在东八区时间 2 月 3 日上午,我们的系统报告了一笔针对 HypeBears NFT 合约的攻击交易 0xfa97c3476aa8aeac662dae0cc3f0d3da48472ff4e7c55d0e305901ec37a2f704。经过调查,我们发现这是由 ERC721 的 _safeMint 函数引起的重入攻击。
根本原因
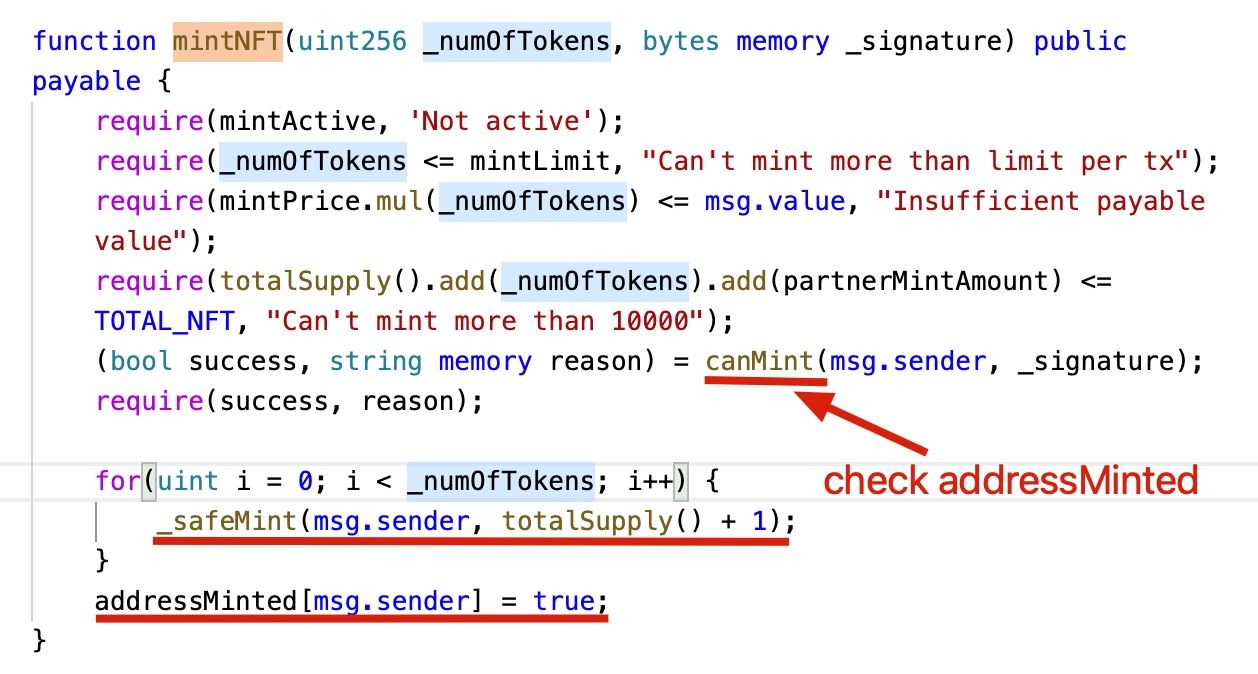
该项目对一个账户可以铸造的 NFT 数量有限制。基本上,它有一个 addressMinted 的映射,用于记录一个账户是否已经铸造过 NFT。
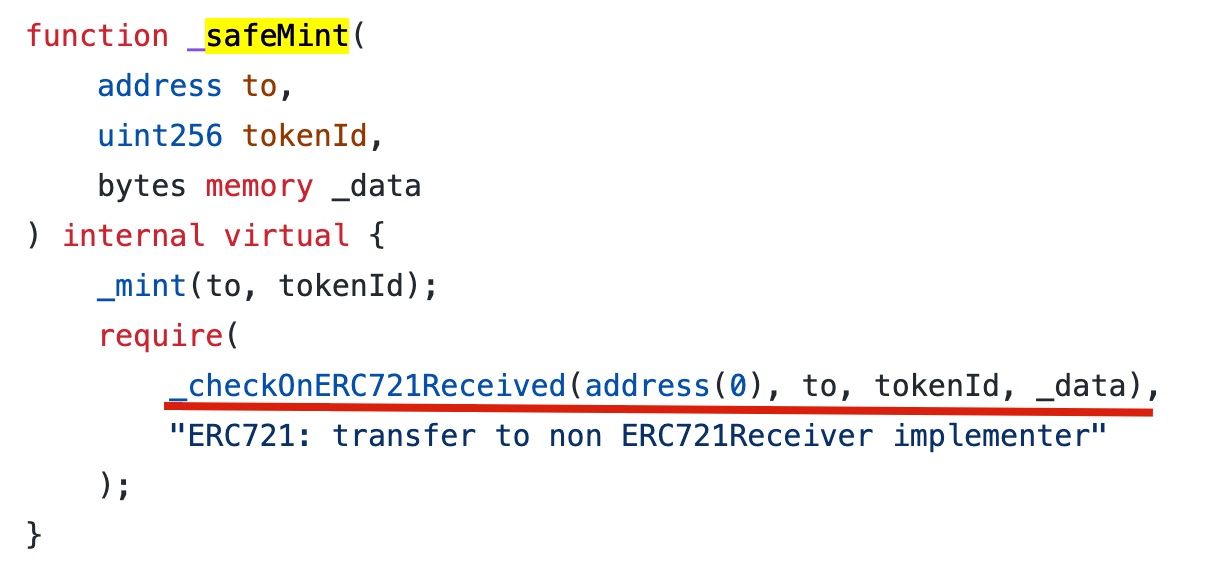
在铸造 NFT 时,代码使用了 OZ 参考实现中的 _safeMint 函数。这个函数是 safe 的,因为它检查接收方是否可以接收 ERC721 代币。这可以防止 NFT 被铸造到无法处理 ERC721 代币的合约中。根据 文档:
如果 to 指的是一个智能合约,它必须实现 IERC721Receiver.onERC721Received,该函数在安全转账时被调用。以下代码显示了 OZ 对
_safeMint函数的实现。
然而,这个外部函数调用会产生一个安全漏洞。具体来说,攻击者可以在 onERC721Received 回调中执行重入调用。例如,在 有漏洞的 HypeBears 合约 中,攻击者可以在 onERC721Received 回调中再次调用 mintNFT 函数(因为 addressMinted 尚未更新)。
攻击
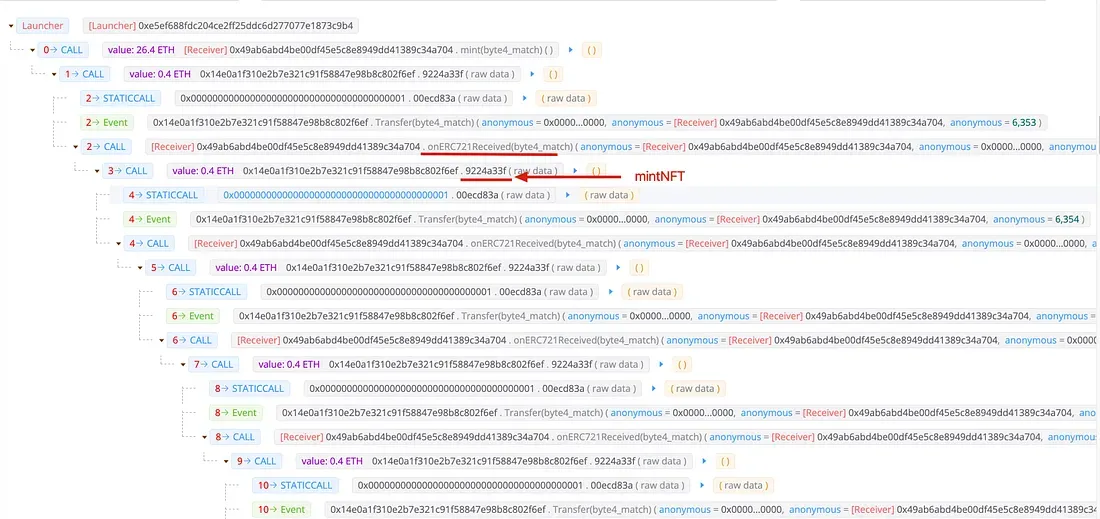
下图显示了 攻击交易。
教训
安全研究人员讨论过 SafeMint 带来的风险 链接1 链接2。然而,我们仍然可以看到有漏洞的代码和实际发生的攻击。正如在 QBridge 安全事件 中的 safeTransfer 中所示,使用一个 安全 的函数并不能保证一个 安全 的合约 😃。




