A Global Stage for a Global Fight
On August 27-28, BlockSec was invited to the 2025 Virtual Asset Technical Exchange in New Orleans. As the first keynote speaker, we presented our frontline research to a global audience of law enforcement, industry leaders, and academic experts, sharing critical intelligence on fighting crypto-enabled crime.
The summit, co-hosted by the NCIJTF and FBI, is a leading U.S. cyber-crime collaboration forum, advancing international cooperation and addressing emerging risks from virtual asset abuse.
Keynote Spotlight: Exposing the "Guarantee Platform" Ecosystem
BlockSec Co-Founder, Professor Yajin Zhou, delivered the keynote, “An Initial Investigation on the TG Crypto Guarantee Ecosystem.” His presentation went deep into the dark financial infrastructure enabling human trafficking in Southeast Asia.
Our investigation revealed a chillingly corporate-like system:
-
The Structure: Over 65 industrial-scale scam compounds in regions like Cambodia and Myanmar operate with terrifying efficiency.
-
The Mechanism: Traffickers use USDT-based "guarantee platforms" as escrow services to trade human lives. These platforms process transactions—like 💲1.9 million in just 6 months—and charge a 10-15% fee for each victim delivered.
-
The Human Cost: Our system recorded days with more than 10 victims being trafficked, a stark reminder of the urgency of this fight.

Our Technology: From Automated Intelligence to Actionable Insights
How can we fight an enemy that moves at the speed of the blockchain? Professor Zhou detailed BlockSec’s proprietary four-step intelligence system, the engine behind our Phalcon Compliance suite:
-
Automated Data Collection: Proactively gathering intelligence from high-risk online communities.
-
LLM-Based Analysis: Using Large Language Models to interpret unstructured data and identify criminal patterns.
-
Blockchain Database Matching: Correlating off-chain intelligence with our massive on-chain address database.
-
Deep Fund Tracing: Visualizing and tracking the flow of illicit funds across multiple hops and chains.
This powerful, replicable model, developed by our team, provides law enforcement and Virtual Asset Service Providers (VASPs) with the tools to move from reactive analysis to proactive defense.
A Global Challenge Demands a Collaborative Response
The enthusiastic reception at the FBI summit reinforced a critical belief: Web3 security is not a regional issue; it's a global one that requires a united front.
The insights from our research, backed by over 10,000 academic citations at premier security conferences like IEEE S&P and USENIX Security, demonstrate that expertise knows no borders. We are proud to contribute our unique intelligence and technical capabilities to this global effort.
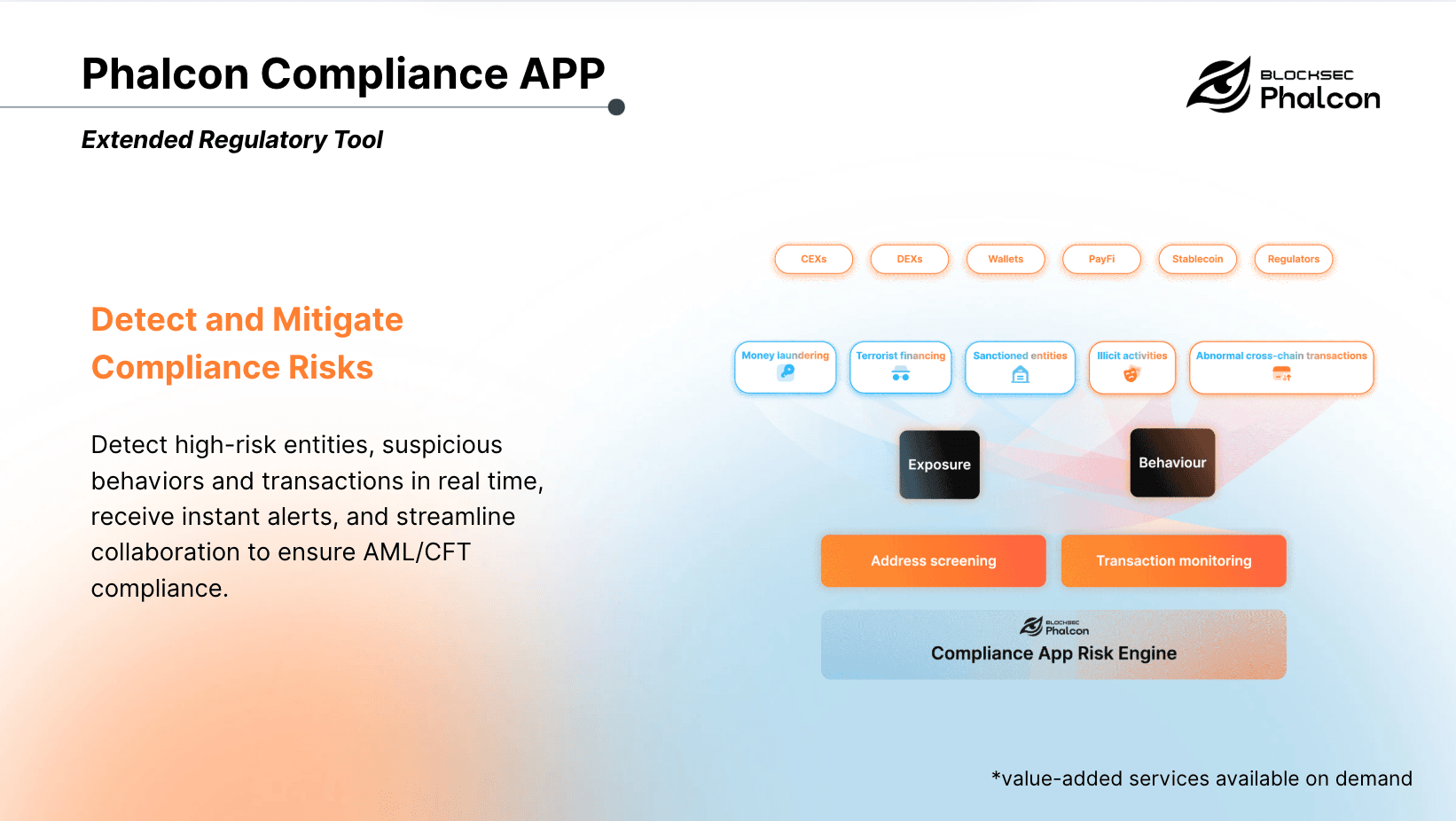
Protect Your Platform from Tainted Funds
Being invited by the FBI is both an honor and a responsibility. BlockSec is committed to building a safer Web3 ecosystem by bridging the gap between cutting-edge research and real-world compliance needs.
Illicit funds from trafficking rings and scam compounds can silently contaminate your platform, putting you at risk. Don't wait for a crisis.
🔗 Discover how Phalcon Compliance can shield your platform with real-time, AI-powered transaction monitoring. Book a Demo Today




