On May 22, 2025, Cetus Protocol, the largest concentrated-liquidity DEX on Sui, suffered a catastrophic exploit that drained liquidity across multiple pools, resulting in an estimated ~$223 million in losses. This incident stands as the largest DeFi hack of 2025, highlighting critical vulnerabilities in smart contract security, particularly concerning fixed-point arithmetic.
The exploit originated from a flaw in a custom overflow-prevention function, checked_shlw(). Due to an incorrect constant and comparison, this function failed to detect unsafe conditions before performing a left shift used in fixed-point u256 math. This oversight enabled a silent truncation of the most significant bits during crucial delta calculations, such as determining the token input required for a given liquidity. By carefully manipulating parameters like liquidity size and tick/price-range settings, the attacker could trick the protocol into computing a required deposit of essentially 1 unit of token, while simultaneously crediting their position with an enormous amount of liquidity. With this inflated position recorded on-chain, the attacker then removed liquidity and withdrew real reserves, effectively draining the pools.
Understanding Concentrated Liquidity and Fixed-Point Math
Cetus Protocol utilizes a concentrated liquidity market maker (CLMM) design, a sophisticated approach where liquidity providers (LPs) supply assets only within a chosen price range (a tick interval). Unlike traditional AMMs that distribute liquidity uniformly, CLMMs allow LPs to concentrate capital between specific lower and upper bounds. This design significantly improves capital efficiency but introduces a heavy reliance on precise fixed-point math for converting between:
- The liquidity amount credited to a position.
- The actual token amounts that must be deposited or can be withdrawn.
