2020年11月30日,我们的安全事件监控系统ThunderForecast通过扫描以太坊上的历史交易,发现Loopring协议遭受攻击(中文博客CN)。结论是,此次攻击的根本原因在于sellTokenForLRC函数缺乏访问控制。攻击者利用了80.97个ETH,按当时价格计算,相当于48,849.2美元。
2020年12月11日,我们的监控系统ThunderForecast报告了一系列交易异常的交易。随后,我们使用我们研究团队开发的EthScope系统分析了这些交易,并发现这是一起利用Seal Finance Protocol漏洞进行套利的攻击。
什么是Seal?
Seal在白皮书中提到:“SEAL——一个实验性协议,作为主要DeFi协议代币之间的中介,在它们之间创造更深层次的流动性。”截至目前,存在超过10个流动性池将Seal与其他不同的知名代币(如UNI、YFI、USDT、SNX等)连接起来。为了获得奖励,投资者需要将LP代币存入SEAL奖励合约,并触发Farm合约中的breed()函数来生成新的SEAL代币。Farm合约部署在每个Seal池中,该合约中的breed()函数用于发行新的Seal代币。根据breed()的设置,它额外发行1.6%的Seal Token。此外,0.8%的已发行Seal代币会兑换成另一种存入该池的代币,与另外0.8%的已发行Seal代币作为流动性。然而,由于breed()函数没有设计访问控制,任何人都可以触发该函数,而这个原始设计成为了此次报告攻击的根本原因。
以下是breed()函数的已确认源代码:
function breed() external {
require(now / 1 days > today);
today += 1;
uint256 sealPairAmount = seal.balanceOf(address(cSeal));
uint256 tokenPairAmount = token.balanceOf(address(cSeal));
uint256 newSeal = sealPairAmount.mul(spawnRate).div(1e18);
uint256 amount = UniswapV2Library.getAmountOut(newSeal, sealPairAmount, tokenPairAmount);
