We are thrilled to announce the integration of Solana into MetaSleuth, our comprehensive tracking and investigation platform!
As the Solana ecosystem expands, we recognize the need for robust tools to navigate and analyze its blockchain. With Solana now live on MetaSleuth, users can effortlessly explore Solana, track funds and DYOR, and share valuable insights with others.
The Integration of Solana on MetaSleuth
Solana sets itself apart from other blockchains, such as Ethereum, with its innovative approach to data storage and management. Notably, Solana's design of token accounts offers unique advantages. To provide users with clear analysis and insights into token funds on MetaSleuth, we have implemented special design elements:
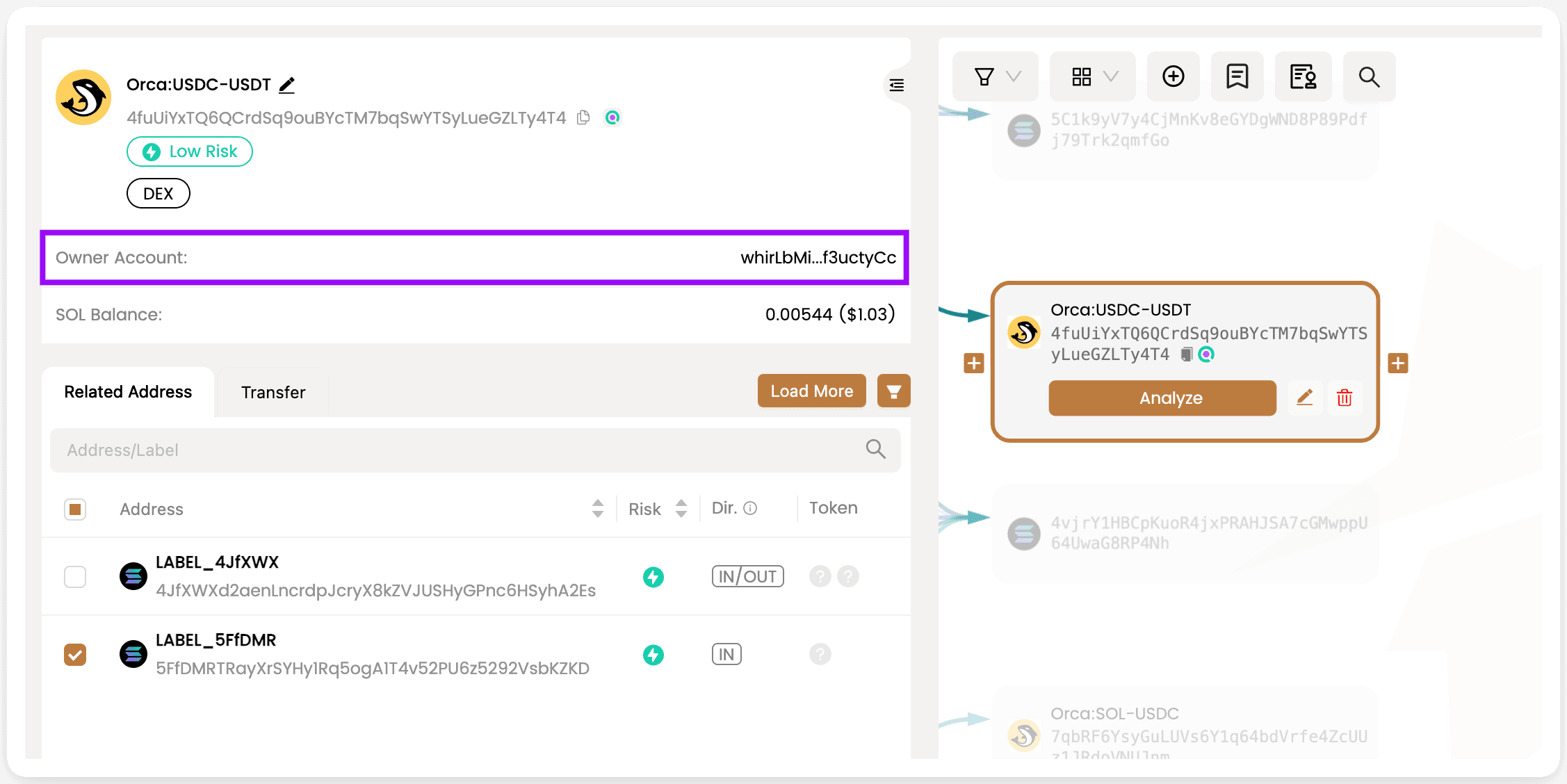
- Owner account information for Solana accounts is now included and can be accessed in the address panel.