When a user adds liquidity, the protocol calculates the token deltas (how much underlying tokens are required) based on the current price and the selected range. Conversely, when liquidity is removed, the inverse calculation determines the amount of assets the position is entitled to withdraw.
The core vulnerability in the Cetus Incident exploited this intricate relationship: if the "how much you must deposit" calculation could be manipulated to be too small, while the position was still credited with large liquidity, an attacker could later remove that credited liquidity to withdraw real reserves from the pool. This highlights a common attack vector in DeFi protocols involving complex mathematical operations.
The Critical u256 Shift Vulnerability
The root cause of this massive DeFi hack was a bug within a helper function designed to safely perform a left-shift, a common operation in fixed-point u256 arithmetic (typically << 64 to apply a 2^64 scaling factor). In Move-based systems like Sui, overflow checks are not uniformly enforced across all operations, making manual safeguards for bit shifting crucial.
Cetus implemented an overflow-prevention helper, checked_shlw(), to verify whether shifting a u256 value left by 64 bits would exceed the 256-bit boundary. However, due to an incorrect constant and comparison, this critical check could be bypassed for certain large inputs that should have been rejected.
Specifically, the get_delta_a function, responsible for computing the amount of underlying tokens (Token A) required for liquidity provision between two prices (sqrt_price_0 and sqrt_price_1), calls checked_shlw(). The purpose of checked_shlw() here is to ensure the numerator in the Token A calculation does not overflow when shifted.
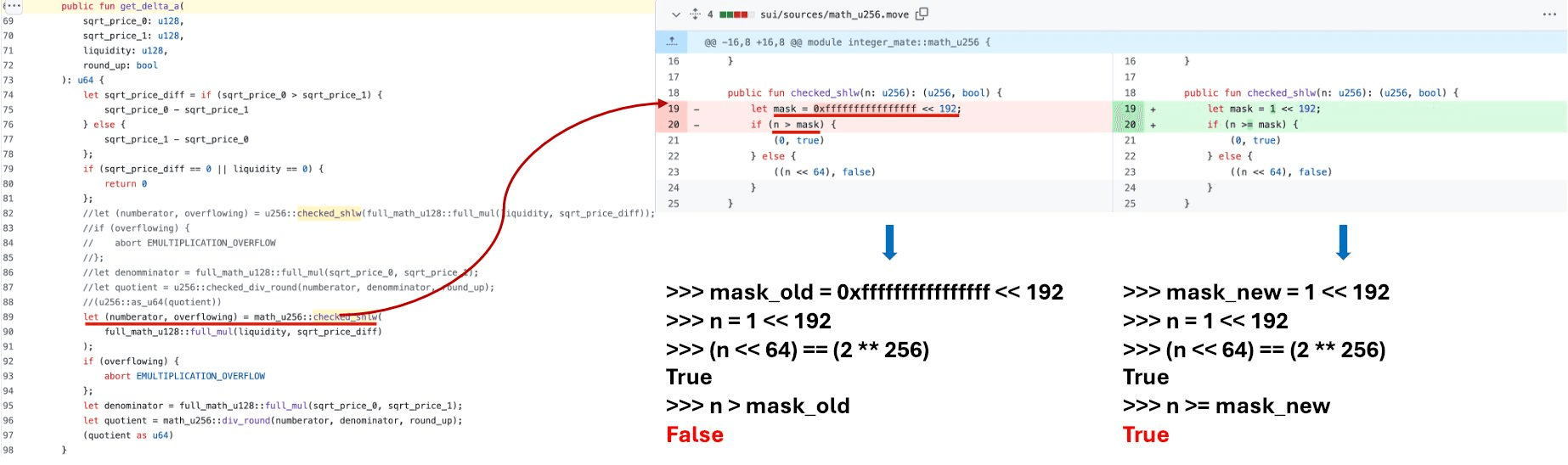
