2026年2月22日,在Stellar的Blend V2上由YieldBlox DAO运营的一个借贷池遭到利用,导致损失超过1000万美元。
攻击者操纵了SDEX上的USTRY/USDC市场。该池配置的Reflector预言机路径随后接受了被操纵的价格,高估了USTRY的抵押品价值,并使攻击者能够提取池中的资产(USDC和XLM)。
此次事件并非Blend V2核心合约问题,而是池操作者(YieldBlox DAO)的配置问题。
2. 背景
在Stellar上,Blend V2是一个允许用户创建隔离借贷池的流动性协议。每个池定义了自己的借款资产、抵押资产和预言机设置。
在此次事件中,受影响的池允许用户使用USTRY作为抵押品借入XLM和USDC。该池使用了Reflector预言机[2],USTRY的价格来自SDEX上的USTRY/USDC市场[3],并定期更新。
3. 漏洞分析(根本原因分析)
此次利用的根本原因是池侧定价设计依赖于一个可操纵的市场。
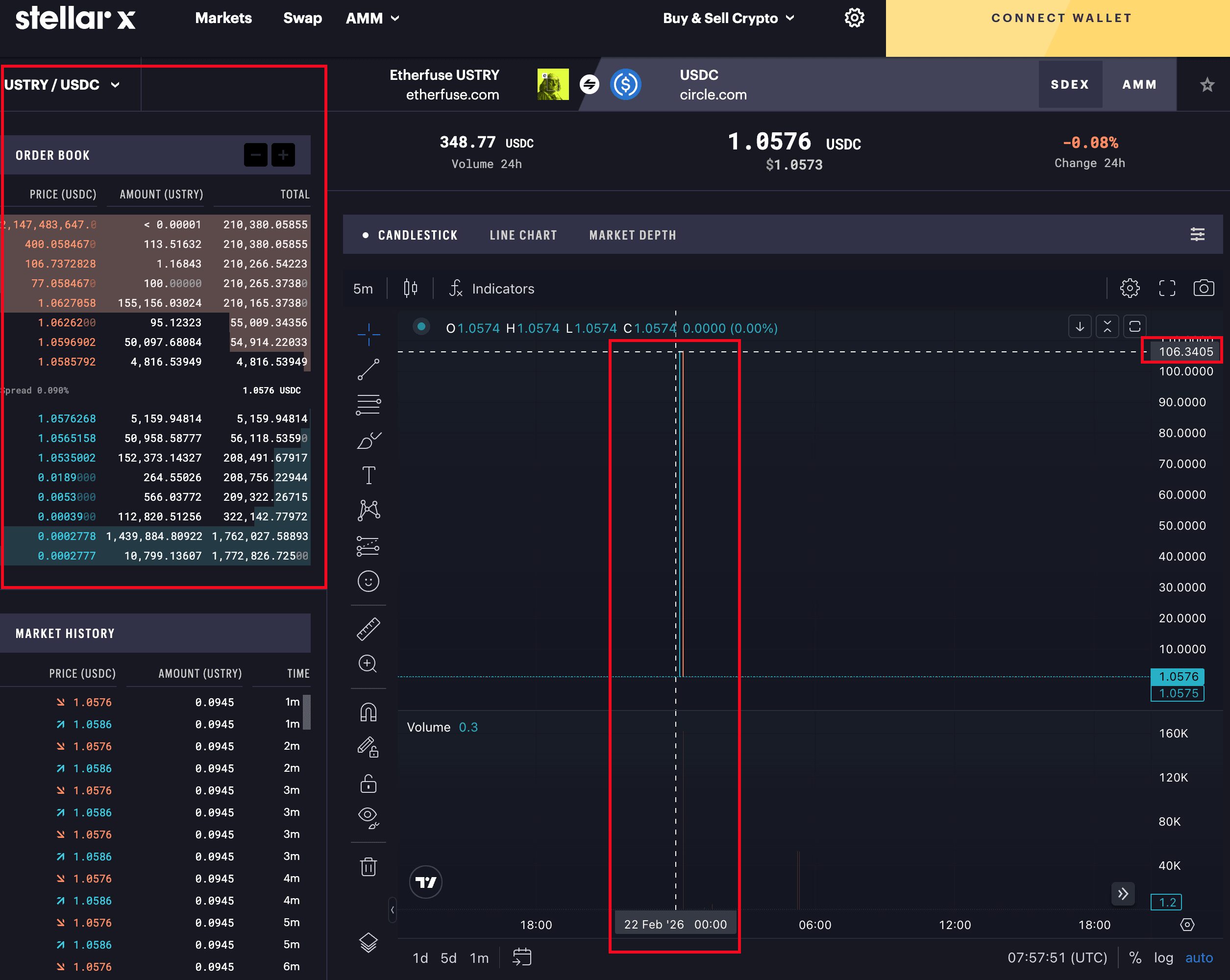
