Brief Summary
On March 15, 2026, an attacker bypassed the THE (Thena) market's supply cap on Venus Protocol's Core Pool (BNB Chain), inflated a collateral position to 3.67x the intended limit, and extracted borrowed assets. Early media reports estimated total losses at $3.7M; our on-chain analysis across all three extraction transactions also confirms $5.77M in total extracted value and $2.15M in protocol bad debt [3].
Several analyses [1, 2, 3] and Venus's own statement [5] have already dissected the attack mechanism, including the supply cap bypass, the donation vector, and the fund flow. This article does not revisit those findings in detail. Instead, it focuses on what the complete on-chain data reveals about the risk assumptions that lending protocols rely on, and the lessons the DeFi community can draw from this incident.
Two data points deserve closer examination. First, the attacker's full P&L: approximately $9.16M was spent acquiring THE and vTHE over nine months, $5.77M was extracted from Venus, and the attacker remains $4.15M in the red on-chain. Second, the liquidation record: 254 distinct bots competed across 8,048 transactions to unwind the position, yet $2.15M in bad debt still accumulated because 53M THE could not be sold into a market with only a few million dollars of depth.
These data points challenge a common assumption in DeFi lending: that overcollateralization plus competitive liquidation markets will keep protocols solvent. In this case, the position was nominally 3.67x overcollateralized, and the liquidation market showed up in force. Neither was sufficient when the collateral lacked real liquidity.
Background
Supply caps are a standard risk control in Compound-style lending markets. They limit how much of a given asset can be deposited as collateral, providing a ceiling on the protocol's exposure to volatile or low-liquidity tokens. Venus set a supply cap of 14.5M THE for its THE market, reflecting the token's thin on-chain liquidity.
Behind the supply cap sit two additional safety layers. Oracle-based collateral valuation determines how much a borrower can draw against their deposits. If a position becomes undercollateralized, a competitive liquidation market is expected to step in: third-party bots repay the debt and seize collateral at a discount, keeping the protocol solvent.
This three-layer structure (exposure limits, valuation, liquidation) forms the risk framework for most lending protocols. The Venus THE incident tested all three layers simultaneously, and all three proved insufficient. The following sections trace how each layer was breached in sequence.
The Attack
The Bypass: Donation Attack
Supply caps in most Compound forks only constrain the mint path: the standard deposit function that checks the cap before issuing vTokens. They do not account for tokens transferred directly to the contract address.
The attacker exploited this gap. A direct ERC-20 transfer to the vTHE contract increases the contract's underlying token balance without minting new vTokens. In Compound-style accounting, this inflates the exchangeRate between vTokens and the underlying asset. Any existing vToken holder benefits: their vTokens now represent a claim on more underlying tokens, increasing their effective collateral value as seen by the protocol.
This "donation attack" is a known class of vulnerability in Compound forks. Any protocol that enforces supply caps only on the mint path is susceptible.
Preparation (June 2025 to March 2026)
The attack did not begin on March 15. The attacker received 7,400 ETH through Tornado Cash via a funding address (0x7a79...f234), deposited the ETH into Aave as collateral, and borrowed $9.92M in stablecoins (USDT, DAI, USDC). These funds were distributed across multiple wallets to purchase THE starting in June 2025, gradually building a combined position that reached 84% of the supply cap (approximately 12.2M THE) by the morning of the attack.
