1月28日,QBridge 遭到攻击,约8000万美元的资产被盗。经过分析,我们发现代码中的根本原因是 safeTransfer(以及 safeTransferFrom)函数的实现方式。
根本原因
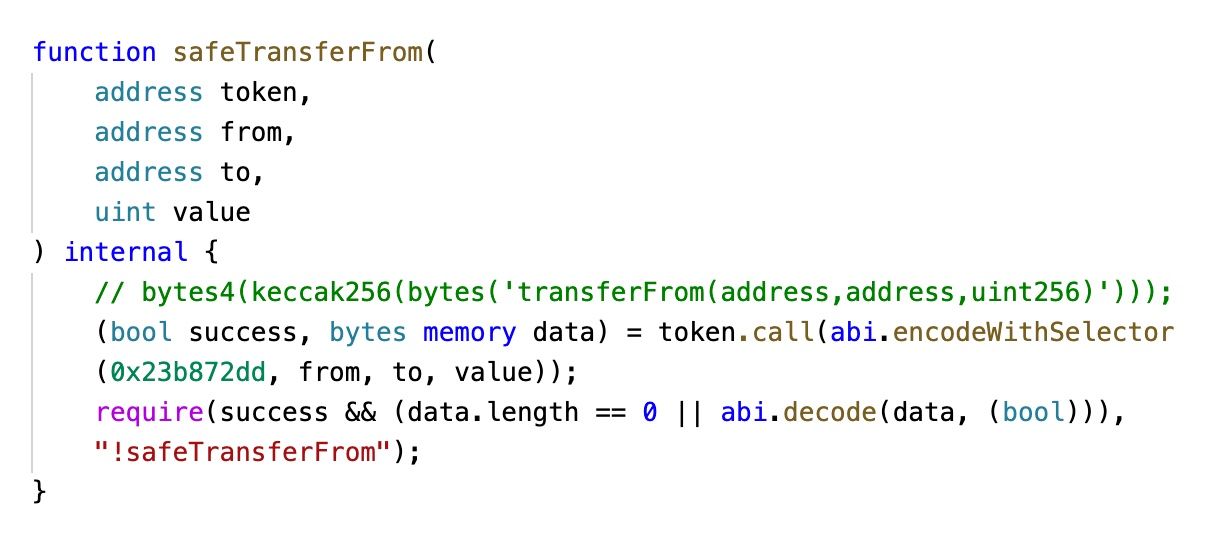
首先,该项目没有使用主流的 OpenZeppelin SafeERC20 库来进行代币转账。相反,他们自己实现了一个名为 SafeToken 的库。
其次,该实现没有检查目标地址是否为有效合约(或是否为零地址)。
第三,EVM 的底层调用在目标合约为零地址时不会返回 false。 这与开发者的常识相违背。
当然,此次事件还涉及其他原因,例如将零地址加入白名单。然而,如果代码能够正确处理这种特殊情况,它就不会存在漏洞。
顺便提一下:还有其他项目使用了类似的代码。它们可能也容易受到类似的问题影响。
实验
为了证实第三个原因——即当目标合约为零地址时 VM 不会返回 false,我们开发了一个测试合约,如下所示:
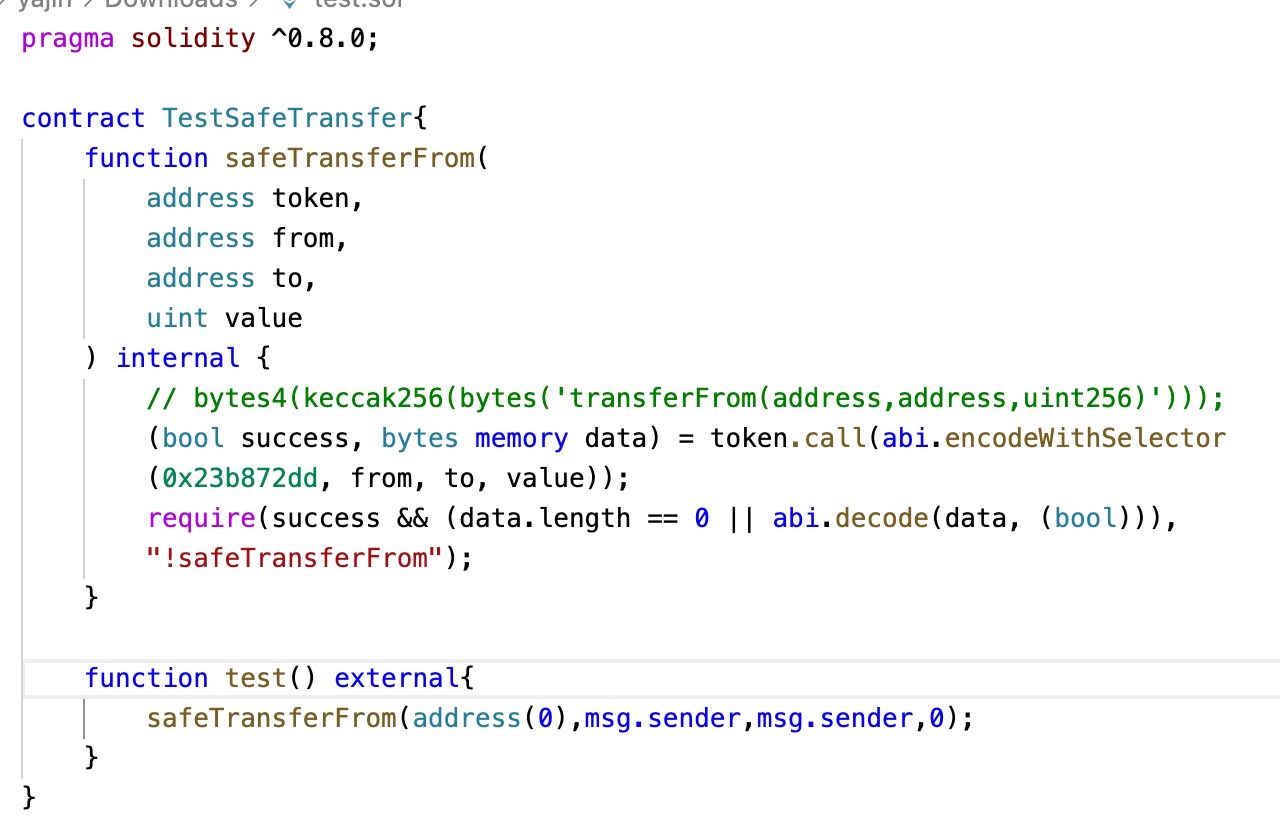
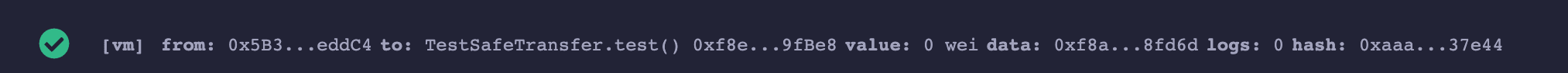
执行 TestSafeTransfer.test() 并不会回滚(revert)。
教训与风险缓解措施
我们建议:
- 除非有非常充分的理由,否则请使用现成的主流库,而不要重复造轮子。
- 在资产转账前后检查余额,以确保转账的资产数量符合预期。这也能够避免通缩和通胀代币带来的问题。
关于 BlockSec
BlockSec 是一家由多位世界顶尖安全专家于2021年创立的先驱区块链安全公司。公司致力于提升新兴 Web3 世界的安全性和易用性,以促进其大规模应用。为此,BlockSec 提供智能合约和 EVM 链安全审计服务、用于安全开发和主动阻断威胁的 Phalcon 平台、用于资金追踪与调查的 MetaSleuth 平台,以及帮助 Web3 构建者高效探索加密世界的 MetaDock 插件。
迄今为止,公司已服务过 MetaMask、Uniswap Foundation、Compound、Forta 和 PancakeSwap 等超过 300 家知名客户,并获得了包括经纬创投(Matrix Partners)、毅峰资本(Vitalbridge Capital)和分布式资本(Fenbushi Capital)在内的顶级投资机构两轮数千万美元的融资。




