2021年8月8日(北京时间,区块高度12982491),Zerogoki遭受攻击,损失约67万美元。经过调查,我们发现攻击与被篡改的价格预言机有关。攻击者提供了一个由合法私钥签名的价格预言机,其中包含精心构造的兑换代币数量。然而,攻击者能够构建有效签名的方式目前尚不清楚。
代码分析
我们首先对被攻击的合约进行了分析(0x80ecdb90)。
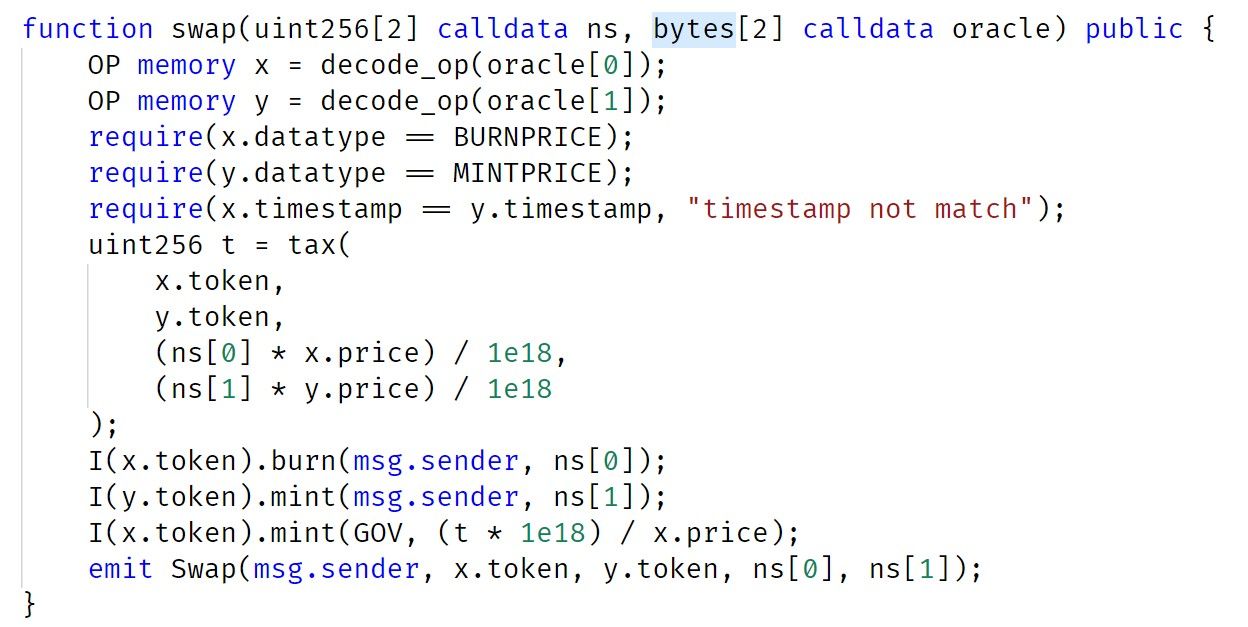
swap函数调用decode_op以获取预言机中的信息。在执行验证后,合约会销毁ns[0] x.token,铸造ns[1] y.token,并将兑换费用支付给GOV合约。
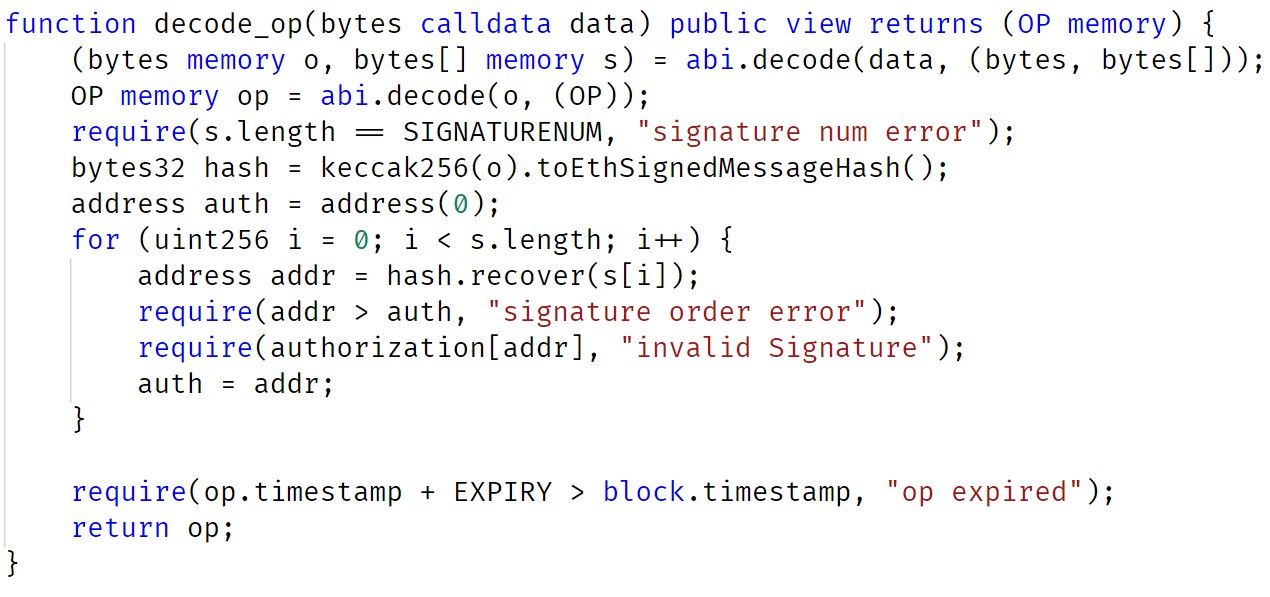
从decode_op的实现来看,参数中存在三个签名。在执行代币兑换(销毁和铸造)之前,需要对这些签名进行检查(和授权)。
总而言之,swap函数的第一个参数ns定义了要兑换的代币数量。第二个参数包含需要验证的签名。当验证通过后,兑换的代币数量由第一个参数(ns)定义。
攻击分析
在攻击交易0x81e5f715中,攻击者构造了一个包含有效签名的消息,并传递了一个精心构造的ns参数(其中包含大量zUSD)。结果,攻击者使用300 REI兑换了70万zUSD。
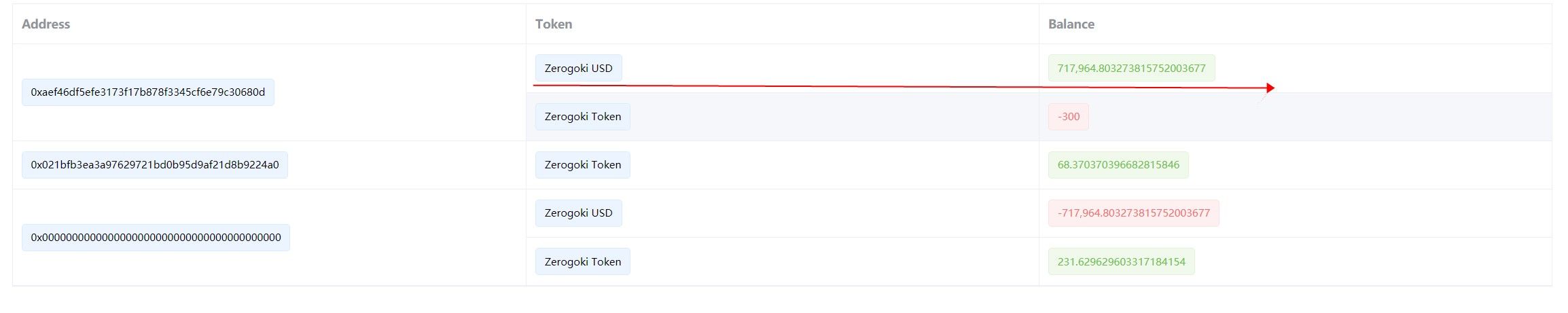
与签名相关的三个地址是:
0x0d93A21b4A971dF713CfC057e43F5D230E76261C
0x3054e19707447800f0666ba274a249fc9a67aa4a
0x4448993f493b1d8d9ed51f22f1d30b9b4377dfd2然而,在现阶段,我们没有关于这些地址私钥泄露原因的信息。
启示
使DeFi项目安全并非易事。除了代码审计,我们认为社区应该采取积极主动的方法来监控项目状态,并在攻击发生之前就将其阻止。
关于BlockSec
BlockSec是一家开创性的区块链安全公司,由一群全球知名的安全专家于2021年创立。公司致力于提升新兴Web3世界的安全性和可用性,以促进其大规模采用。为此,BlockSec提供智能合约和EVM链安全审计服务、用于安全开发和主动阻止威胁的Phalcon平台、用于资金追踪和调查的MetaSleuth平台,以及供Web3构建者在加密世界高效冲浪的MetaSuites扩展。
迄今为止,公司已为MetaMask、Uniswap Foundation、Compound、Forta和PancakeSwap等300多家知名客户提供服务,并通过两轮融资从Matrix Partners、Vitalbridge Capital和Fenbushi Capital等顶尖投资者那里获得了数千万美元的投资。
官方Twitter账号:https://twitter.com/BlockSecTeam




