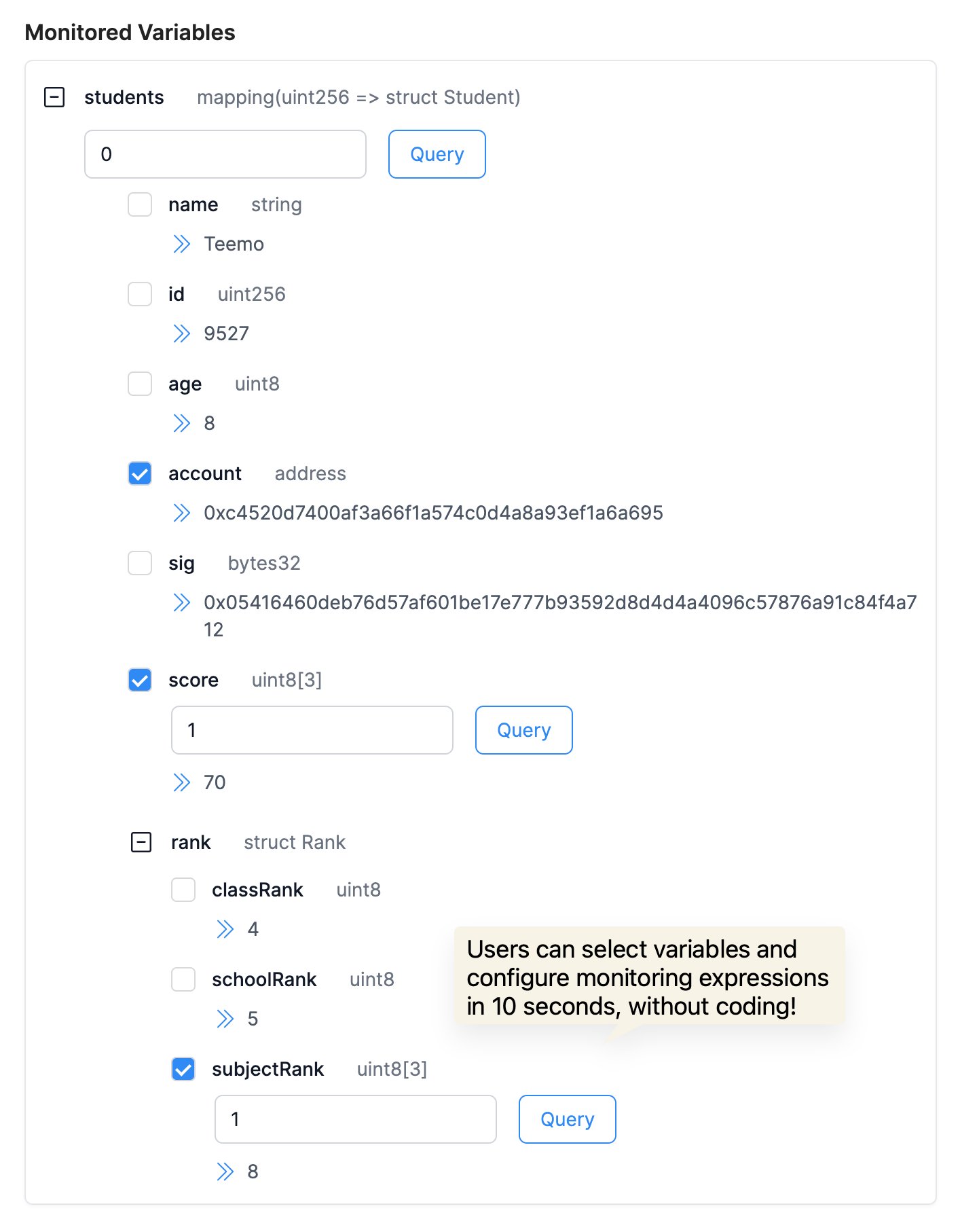
We have made substantial improvements in handling complex data structures, enhancing Phalcon's ability to analyze and monitor nested structures, including structs, mappings, and arrays.