- SDEX上的USTRY/USDC市场深度非常浅。
- 攻击者可以通过清空正常订单并下达异常订单来急剧推高市场名义价格。
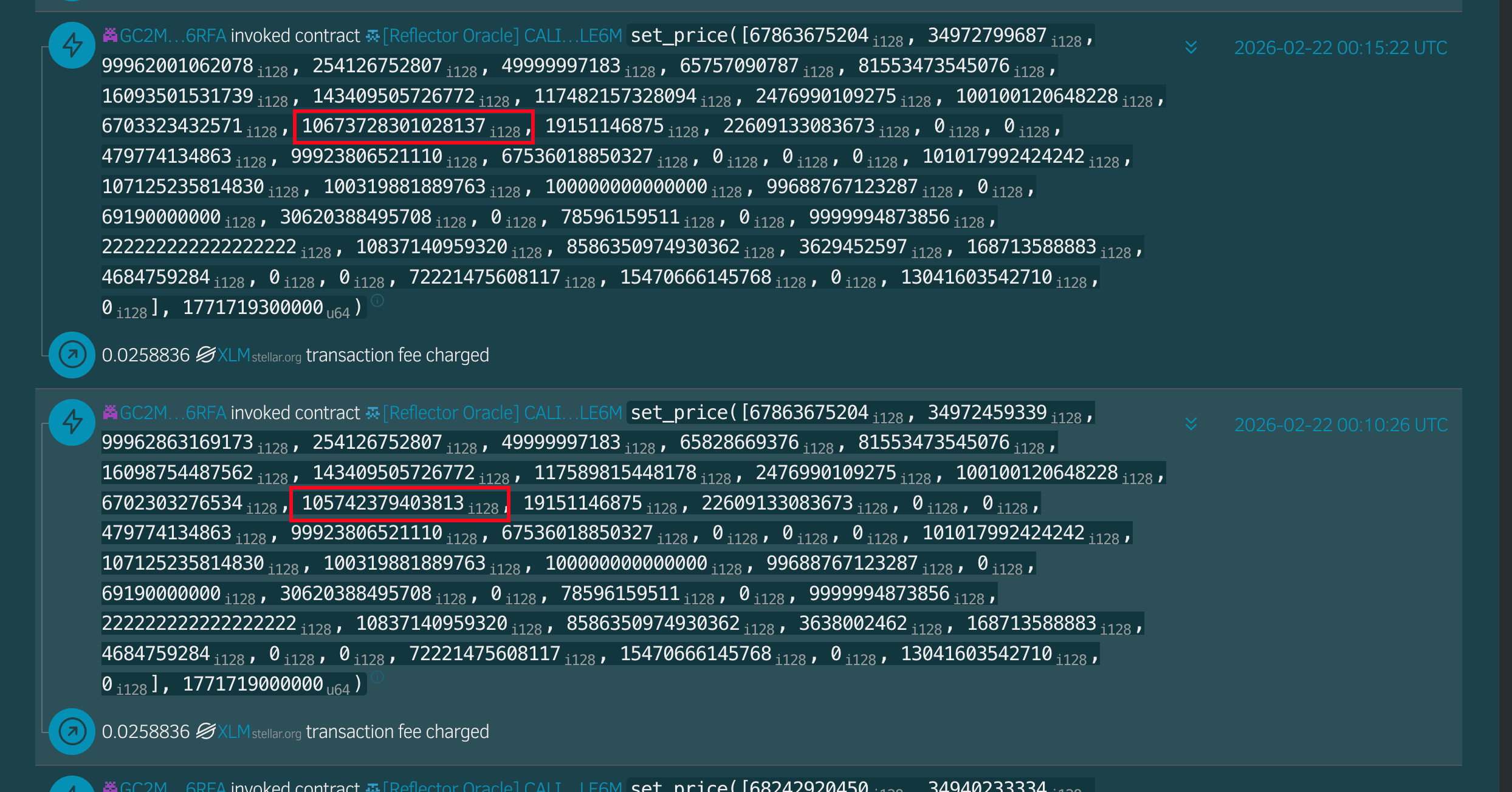
- Reflector随后将USTRY的价格更新为被操纵的值。
- 该池的风险逻辑接受该值为抵押品估值,从而膨胀了借款能力。
因此,攻击者利用高估的USTRY抵押品从池中提取了可借入的资产。
4. 攻击分析
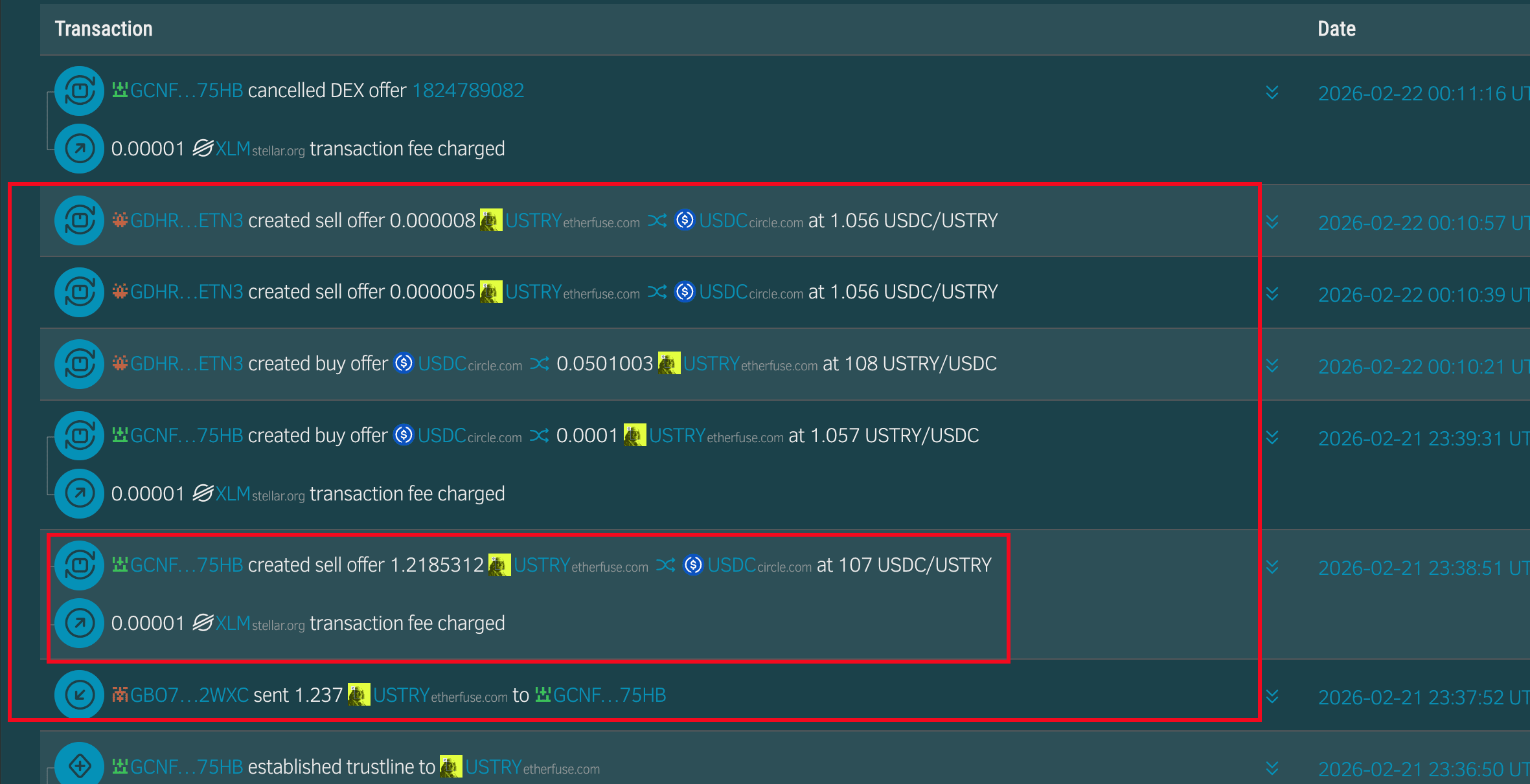
1.(Tx 1, 2)攻击者通过消耗正常流动性并下达异常订单,将SDEX上的USTRY价格从约1.06美元操纵到约107美元。
2.(Tx 3)Reflector拉取了被操纵的SDEX价格并更新了其馈送。
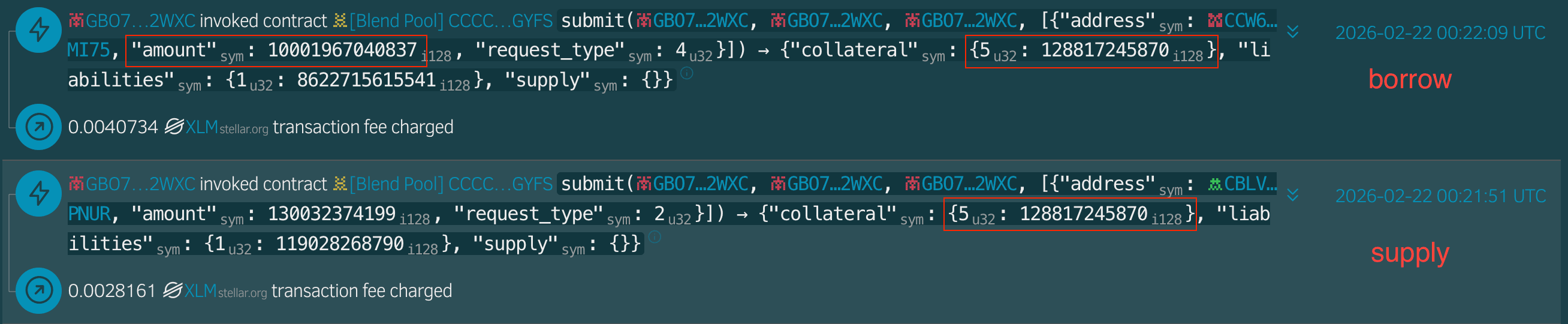
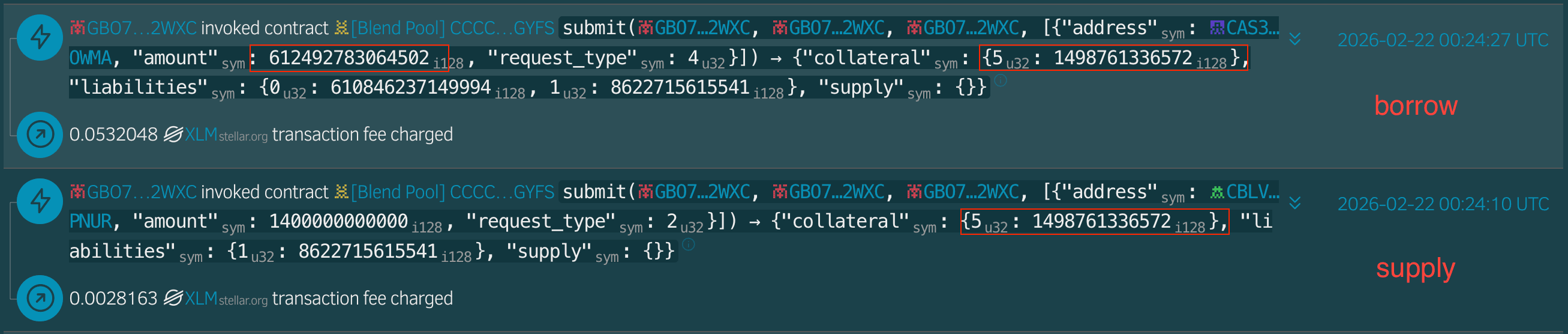
3.(Tx 4, 5)攻击者以12,881e7 USTRY的抵押品借入了1,000,196e7 USDC。
