PolyNetwork遭到黑客攻击,超过3亿美元被盗。攻击者在多个链上执行了此次攻击。在本博客中,我们以以太坊上的攻击交易 (0xd8c1f7424593ddba11a0e072b61082bf3d931583cb75f7843fc2a8685d20033a) 来分析此次黑客攻击的可能原因。我们初步分析表明,可能的原因是用于签署跨链消息的私钥泄露,或者PolyNetwork的签名过程中存在一个bug,该bug被滥用以签署精心构造的消息。
免责声明:本博客仅包含基于以太坊链上数据的初步分析结果。在未获得Poly Network的进一步信息的情况下,我们无法核实我们的发现。
更新 2021/08/12:进一步信息显示,攻击原因是 Keeper 被攻击者篡改(而非私钥泄露)。我们对 Keeper 更改交易为何会首先被执行进行了进一步分析。
交易和调用追踪
我们使用我们的交易分析系统来恢复追踪。

攻击者 -> EthCrossChainManager -> EthCrossChainData -> LockProxy -> managerProxyContractforLockProxy
- 0xc8a65fadf0e0ddaf421f28feab69bf6e2e589963: 攻击者
- 0x838bf9e95cb12dd76a54c9f9d2e3082eaf928270: EthCrossChainManager
- 0xcf2afe102057ba5c16f899271045a0a37fcb10f2: EthCrossChainData
- 0x250e76987d838a75310c34bf422ea9f1ac4cc906: LockProxy
- 0x5a51e2ebf8d136926b9ca7b59b60464e7c44d2eb: managerProxyContract for LockProxy
函数签名:
- d450e04c (verifyHeaderAndExecuteTx)
- 69d48074 (getCurEpochConPubKeyBytes)
- 5ac40790 (getCurEpochStartHeight)
- 0586763c (checkIfFromChainTxExist)