-
To maintain clarity and prevent overwhelming users with individual token account details, we have chosen not to display token accounts on the MetaSleuth canvas.
-
Instead, when users input a token account for analysis, we provide a focused approach. For example, when analyzing the account '2bx7rHMpDUthvur8qnUJN9dNUsjKVE9S6tN16B78FoRG,' which is the USDC token account owned by 'Solend main Pool Vault,' we offer a clear view of the USDC fund flow of the vault. This tailored analysis enables a deeper understanding of fund movement within the Solana ecosystem.
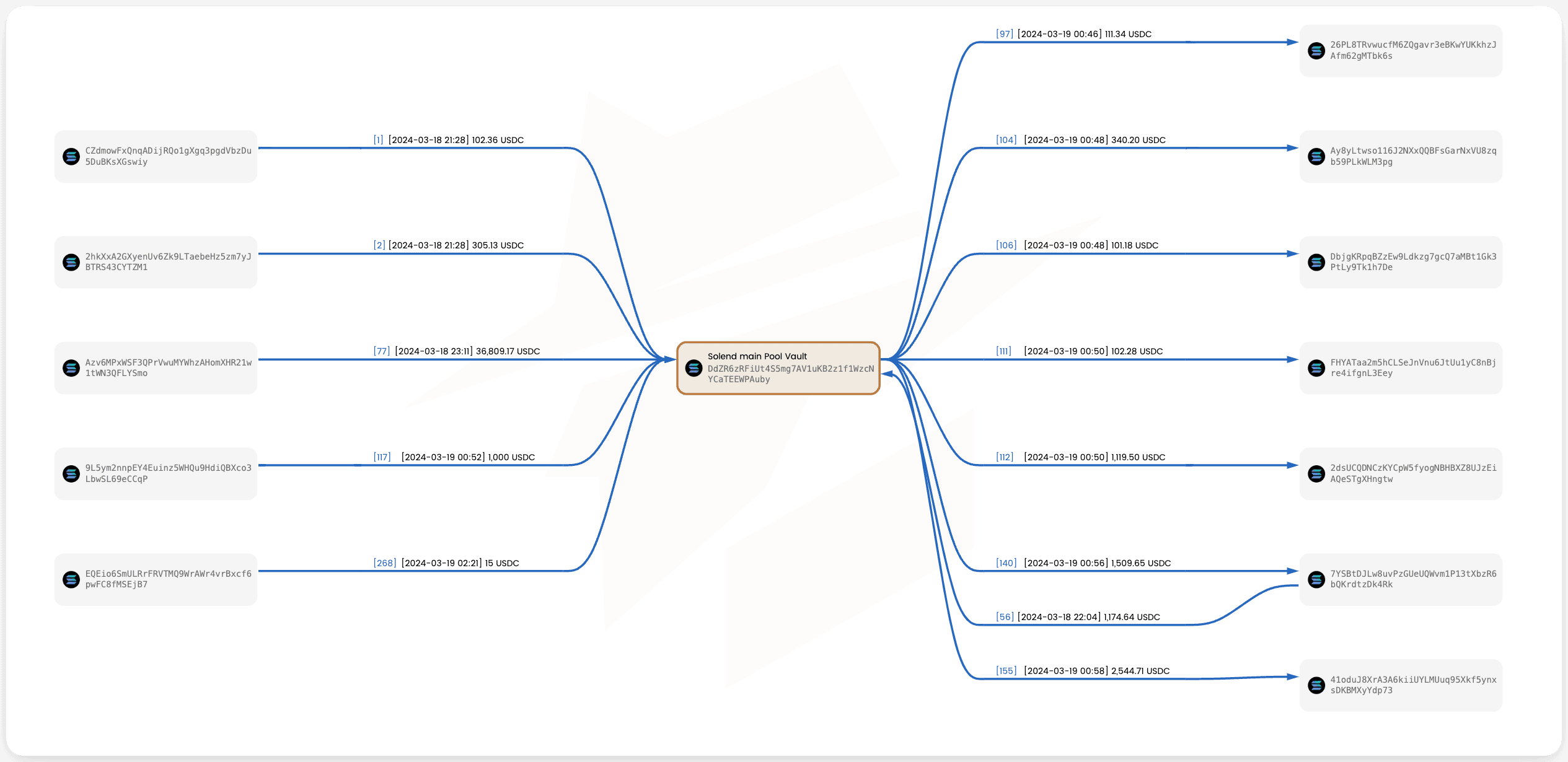
These optimized designs enhance clarity and provide users with precise analyses of token funds on Solana within the MetaSleuth platform. Try it out for yourself at: https://metasleuth.io/result/solana/2bx7rHMpDUthvur8qnUJN9dNUsjKVE9S6tN16B78FoRG
Case Study : The Slope Wallet Hack Incident
