We are pleased to announce that our attack monitoring and blocking platform, Phalcon, now supports Mantle Network, ensuring hack-free security for the Mantle Ecosystem at the post-launch stage.
Phalcon: Elevate Mantle Ecosystem Security to New Heights
Code audits significantly enhance the security of a protocol. However, once a DeFi protocol is live, it faces numerous risks, including external dependencies, zero-day attacks, and unaudited smart contract upgrades. Recognizing these risks, an increasing number of blockchains understand that code audits alone are insufficient. Consequently, they are adopting proactive defense measures to secure their ecosystems at the post-launch stage.
Currently, most post-launch security solutions rely on attack monitoring platforms. However, upon detecting an attack, protocol teams often need to engage in multi-party discussions and manually authorize responses, which often proves to be too late.
Our attack monitoring and blocking platform, Phalcon, now supports Mantle, offering robust security for the entire Mantle Ecosystem. Phalcon is the world’s first and only platform that not only monitors attacks but also automatically blocks them. This capability has been battle-tested, with a proven record of blocking over 20 hacks and rescuing over $20 million worth of assets.

How Phalcon Empowers Mantle Ecosystem
-
For the Ecosystem: Mantle can deploy monitoring for protocols on Mantle Network, allowing it to immediately detect any suspicious activity and inform protocol teams to take in response.
-