- e90bfdcf (markFromChainTxExist(uint64,bytes32))
攻击的主要流程
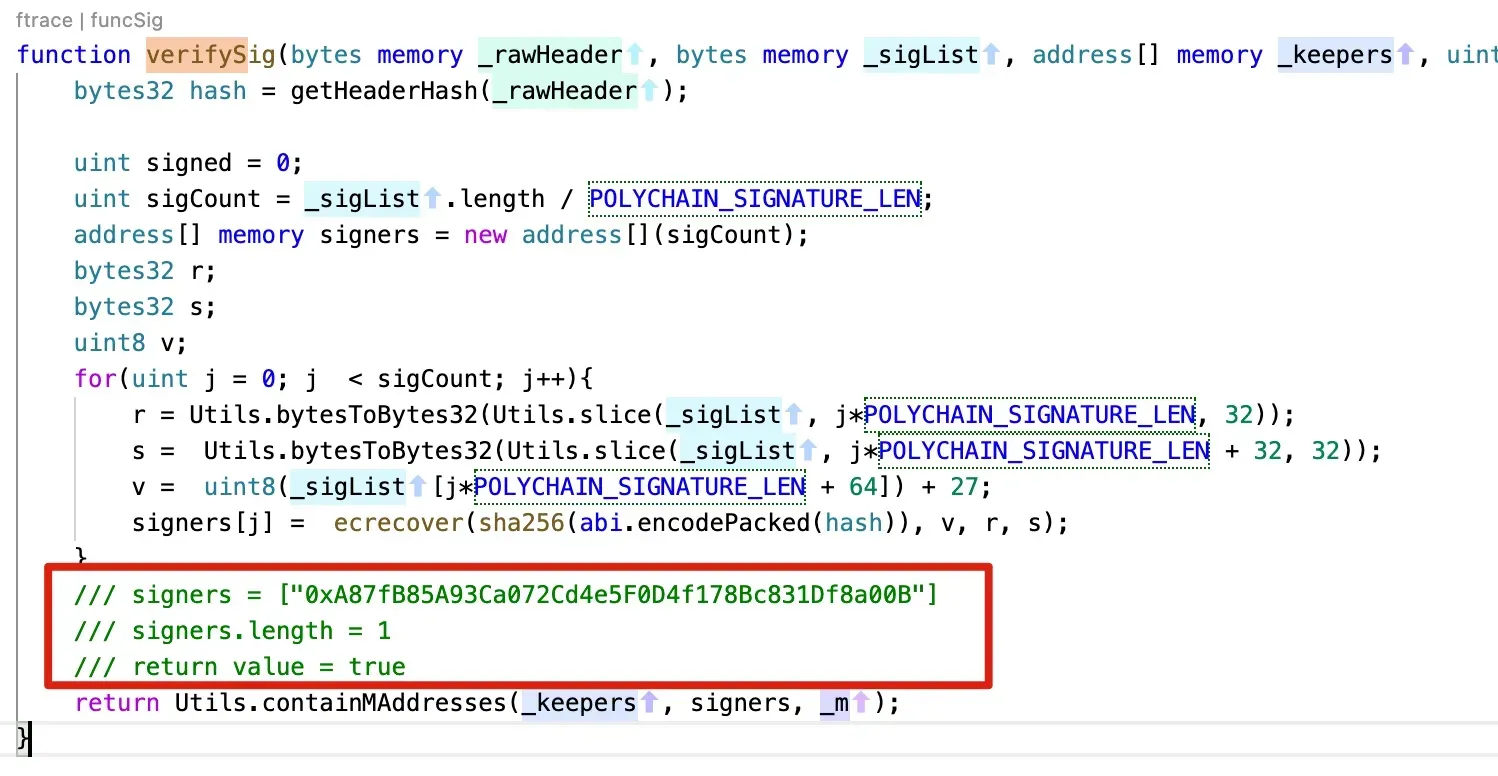
攻击的主要流程是攻击者将签名数据传递给 verifyHeaderAndExecuteTx() 函数。该函数将解码数据并验证用于签名数据的签名。如果此过程通过,将执行消息中指定的函数(及其合约地址)。在本次攻击中,调用了智能合约 0x250e76987d838a75310c34bf422ea9f1ac4cc906 的 unlock 函数,将Fei转移给了攻击者。
总而言之,攻击是由于向 verifyHeaderAndExecuteTx 函数传递了有效的参数。这些参数能够通过签名验证过程。之后,消息中指定的交易将被执行(类似于软件安全中的任意命令执行)。
为了更好地理解这个过程,我们恢复了调用追踪的关键值。
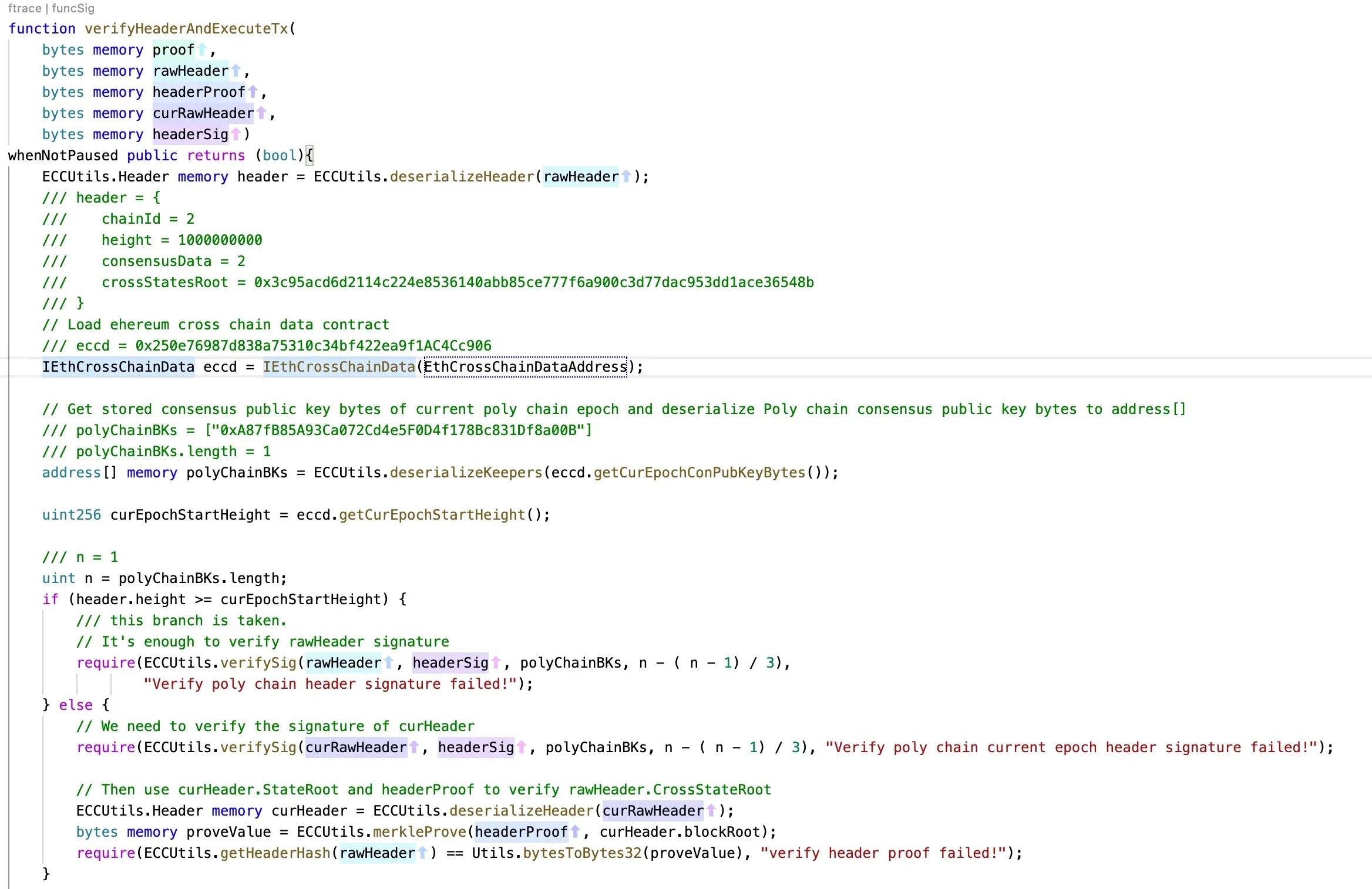
函数:verifyHeaderAndExecuteTx:
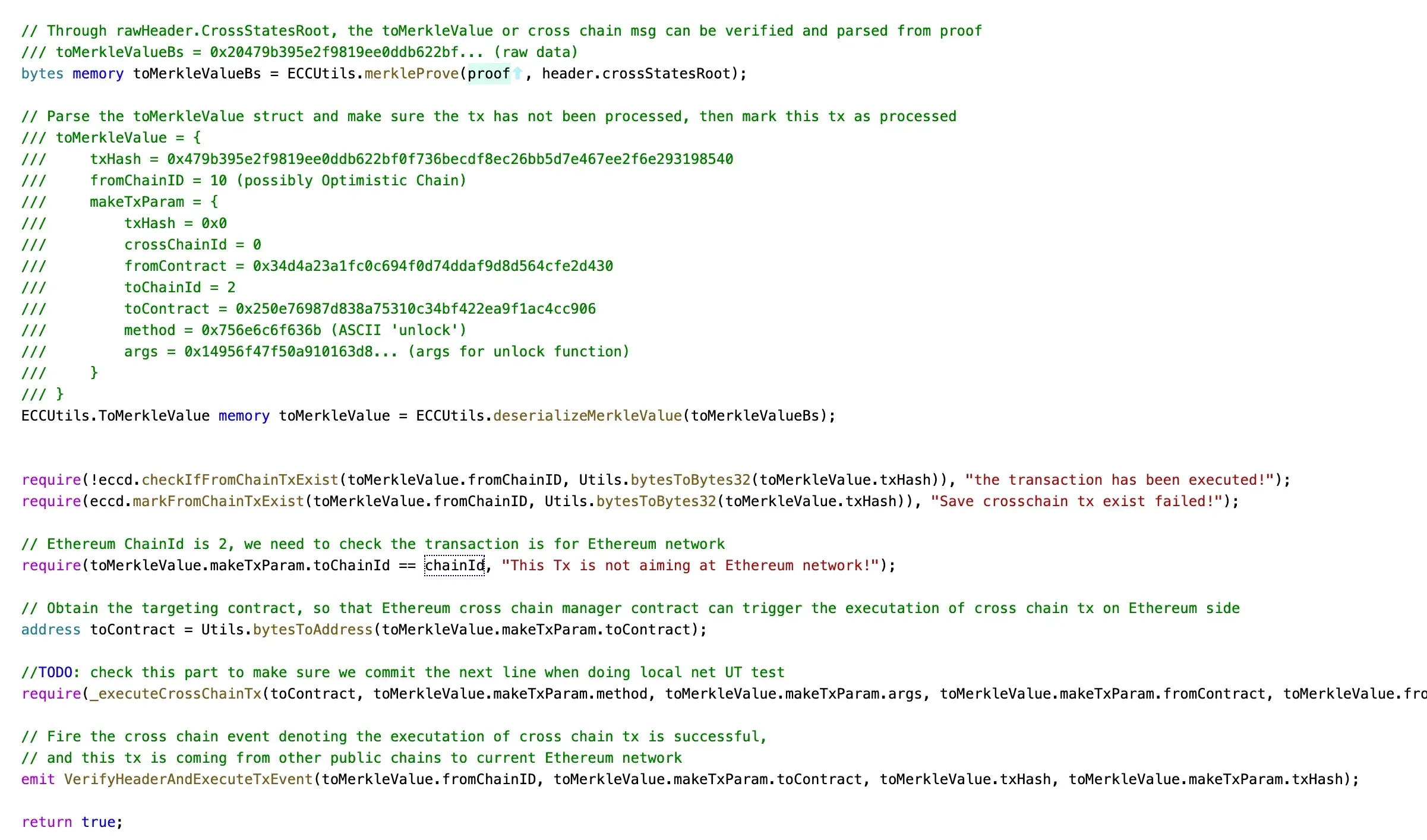
