背景
2023年3月17日,NFT借贷平台Paraspace(现已更名为Parallel Finance)因其价格预言机中的一个漏洞遭受了重大攻击。Paraspace允许用户质押NFT和ERC-20代币作为抵押品来借入ERC-20代币,从而在不出售NFT的情况下获得收益。
ParaSpace的一个关键功能是ApeStaking,它可以自动复投APE奖励。质押APE的用户会收到cAPE代币,这是APE的cToken表示,可以作为抵押品借入USDC和WETH等资产。存入cAPE代币会获得pcAPE份额,其抵押品价值通过将pcAPE数量乘以其rebasinIndex计算得出。
rebasinIndex从总汇聚的APE余额和总份额中得出,如下面的代码片段所示:
function _scaledBalanceOf(address user, uint256 rebasingIndex)
internal
view
returns (uint256)
{
return super.scaledBalanceOf(user).rayMul(rebasingIndex);
}
function lastRebasingIndex() internal view override returns (uint256) {
return ICApe(_underlyingAsset).getPooledApeByShares(WadRayMath.RAY);
}
function getPooledApeByShares(uint256 sharesAmount)
public
view
returns (uint256)
{
uint256 totalShares = _getTotalShares();
if (totalShares == 0) {
return 0;
} else {
return
sharesAmount.mul(_getTotalPooledApeBalance()).div(totalShares);
}
}
function _getTotalPooledApeBalance()
internal
view
override
returns (uint256)
{
(uint256 stakedAmount, ) = apeStaking.addressPosition(address(this));
uint256 rewardAmount = apeStaking.pendingRewards(
APE_COIN_POOL_ID,
address(this),
0
);
return stakedAmount + rewardAmount + bufferBalance;
}_getTotalPooledApeBalance()函数将APE代币的质押量、待处理奖励以及ApeCoinStaking合约中的缓冲余额相加。
漏洞分析
该漏洞在于操纵rebasingIndex,从而人为地夸大了cAPE代币的抵押品价值。具体来说,ApeCoinStaking合约中的depositApeCoin()函数会增加某个头寸的stakedAmount。攻击者可以通过将APE代币存入cAPE头寸来利用这一点,从而夸大_getTotalPooledApeBalance()的输出,进而夸大rebasingIndex。
function depositApeCoin(uint256 _amount, address _recipient) public {
if (_amount < MIN_DEPOSIT) revert DepositMoreThanOneAPE();
