安全一览 👀
2024 年 3 月,DeFi 攻击导致约 8100 万美元的损失。幸运的是,得益于各方的努力,大部分资金已追回,或正在进行谈判。
- PrismaFi 攻击事件
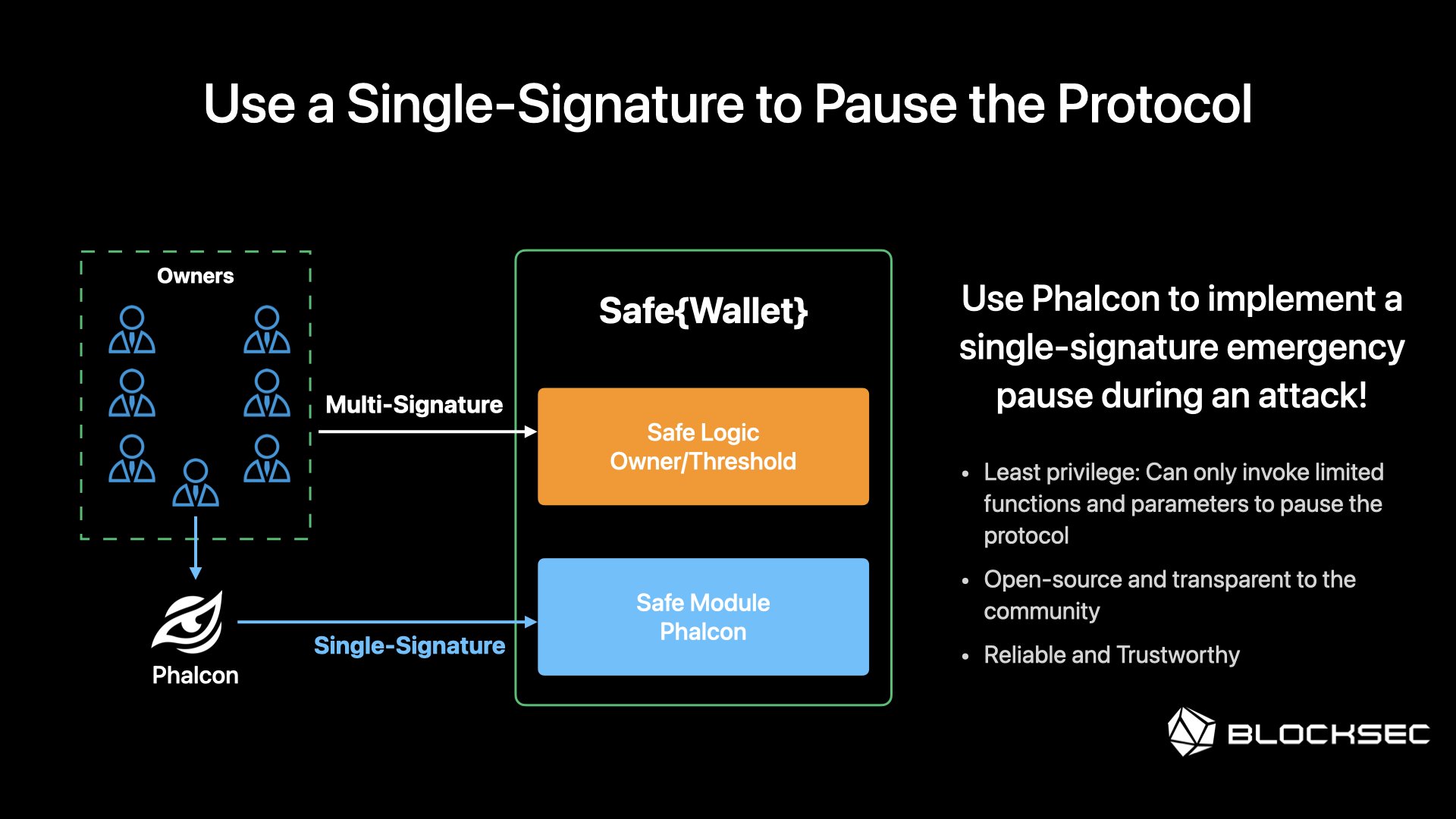
3 月 28 日,以太坊上的 PrismaFi 遭到攻击,损失约 1100 万美元。 根本原因在于 未经验证的用户输入。值得注意的是,此次攻击通过 10 笔以上交易完成,并出现了 2 名模仿者。项目团队在首次攻击发生 90 分钟后,通过多重签名暂停了合约。在此次攻击中,使用 Phalcon 实现 单签名紧急暂停 可以显著减少损失。
主攻击者已表示愿意归还资金,与项目团队的谈判仍在进行中,请查看 谈判聊天记录。
- Munchables 事件
3 月 27 日,Blast L2 上的 Munchables 资产被盗 6200 万美元。 此事件是由于开发者实施了恶意升级(合约未开源)所致。幸运的是,项目团队和 Blast L2 核心团队迅速采取行动,开发者已归还资金。目前,所有资金都存放在一个由 Blast L2 核心团队控制的 Safe{wallet} 中。
- ParaSwap 攻击事件
3 月 19 日至 3 月 21 日,ParaSwap 的多名用户遭到攻击,总损失至少为 30 万美元。 根本原因是 访问控制问题。值得一提的是,主攻击者已归还 90% 的资产。
