我们很高兴地宣布,我们的攻击监控和拦截平台 Phalcon 现在支持 Mantle Network,为 Mantle 生态系统在上线后阶段确保无黑客攻击的安全。
Phalcon:将 Mantle 生态系统安全性提升到新高度
代码审计可显著增强协议的安全性。然而,一旦 DeFi 协议上线,它就会面临许多风险,包括外部依赖、零日攻击和未经审计的智能合约升级。认识到这些风险,越来越多的区块链意识到仅靠代码审计是不足够的。因此,它们正在采取积极的防御措施来保护其生态系统在上线后的安全。
目前,大多数上线后安全解决方案都依赖于攻击监控平台。然而,在检测到攻击后,协议团队通常需要进行多方讨论并手动授权响应,这往往为时已晚。
我们的攻击监控和拦截平台 Phalcon 现在支持 Mantle,为整个 Mantle 生态系统提供强大的安全保障。Phalcon 是全球首个也是唯一一个不仅监控攻击,还能自动拦截攻击的平台。此功能已经过实战检验,成功 拦截了超过 20 起黑客攻击,挽救了超过 2000 万美元的资产。

Phalcon 如何赋能 Mantle 生态系统
-
对于生态系统: Mantle 可以部署监控 Mantle Network 上的协议,从而立即检测到任何可疑活动并通知协议团队进行响应。
-
对于协议: Mantle 上的协议可以使用 Phalcon 监控攻击,并在检测到攻击时自动暂停协议。此外,协议运营商还可以利用 Phalcon 监控敏感操作,例如管理员密钥更改、角色授予、关键变量等。
