On February 22, 2026, a lending pool operated by YieldBlox DAO on Stellar's Blend V2 was exploited, resulting in losses exceeding $10 million.
The attacker manipulated the USTRY/USDC market on SDEX. The pool's configured Reflector oracle path then accepted the manipulated price, overvalued USTRY collateral, and enabled the attacker to drain pool assets (USDC and XLM).
This incident was not a Blend V2 core-contract issue. It was a pool-operator (YieldBlox DAO) configuration issue.
2. Background
On Stellar, Blend V2 is a liquidity protocol that allows users to create isolated lending pools. Each pool defines its own borrow assets, collateral assets, and oracle settings.
In this incident, the affected pool allowed users to borrow XLM and USDC using USTRY as collateral. The pool used the Reflector oracle [2], and USTRY pricing was sourced from the USTRY/USDC market on SDEX [3], with periodic updates.
3. Vulnerability Analysis (Root Cause Analysis)
The exploit was enabled by a pool-side pricing design that relied on a manipulable market.
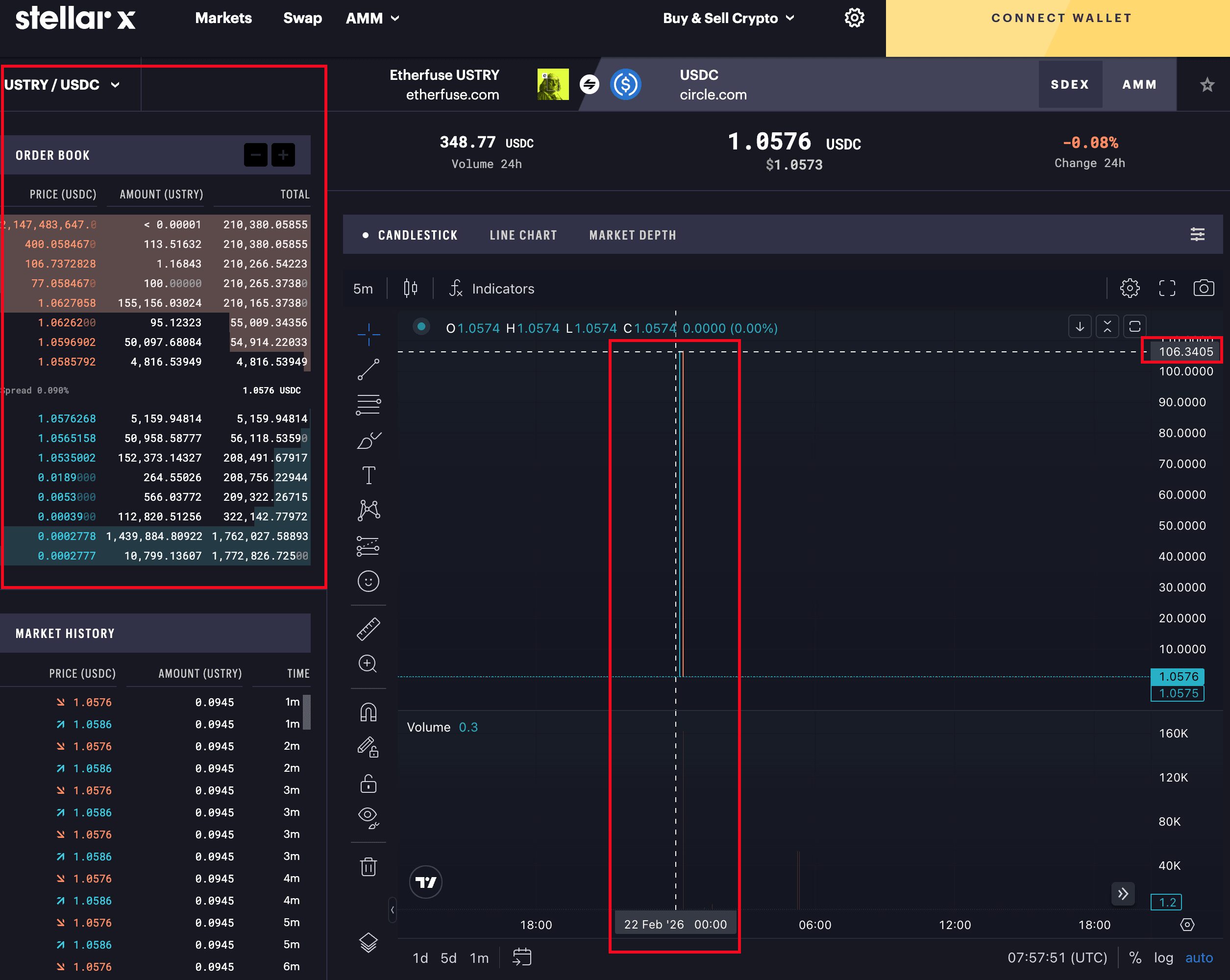
- The USTRY/USDC market on SDEX was very shallow.
