USDT的十年:机遇与风险
自2014年Tether推出全球首个主流美元挂钩稳定币USDT以来,已经过去了十年。现在,稳定币的发展前景十分广阔:2024 年,稳定币交易额达到 27.6 万亿美元,预计 2025 年总市值将超过 25亿美元,年交易额将达到 36.3万亿美元,超过维萨卡和万事达卡的交易额总和。 稳定币的价格稳定性与法定货币或其他储备资产挂钩,因此被广泛用于跨境贸易、资金管理和消费者支付。 然而,USDT 的匿名性也使其成为非法金融**的首选工具。2025 年,"新康佳 "欺诈丑闻揭露了 USDT 如何被滥用于集资和洗钱,导致大量投资者损失。 本文探讨了犯罪分子如何跨区块链利用 USDT,并重点介绍了企业和用户如何保护自己。 ##跨主要区块链的 USDT USDT 在多个链上发行,因此犯罪分子很容易跨链转移资金并避免被发现:
-
Tron (TRC-20):供应量为 758 亿美元;手续费低,交易量大,适合小额洗钱。
-
以太坊(ERC-20)**:供应量为 790 亿美元;与 DeF 集成--用于掩盖 "虚假投资 "交易。
-
BNB 链(BEP-20):供应量为 74 亿美元;与交易所紧密集成--钥匙洗钱途径。
-
Solana (SPL):23 亿美元供应量;快速确认--缩短洗钱周期。
-
Polygon (ERC-20):14 亿美元供应量;缩放层--通常会分散大量非法转账。
这种多链分布增加了追踪难度。BlockSec 的 Phalcon Compliance 和 MetaSleuth 全面覆盖主要 EVM 链和 20 多个跨链桥,提供实时检测和取证。
使用 USDT 的六种新兴犯罪手段
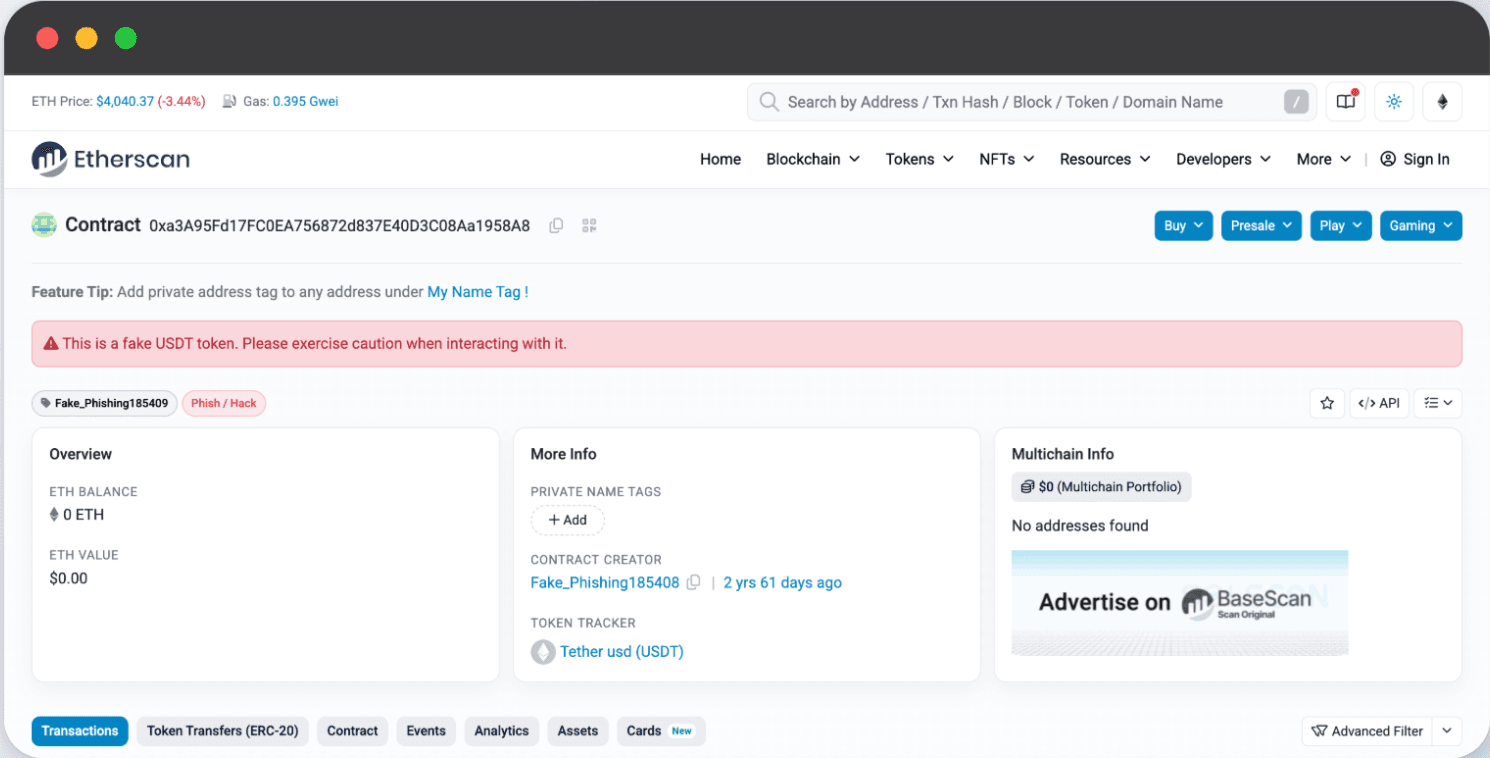
1.伪造 USDT
犯罪分子伪造虚假代币或伪造交易记录,通过以下方式诈骗用户:
-
以低于市场价 5-10% 的价格进行 "打折 "场外交易
-
伪造转账截图,诱骗用户预付法定货币
-
带有 "虚假 USDT 余额 "的恶意钱包应用程序
➡️ 利用 BlockSec 的 MetaSuites 浏览器插件等工具和包含数亿条目的风险标签地址数据库,可以立即标记出虚假代币。
 2.黑色 USDT
2.黑色 USDT
通过以下方式清洗欺诈、赌博、贩运或恐怖主义融资的资金:
-
使用骡子账户的**"跑分 "平台**
-
通过借贷和流动性协议**"DeFi 混合器
-
跨境场外交易**进入交易所