The flaw lay in checked_shlw()'s overflow check, which used a mask of 0xffffffffffffffff << 192 (equivalent to 2^256 - 2^192). This mask is significantly larger than the correct threshold. Consequently, an input value greater than 2^192 but smaller than this erroneous mask could pass the check, even though shifting it left would indeed exceed the u256 range. The subsequent left shift then resulted in a silent truncation, producing an incorrect and significantly smaller value.
The figure below illustrates the difference between the vulnerable implementation and the patched version. The correct boundary should have been 1 << 192, not the much larger 0xffffffffffffffff << 192. The attacker ingeniously exploited this flawed check to mint an unusually large amount of LP tokens while depositing a minimal amount, such as 1 wei of Token A.
Anatomy of the Cetus DeFi Hack
While the attacker applied the same technique across multiple pools, the underlying attack flow remained consistent. Let's analyze a specific transaction to understand the steps involved in this sophisticated blockchain security breach.
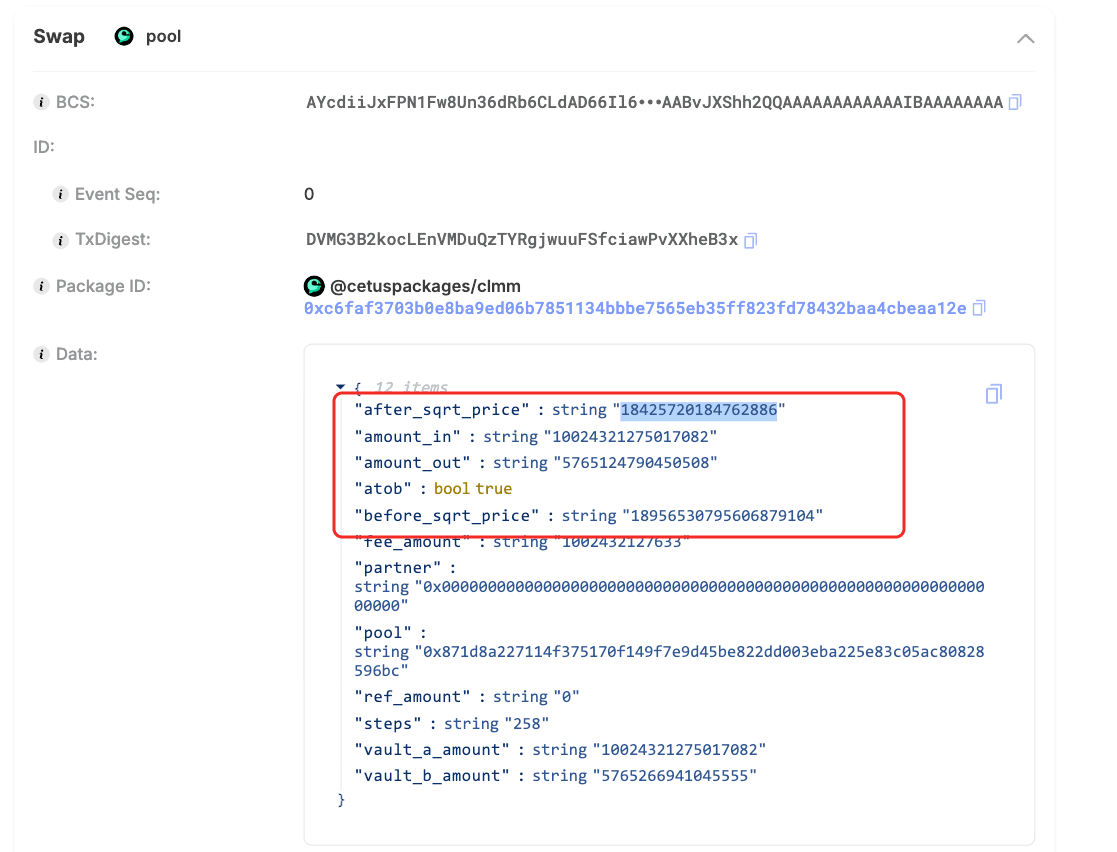
1. Manipulate the Pool Price with a Flashloan
The attack began with the attacker utilizing a flashloan to rapidly acquire 10,024,321.28 haSUI. They then swapped out 5,765,124.79 SUI, intentionally driving the pool price down from 18,956,530,795,606,879,104 to 18,425,720,184,762,886. This strategic price movement was crucial, as it allowed the attacker to open a CLMM position that required only a minimal amount of one token, leveraging the "single-sided / nearly single-token" liquidity behavior inherent in concentrated liquidity designs.
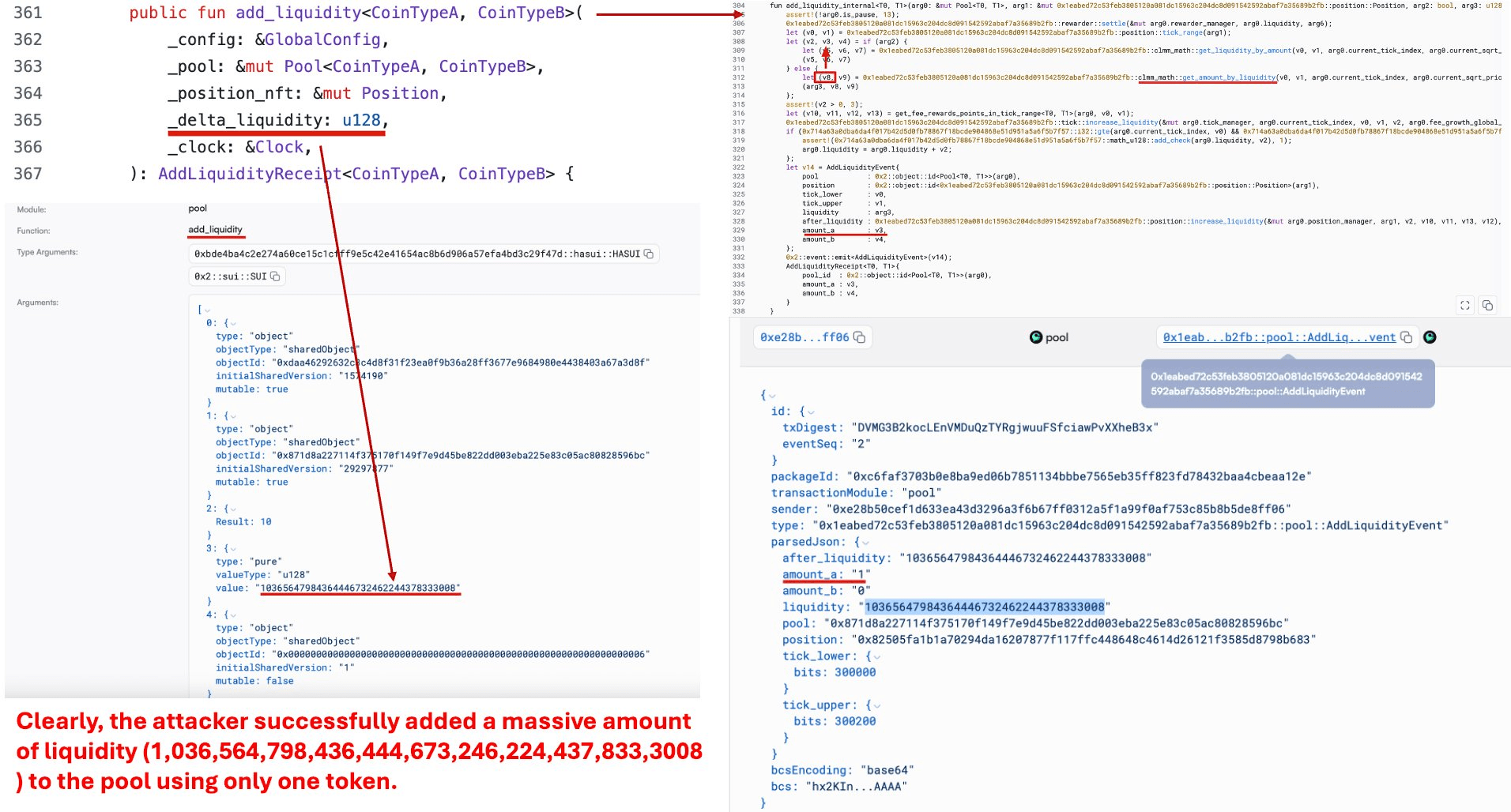
2. Add Liquidity with an "Almost Free" Deposit
Next, the attacker selected a very tight tick range (e.g., 300000–300200) and precisely tuned the target liquidity. In CLMM systems, token delta calculations are highly dependent on the square-root prices at the range boundaries, and narrow ranges can make certain intermediate values extremely sensitive to small changes.