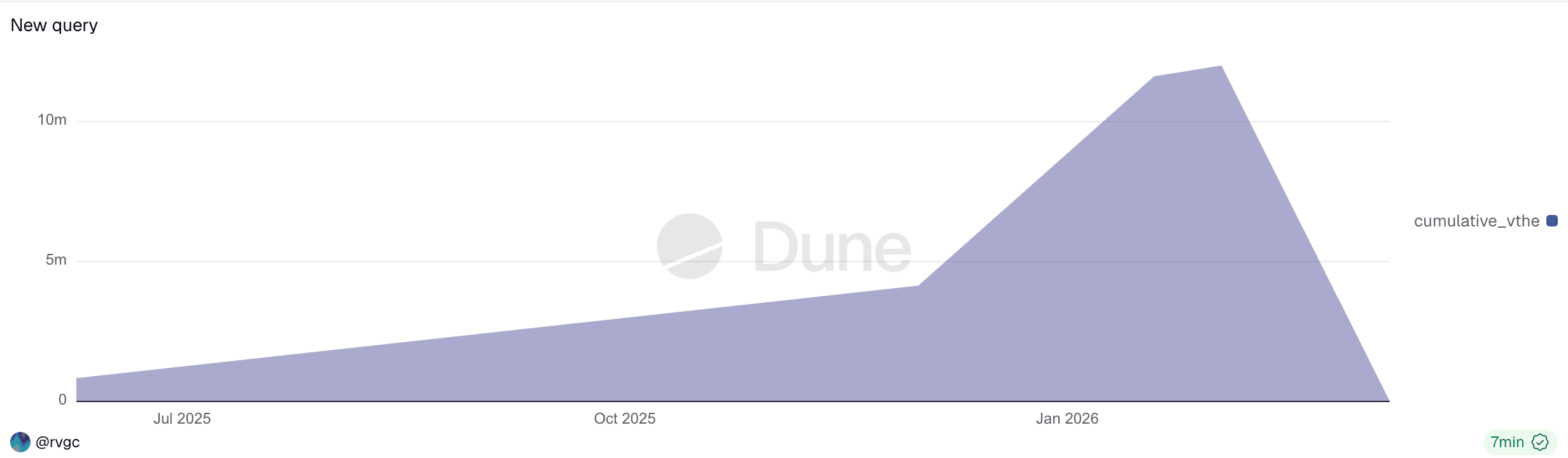
This nine-month preparation period was visible on-chain the entire time. The growing concentration of a single entity approaching the supply cap was a detectable risk signal that traditional transaction-level monitoring would miss.
The attacker operated through multiple addresses, all traceable to a single Tornado Cash funding source:
| Address | Role |
|---|---|
| 0x7a79...f234 | Funding: received 7,400 ETH from Tornado Cash, deposited into Aave, borrowed $9.92M in stablecoins |
| 0x43c7...2f82 | Attacker EOA |
| 0x737b...a619 | Attack contract: donated ~36.1M THE via transferFrom(), pre-supplied 1.58M USDC as collateral, borrowed 4.63M THE for donation, executed donation bypass, received borrowed assets. Liquidated at 12:04 UTC. |
| 0x1a35...6231 | Attacker wallet: supplied THE via mint path, held vTHE |
Execution (March 15, 11:00-12:42 UTC)
The following analysis is based on three attack transactions:
At 11:00 UTC, the attacker held 12.2M THE within the protocol, still within the 14.5M cap. Over the next two hours, they executed the donation bypass and a recursive leverage loop:
- Directly transfer
THEtokens to thevTHEcontract (bypassing the supply cap) - Borrow assets against the inflated collateral (
CAKE,BNB,BTCB,USDC) - Use borrowed assets to buy more
THEon the open market - Wait for the TWAP oracle to update to reflect the higher price
- Repeat with increased borrowing power
| Time (UTC) | THE Supplied |
% of Cap | Status |
|---|---|---|---|
| 11:00 | 12.2M | 84% | Within cap |
| 12:00 | 49.5M | 341% | Cap bypassed |
| 12:42 | 53.2M | 367% | Peak position |
Timeline data sourced from AllezLabs [1].