updatePool(APECOIN_POOL_ID);
Position storage position = addressPosition[_recipient];
_deposit(APECOIN_POOL_ID, position, _amount);
apeCoin.transferFrom(msg.sender, address(this), _amount);
emit Deposit(msg.sender, _amount, _recipient);
}
function _deposit(uint256 _poolId, Position storage _position, uint256 _amount) private {
Pool storage pool = pools[_poolId];
_position.stakedAmount += _amount;
pool.stakedAmount += _amount.toUint96();
_position.rewardsDebt += (_amount * pool.accumulatedRewardsPerShare).toInt256();
}这种设计缺陷允许攻击者通过将cAPE作为接收者,调用depositApeCoin()存入APE代币,从而夸大抵押品价值。
攻击分析
攻击者通过五步闪电贷攻击利用了这一漏洞:
- 通过多个合约进行了一笔约47,352 wstETH的闪电贷,并提供了约46,018 wstETH以借入cAPE。
- 存入了约12,880,000 cAPE代币作为抵押品。
- 使用约1,205 wstETH交易了约492,124 APE代币,并将1,839,999 cAPE提取为APE代币。
- 通过调用
ApeCoinStaking.depositApeCoin()向cAPE头寸存入了2,332,214 APE代币,将协议的stakedAmount从851,662增加到3,183,876(增加了373%)。 - 利用夸大的抵押品借入了大量的USDC和WETH等资产以获取利润。
通过闪电贷操纵pcAPE价格,利用了预言机计算中使用的现货价格。
总结
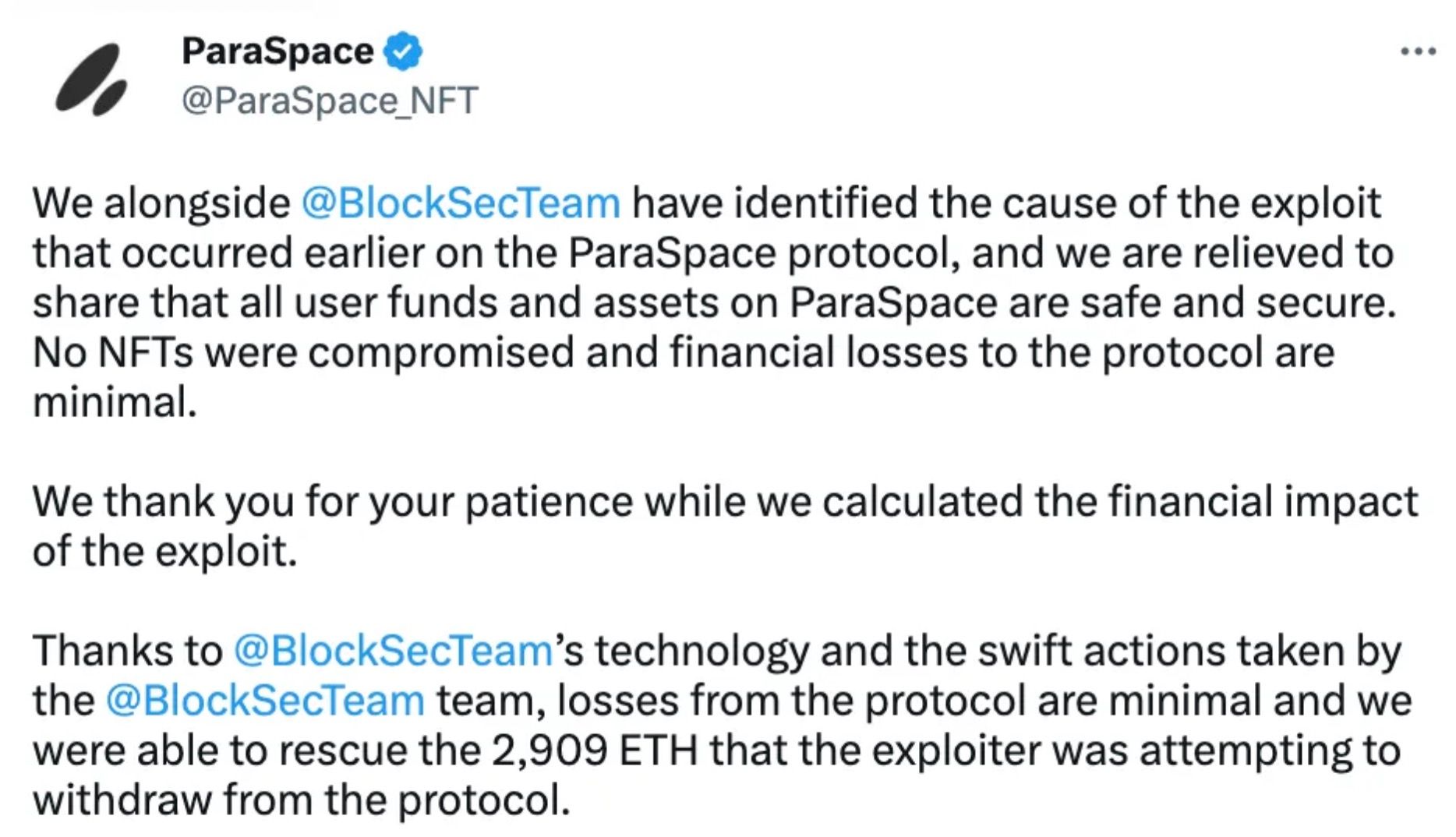
ParaSpace事件凸显了DeFi协议中预言机操纵和闪电贷攻击的风险。它强调了对健壮、抗操纵的价格预言机以及超越发布前审计的持续安全监控的迫切需求。
BlockSec的Phalcon Security系统通过自动阻止攻击并保护用户资产,展示了主动威胁检测和预防的价值。该事件提醒DeFi协议必须实施全面的安全措施,包括智能合约审计、基础设施审计和实时监控。
如需了解更多DeFi安全事件和最佳实践,请浏览我们的安全事件库,并考虑我们的智能合约审计和基础设施审计服务。
阅读本系列的更多文章:
- 导语:2023年十大“惊人”安全事件
- 第一篇:利用Flashbots Relay中的漏洞收割MEV机器人
- 第二篇:Euler Finance事件:2023年最大规模的黑客攻击
- 第三篇:KyberSwap事件:精湛地利用舍入错误
- 第四篇:Curve事件:编译器错误生成了错误的字节码
- 第五篇:Platypus Finance:经受住三次攻击
- 第六篇:Hundred Finance事件:与精度相关的漏洞
- 第八篇:SushiSwap事件:一次笨拙的救援尝试
- 第九篇:MEV机器人0xd61492:从捕食者到猎物
- 第十篇:ThirdWeb事件:可信模块之间的不兼容性
Web3最佳安全审计师
在上线前验证设计、代码和业务逻辑