-
对于 LP: 流动性提供者可以在其投资的协议被黑客攻击时收到通知。同时,系统将自动提取资金以最大限度地减少潜在损失。
Phalcon 是一个 SaaS 平台,用户登录后即可直接 查看价格并订阅。 我们还邀请您与我们的安全专家 预约演示,详细了解 Phalcon 如何保护您的协议或资产。
Phalcon 内置工具,提供卓越的安全性和易用性
为了让项目团队更轻松地了解每次触发的交易情况,我们将 Phalcon Explorer 集成到 Phalcon 中,用户可以无缝切换到 Phalcon Explorer 查看交易的调用流程、余额变化、资金流等详细信息。
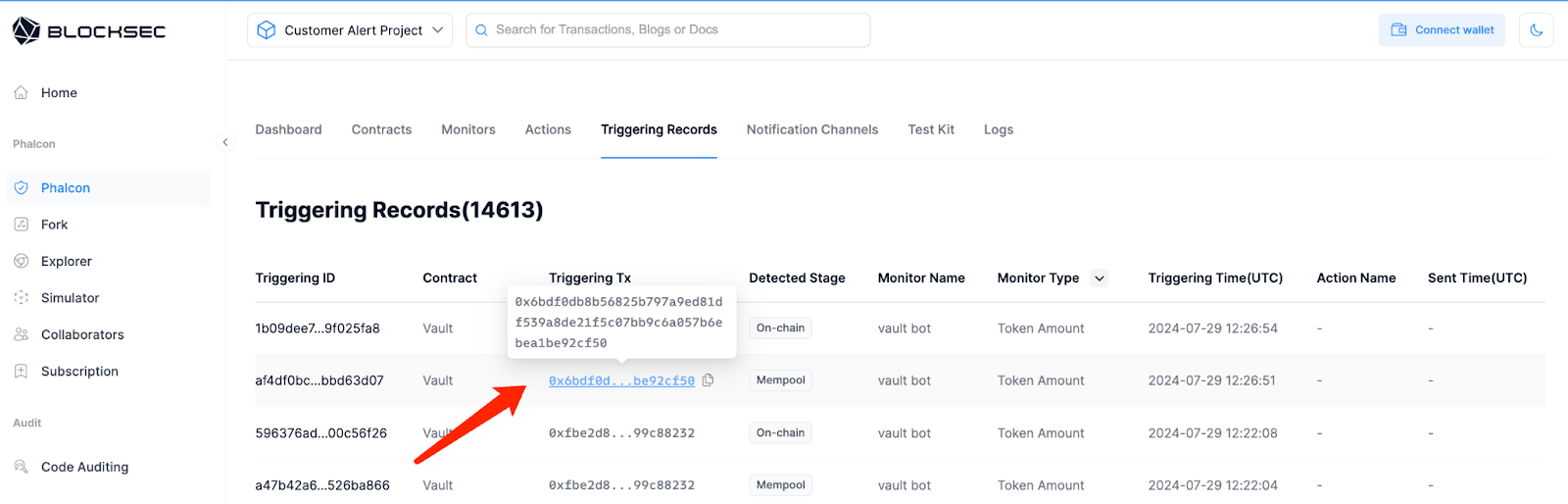
点击触发交易:
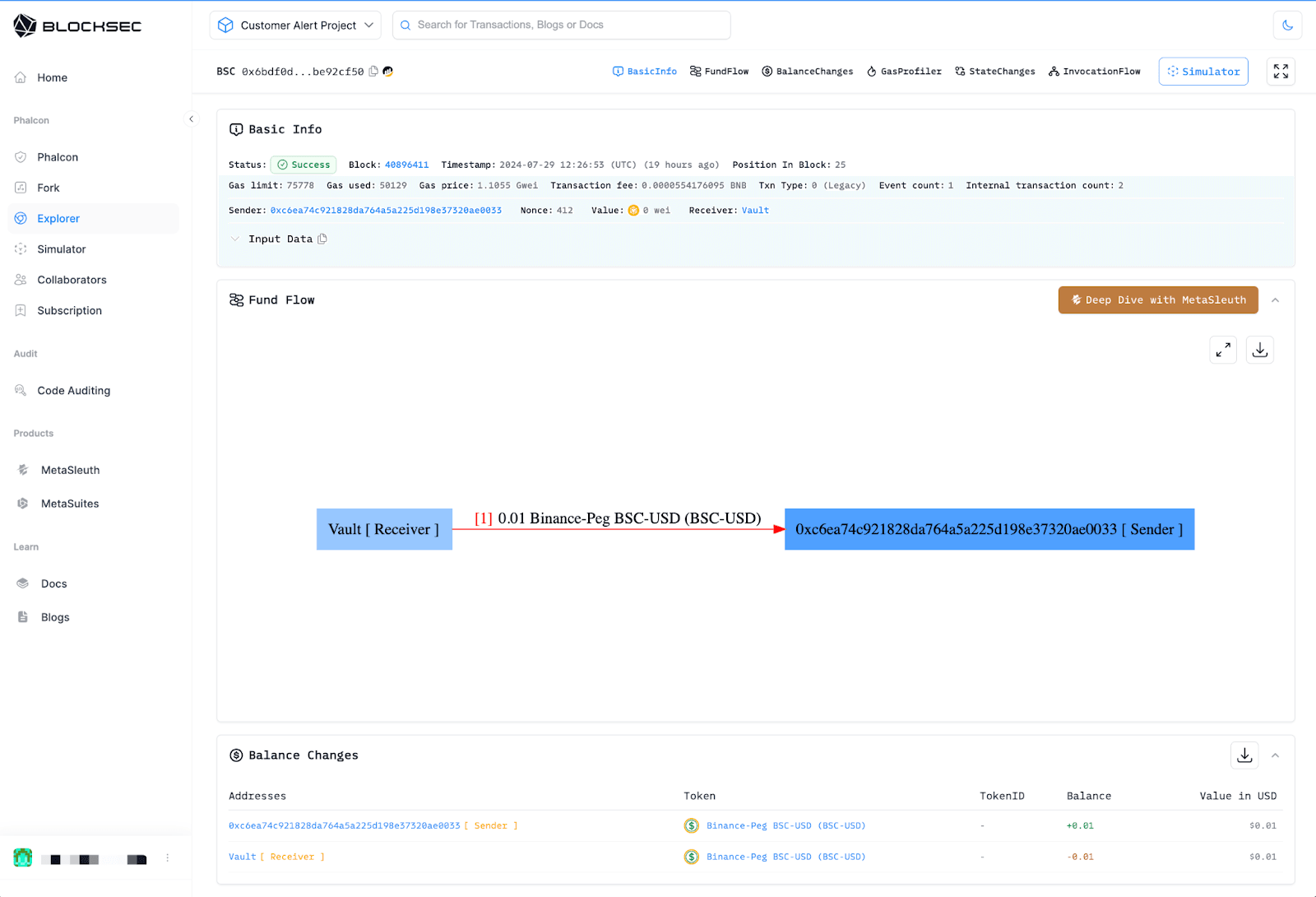
然后 跳转到 Phalcon Explorer 上的交易页面:
结论
Phalcon 的使命是通过我们最先进的攻击监控和拦截平台,提供无与伦比的生态系统安全性。通过支持 Mantle Network,我们为其生态系统参与者提供无与伦比的保护,有效抵御潜在威胁。我们经过实战检验的解决方案已成功阻止了多次真实世界的黑客攻击,彰显了我们的有效性。展望未来,此次合作将继续推动创新,并在区块链安全领域树立新的标杆。