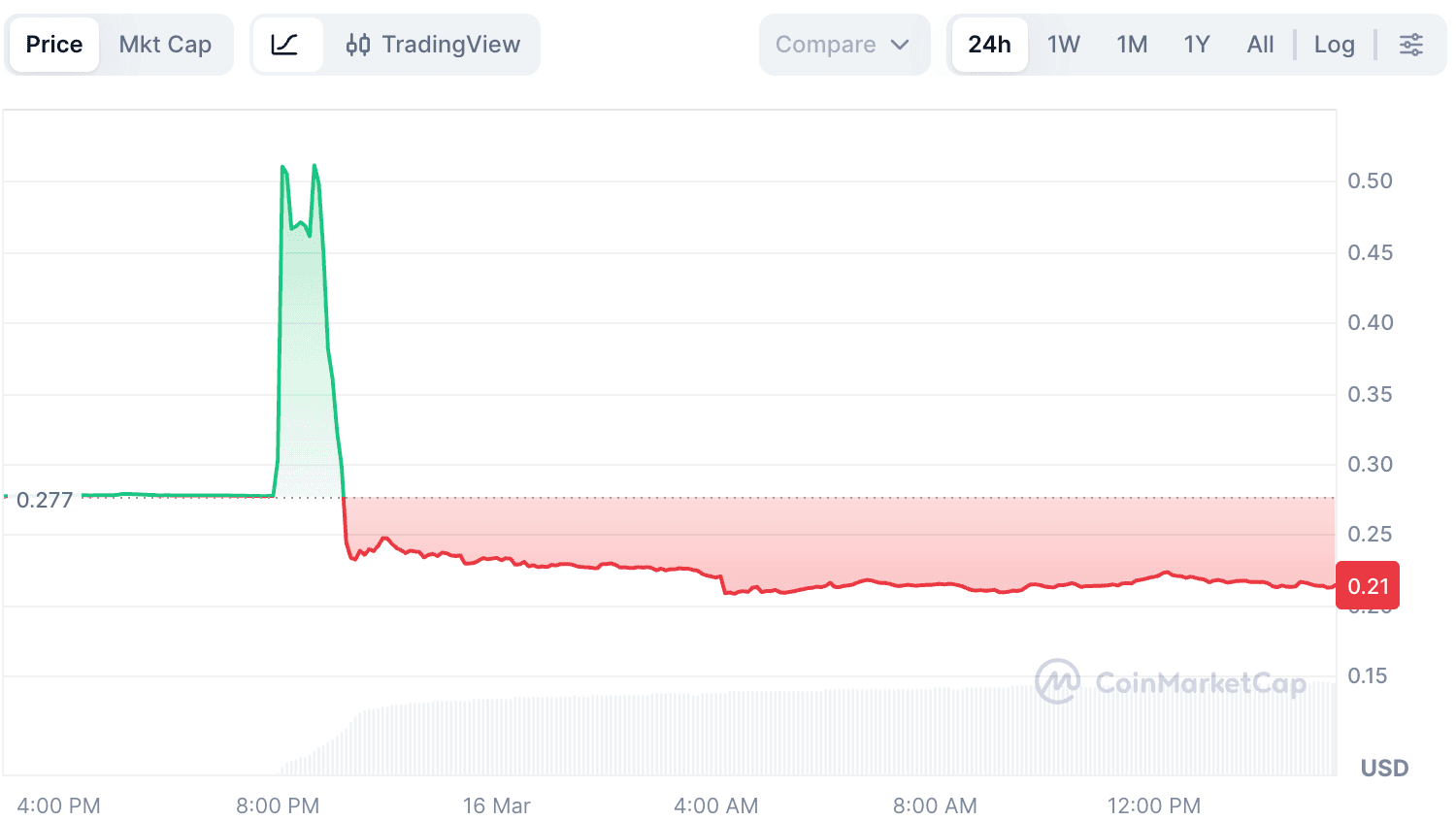
Because THE had extremely thin on-chain liquidity, even modest purchases caused significant price impact. THE's aggregated market price surged from approximately $0.27 to over $0.53 (per CoinMarketCap), with DEX spot prices likely spiking even higher on individual trades due to thin liquidity. Venus's TWAP oracle updated to approximately $0.53, giving the attacker progressively more borrowing capacity with each cycle.
The system valued this collateral at roughly $30M. This valuation was based on oracle prices, not on what the market could actually absorb. THE's real market depth was a fraction of this nominal value.