- The attacker could clear normal orders and place abnormal orders to push the apparent market price sharply higher.
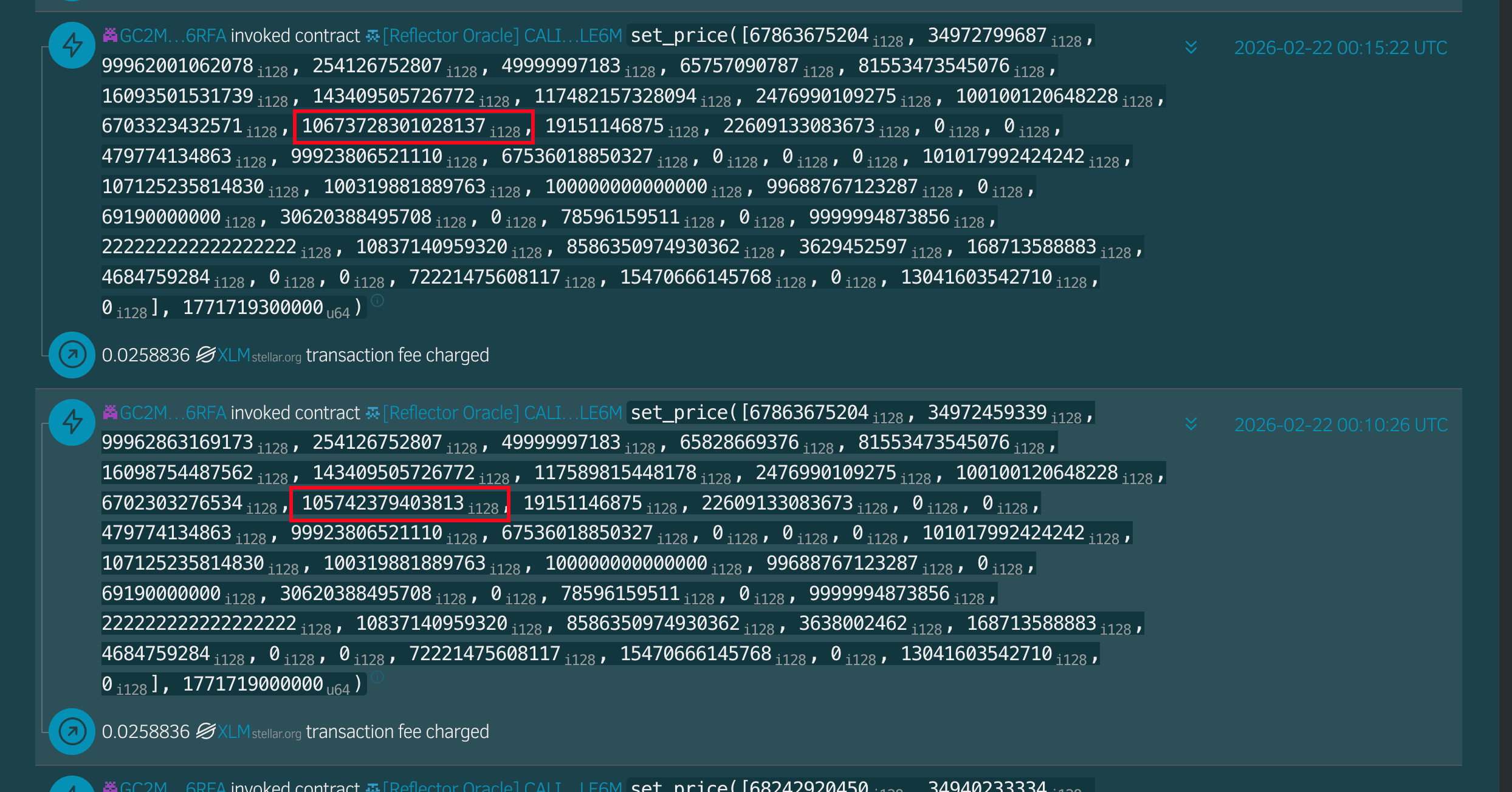
- Reflector then updated USTRY to the manipulated value.