- Unizen 攻击事件
3 月 8 日,以太坊和 Polygon 上的 Unizen 遭受攻击,损失 280 万美元。 根本原因是未经验证的用户输入问题。DeFi 用户应定期检查其授权并保持警惕!
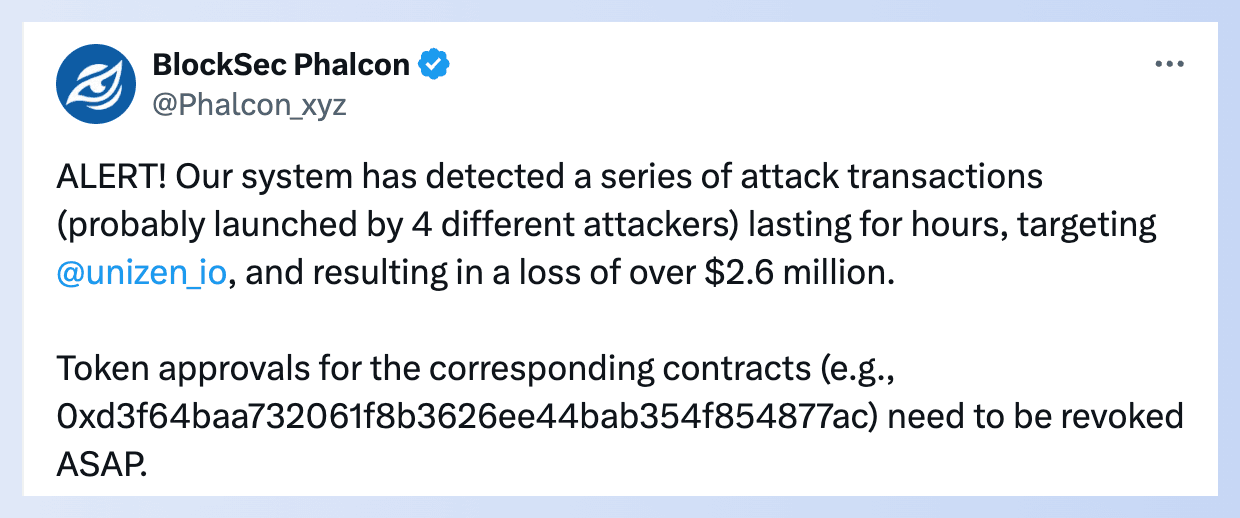
此外,白帽黑客通过 bloXroute 的半私有 RPC 在 Polygon 上发送了救援交易,但该救援交易被发送到内存池并被 MEV 机器人抢跑,引发了争议。阅读更多关于此事件。
- TGBS Token 攻击事件
3 月 6 日,BSC 上的 TGBS Token 遭受攻击,损失 15 万美元。 有趣的是,所有者在一小时前所做的更改触发了此次攻击,因此这可能又是一次 rug pull。查看警报
- WooFi 攻击事件
3 月 5 日,Arbitrum 上的 WooFi 遭受攻击,损失 875 万美元。 根本原因是 易受攻击的价格依赖性 问题。WooFi 的借贷市场被利用,因为 $Woo 的价格被操纵得非常便宜,使得攻击者可以通过闪电贷借入大量 $Woo 并轻松偿还。
尽管其价格机制利用 Chainlink 的预言机进行价格检查,但 Arbitrum 上的 Chainlink 未能提供 $Woo 的价格,未能阻止此次攻击。阅读事后分析报告