In August 2022, a significant incident occurred where over 8,000 Solana wallets were drained, resulting in losses of approximately $5.2 million. The attacker's profits were distributed across four different accounts:
GeEccGJ9BEzVbVor1njkBCCiqXJbXVeDHaXDCrBDbmuy
5WwBYgQG6BdErM2nNNyUmQXfcUnB68b6kesxBywh1J3n
CEzN7mqP9xoxn2HdyW6fjEJ73t7qaX9Rp2zyS6hb3iEu
Htp9MGP8Tig923ZFY7Qf2zzbMUmYneFRAhSp7vSg4wxV
To initiate the investigation, open a new chart with an empty canvas in the "Saved Charts/Shared Links" panel. Add the four attacker accounts to the canvas, and for each account, click on "Expand Outgoing" to trace the destination of the stolen funds. It appears that the attacker held the funds for several months before initiating transfers and laundering activities from March 2023 onwards.
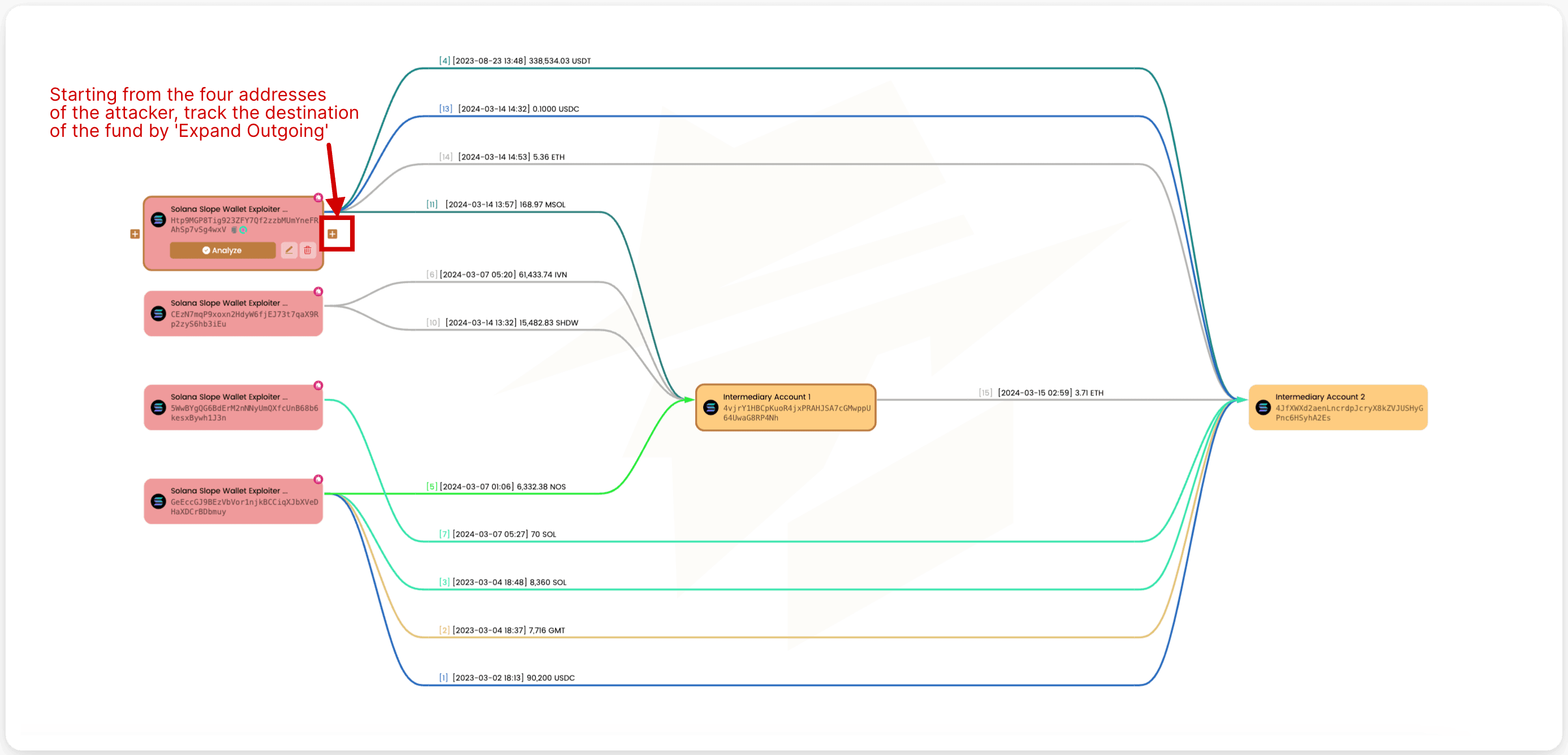
The account 4JfXWX, the majority of the funds, which were subsequently swapped and transferred further. As of today, a significant amount of funds still remains untransferred in this account.
