To address the core challenges faced by Web3 security professionals in blockchain transaction analysis, BlockSec conducted in-depth research with 100+ participants across 20+ countries, collecting 2,000+ qualified survey responses. Respondents included security researchers, developers, and on-chain analysis traders, representing diverse perspectives. Based on these insights, BlockSec has officially released the new version of Phalcon Explorer, our flagship blockchain transaction analysis tool. This upgrade delivers a more efficient, intuitive, and professional experience for global users.
A Benchmark Tool for blockchain transaction analysis
As BlockSec’s flagship on-chain analysis product, Phalcon Explorer has become an essential tool for Web3 practitioners worldwide, thanks to 3 core advantages:
-
Broad Chain Coverage
-
Supports 26+ major EVM-compatible chains including Ethereum, BSC, Polygon, Arbitrum, and Avalanche, as well as non-EVM chains such as Solana—meeting multi-ecosystem analysis needs.
-
Professional Use Cases
-
Serves core scenarios such as transaction trace analysis, transaction simulation, and smart contract debugging, enabling professionals to work faster and with greater precision.
-
Global Recognition
-
Trusted by 100,000+ global users across 160+ countries and regions, with 50K+ daily active users.
Three Core Modules
1. Invocation Flow
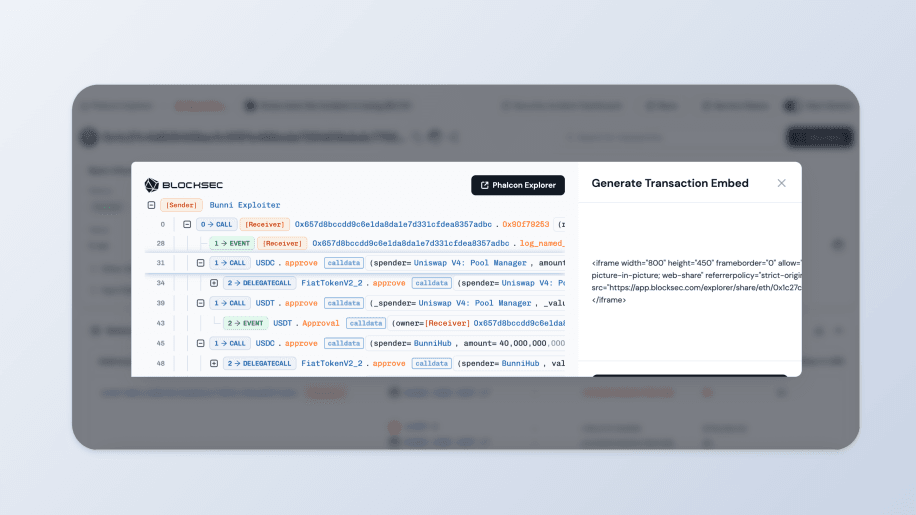
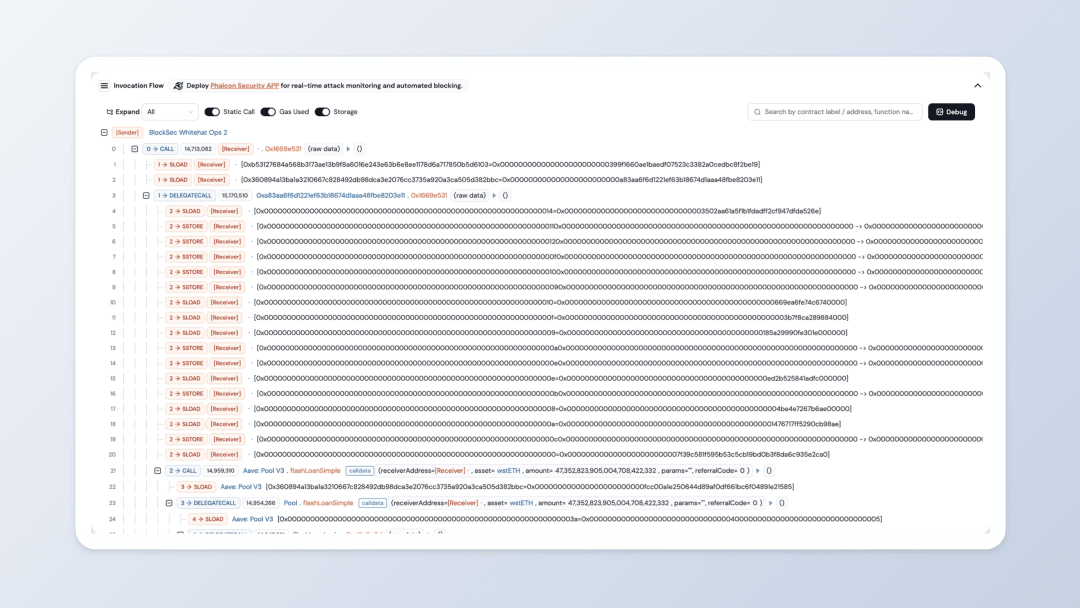 The Invocation Flow module provides a tree-structured view of function calls (call trace), making transaction logic clear at a glance. New upgrades include:
The Invocation Flow module provides a tree-structured view of function calls (call trace), making transaction logic clear at a glance. New upgrades include:
-
One-Click Expansion: Instantly view full data such as call parameters, return values, and gas usage, improving efficiency.
