如 Will Sheehan 所报道,APE 代币受到了 MEV 的攻击。经过分析,我们认为这是由于 APE 代币的空投过程只考虑了即时状态的漏洞,攻击者可以操纵该状态。
具体来说,攻击者可以借入可以兑换成 NFT 的 BYAC 代币,然后使用这些 NFT 来申领空投。之后,攻击者通过 BYAC NFT 来铸造 BYAC 代币,以偿还闪电贷。然而,攻击者在此过程中获得了空投的 APE 代币。我们认为这类似于基于闪电贷的价格操纵攻击,即合约只考虑资产的即时价格(可以被操纵)。
接下来,我们将使用 攻击交易 来说明这一过程。
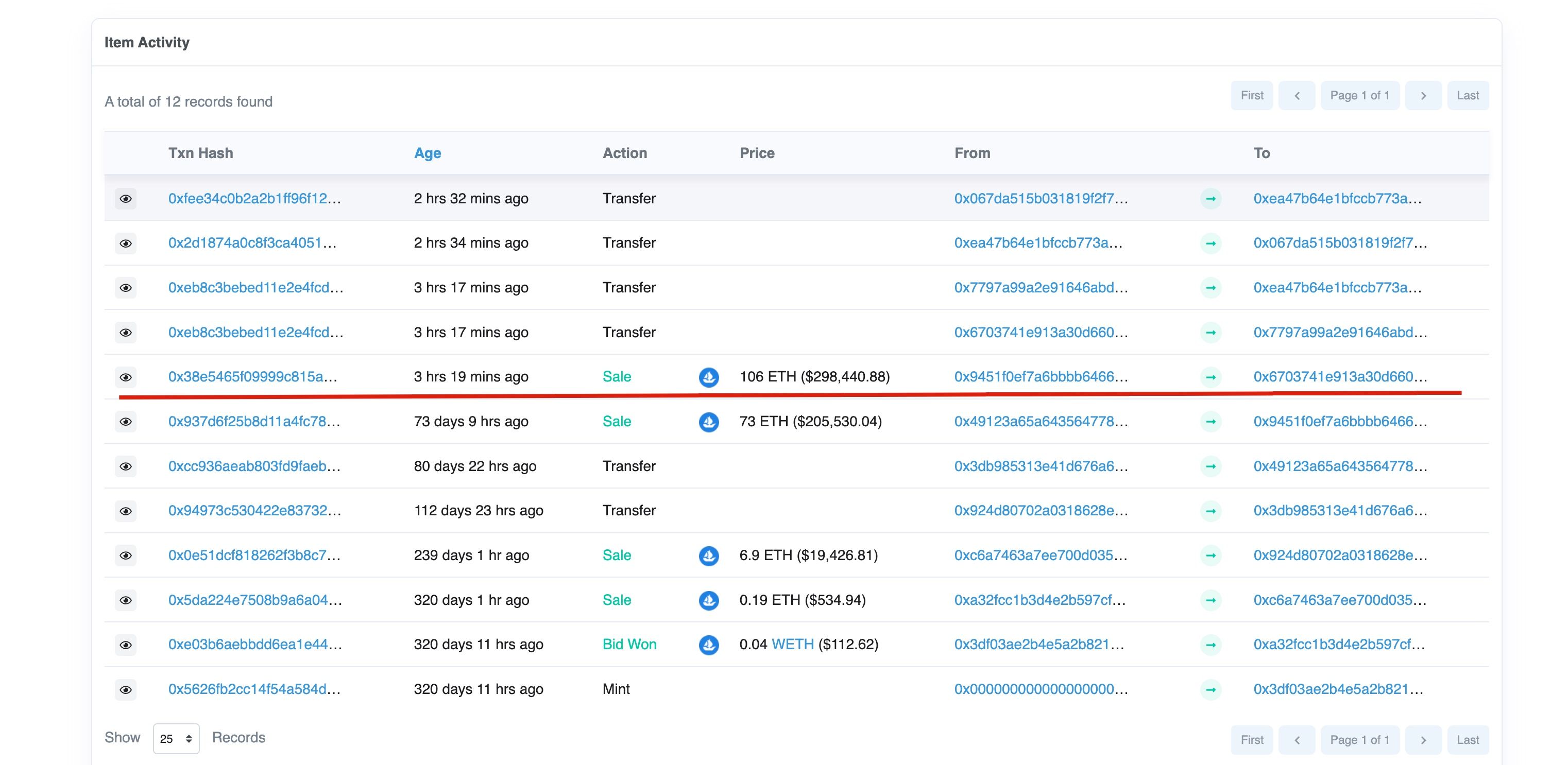
第一步:准备用于闪电贷费用的 NFT
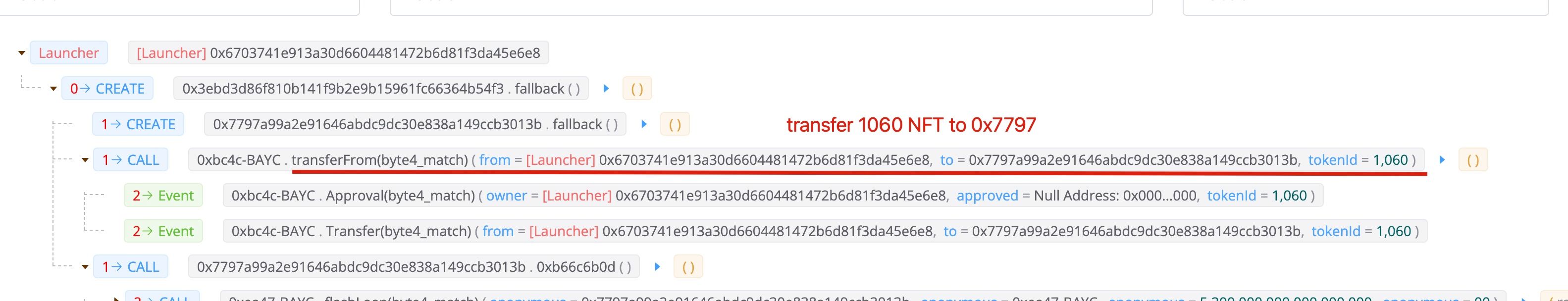
攻击者将 1060 个 NFT 转入了攻击合约 0x7797。请注意,此 NFT 并非通过闪电贷借入,而是以 106 ETH 买入。
第二步:通过闪电贷借入 BYAC 代币
