2020年11月,Loopring的LRC协议费用金库(Protocol Fee Vault)中出现了一个关键漏洞,攻击者利用了访问控制的薄弱环节,并通过闪电贷攻击操纵了代币价格。此事件凸显了强大的访问控制和持续的DeFi安全监控对于防止代价高昂的攻击的重要性。
Loopring (LRC) 协议事件简介
2020年末,包括Pickle Finance和88mph在内的多个基于以太坊的DeFi平台经历了安全事件。为了检测此类漏洞,BlockSec开发了ThunderForecast系统,该系统识别出涉及异常大的交易汇率差异以及同一外部拥有账户(EOA)持续获得以太币的疑似交易。
通过我们的EthScope系统,我们分析了这些交易,并发现了一个针对Loopring金库协议(特别是LRC协议费用金库 LRCPFV)中漏洞的攻击。本博客文章将详细介绍此次攻击、其影响以及为DeFi安全社区带来的经验教训。
LRC协议费用金库概述
Loopring是以太坊上的一个开源去中心化交易所(DEX)协议。其原生代币LRC(ERC-20)在该生态系统中使用。Loopring的金库协议,称为LRC协议费用金库(LRCPFV),存储协议费用并允许将交易费用兑换成LRC代币。
LRCPFV中的漏洞函数是sellTokenForLRC,它允许在没有适当访问控制的情况下将代币兑换成LRC,使得任何人都可以调用它。
function sellTokenForLRC(
address token,
uint amount
)
external
nonReentrant
{
require(amount > 0, "ZERO_AMOUNT");
require(token != lrcAddress, "PROHIBITED");
address recipient = tokenSellerAddress == address(0) ? owner : tokenSellerAddress;
if (token == address(0)) {
recipient.sendETHAndVerify(amount, gasleft());
} else {
token.safeTransferAndVerify(recipient, amount);
}
require(
tokenSellerAddress == address(0) ||
ITokenSeller(tokenSellerAddress).sellToken(token, lrcAddress),
"SELL_FAILURE"
);
emit TokenSold(token, amount);
}由于此函数缺乏访问控制,攻击者可以反复调用它来操纵代币价格并从套利机会中获利。
攻击详情
我们分析了一个代表性的攻击交易:0x00b2c...。攻击涉及六个关键步骤:
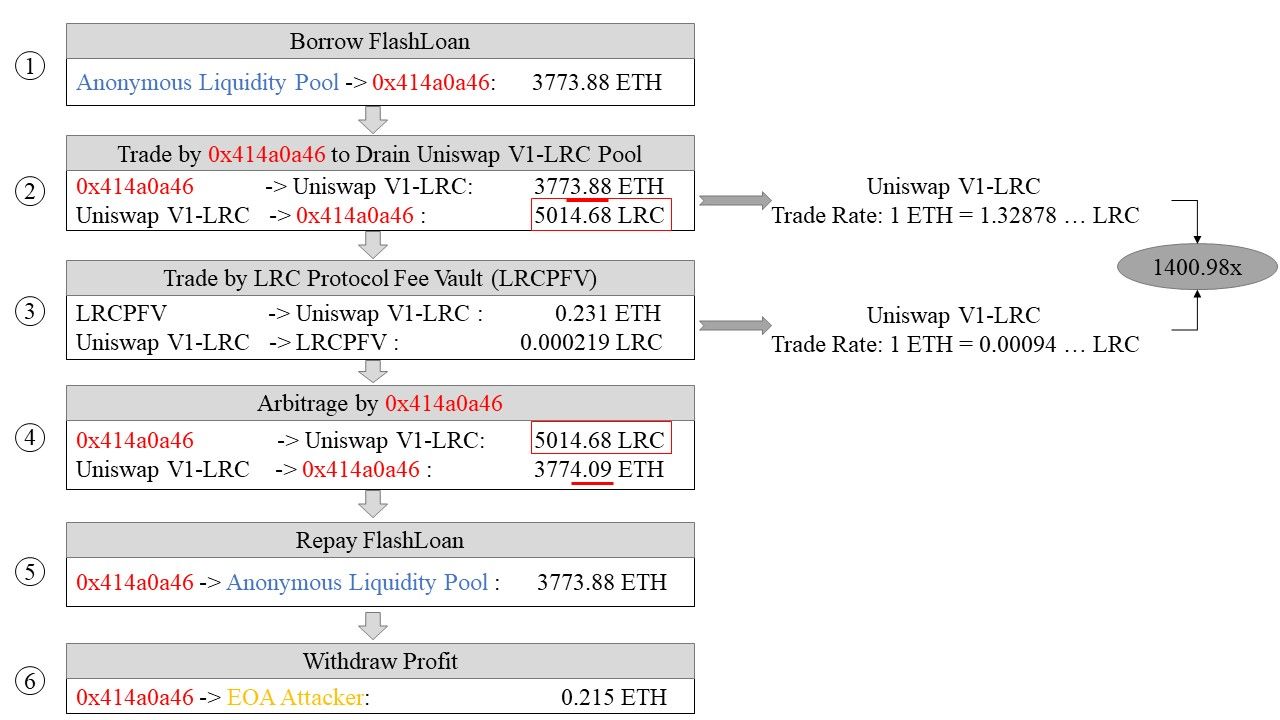
- 闪电贷: 从闪电贷提供商(
0xEB7e...)借入3,773.88 ETH。 - 初始兑换: 在Uniswap V1-LRC上将3,773.88 ETH兑换成5,014.68 LRC,汇率为1 ETH = 1.32878 LRC。
- 费用金库兑换: 通过调用有漏洞的
sellTokenForLRC函数,将LRCPFV中存储的0.231 ETH费用兑换成0.000219 LRC。此未经授权的调用操纵了Uniswap上的LRC价格,使其相对于ETH的价值急剧增加(1 ETH = 0.00094 LRC)。 - 盈利兑换: 在Uniswap V1-LRC上将5,014.68 LRC兑换回3,774.09 ETH,由于操纵的价格,额外获得了0.215 ETH。
- 贷款偿还: 偿还3,773.88 ETH的闪电贷。
- 利润转移: 将0.215 ETH的利润发送到攻击者的EOA。
此漏洞利用了闪电贷攻击,结合价格操纵和金库合约中缺乏访问控制。
攻击的影响和规模
分析的交易发生在2020年10月13日。根据CoinGecko的数据,当时LRC的价格约为0.0005175 ETH。
我们的调查发现:
- 恶意合约: 攻击者部署了3个(
0xa896...,0x414a...,0xd91d...)。 - 攻击量: 自LRCPFV部署的区块9,644,449以来,攻击者的EOA(
0x81e8...)发起了90笔交易。 - 最高利润: 一笔交易(
0x33eab...)产生了9.89 ETH的利润。 - 总利润: 约80.97 ETH(截至2020年10月1日,约合48,849美元)。
根本原因是sellTokenForLRC函数缺少访问控制,使得重复利用成为可能。
经验教训与结局
随着以太坊DeFi生态系统的发展,访问控制漏洞等安全挑战变得越来越关键。虽然引人注目的攻击常常吸引眼球,但不太显眼的漏洞也会造成重大的经济损失,正如此次事件所示。
Loopring因这次漏洞损失了约80.97 ETH,这凸显了进行严格的智能合约审计和持续安全监控的必要性。
对于DeFi协议而言,实施严格的访问控制,利用BlockSec的智能合约审计和Phalcon Security等工具,以及主动的风险管理,对于保护数字资产至关重要。
事件时间线
- 2020/11/30: ThunderForecast检测到可疑交易。
- 2020/12/01: 使用EthScope完成详细分析。
- 2020/12/02: 向Loopring团队报告漏洞。
- 2020/12/03: 确认漏洞;实施修复。
- 2020/12/03: 公开披露事件详情。
- 2021/01/03: 为该漏洞分配CVE-2020-35962。