-
Cross-Module Tag Synchronization: Custom address labels (e.g., “hacker address,” “project multisig”) now sync across other modules, ensuring smoother analysis.
Additional features include Static Call toggling, Gas Used filtering, and one-click raw data copying—enabling even complex transactions like flash loan analysis or cross-chain transaction analysis to be understood easily.
2. Debugger
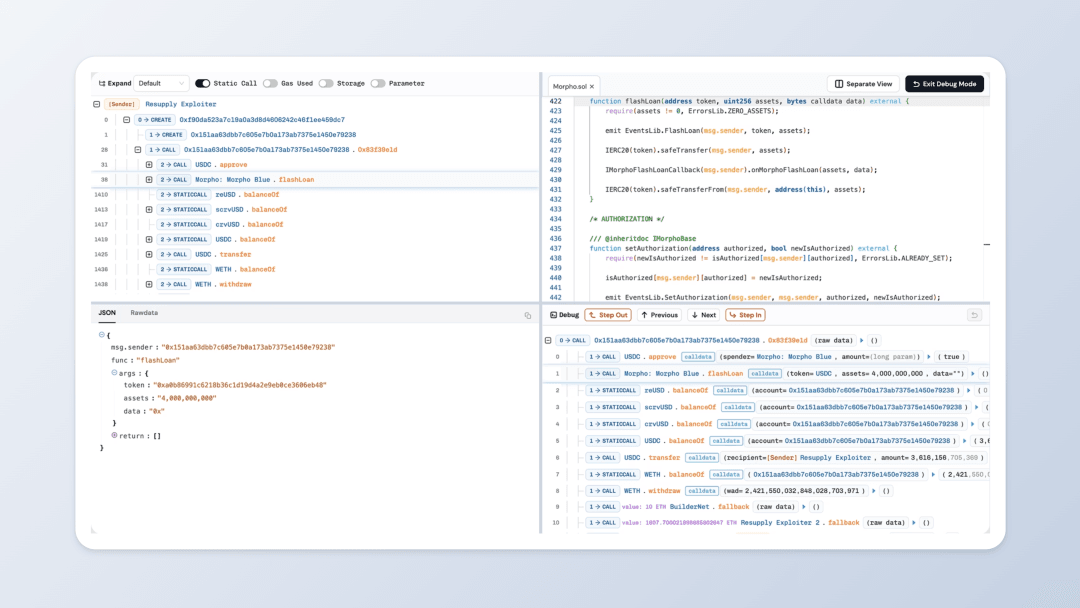 Built for developers, the Debugger links smart contract source code with transaction traces for deeper EVM transaction analysis.
Built for developers, the Debugger links smart contract source code with transaction traces for deeper EVM transaction analysis.
-
Dual-Screen Mode: For users with multiple monitors, view contract code and transaction flows simultaneously for double efficiency.
-
One-Click Debug Navigation: Jump directly from any invocation step to the exact source code line executed—saving significant debugging time.
-
Full Data Display: View traces, source code, logs, parameters, and return values in sync, even for complex transactions with 4,000+ internal calls.
