2023年2月2日,Polygon 上的 BonqDAO 遭到攻击,导致约 9860 万 BEUR 和 1.13 亿 WALBT 的损失。经调查,我们发现用于确定 WALBT 代币价格的逻辑缺陷是此次攻击的根本原因。作为一家区块链安全公司,我们密切关注此类可能对 DeFi 领域产生深远影响的攻击事件。
| 日期 | 攻击类型 | 链 | 损失金额 | 是否追回 |
|---|---|---|---|---|
| 2023/2/1 | 价格预言机依赖性缺陷 | Polygon | ~ 1.2 亿美元 | 否 |
1/ Polygon 上的 @BonqDAO 因用于确定 WALBT 代币价格的逻辑存在缺陷而遭到黑客攻击。具体而言,攻击者质押了少量 TRB 代币,随后通过 TellorPriceFeed (0x8f55) 更新了 WALBT 代币的价格,而该更新后的价格被直接使用。https://t.co/ZD7M73L0uM pic.twitter.com/4qPLqGj6jY
— BlockSec (@BlockSecTeam) 2023年2月2日
项目介绍
BonqDAO (Bonq 去中心化自治组织) 是一个部署在 Polygon 上的 DeFi 借贷平台。用户可以向该协议提供流动性或进行超额抵押借贷以赚取收益,并可以铸造与欧元挂钩的稳定币 BEUR。