Overextension and Collapse
After extracting the first round of borrowed assets, the attacker could have stopped. Instead, they continued deploying borrowed funds to buy more THE, attempting to force another price leg up. This pushed the health factor to ~1.
Once liquidation started, 53M THE hit a market with no depth. THE's price collapsed to approximately $0.21, well below the pre-attack level of $0.27. At this point, the protocol's last line of defense was supposed to activate: third-party liquidators stepping in to unwind the position and limit losses.
The Liquidation Reality
In DeFi lending, the assumption is straightforward: when positions go underwater, third-party liquidators step in, repay the debt, seize the collateral at a discount, and keep the protocol solvent. The Venus THE incident did not break this mechanism. It exposed its limits.
They Came. It Was Not Enough.
On-chain liquidation data (sourced from Venus's Dune dashboard [4], with additional transaction-level analysis) reveals:
| Metric | Value |
|---|---|
Total liquidation transactions (vTHE, Mar 15) |
8,048 |
| Unique liquidation callers | 254 |
| Liquidation entry contract | 0x0870...cf43 (Venus Core Pool Liquidator) |
| Total debt repaid | ~$14.2M |
| Remaining bad debt | $2.15M |
An initial reading of the Dune dashboard suggested that Venus's own contract was the sole liquidator. This was misleading. 0x0870...cf43 is Venus's Core Pool Liquidator contract, a permissionless entry point through which any external caller can execute liquidations. Querying the actual transaction senders reveals 254 distinct addresses competing for liquidation opportunities across 8,048 transactions. The liquidation market showed up in force.
Of the 8,048 vTHE liquidation transactions, 8,039 targeted the attacker's main position (0x1a35); the remaining 9 liquidated four unrelated users with small vTHE holdings who were caught in the price collapse.
Participation did not translate into recovery. The bots repaid approximately $14.2M in debt (BNB, BTC, CAKE, USDC, WBNB) and seized vTHE in return. To realize any profit, they needed to sell that THE on the open market. With 53M THE having just been dumped into a market with only a few million dollars of depth, the seized collateral could not be converted to stable value without massive slippage. The result: $2.15M in debt could not be covered, becoming bad debt on Venus's balance sheet.
Two Positions, Two Outcomes
The attacker operated two positions with different collateral types [1]. Their liquidation outcomes were strikingly different:
| Address | Collateral | Txs | Debt Repaid | Outcome |
|---|---|---|---|---|
| 0x1a35 (attacker wallet) | vTHE |
8,039 | ~$14.2M | $2.15M bad debt (seized THE illiquid) |
| 0x737b (attack contract) | vUSDC |
603 | $729K | Clean recovery (seized 1.58M USDC) |
The 0x737b position was liquidated early (12:04 UTC) because its collateral was 1.58M USDC while its debt was denominated in THE, which was rapidly appreciating. As THE's price surged during the manipulation phase, the value of 0x737b's THE debt exceeded its USDC collateral, triggering liquidation. This was likely by design: 0x737b's purpose was to borrow THE for the donation bypass, and once that mission was complete, losing the USDC collateral was an acceptable cost. From Venus's perspective, this liquidation was clean: USDC is liquid and stable, so the protocol recovered more than it repaid.
The 0x1a35 liquidation tells the real story. Its collateral was THE itself. 254 bots competed to liquidate it across 8,039 transactions, but the seized THE could not be sold at anything close to its oracle-reported value. The timeline shows the dynamic:
| Hour (UTC) | Txs | Debt Repaid | Phase |
|---|---|---|---|
| 12:00 | 3,416 | ~$3.83M | THE price collapsing, heaviest slippage |
| 13:00 | 4,626 | ~$10.40M | Price stabilizing, bulk of liquidation |
All bad debt originated from this THE-collateralized position. The total debt on 0x1a35 was approximately $16.4M (repaid + bad debt). Liquidators managed to cover ~87% of it. The remaining ~13%, or $2.15M, became protocol losses.