- The pool's risk logic accepted that value for collateral valuation, which inflated borrow power.
As a result, the attacker used overvalued USTRY collateral to drain borrowable assets from the pool.
4. Attack Analysis
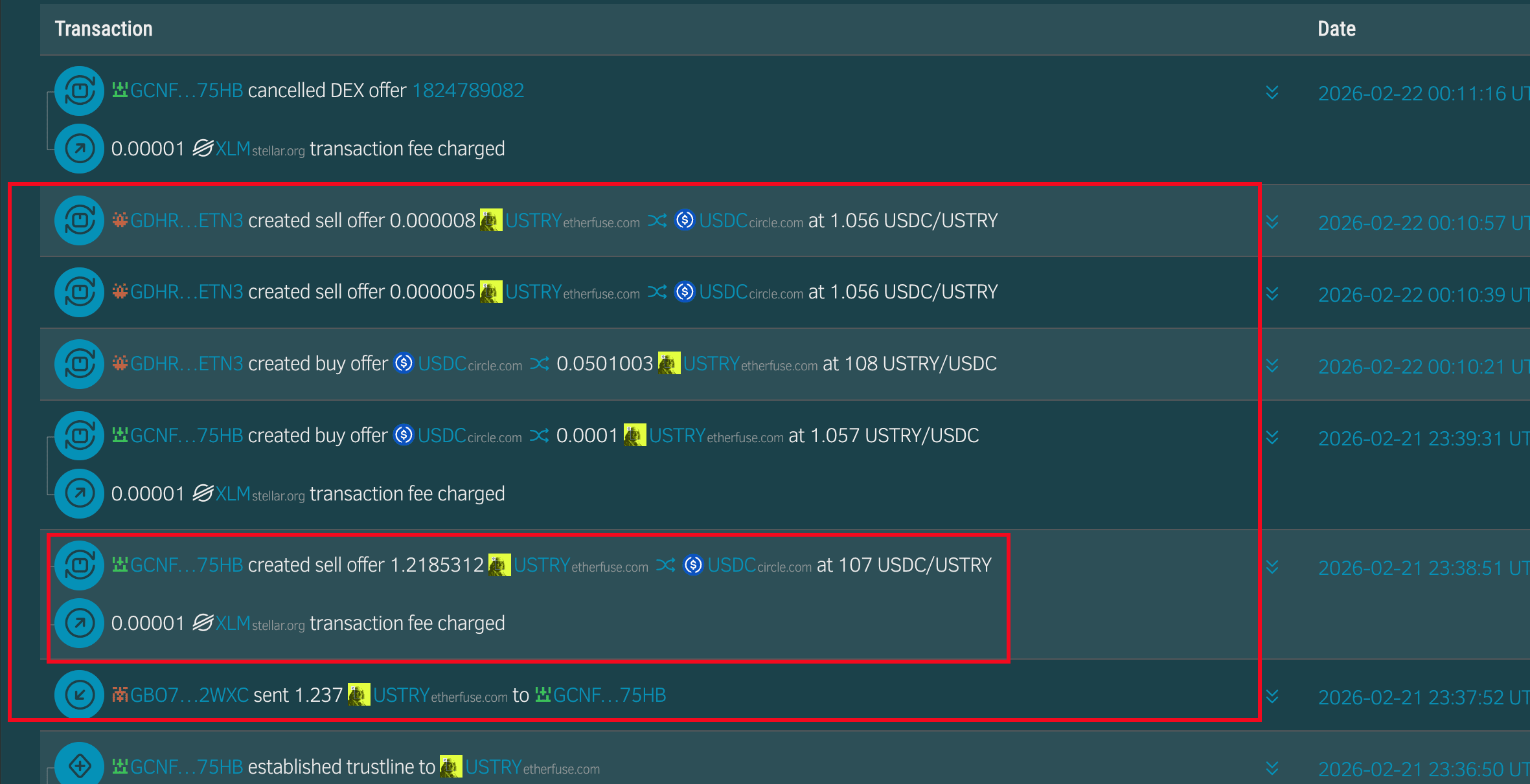
- (Tx 1, 2) The attacker manipulated USTRY on SDEX from about $1.06 to about $107 by consuming normal liquidity and placing abnormal orders.
- (Tx 3) Reflector pulled the manipulated SDEX price and updated its feed.
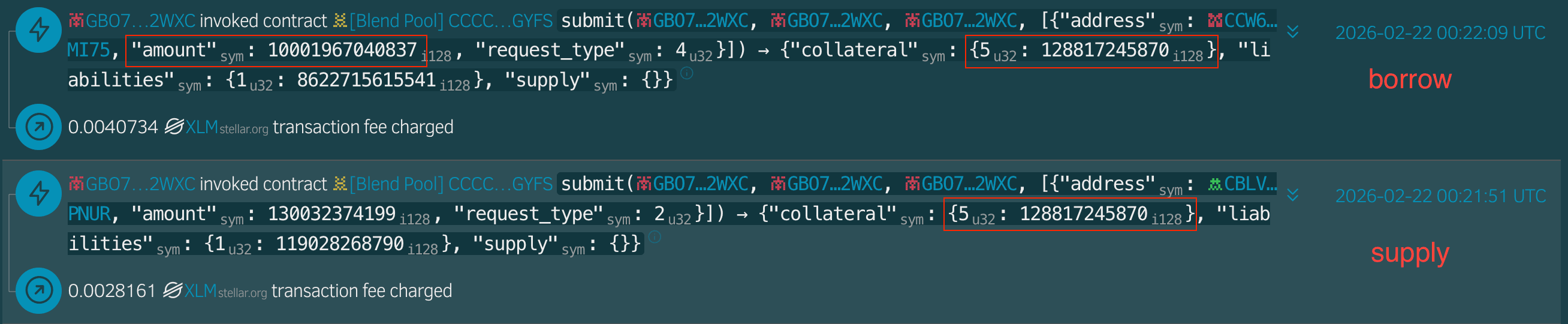
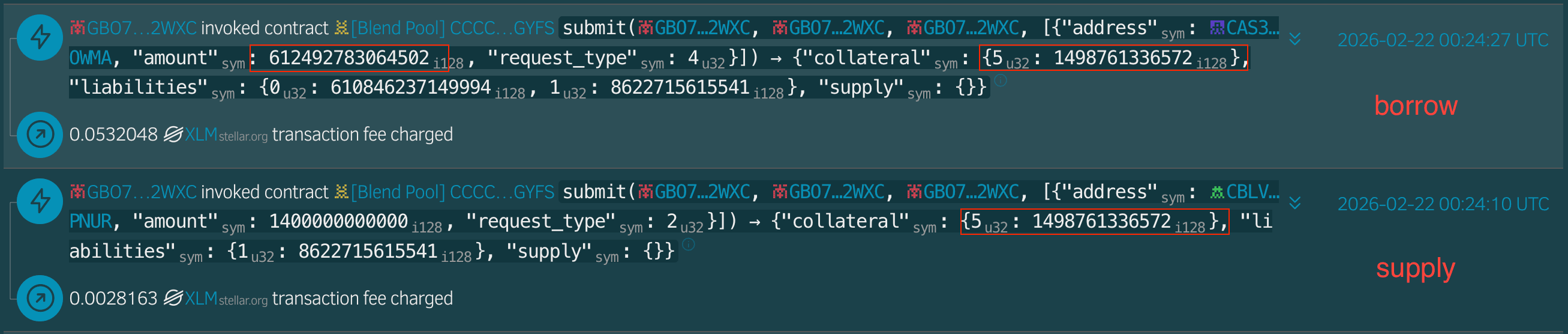
- (Tx 4, 5) The attacker borrowed 1,000,196e7 USDC with 12,881e7 USTRY collateral.