verifySig
unlock
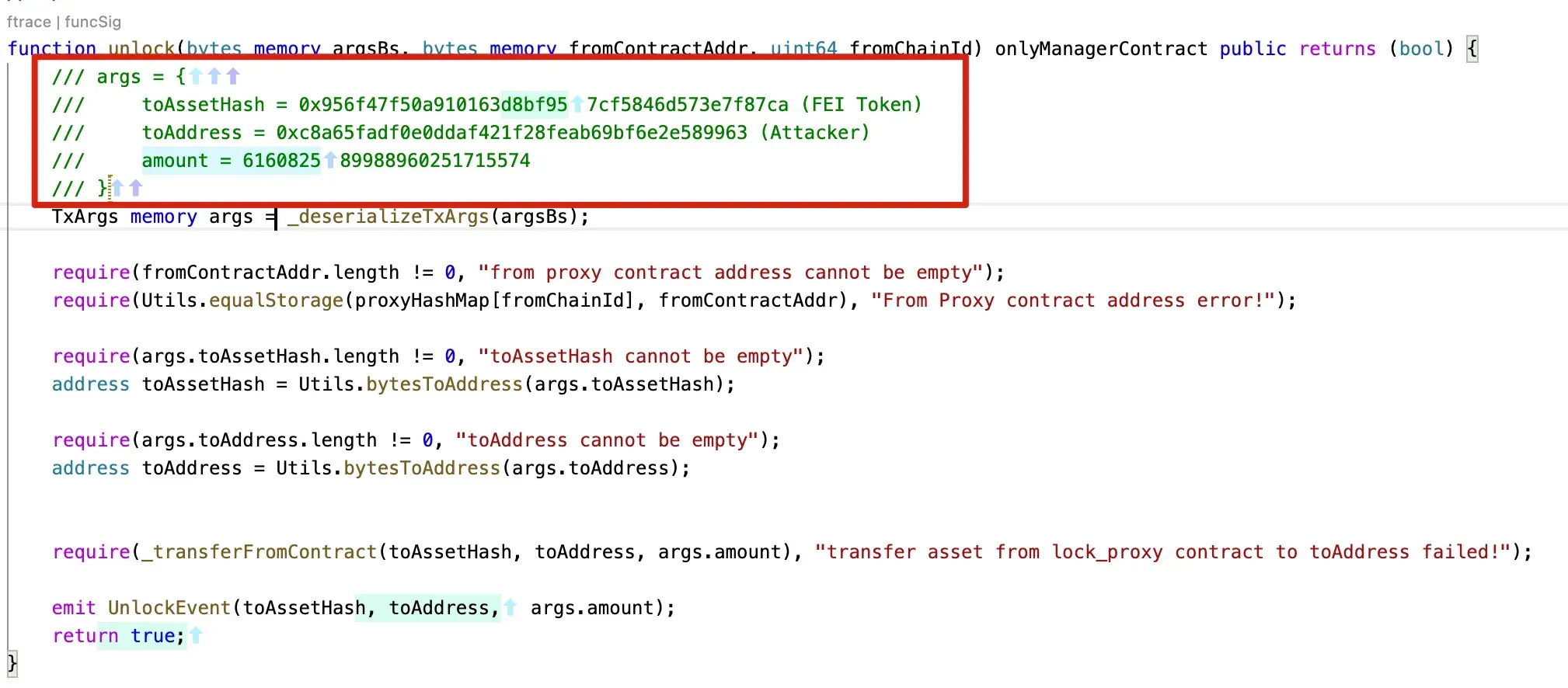
LockProxy 中的 managerProxyContract 变量。它与 unlock 函数的调用者地址值匹配。

结论
从恢复的值中,我们发现:
- 攻击者向
verifyHeaderAndExecuteTx函数提供了一个有效的签名消息。 - LockProxy 智能合约中的
onlyManagerContract修饰符未被绕过。
基于这两点观察,我们怀疑:
- 攻击者可能拥有用于签署消息的合法密钥,这表明签名密钥可能已泄露。
或者
- PolyNetwork 的签名过程中存在一个bug,该bug被滥用以签署精心构造的消息。
但是,我们没有更多的链下数据来验证我们的发现。我们希望我们的分析能够有助于进一步的调查。
致谢:Yufeng Hu, Siwei Wu, Lei Wu, Yajin Zhou @BlockSec
Twitter:https://twitter.com/BlockSecTeam




