2021年1月2日(北京时间07:25),我们的监控系统ThunderForecast报告了一系列针对yCREDIT智能合约的可疑交易。随后,我们使用研究团队开发的EthScope系统分析了这些交易,并确认所有报告的交易都是恶意的。在本篇博文中,我们将详细说明攻击细节。
详情
此次攻击是由于铸造的代币数量与预期不符。因此,攻击者可以以较低的价格获得更多的yCREDIT代币。然后,这些代币可以被出售以获利。
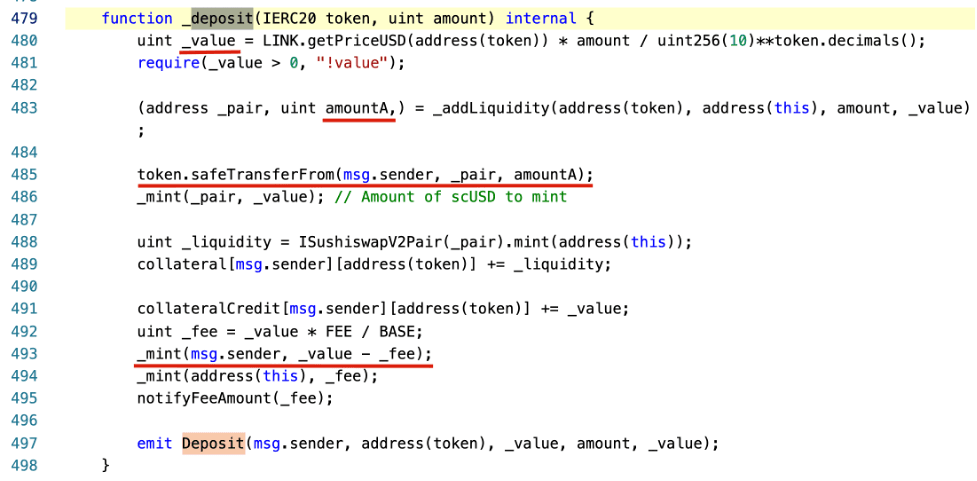
易受攻击的函数位于StableYieldCredit合约的_deposit函数中。
下面,我们将使用一个攻击交易来演示整个过程。
攻击者首先向WBTC-yCREDIT交易对池转入了1e-8 WBTC和331.335 yCredit代币。然后,攻击者向StableYieldCredit合约存入了0.5 WBTC以发动攻击。
具体来说,_value是根据ChainLink价格预言机(在第480行,_value为1466786010075)基于token(0x2260fac5e5542a773aa44fbcfedf7c193bc2c599 - WBTC)的amount(0.5)计算得出的。目的是计算存入的WBTC以美元计的价值。然后,合约会将yCREDIT代币的数量(_value - fee)转给存入WBTC的人(攻击者)。这是因为yCREDIT的价值等于一美元(由系统设计)。除了攻击者损失少量fee之外,一切都正常。
此外,合约会将存入的WBTC添加到WBTC-yCREDIT交易对池中。这是因为如果存入的WBTC被锁定在合约中,它将失去流动性。因此,它首先计算将被放入池中的代币对(WBTC到yCREDIT)的价值。这个价值是通过_addLiquidity函数计算的。基本上,它是基于池中现有的储备来计算的。由于池中只有1e-8 WBTC和331.335 yCREDIT代币,计算出的amountA为44(amountB为1466786010075)。这意味着攻击者只花费了44e-8 WBTC(第485行),并获得了14667.86010075 - fee = 14594.52080025 yCREDIT代币(第493行)。同时,池中留下了少量WBTC(1e-8 + 44e-8)和(331.335 + 14667.86010075)yCREDIT代币。
为了获利,攻击者可以简单地在交易所交易获得的14594.52080025 yCREDIT代币。有趣的是,在此交易中获利的过程比必要的要复杂得多。我们也在其他交易中观察到了巧妙的攻击策略。
此次攻击涉及一系列交易,包括(但不限于)以下交易。
更新
2020/01/03:已发布一个新智能合约来修复此漏洞。
时间线
- 2021/01/01 23:25 UTC,攻击被我们的系统捕获
- 2021/01/02 16:20 UTC,发布此博文




