案件背景
2024年8月20日,一起网络钓鱼事件导致超过5400万枚稳定币DAI被盗。被盗地址是一个由Gemini资助的金库,关联的“Maker金库所有者”地址是0xf2b8。网络钓鱼者诱骗受害者(金库的原始所有者)签署一笔交易,将金库所有者更改为攻击者控制的地址,然后执行交易来清空金库。
- 钓鱼地址:0x0000db5c8b030ae20308ac975898e09741e70000
- 清空金库的地址:0x5D4b2A02c59197eB2cAe95A6Df9fE27af60459d4
- 更改所有者的交易:0x2805, 0xb721
- 清空交易:0xf700
资金流向分析
2024年8月20日,受害金库的原始所有者被诱骗签署了一笔交易,将金库所有者更改为攻击者控制的地址。大约五个小时后,攻击者发送了一笔交易,将所有权进一步更改为新的地址。在新地址获得金库的完全控制权20分钟后,它签署了一笔交易,将5500万DAI从金库转移走。
随后,在两个小时内,所有非法获得的DAI代币都被转移到攻击者控制的下游地址,而最初清空金库的地址已空无一文。直接与地址0x5D4b(即距离初始地址一个跳点)连接的下游地址共有六个。大部分DAI代币(4400万)被直接转移到下游地址,而1000万枚则兑换成原生代币(3880)ETH,然后转移到地址0x8cc5。用于兑换的DEX是CoW Protocol: GPv2Settlement。兑换交易:0x7c63。
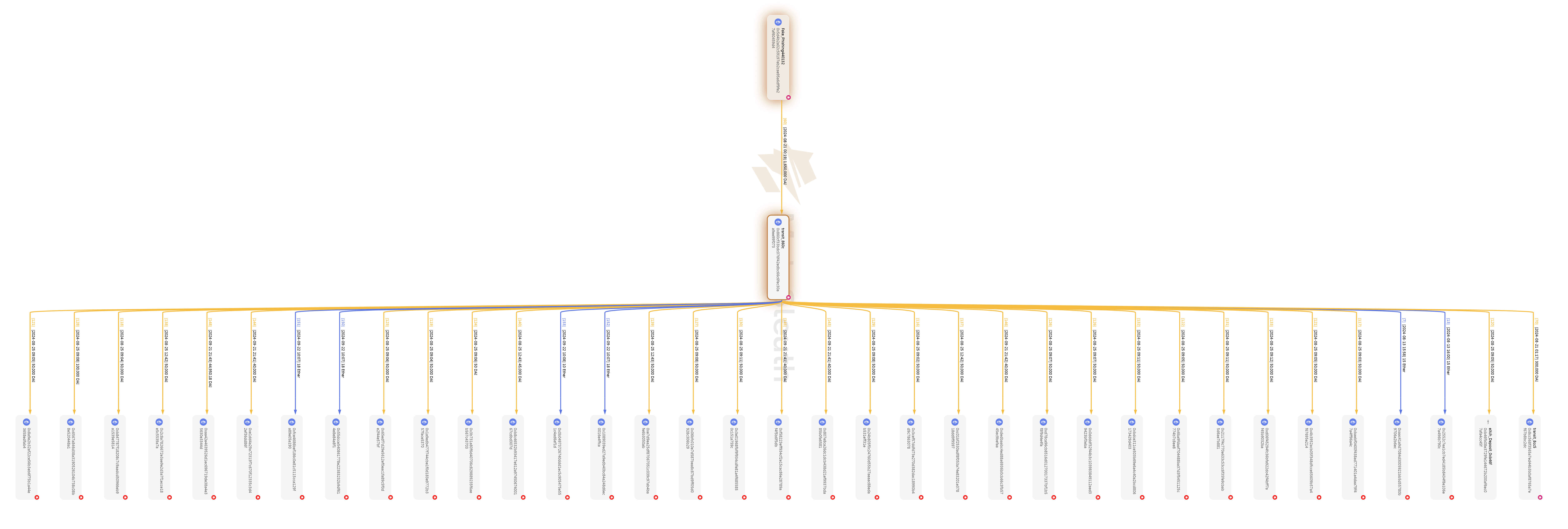
被盗DAI从原始地址0x5D4b到1跳下游地址的资金流向图。
将非法资金转移到1跳下游地址后,攻击者开始分批将资金进一步转移到更深的地址。在转移过程中,攻击者逐渐将下游地址持有的DAI兑换成ETH。在距离初始地址4跳的下游地址,所有被盗DAI已被兑换成ETH。这些非法资产以ETH的形式,随后流入中心化交易所(eXch, KuCoin, ChangeNOW)和跨链桥(THORChain, Hop Protocol)。 (点击名称即可查看这些套现地址。)将非法收益存入eXch的交易示例:0x2e42, 0xa982, 0x1e1e, 0xb7a9。将非法收益转移到THORChain的交易示例:0x5c06, 0xf824, 0x391e。