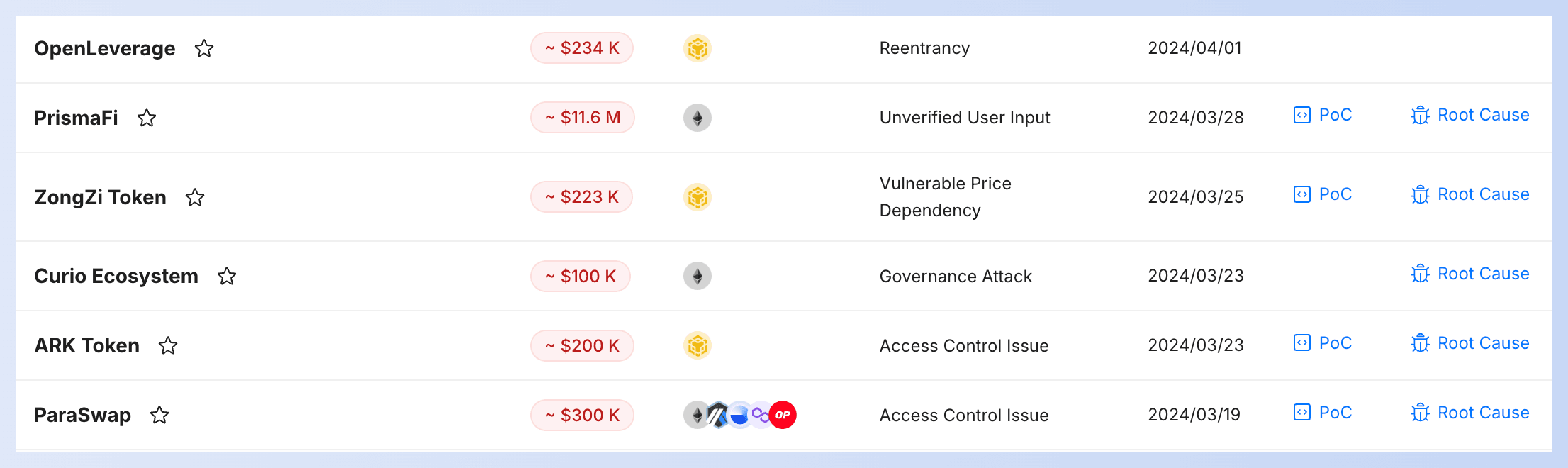
👉 您可以在我们的 安全事件列表 中查看上述事件的攻击交易、根本原因和 PoC。
博文 & 视频
L2 链如何实施多项措施来增强顶级协议的安全性并保护链上用户资产。
利用 BlockSec 保护协议的整个生命周期。从发布前的安全审计到发布后的攻击监控和拦截(Phalcon),我们一应俱全。

BlockSec 首席执行官 Yajin Zhou 在 2024 年 ETHDenver 的 Open Information House 上发表了题为“BlockSec 与安全前沿”的重要演讲。
不要错过这个机会,进行一场引人入胜且富有洞察力的讨论,它有望改变您对区块链安全的看法。
合作
Blockscout 区块链浏览器集成了 MetaSuites 的 地址标签(Ethereum、Polygon、Gnosis、Optimism 和 Base)和 GPT 驱动的交易解释(Ethereum)功能,并添加了对 Phalcon Explorer 的快速访问。🎉🎉
新网站,新篇章
激动人心的消息——我们对网站进行了全面改版!

在 BlockSec,我们随时为您提供支持,确保您的协议在从发布前到发布后的每个阶段都安全可靠!点击 此处 进行探索。



