Security at a Glance 👀
DeFi Sector
- UwU Lend Hacks
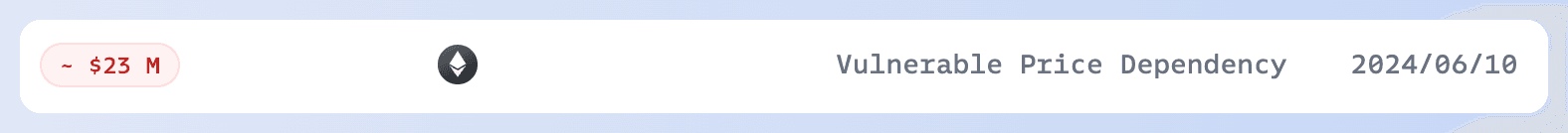
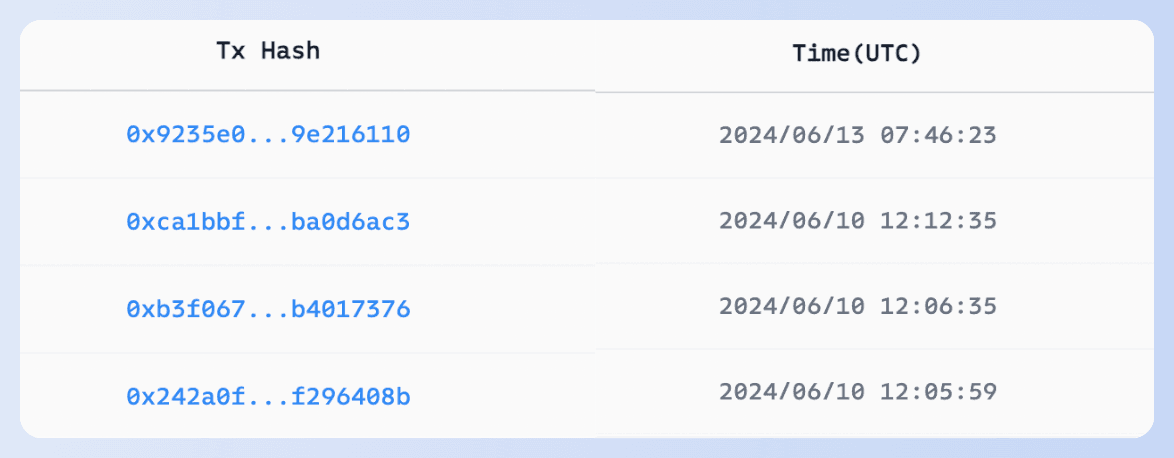
On June 10 and 13, UwU Lend suffered attacks resulting in losses exceeding $23M.
The root cause of the first attack was Vulnerable Price Dependency. The lending pool fetched prices from 11 sources, including 5 current (AMM) prices from Curve, 5 Curve oracle (EMA) prices, and one Uniswap (TWAP) price, ultimately taking the median. Since current prices could be manipulated within a single transaction, the attacker used a flash loan to drastically alter the 5 current prices, causing the fetched price to be the minimum or maximum of the oracle prices. This resulted in a loss of approximately $20M.
On June 13, the UwU Lend team restarted the protocol and got attacked again. The attacker added uSUSDe and WETH as collateral and then borrowed WETH based on the LTV. The uSUSDe did not participate in the LTV but did in the health factor calculation during liquidity withdrawal, allowing the attacker to withdraw more WETH and profit.
Notably, white hat makemake_kbo tweeted that he had reported the vulnerability a year ago and contacted the project team without a response, eventually issuing a warning on Twitter.
- Velocore Hack
Root Cause: A lack of check on effectiveFee1e9 led to an underflow in the velocore__execute function.
After the attack, Linea halted block production for 1 hour. For L2 projects, having an emergency response mechanism is more effective than pausing the entire chain. 👉 Learn about the world's first crypto hack monitoring and blocking platform here.
- Holograph Hack
Holograph announced that a former contractor exploited the protocol to mint additional HLG.
Many past attacks have shown that projects often compromise private key management for convenience. This exposes them to severe risks of internal and external attacks gaining admin permissions or private keys. Using Phalcon for external monitoring allows one-click operational monitoring, enabling early detection and loss minimization.
Other
- DMM Exchange Hack
In early June, DMM Exchange disclosed a security incident where 4,502.9 BTC (over $300M) were stolen on May 31 (UTC).