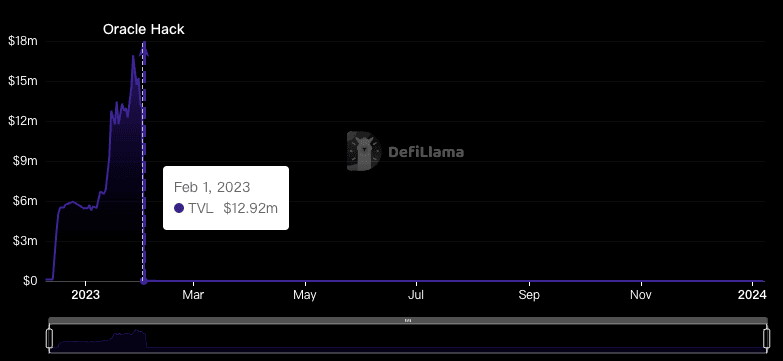
此次攻击发生后,BonqDAO 的总锁仓量 (TVL) 从 1300 万美元暴跌至 4.4 万美元,降幅达 99.66%。
BonqDAO 随后宣布 Bonq 协议已暂停,AllianceBlock 和 Bonq 团队铸造了新的 ALBT 代币并空投给受影响的用户。
攻击分析
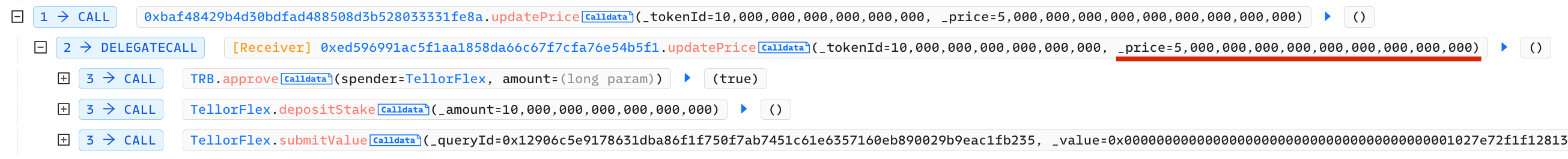
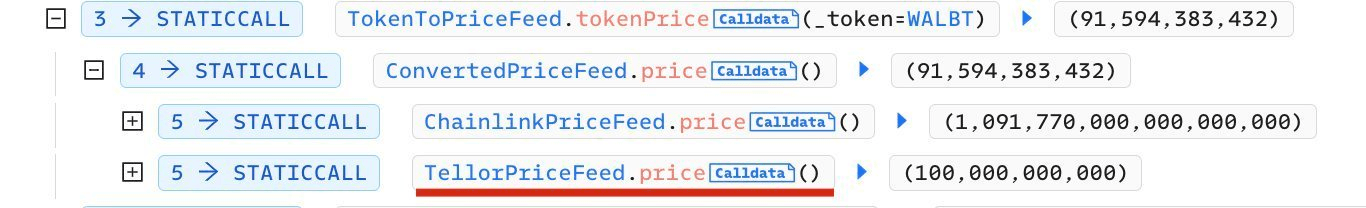
TellorFlex 是 BonqDAO 的预言机。它是去中心化的,任何人只需质押 10 个 TRB 代币即可成为价格提供者,并随意修改预言机价格。
在此次攻击中,攻击者通过两种方式获利:
- 提高 WALBT 的价格,然后借出大量的 BEUR 代币
- 降低 WALBT 的价格,然后清算其他用户的 WALBT。
攻击者的策略可归纳为以下关键步骤:
- 准备资金
- 攻击者质押了 10 个 TRB 代币,并通过
TellorPriceFeed (0x8f55)提高了 WALBT 代币的价格。
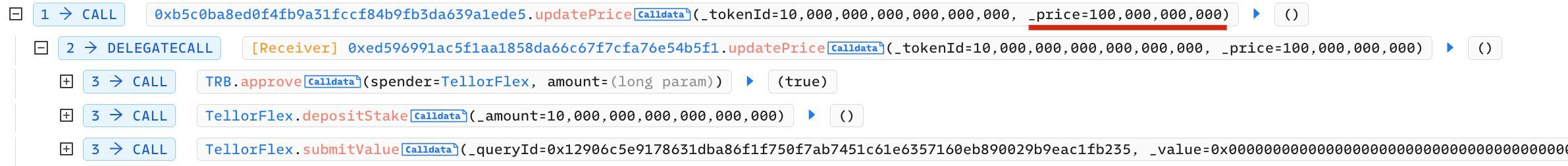
- 攻击者使用同样的方法操纵 WALBT 价格下跌,清算其他 BonqDAO 用户的 WALBT 抵押品,然后将其转售以获取额外利润。
资金追踪