- (Tx 6, 7) The attacker borrowed 6,124,927,810e7 XLM with 14,987,610e7 USTRY collateral.
- (Tx 8, 9, 10) The attacker bridged drained assets to Base, BSC, and Ethereum.
5. Loss/Profit Analysis
Estimated total loss was about $10M+ on Stellar.
| Chain | Type | Address |
|---|---|---|
| Stellar | Attacker | GBO7VUL2TOKPWFAWKATIW7K3QYA7WQ63VDY5CAE6AFUUX6BHZBOC2WXC |
| Stellar | Attacker | GCNF5GNRIT6VWYZ7LXUZ33Q3SR2NUGO32F5X65VVKAEWWIQCKGYN75HB |
| Stellar | Attacker | GDHRCQNC64UVL27EXSC6OG6I2FCT4NWM72KNHLHKEB3LK4MEEYYWETN3 |
| Stellar | Attacker | GATDQL767ZM2JQTBEG4BQ5WKOQNGAGWZDUN4GYT2UINPEU3RT2UAMVZH |
| Stellar | Reflector Oracle | CALI2BYU2JE6WVRUFYTS6MSBNEHGJ35P4AVCZYF3B6QOE3QKOB2PLE6M |
| Stellar | Victim Pool | CCCCIQSDILITHMM7PBSLVDT5MISSY7R26MNZXCX4H7J5JQ5FPIYOGYFS |
| BSC, Base, Ethereum | Attacker | 0x2d1ce29b4af15fb6e76ba9995bbe1421e8546482 |
| Ethereum | Attacker | 0x0b2b16e1a9e2e9b15027ae46fa5ec547f5ef3ec6 |
| Ethereum | Attacker | 0xe69f6d77db6ff493fdd15d8a0b390c36e18e5b21 |
6. Conclusion
The core issue is straightforward: collateral valuation in this pool depended on a manipulable price source. This was a pool-operator (YieldBlox DAO) configuration failure, not a Blend V2 core-contract flaw. This incident is a reminder that lending pools must select and monitor price dependencies with strong manipulation resistance.
References
[1] YieldBlox DAO
[2] https://reflector.network/
[3] USTRY/USDC Market on the SDEX
About BlockSec
BlockSec is a full-stack blockchain security and crypto compliance provider. We build products and services that help customers to perform code audit (including smart contracts, blockchain and wallets), intercept attacks in real time, analyze incidents, trace illicit funds, and meet AML/CFT obligations, across the full lifecycle of protocols and platforms.
BlockSec has published multiple blockchain security papers in prestigious conferences, reported several zero-day attacks of DeFi applications, blocked multiple hacks to rescue more than 20 million dollars, and secured billions of cryptocurrencies.
-
Official website: https://blocksec.com/
-
Official Twitter account: https://twitter.com/BlockSecTeam