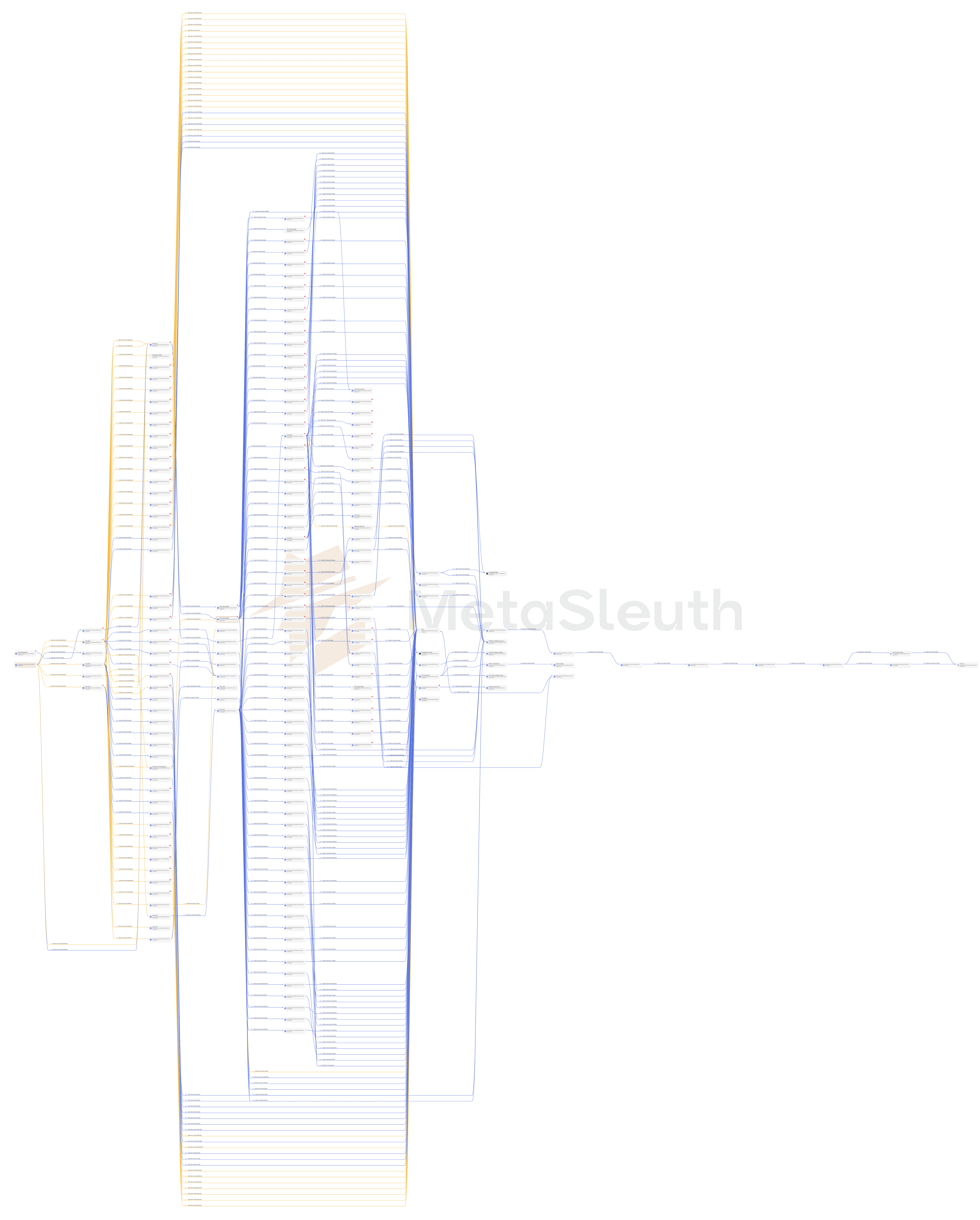
部分资金从layer2地址(距离初始地址2跳)流向layer5地址:
在将非法收益转移到深层下游地址的过程中,最长的转移路径达到了12跳,其中约8万美元被转移到交易所KuCoin 17。如下图所示的资金流向图,在2024年8月21日至8月22日期间,攻击者通过12跳路径,分批将38 ETH转移到了中心化交易所。
为了避免引起过多关注,犯罪分子倾向于将大笔资金分配到多个地址,并使用小额转账将资产转移到更深的地址。以下是一个将165万DAI拆分成36个小额转账的例子,由1跳地址0x860c处理:
部分相关地址和交易
| 地址 | 交易 | 非法资金流向 |
|---|---|---|
| 0x860cf33bdc076f42edbc66c6fec30aa9ee99f073 | 0xa11e, 0x9ef1 | 1,650,000 DAI |
| 0xdd6397104d57533e507bd571ac88c4b24852bce9 | 0x7af2, 0x1d45 | 36,733,858 DAI |
| 0x8cc568f3565a7ed44b3b0af8765a7ef67b8bc2dc | 0x7e10, 0x5d08 | 3879 ETH + 1,825,000 DAI |
| 0xca6061c6e5a7c3657297f9cc45ce110dc4d14470 | 0xee0d | 875 ETH |
| 0x77b9f7e33e42b1f64b915bb27e9a9bca199da83e | 0xf97a, 0xbc5c | 2164 ETH |
资金流向概览:
在MetaSleuth中探索详情: https://metasleuth.io/result/eth/0x5d4b2a02c59197eb2cae95a6df9fe27af60459d4?source=c81289c1-2bd9-49af-a397-e4cc71990595




