliance provides a critical advantage. Unlike older tools that are slow and manual, Phalcon Compliance features a search-first architecture. This allows your team to instantly scan any wallet address or transaction hash directly from a landing page, no long onboarding required.
-
Risk Detection: Use Phalcon Compliance’s millisecond-level APIs to conduct KYT + KYA screens on addresses and monitors transactions in real time. By identifying high-risk signals before execution, you can prevent sanctioned funds from ever reaching your smart contracts.
-
AI-Driven Risk Scoring: Phalcon uses a database of over 400 million address labels and AI behavior analysis to give every transaction a risk score (High, Medium, or Low). This allows you to set automated rules: for example, you can automatically block any transaction with a "High" risk score.
Step 4: Automating "Compliance Hooks" in Smart Contracts
To achieve true DeFi compliance, the rules must be part of the code. "Compliance Hooks" are modular pieces of code that trigger a check during every interaction.
-
API Integration: Connect your smart contracts to the Phalcon Compliance API. Before a user swaps tokens or provides liquidity, the contract sends a quick query.
-
Multi-Chain Tracing: Criminals often move funds across different networks to hide their tracks. Phalcon’s Multi-Chain and Multi-Hop Tracing allows your protocol to see if a user's funds originated from a mixer or a known hack on a different blockchain (like the Lazarus Group exploits), ensuring your protocol remains clean across the entire ecosystem.
Step 5: Transparency and Regulatory Reporting
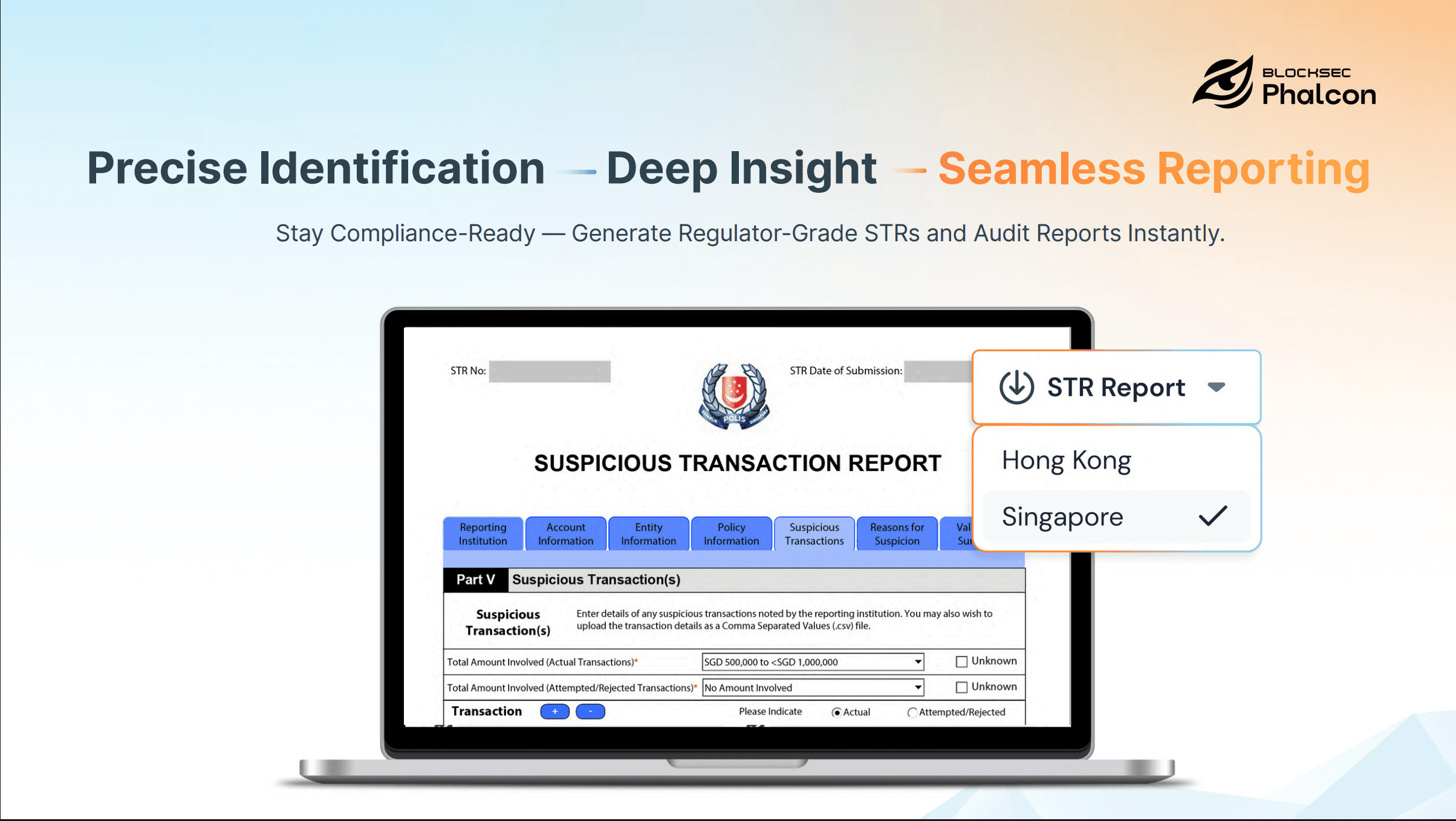
When suspicious activity occurs, you must be able to document it for the authorities. Manual reporting is slow and prone to errors.
-
One-Click STR Generation: With Phalcon Compliance, you can generate "regulator-ready" Suspicious Transaction Reports (STR) with a single click. These reports include full audit trails and fund-flow visualizations, making it easy to share accurate data with law enforcement.
-
Customizable Risk Engines: Every country has different rules. Use a customizable risk engine to adjust your protocol’s filters based on the specific market you are serving.
Step 6: Continuous Security and Compliance Audits
Compliance is not a one-time setup, it is a living process. Just as you perform regular security audits to find code bugs, you must perform "compliance audits."
-
Post-Incident Forensics: If an attack occurs, use visualization tools to trace where the funds went and identify the "exit points" (such as exchanges).