A note on Dune valuation: The Venus Dune dashboard [4] values seized collateral using daily snapshot prices from its
daily_market_infotable. BecauseTHE's price crashed intraday from ~$0.53 to $0.21, this methodology significantly understates the value ofTHEseized during the earlier, higher-priced liquidation window. The actual bad debt, i.e., the outstanding debt that could not be covered after all liquidations completed, is approximately $2.15M [3], a more reliable figure than the raw Dune USD gap.
Following the Money
The liquidation data shows how the position was unwound, but does not answer who actually profited from this incident. Tracing the full fund flow reveals a picture that contradicts the standard "theft" narrative.
Some media coverage described this as a "$3.7M exploit," likely counting only a subset of the borrowed assets. Early analyses focused on the THE-collateralized position (0x1a35) but overlooked the attack contract's separate USDC-collateralized position (0x737b), leading to incomplete accounting. On-chain tracing across all three extraction transactions totals $5.77M.
Attacker's On-Chain P&L
Cost side:
The attacker's funding chain: 7,400 ETH received via Tornado Cash, deposited into Aave as collateral, borrowed $9.92M in stablecoins (USDT, DAI, USDC), and distributed to multiple wallets to acquire THE and vTHE.
| Item | Amount | USD Value | Notes |
|---|---|---|---|
| Aave collateral | 7,400 ETH |
~$14M+ | Deposited from Tornado Cash |
| Aave borrowing | USDT + DAI + USDC |
$9.92M | Secured against ETH collateral |
THE acquisition |
~36.1M THE |
~$6.49M | Avg purchase price ~$0.17 over 9 months |
vTHE acquisition |
~12.1M vTHE |
~$2.67M | Purchased and held by 0x1a35 |
The total deployment ($6.49M + $2.67M = $9.16M) accounts for most of the $9.92M Aave borrowing. The Aave position (7,400 ETH collateral, ~$9.92M debt) remains open; the attacker retains access to the ETH minus outstanding debt.
Revenue side (extracted from Venus in 3 transactions):
| Tx | Assets Received by Attack Contract (0x737b) | USD Value |
|---|---|---|
| 0x4f477e...5663f | 60M vUSDC + 913,858 CAKE + 1,972.53 WBNB |
$4,189,131 |
| 0x4253a8...ca296 | 1,044,003 CAKE |
$1,460,264 |
| 0xfd64d0...54808 | 95,164 CAKE |
$124,910 |
| Total | 2,053,025 CAKE + 1,972.53 WBNB + 60M vUSDC |
$5,774,305 |
Net on-chain P&L: negative. The attacker borrowed $9.92M from Aave and extracted $5.77M from Venus. Both Venus positions (contract 0x737b and wallet 0x1a35) were fully liquidated, leaving no residual on-chain value. The $4.15M gap remains as outstanding Aave debt. The attacker's 7,400 ETH collateral on Aave (~$14M+) can absorb this loss, but the on-chain operation was clearly unprofitable in isolation.
Protocol Losses
After all liquidations completed, Venus was left with approximately $2.15M in bad debt [3]:
| Asset | Amount | USD Value |
|---|---|---|
CAKE |
~1.18M | ~$1.65M |
THE |
~1.84M | ~$0.50M |
| Total bad debt | ~$2.15M |
Value Distribution
| Party | Net P&L | Notes |
|---|---|---|
| Attacker (on-chain) | -$4.15M | $9.92M borrowed, $5.77M extracted, $4.15M outstanding Aave debt |
| Third-party liquidators | Unknown | 254 bots participated; P&L depends on THE exit prices |
| Venus Protocol | -$2.15M | Bad debt after all liquidations completed |
| Attacker (CEX) | Unknown | Likely profited via perp positions |
In most DeFi exploits, the "missing value" between protocol losses and attacker gains is captured by liquidators and arbitrage traders. Here, 254 liquidation bots competed for the seized THE, but the token's destroyed liquidity meant the collateral could not be efficiently converted to stable value. Much of the value was destroyed rather than redistributed.