Without more details from DMM, the cause remains unknown. However, the hacker's address and DMM's normal address shared the same first five and last two characters, and the stolen BTC was from a multisig address. Speculation suggests an off-chain attack replaced the transfer address, deceiving personnel into signing the transaction. Use MetaSleuth to track the funds here.
- Kraken
On June 19, Kraken's Chief Security Officer, Nick Percoco, disclosed on X that they had received a report of an "extremely critical" vulnerability from a security company through their bug bounty program. The report claimed to have found a vulnerability that could artificially increase account balances. However, after Kraken fixed the vulnerability, they discovered some suspicious behavior during negotiations with the security company, involving $3 million. Nick Percoco's Post: View Post
CertiK later claimed responsibility for the matter on X, disclosed more information, and explained their actions. They emphasized that they had conducted multi-day tests on Kraken and had already returned the funds. This incident sparked intense discussion within the community.CertiK's Post: View Post Check out the root cause here and the sample transaction here.
- CoinStats
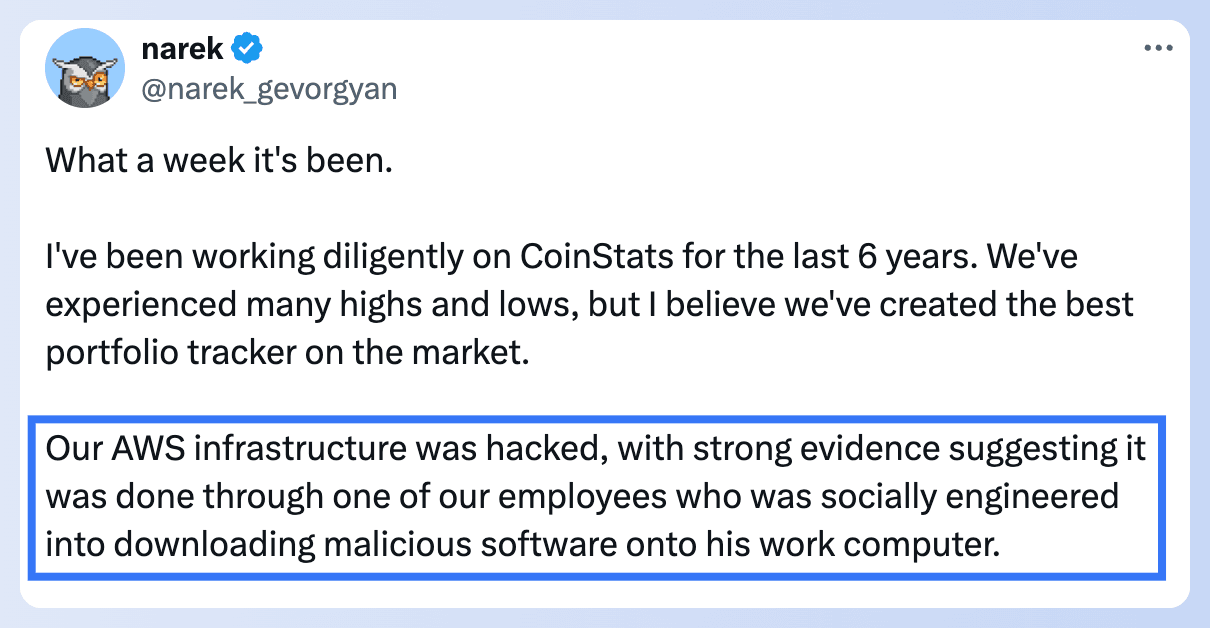
CoinStats suffered a $2 million loss in an attack. Their CEO stated that the breach was due to a social engineering attack on an employee, which compromised their AWS infrastructure. Click here to learn more
Blog Articles
BlockSec has curated the "Solana Simplified" series, which includes articles on Solana's basic concepts, tutorials on writing Solana smart contracts and guides for analyzing Solana transactions. The goal is to help readers understand the Solana ecosystem and master essential skills for developing projects and conducting transactions on Solana.
01: Master Solana Core Concepts in One Read
02: Writing Your First Solana Smart Contract from Scratch
03: Understand Solana Transactions in 5 Minutes
BlockSec X Solana Summit
From June 20 to June 22, BlockSec proudly presented at the 2024 Solana Summit APAC in KL. Looking forward to meeting you all at more global events in the future!
Phalcon Explorer now fully supports Solana!
Phalcon Explorer introduces new features to enhance the user and developer experience, including:
🚀 Clarified account relationships & token changes
🚀 MEV transaction tagging & 300M+ address labels
🚀 Accurate, clear function call hierarchies with expandable levels
Experience Phalcon Explorer here
Click here to learn more