-
Evolving Data Feeds: Ensure your protocol is connected to real-time intelligence feeds that update as soon as the OFAC SDN List or other global sanctions change.
Conclusion: Compliance as the Foundation for Growth
The future of decentralized finance depends on a stable balance between privacy and accountability. As we move through 2026, the industry has clearly shifted away from the "Wild West" era toward a more regulated environment. Global frameworks, such as the EU’s MiCA, now provide the roadmap for legitimate on-chain growth and consumer protection.
For modern protocols, DeFi compliance is much more than a legal burden; it is a vital competitive advantage. By meeting these standards, projects can unlock massive institutional liquidity and build lasting trust with their users. Integrating proactive solutions like Phalcon Compliance ensures that your protocol remains secure and stays ahead of rapidly changing global sanctions. Ultimately, the winners in the Web3 space will be those who treat compliance as an essential part of their security architecture, paving the way for a mature and sustainable financial future.
FAQ
1. What does DeFi compliance mean for protocols?
It refers to the technical framework used to follow global AML/CTF laws. This includes screening wallets against sanctions lists and monitoring transaction risks to prevent financial crimes.
2. Can DeFi projects stay compliant while protecting user privacy?
Yes. By using Zero-Knowledge Proofs (ZKP) and Decentralized Identity (DID), protocols can verify if a user meets legal requirements without ever seeing or storing their sensitive personal data.
3. How does Phalcon Compliance help DeFi teams?
Phalcon Compliance provides real-time risk scoring and AML screening. It identifies high-risk wallets and generates "regulator-ready" reports, helping protocols make informed decisions about their liquidity exposure.
4. What is the difference between Phalcon Compliance and Phalcon Security?
Phalcon Compliance focuses on risk identification and reporting, such as AML screening and forensics. Phalcon Security is the tool used for active intervention, such as blocking or stopping malicious transactions.
5. Why a risk-scoring engine important for DeFi?
Because global sanctions lists change daily. A real-time engine allows protocols to detect funds from high-risk sources, like mixers or recent hacks, before they damage the protocol's reputation or institutional access.