If the attacker profited, the most plausible mechanism is off-chain perpetual futures positions on centralized exchanges: long THE during the pump phase ($0.27 to over $0.53), then short THE before the liquidation cascade ($0.53 to $0.21 post-liquidation) [2, 3]. This CEX activity cannot be verified from on-chain data. The pattern of using on-chain manipulation as a loss leader for off-chain derivatives profit has been hypothesized in similar incidents, but remains difficult to confirm due to the opacity of centralized exchange activity. As DeFi-CEX interplay deepens and perpetual markets for long-tail tokens expand, this type of cross-venue attack could become an increasingly common vector.
Lessons: Three Lines of Defense
The attack exploited a known vulnerability, used a textbook leverage loop, and still caused $2.15M in bad debt. The real failure was not any single mechanism but the compounding effect of weaknesses across the entire risk stack.
First Line: Exposure Limits
Venus's supply cap only constrained the standard mint path. Direct token transfers to the vToken contract bypassed it entirely. Any risk control that relies on accounting assumptions must validate those assumptions across all possible state-changing operations, not just the expected deposit flow.
Second Line: Collateral Valuation
Oracle-reported collateral value can diverge sharply from what liquidators can actually realize [2]. This position had oracle-reported collateral of roughly $30M against ~$16M in debt, yet still produced $2.15M in bad debt, because $30M of THE on paper could only realize a fraction of that value in a market with a few million dollars of depth. For illiquid tokens, even a 3x collateral ratio provides no real safety margin. Lending protocols should incorporate liquidity-adjusted collateral valuation that accounts for market depth, expected slippage, and concentration risk.
Third Line: Liquidation
The entire lending model assumes that when positions go underwater, liquidators will step in and make the protocol whole. In this incident, 254 liquidation bots processed 8,048 transactions on the vTHE position alone. The liquidation market was active and competitive. It still was not enough: $2.15M in bad debt remained. The problem was not a lack of liquidators but a lack of liquidity. When 53M THE hit a market with only a few million dollars of depth, no amount of bot competition could convert the seized collateral into enough value to cover the outstanding debt. Protocols cannot treat liquidation as a reliable backstop when the collateral's realizable value diverges sharply from its oracle-reported value.
The Monitoring Gap
The nine-month accumulation phase was visible on-chain from the beginning: a single entity approaching the supply cap, increasing concentration in a low-liquidity asset, gradual position building over months. Venus has acknowledged that "some community members flagged this address prior to the exploit," but noted that "the address was operating entirely within protocol limits at the time" and that, as a permissionless protocol, "we cannot and should not freeze or blacklist addresses based on suspicion alone" [5]. As part of its remediation, Venus has stated that it is "exploring on-chain risk monitoring mechanisms that can flag anomalous accumulation patterns and trigger governance-level review" [5].
This points to a critical capability gap. Traditional transaction-level monitoring would not have caught this attack: no single transaction was malicious, and no rule was broken at any point during the nine-month buildup. What was needed is position-level trend detection: tracking how a single entity's concentration in a low-liquidity asset evolves over time relative to supply caps, market depth, and liquidation capacity. This requires continuous monitoring infrastructure that operates above the transaction layer, correlating on-chain state changes across addresses and time windows to surface systemic risk before it materializes.
References
- [1] AllezLabs, "Venus Protocol THE Incident Timeline": https://x.com/AllezLabs/status/2033239532355858536
- [2] hklst4r, "Venus THE Attack Analysis": https://x.com/hklst4r/status/2033192855443808515
- [3] EmberCN, "Venus THE Attacker Fund Flow": https://x.com/EmberCN/status/2033204517467308144
- [4] Venus Protocol Liquidation Dashboard (Dune): https://dune.com/xvslove_team/venus-liquidations
- [5] Venus Protocol, "$THE Market Incident: What We Know So Far": https://x.com/VenusProtocol/status/2033471885259034989