seal.mint(address(cSeal), newSeal);
if(address(seal) < address(token))
cSeal.swap(0, amount, address(this), "");
else
cSeal.swap(amount, 0, address(this), "");
token.transfer(address(cSeal), amount);
seal.mint(address(cSeal), newSeal);
cSeal.mint(address(this));
}详情
我们现在开始披露此次攻击的更多细节,其中一次攻击交易。在此次交易中,攻击者在10个Seal池中重复了攻击逻辑,以最大化其利润。在接下来的分析中,我们将重点关注在Seal-SNX池中发起的攻击。
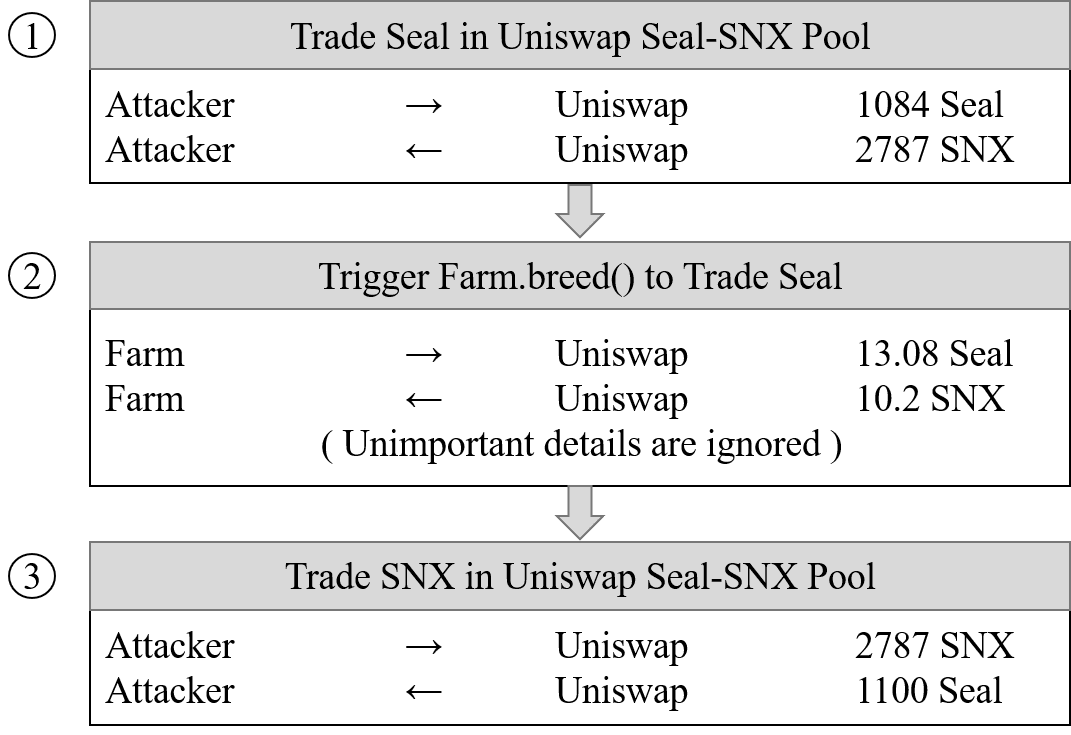
攻击涉及三个步骤:
- 步骤1:在Seal-SNX池中将1,084个Seal兑换为2,787个SNX。交易汇率为:1 Seal = 2.57 SNX。
- 步骤2:触发
Farm合约中的breed()函数。此函数发行13.08个Seal并将其兑换为10.20个SNX。交易汇率变为:1 SNX = 0.78 Seal。原因是池中大部分SNX已兑换成Seal,导致SNX和Seal的数量之间存在巨大差异。然后,根据Uniswap的价格计算算法,SNX在池中变得极其有价值(价格上涨超过3倍)。 - 步骤3:在Seal-SNX池中将2787个SNX兑换为1100个Seal。由于此次兑换进一步推高了SNX的价格,攻击者套利出更多的Seal代币(额外16个Seal)。
为了进一步衡量和确认损失,我们使用我们的EthScope系统在攻击前的区块状态下重放了breed()函数。结果显示,与正常调用相比,Farm发行了18个额外的Seal代币。攻击者取出了16个Seal,池中仅剩下2个Seal。
收益与损失
在此次交易中,攻击者总共获得了175个Seal。
攻击规模
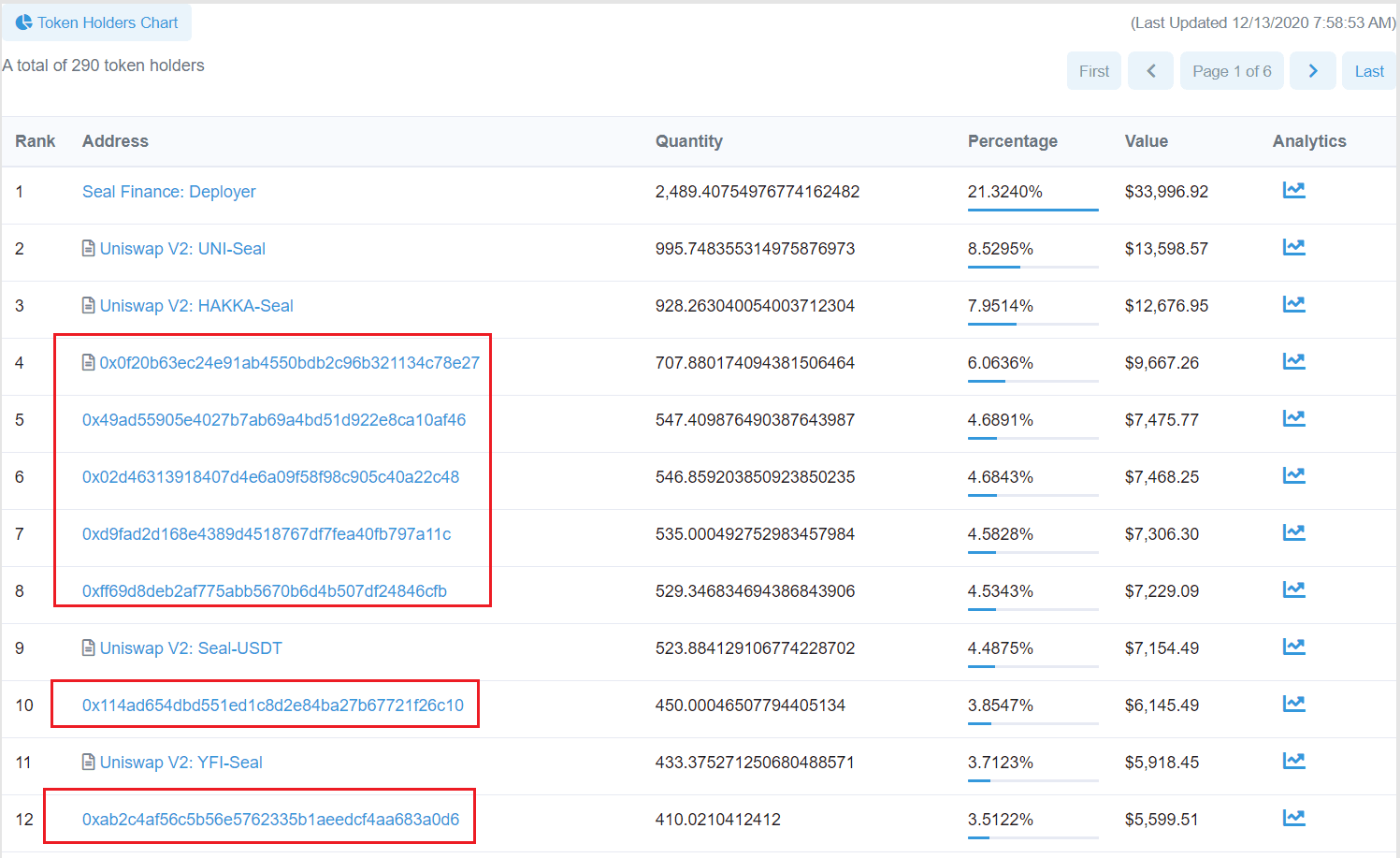