For Protocols: Protocols on Mantle can use Phalcon to monitor for attacks and automatically pause the protocol if an attack is detected. Additionally, protocol operators can leverage Phalcon to monitor sensitive operations such as changes to admin keys, role grants, key variables, and more.
-
For LPs: Liquidity providers can use Phalcon to receive notifications if their investment protocols are hacked. At the same time, the system will automatically withdraw funds to minimize potential losses.
Phalcon is a SaaS platform that allows users to check prices and subscribe directly after logging in. We also invite you to book a demo with our security experts to learn more about how Phalcon can protect your protocols or assets.
Phalcon's Inbuilt Tool for Superior Security and Usability
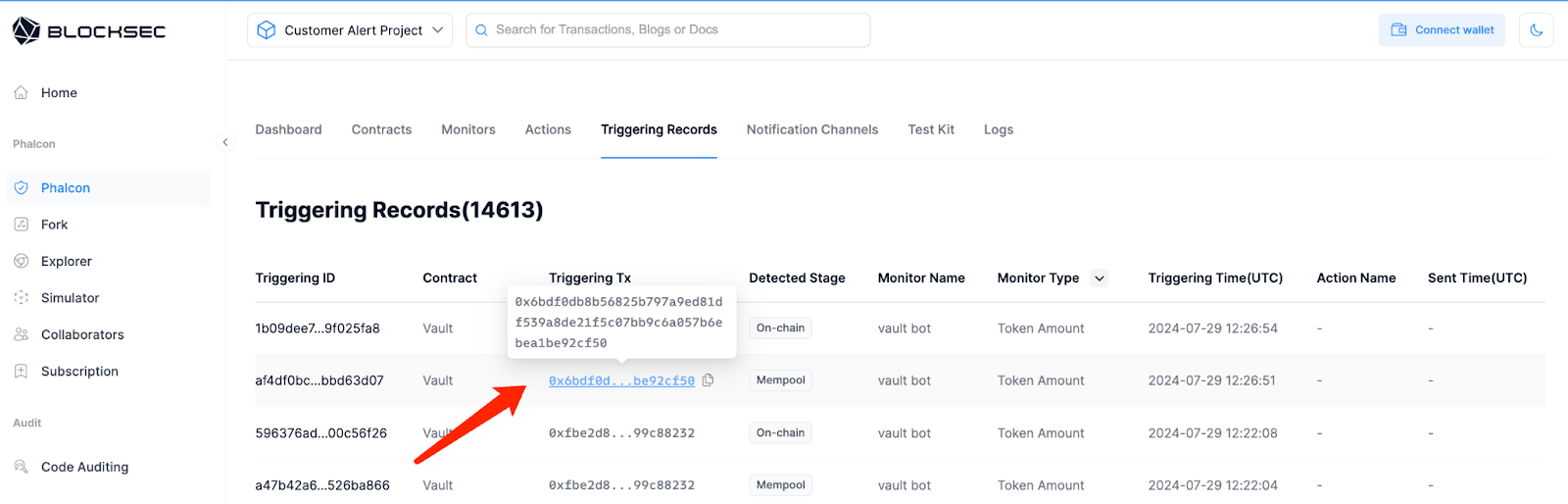
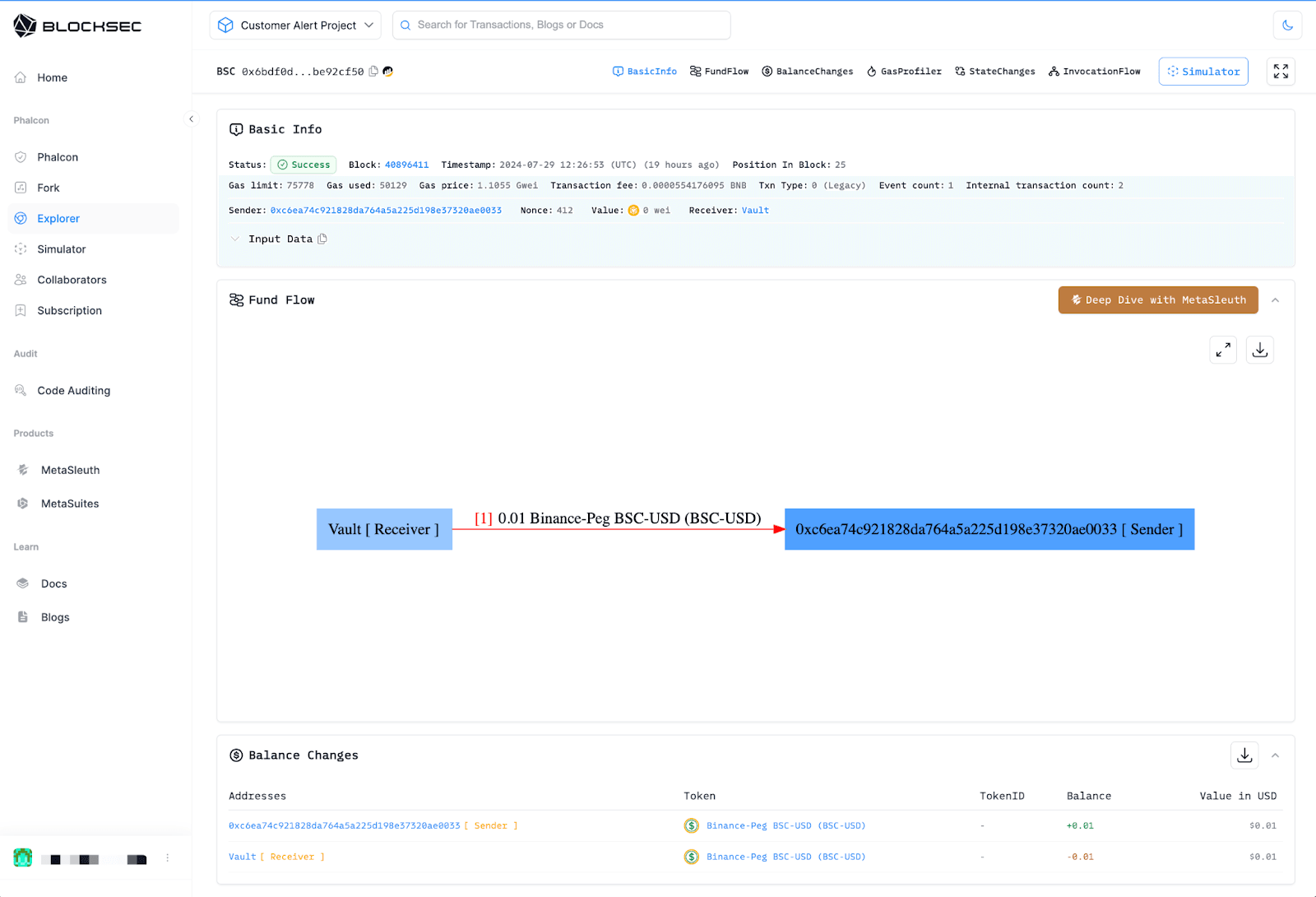
To make it easier for project teams to understand what happened with each triggered transaction, we have integrated Phalcon Explorer into Phalcon, which allows users to seamlessly switch to Phalcon Explorer to view the invocation flow, balance changes, fund flow, and other details of the transactions.
Click the triggering tx:
Then jump into the tx page on Phalcon Explorer:
Conclusion
Phalcon's mission is to deliver unmatched ecosystem security through our state-of-the-art attack monitoring and blocking platform. By supporting Mantle Network, we offer unparalleled protection to its ecosystem participants, effectively safeguarding them from potential threats. Our battle-tested solutions have successfully prevented numerous real-world hacks, underscoring our effectiveness. Looking ahead, this partnership is poised to continue innovating and setting new benchmarks in blockchain security.