作为一家致力于维护区块链安全的公司,我们也一直在密切监控这次攻击的进展。(我们的官方 Twitter 账号一直在持续报道此事,感兴趣的读者可以关注我们的账号 @BlockSecTeam 和 @MetaSleuth 来共同追踪这些资金的动向。)
MetaSleuth 是一款高性能的跨链资金流分析工具,能够增强区块链交易活动的透明度。它允许用户近乎实时地追踪受影响数字资产的踪迹。通过利用 MetaSleuth,我们可以清楚地查看在攻击发生及其后续过程中的相关资金流向信息。
- BonqDAO 攻击者的获利约为 9860 万 BEUR 和 1.13 亿 WALBT。具体而言,1.13 亿 WALBT 被销毁以解锁 ETH 链上的 1.13 亿 ALBT。约 50 万 BEUR 被兑换为 534,535 USDC,然后兑换成以太坊 (0xcacf...6642)。攻击者在他们的 Polygon 账户中仍保留了 9810 万 BEUR。
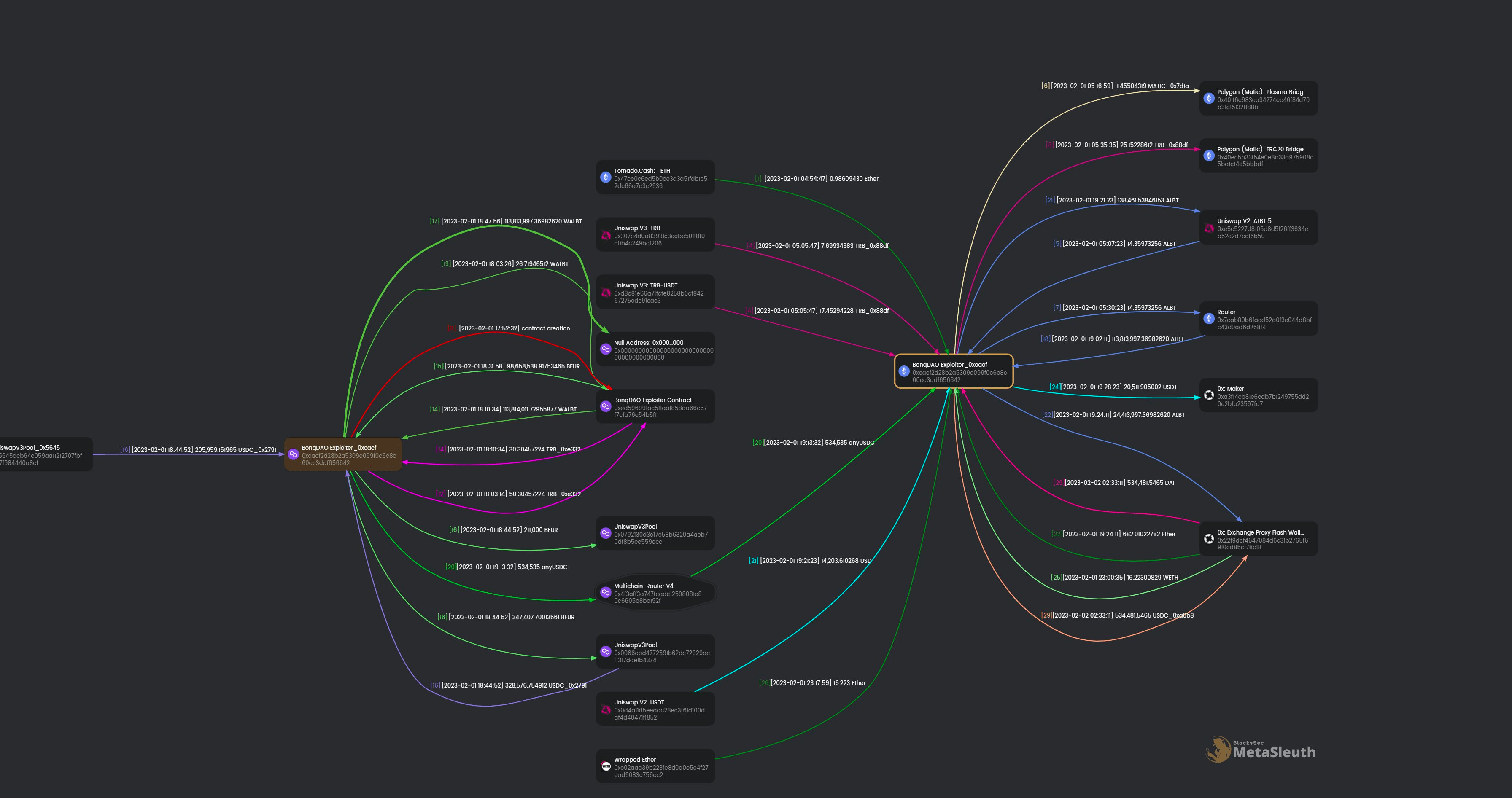
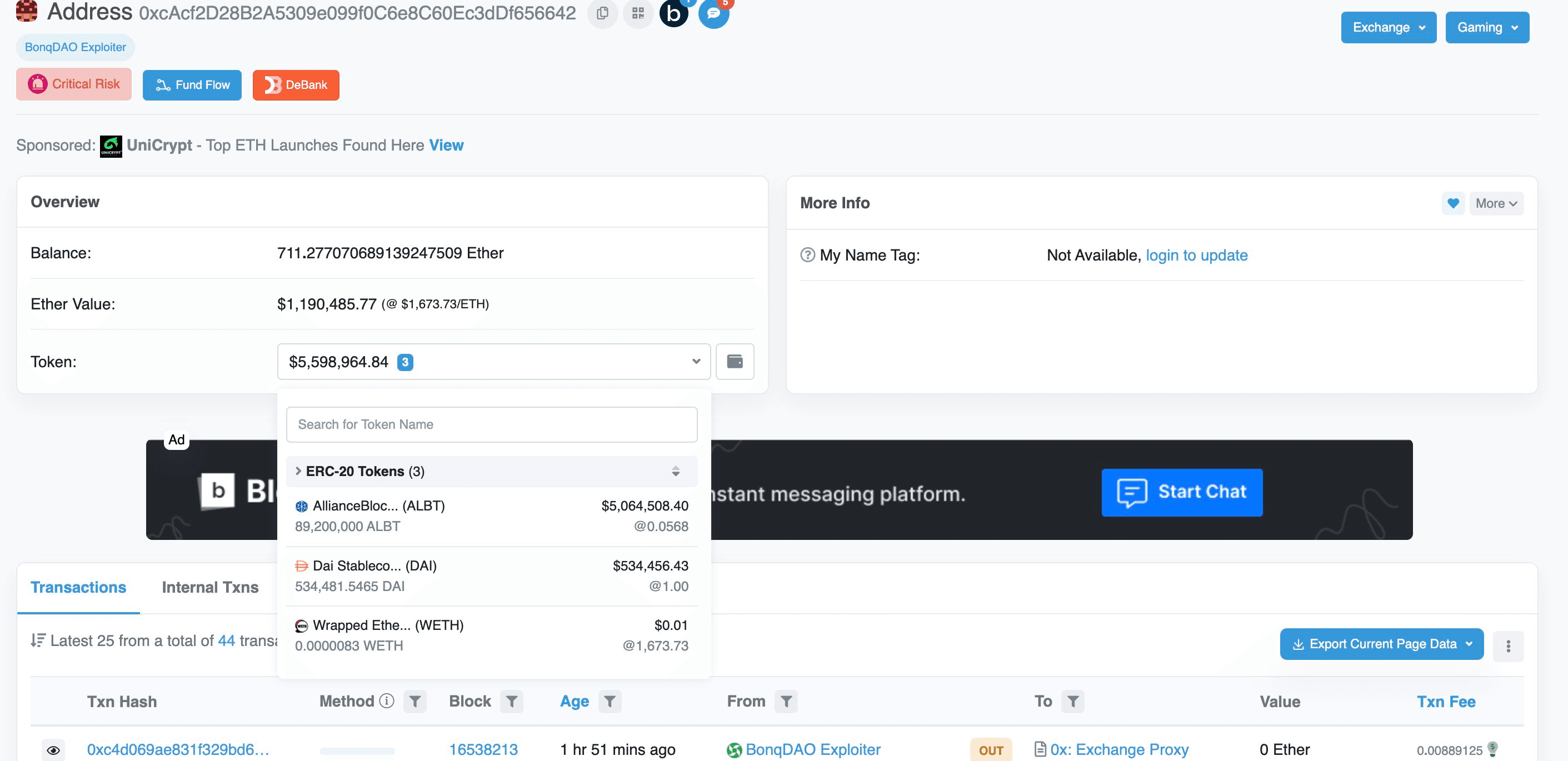
- 关于以太坊地址 0xcacf..6642 ,该地址使用 0xExchange(@0xproject) 将收到的 USDC 兑换为 DAI。此外,WALBT 也通过 0xExchange 和 Uniswap 兑换成了 ETH/USDT。该账户目前持有 711 ETH、534,481 DAI 和 8900 万 ALBT。