➡️ 对于交易所和支付提供商等企业而言,接受黑色 USDT 可能导致资产被冻结、许可证被吊销、巨额罚款甚至刑事指控。Phalcon Compliance 通过地址评分、资金追踪和人工智能驱动的异常检测来检测风险资金流入,从而在非法存款污染平台之前将其拦截。
3.被盗 USDT
技术从网络钓鱼发展到
-
插件劫持**窃取钱包密钥
-
智能合约漏洞***榨干协议(如 2024 年 1.2 亿美元的盗窃案)
-
供应链黑客***在 SDK 中注入后门(如备受瞩目的 Bybit 事件)。
-
恶意升级***利用 EIP-7702 等新功能(用于攻击 SeedifyFund 和 Griffin_AI)
➡️ BlockSec 的Phalcon Security可阻止实时攻击,而Phalcon Compliance则将攻击者链接的地址列入黑名单,以防止洗钱。通过BlockSec的白帽干预,已经挽救了超过**2000万美元的资产。
4.美国数据传输洗钱
现代洗钱=多链跳转+DeFi嵌套:
1.将资金分成 10-20 个 "中间钱包"
2.使用跨链桥梁 + DeFi 循环(借贷-股权-交换)
3.通过离岸交易所套现
➡️ Phalcon合规性重建跨链资金图表,检测 "循环模式 "并提供与FATF一致的合规性报告。
5.5. USDT "跑分 "平台
骡子平台通过 "在家工作 "广告招募个人(学生、失业者):
-
用户绑定个人银行卡
-
接收非法 USDT → 向犯罪账户转移法币
-
赚取 1-3% 的佣金
➡️ Phalcon Compliance 可检测异常的 "多账户资金池 "和 "高频小额转账",准确定位骡子网络。
6.USDT 庞氏骗局
骗子将 USDT 投资伪装成 "低风险、高回报 "的投资:
1.伪造角色**(有影响力的人,"投资大师")** *.
2.** 多层次推荐**,收取会员费(1,000-10,000 USDT)
3.当资金流入枯竭时崩溃--经营者携所有资金消失
➡️ 用户必须保持警惕:"保证回报"=红旗。
结论
USDT 已成为加密货币经济中的一把双刃剑。它在实现高效跨境支付的同时,也被非法行为者滥用--通过伪造代币、洗钱计划和欺诈网络--给金融诚信带来了严重风险。应对这些威胁需要先进的合规工具和实时情报。 BlockSec 的 Phalcon Compliance 和 MetaSleuth 可帮助企业检测、追踪和阻止非法 USDT 流量,帮助交易所、支付提供商和机构在保护用户的同时保持合规。
采取行动
🚀 **立即加强合规性。
👉 预订演示,了解 BlockSec 如何帮助您阻止非法 USDT 流动,并与监管机构和客户建立长期信任。