3. Simulator
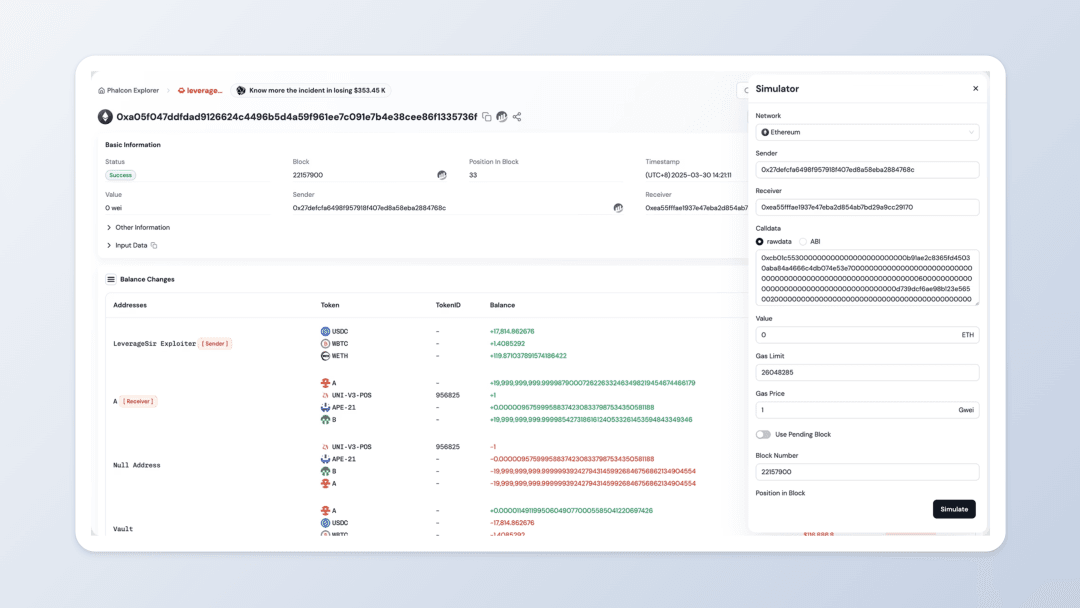 The Simulator serves as an “on-chain sandbox” for traders and developers, allowing strategy testing without executing live transactions.
The Simulator serves as an “on-chain sandbox” for traders and developers, allowing strategy testing without executing live transactions.
-
Multi-Scenario Simulation: Run simulations from any address, at any block height, or with modified function parameters (e.g., transfer amounts, contract addresses).
-
ABI Auto-Parsing: Automatically load and parse ABIs (ABI parsing) or upload them manually, supporting analysis of non-open-source contracts.
-
Case Library for Fast Learning: Includes popular examples such as “TokenSwap” and “ParaSpace Whitehat Rescue” for quick replication and learning.
New Features
This upgrade also introduces several powerful new functions:
-
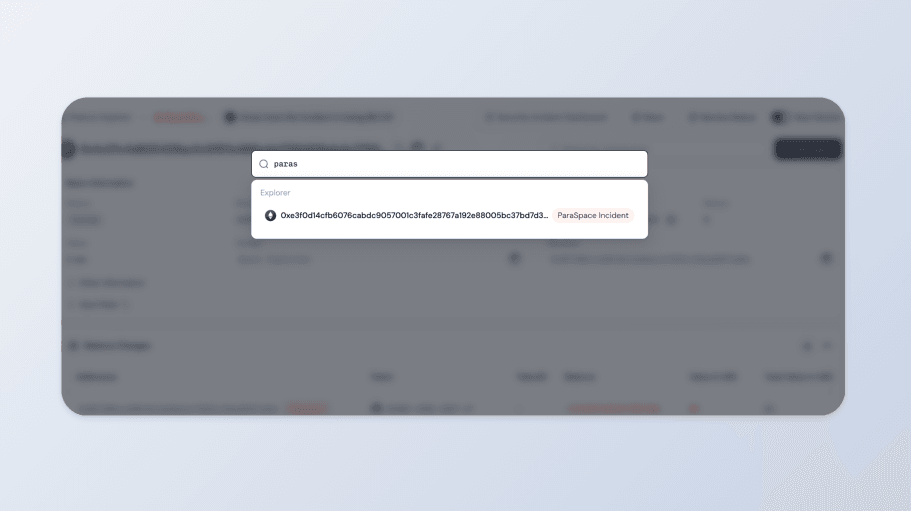
Fuzzy Search (fuzzy search tx hash)
-
Search using partial tx hashes or keywords (e.g., multisig identifiers). The system auto-suggests best matches.
-
Event-Based Search (event-based search)
-
Type in event names (e.g., “ParaSpace Exploit” or “Flash Loan Attack”) to find all related transactions. A new History & Examples section has been added.
-
Sharing Features
-
Share an entire transaction card with a link for social media, or share a specific function call line so teammates can jump directly to a key step.
-
Custom Time Zones
-
Select from 24 major global time zones (UTC, Beijing, New York, etc.). Timestamps will automatically adjust, solving cross-region collaboration pain points.
-
Extended Chain Support
-
New chains have been added, with more available on request via official channels.
User-Centric and Professionally Enhanced
Since launch, Phalcon Explorer has been driven by one mission: solve the pain points of Web3 security analysis. This new release represents not just a functional upgrade, but also a double focus on user experience and professional capabilities.
Going forward, BlockSec will continue improving features, expanding chain coverage, and deepening transaction trace analysis based on user feedback and industry trends—empowering global Web3 security professionals to build a safer and more trustworthy blockchain ecosystem.
Try the New Phalcon Explorer ⚡
👉 Visit the official landing page: https://blocksec.com/explorer
💬 Join our Telegram: https://t.me/BlockSecTeam
🐦 Follow Phalcon on Twitter: https://x.com/Phalcon_xyz