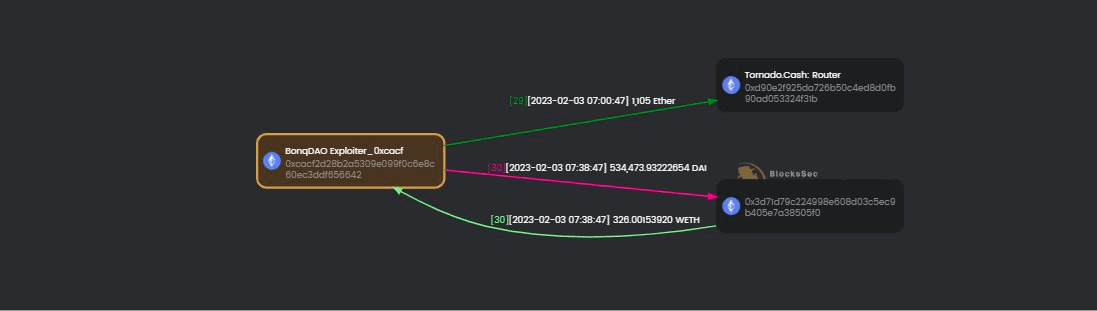
- 2023 年 2 月 3 日,我们检测到 攻击者已将 DAI 兑换为以太币,并通过 Tornado Cash 洗出 1,105 枚以太币。
总结
此次攻击的根本原因是修改 TellorFlex 预言机报价所需的抵押成本过低,而 Bonq 借贷合约中的抵押借贷额度仅与 TellorFlex 预言机报告的价格相关。因此,攻击者可以以相对较低的成本修改报价,并通过抵押借贷获得相当可观的利润。
阅读更多
以上仅为代表性案例。事实上,我们还有更多专注于区块链安全分析的案例。
关于 BlockSec
BlockSec 为区块链项目提供全栈式安全服务,协助其从项目上线前到上线后及事件响应的全过程。在开发和测试阶段,通过专家代码审计服务和 Phalcon 分叉测试平台,帮助识别潜在的安全问题。利用 BlockSec Phalcon 确保您的区块链项目在上线后拥有稳健的安全性。该精简的 SaaS 平台提供事件警报和自动拦截功能,以防止加密黑客攻击。它采用精确的攻击检测技术,扫描待定和链上交易,使您能够迅速拦截黑客。此外,MetaSleuth 是一款直观的加密资产追踪与调查平台,有助于增强资产的可追溯性和透明度。