截至2020年12月13日,链上部署了3个恶意合约(0x49f93e、0x8b3710、0x0f20b6),并成功发起了22笔交易,共计4,247枚Seal代币。按当时价格计算,攻击者通过利用Seal协议的漏洞获得了约58,467美元。值得注意的是,Seal协议的漏洞仍在被攻击中!!!
此外,通过分析获得的Seal代币的流动,我们发现约有900枚Seal代币被存入DEX,其余的则分配到6个不同的地址。如下图所示,除Seal Finance和Uniswap V2中的流动性池外,这些地址都是Seal代币的顶级持有者。
结语
随着以太坊DeFi生态系统的发展,各种安全问题逐渐显现。事实上,此次攻击的根本原因——访问控制——导致Seal在截至2020年12月13日的22笔交易中遭受了相当大的损失(58,467美元)。
更新(2021/01/04)
在2020年11月30日首次攻击后,攻击者又部署了一个第三方攻击合约并发起了五次攻击。最后一次攻击发生在2020年12月24日,并将获得的Seal代币转账到了该地址。在此过程中,攻击者获得了6,021枚Seal代币。
时间线:
- 2020/12/11:发现可疑交易
- 2020/12/12:完成分析
- 2020/12/13:报告给Seal Finance
- 2021/01/03:发布细节
- 2021/01/03:分配CVE-2021–3006
关于BlockSec
BlockSec是一家开创性的区块链安全公司,由一群享誉全球的安全专家于2021年创立。公司致力于提升新兴Web3世界的安全性和可用性,以促进其大规模采用。为此,BlockSec提供智能合约和EVM链安全审计服务、用于安全开发和主动阻止威胁的Phalcon平台、用于资金追踪和调查的MetaSleuth平台,以及供Web3开发者在加密世界高效冲浪的MetaSuites扩展。
截至目前,该公司已为MetaMask、Uniswap Foundation、Compound、Forta和PancakeSwap等300多家知名客户提供服务,并在两轮融资中从Matrix Partners、Vitalbridge Capital和Fenbushi Capital等知名投资者那里获得了数千万美元。
官方Twitter账号:https://twitter.com/BlockSecTeam