These advancements in storage analysis and monitoring empower developers and security researchers to better comprehend and monitor onchain activities, swiftly identifying potential security threats or misconfigurations to ensure the stability of protocols and safety of funds.
Introduction to Blockchain Storage and Its Importance
In blockchain technology, "storage" is the component that permanently retains all state and data, including the varied state data resulting from contract executions. Each blockchain transaction can alter the information stored, making storage a crucial element of the blockchain network. Robust storage analysis and monitoring capabilities are essential for developers and security researchers to effectively oversee on-chain transactions, detect potential security issues or misconfigurations promptly, thereby maintaining protocol stability and securing funds.
In the realm of contract development, developers often craft complex and nested data structures. Prior to the introduction of Phalcon, no tool existed that could monitor the variables within these intricate structures accurately without additional coding. Phalcon has revolutionized this aspect, offering tools that allow for seamless monitoring of such complex data structures.
Major Upgrade in Phalcon's Analysis Capabilities
In this upgrade, we have significantly enhanced the analysis capabilities of our blockchain explorer, particularly in handling complex data structures. We have improved the display capabilities for nested situations involving structs, mappings, and arrays. Now, users can more intuitively view and analyze the nested data structures within smart contracts. This represents a major advancement for developers, as it enables them to more accurately verify contract states and internal logic.
Using Phalcon to monitor key variables in contracts, the platform is able to:
- Parse the values of complex variables within current contracts, assisting developers in determining whether the contract state is abnormal.
- Configure precise monitoring for key variables, minimizing false positives and protecting funds. Alerts and pre-configured actions are triggered when key variable changes occur due to attack transactions that meet user-configured conditions.