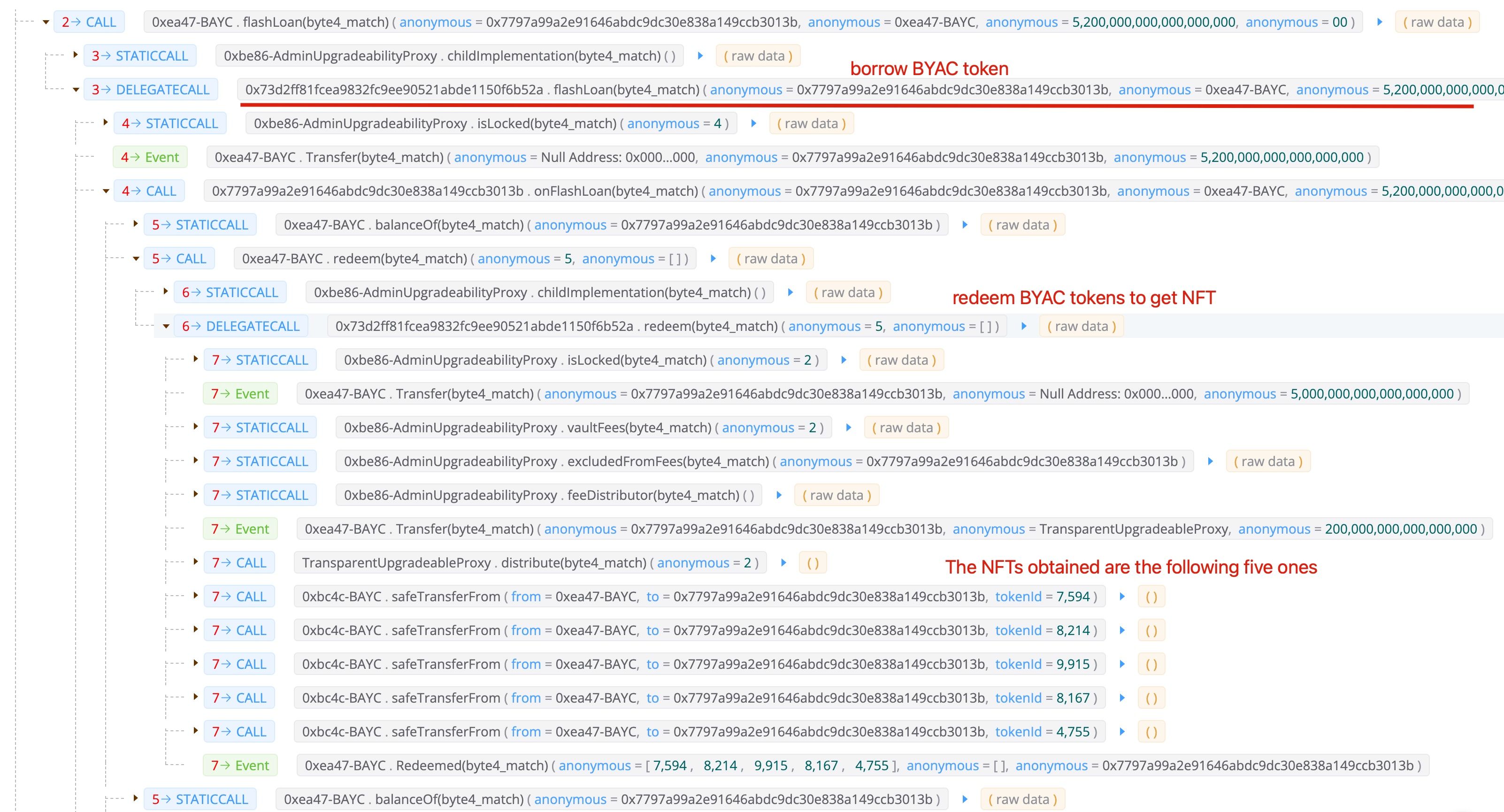
第三步:使用 NFT 申领 APE 代币

请注意,在此过程中,攻击者拥有六个 NFT。一个是其购买的 1060 个,另外五个是通过(第二步)借入的 BYAC 代币兑换而来的。总共获得了 60,564 个 APE 代币。
第四步:铸造 NFT 以获取 BYAC 代币

攻击者铸造了六个 NFT 以获取 BYAC 代币。请注意,攻击者还铸造了其自己的 NFT(1060 个)来支付闪电贷的费用。由于偿还闪电贷后仍有剩余的 BYAC 代币(因为他铸造了自己的 BYAC NFT 1060 个),攻击者将剩余的 BYAC 代币兑换了大约 14 ETH。
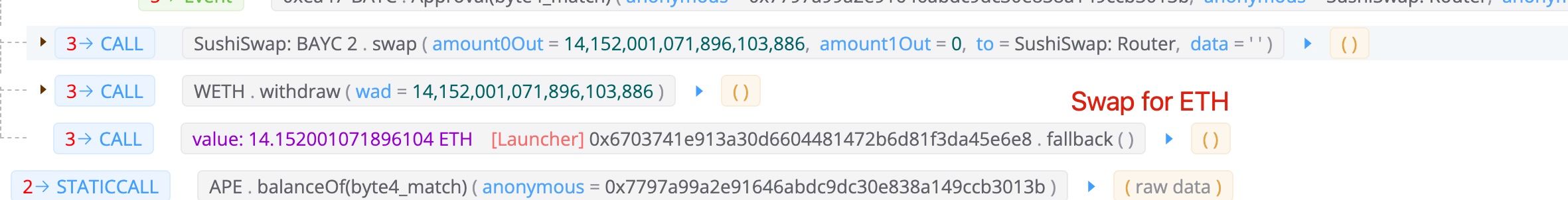
利润
总计,攻击者获得了 60,564 个 APE 代币,其价值约为 500 万美元(撰写本博客时)。成本是一个 NFT(106 ETH - 14 ETH),约为 270K 美元。
教训
我们认为这里的问题是,APE 代币的空投仅考虑了 NFT 是否被持有的即时状态。这很不安全,因为攻击者可以使用闪电贷操纵即时状态。如果闪电贷的成本小于空投代币的价值,那么就会出现如图所示的攻击机会。
致谢
感谢 Will Sheehan 报告了此次交易。
关于 BlockSec
BlockSec 是一家开创性的区块链安全公司,由一群全球知名的安全专家于 2021 年创立。公司致力于提高新兴 Web3 世界的安全性和可用性,以促进其大规模采用。为此,BlockSec 提供智能合约和 EVM 链安全审计服务,Phalcon 平台用于安全开发和主动阻止威胁,MetaSleuth 平台用于资金追踪和调查,以及 MetaDock 扩展,供 Web3 构建者在加密世界中高效冲浪。
迄今为止,该公司已为 MetaMask、Uniswap Foundation、Compound、Forta 和 PancakeSwap 等 300 多家尊贵客户提供服务,并从 Matrix Partners、Vitalbridge Capital 和 Fenbushi Capital 等知名投资者那里获得了两轮数千万美元的融资。