By carefully tuning these parameters, the attacker caused an internal multiplication to produce a u256 intermediate value. This value should have overflowed when left-shifted, but it successfully passed the flawed checked_shlw() guard. As a direct consequence of the unsafe shift-induced truncation, the protocol calculated the required Token A amount as effectively 1 unit, while simultaneously minting and recording the position with a massive amount of liquidity (i.e., 10,365,647,984,364,446,732,462,244,378,333,008).
3. Remove Liquidity to Extract Real Reserves
With an on-chain position that falsely appeared to hold inflated liquidity, the attacker proceeded to remove liquidity and withdraw assets as if the position had been properly funded. This critical step is where the pool’s real reserves were systematically drained, leading to the substantial $223 million loss.
4. Repeat Across Multiple Pools
After successfully validating the exploit primitive, the attacker replicated the same workflow across multiple pools, rapidly compounding the total losses and executing one of the largest DeFi hacks to date.
Best Security Auditor for Web3
Validate design, code, and business logic before launch
Key Takeaways and Blockchain Security Lessons
The Cetus Incident serves as a stark reminder of the intricate challenges in blockchain security, especially within complex DeFi protocols. The root cause was a faulty overflow check around a u256 left shift in the fixed-point math path. This allowed an overflowed shift to silently truncate high bits, making the required deposit appear near-zero while still crediting an LP position with massive liquidity, ultimately enabling reserve extraction.
Lessons Learned for Smart Contract Security:
- Strictness in Arithmetic: Be exceptionally rigorous when dealing with shifts, scaling factors, rounding, and boundary conditions in fixed-point arithmetic. These are common sources of critical vulnerabilities.
- Proven Primitives: Prioritize the use of proven safe-math primitives or formalized invariants over developing ad-hoc helper functions. If custom helpers are necessary, validate their constants and thresholds with extreme care.
- Comprehensive Testing: Implement extensive edge-case and property-based tests to cover maximum values, boundary ticks, and adversarial parameter combinations. This proactive approach can uncover subtle flaws before deployment.
- Continuous Monitoring: Even with robust audits, real-time monitoring solutions are crucial. Tools like BlockSec's Phalcon Security can detect suspicious on-chain activities and potential exploits in progress, offering a vital last line of defense.
The Cetus Incident underscores the importance of a multi-layered approach to blockchain security, combining meticulous code review, advanced testing methodologies, and continuous on-chain monitoring to safeguard against sophisticated DeFi hacks.
Reference
About BlockSec
BlockSec is a full-stack blockchain security and crypto compliance provider. We build products and services that help customers to perform code audit (including smart contracts, blockchain and wallets), intercept attacks in real time, analyze incidents, trace illicit funds, and meet AML/CFT obligations, across the full lifecycle of protocols and platforms.
BlockSec has published multiple blockchain security papers in prestigious conferences, reported several zero-day attacks of DeFi applications, blocked multiple hacks to rescue more than 20 million dollars, and secured billions of cryptocurrencies.
- Official website: https://blocksec.com/
- Official Twitter account: https://twitter.com/BlockSecTeam