For example, in the recent security incident involving the SaitaChain project, if developers had been monitoring the key variable _tokenOwner, any unexpected change would have triggered an immediate alert and executed a predetermined action.
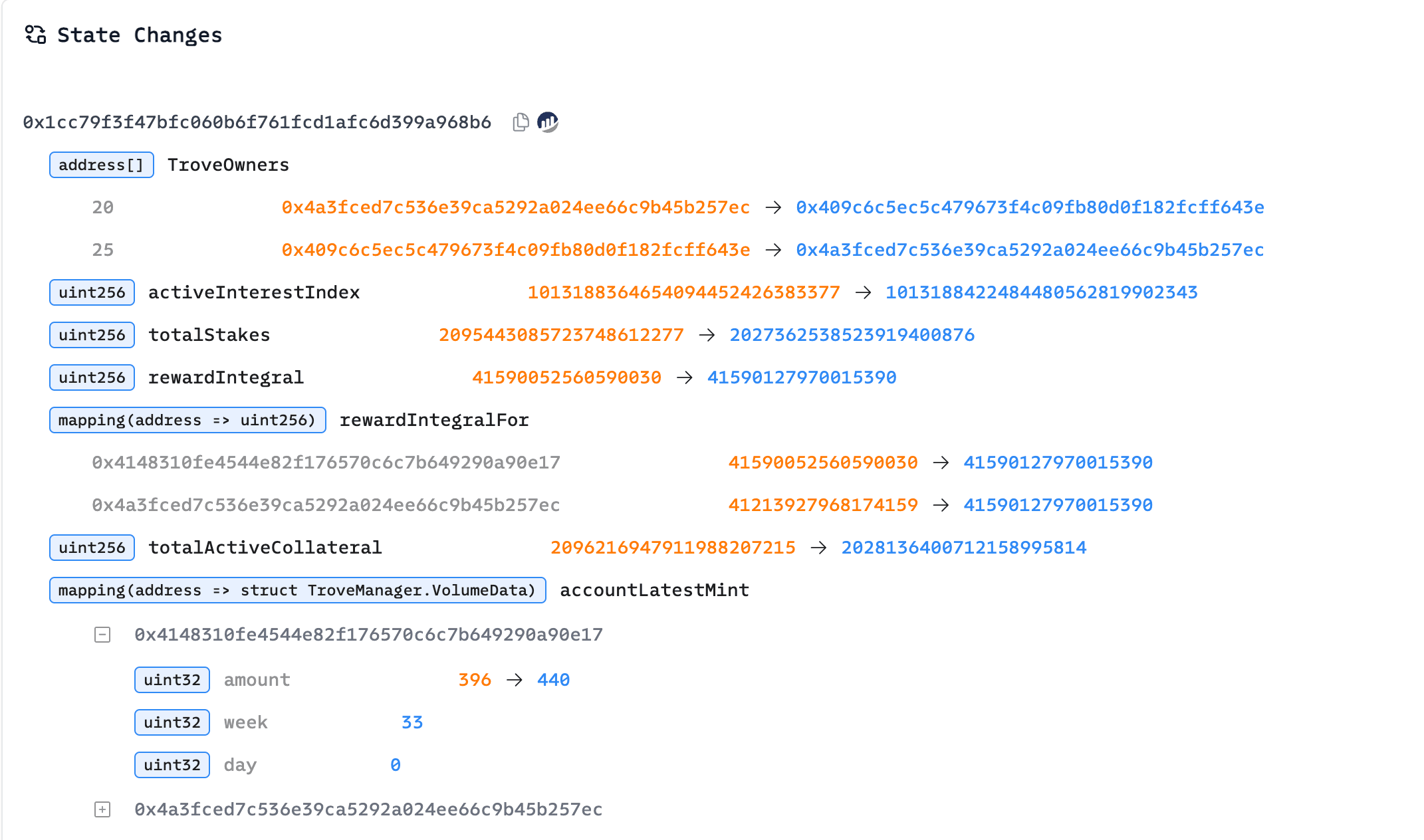
Upgrades to Phalcon Explorer's Storage Change Analysis Capabilities
Complementing the upgrades to Phalcon, our supporting tool, Phalcon Explorer, has also undergone comprehensive enhancements in storage analysis, establishing themselves as leaders in blockchain analysis tools.
Whether developers are debugging transactions or security researchers are analyzing unusual transactions, Phalcon Explorer now provides clearer and more intuitive results for Storage Change, aiding developers in understanding the changes to key variables in transaction storage and helping security researchers more quickly pinpoint issues.
Example transaction: https://app.blocksec.com/explorer/tx/eth/0xdc5c56869862f7da6527ec68da9d8e1e04ccc3ca16a6b3ebe8f714432d505245
BlockSec continues to innovate with Phalcon, providing cutting-edge tools for project teams, developers, LPs, and security researchers, protecting their protocols and assets from security threats. Let's work together towards a safer DeFi ecosystem. 🛡️
About Phalcon
🔗 https://blocksec.com/phalcon
Phalcon is a security platform developed by BlockSec to monitor and block hacks. The system detects suspicious transactions, instantly alerts users, and takes automated actions in response.
Phalcon's Key Advantages:
- Precise detection with minimal to zero FPs.
- Monitors both hacks and operational risks like privilege changes.
- Initiates automatic actions, with support for user-defined responses.
- Enables code-free configuration of monitors and actions.
Phalcon is a SaaS platform where users can directly log in through our official website to view different pricing plans and features, and subscribe immediately (supporting both credit card and crypto payments). For any questions, feel free to book a demo with our security experts who will address your concerns.
Support Tool: Phalcon Explorer
Phalcon Explorer is the support tool for the Phalcon platform. This powerful transaction explorer is designed for the DeFi community. It provides comprehensive data on call flows, balance changes, and transaction fund flows, as well as supports transaction simulation. This helps developers, security researchers, and traders to more intuitively understand transactions.