4.(Tx 6, 7)攻击者以14,987,610e7 USTRY的抵押品借入了6,124,927,810e7 XLM。
5.(Tx 8, 9, 10)攻击者将提取的资产桥接到了Base、BSC和以太坊。
5. 损失/利润分析
在Stellar上估计的总损失约为1000万美元以上。
| Chain | Type | Address |
|---|---|---|
| Stellar | Attacker | GBO7VUL2TOKPWFAWKATIW7K3QYA7WQ63VDY5CAE6AFUUX6BHZBOC2WXC |
| Stellar | Attacker | GCNF5GNRIT6VWYZ7LXUZ33Q3SR2NUGO32F5X65VVKAEWWIQCKGYN75HB |
| Stellar | Attacker | GDHRCQNC64UVL27EXSC6OG6I2FCT4NWM72KNHLHKEB3LK4MEEYYWETN3 |
| Stellar | Attacker | GATDQL767ZM2JQTBEG4BQ5WKOQNGAGWZDUN4GYT2UINPEU3RT2UAMVZH |
| Stellar | Reflector Oracle | CALI2BYU2JE6WVRUFYTS6MSBNEHGJ35P4AVCZYF3B6QOE3QKOB2PLE6M |
| Stellar | Victim Pool | CCCCIQSDILITHMM7PBSLVDT5MISSY7R26MNZXCX4H7J5JQ5FPIYOGYFS |
| BSC, Base, Ethereum | Attacker | 0x2d1ce29b4af15fb6e76ba9995bbe1421e8546482 |
| Ethereum | Attacker | 0x0b2b16e1a9e2e9b15027ae46fa5ec547f5ef3ec6 |
| Ethereum | Attacker | 0xe69f6d77db6ff493fdd15d8a0b390c36e18e5b21 |
6. 结论
核心问题很简单:该池的抵押品估值依赖于一个可操纵的价格来源。这是池操作者(YieldBlox DAO)的配置失败,而非Blend V2核心合约的缺陷。此次事件提醒我们,借贷池必须选择并监控价格依赖性,并具备强大的抗操纵能力。
参考资料
[1] YieldBlox DAO
[2] https://reflector.network/
[3] USTRY/USDC Market on the SDEX
关于BlockSec
BlockSec是一家提供全栈区块链安全和加密合规服务的提供商。我们构建产品和服务,帮助客户在协议和平台的整个生命周期中执行代码审计(包括智能合约、区块链和钱包),实时拦截攻击,分析事件,追踪非法资金,并满足AML/CFT义务。
BlockSec已在著名会议上发表多篇区块链安全论文,报告了多个DeFi应用的零日攻击,阻止了多次黑客攻击并挽救了超过2000万美元,并保障了数十亿美元的加密货币安全。
-
官方Twitter账号:https://twitter.com/BlockSecTeam