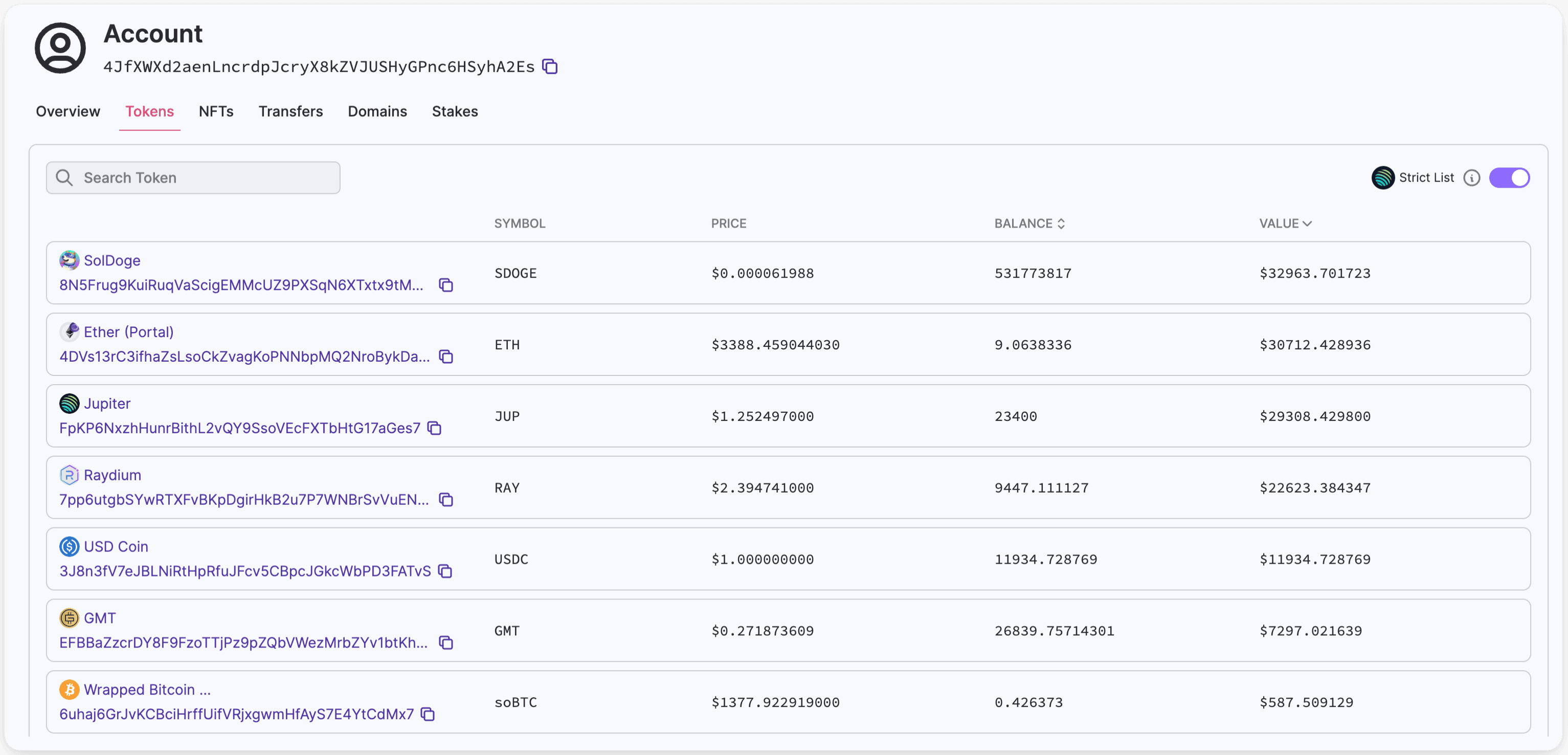 https://solana.fm/address/4JfXWXd2aenLncrdpJcryX8kZVJUSHyGPnc6HSyhA2Es/transactions
https://solana.fm/address/4JfXWXd2aenLncrdpJcryX8kZVJUSHyGPnc6HSyhA2Es/transactions
With all USDT tokens having been transferred out of the account, our priority lies in tracking the subsequent transfers of USDT as they may provide crucial clues. Further investigation has uncovered that the funds were sent to Binance. Upon further analysis, it turns out that the attacker leveraged an Instant Cryptocurrency Exchange service that relied on Binance to execute the transfer of funds to another blockchain. For ongoing investigation, you can match corresponding transactions based on the information obtained from the Instant Cryptocurrency Exchange. For more details, refer to this tweet:
https://twitter.com/zachxbt/status/1711748033954590900
 https://metasleuth.io/result/solana/GeEccGJ9BEzVbVor1njkBCCiqXJbXVeDHaXDCrBDbmuy?source=ff950aab-a7a2-4bd0-a3b0-efb4c60a5a63
https://metasleuth.io/result/solana/GeEccGJ9BEzVbVor1njkBCCiqXJbXVeDHaXDCrBDbmuy?source=ff950aab-a7a2-4bd0-a3b0-efb4c60a5a63
Don't hesitate, come and try it out now!
About MetaSleuth
MetaSleuth is a comprehensive platform developed by BlockSec to assist users in effectively tracking and investigating all crypto activities. With MetaSleuth, users can easily track funds, visualize fund flows, monitor real-time fund movements, save important information, and collaborate by sharing their findings with others. Currently, we support 13 different blockchains, including Bitcoin (BTC), Ethereum (ETH), Tron (TRX), Polygon (MATIC), and more.
Website: https://metasleuth.io/
Twitter: @MetaSleuth
Telegram: https://t.me/MetaSleuthTeam




