引言
在本篇博客中,我们将演示如何使用 MetaSleuth 来追踪 Solana 上的 Meme 币 GME。
MetaSleuth 是一个专门用于加密货币追踪和调查的平台,用户需要利用链上工具进行 DYOR(自己做研究)。它提供了诸如资金追踪、可视化资金流、实时交易监控以及保存和分享分析结果等多样化功能。MetaSleuth 有助于监控市场动态,追踪犯罪活动的资金流向,并支持用户进行独立研究以避免诈骗。MetaSleuth 支持超过 20 条区块链,被社区广泛用于各种调查目的。
6 月 3 日上午 8:03,地址 4VnL1GoHxM3XnFTU1MeZnrLGG3zu9jC2SryANwsD6HML 以 0.004373 的价格花费 17,000 美元购买了约 400 万枚 $GME,距离 $GME 开始上涨仅六分钟。六分钟后,全部头寸被卖出,产生 13,265.06 美元的收益,约合 1.7 倍的回报。买卖时机极其精准。
使用 MetaSleuth 在 Solana 上追踪 Smart Money:案例研究
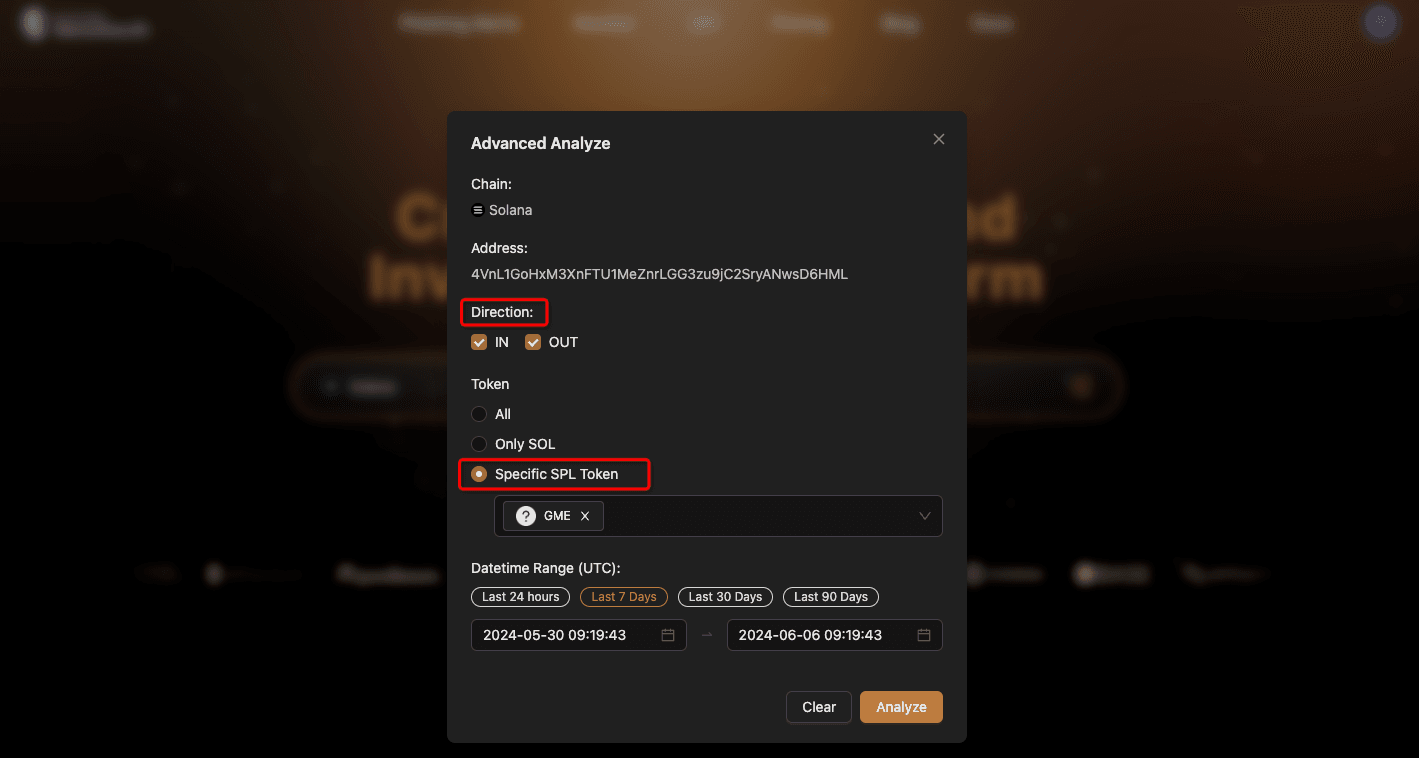
首先,在选项中选择“Solana”,然后输入地址 4VnL1GoHxM3XnFTU1MeZnrLGG3zu9jC2SryANwsD6HML,然后按“Advanced Analyze”。
由于我们的目标非常明确——分析此地址的 $GME 流动情况——我们可以在分析前进一步细化我们的标准,以使结果更加准确。
- 首先,在“Direction”下选择所需的资金流向。
- 接下来,您可以输入特定的代币地址来进一步缩小范围。在这里,我们可以选择“Specific SPL Token”并粘贴 $GME 代币的合约地址:8wXtPeU6557ETkp9WHFY1n1EcU6NxDvbAggHGsMYiHsB。
- 最后,按所需时间段进行过滤。
MetaSleuth 会自动可视化与该地址相关的资金流。每个节点代表一个地址,节点之间的边代表总代币转账。即使两个节点之间发生多次同一代币的交易,也只显示一条边。
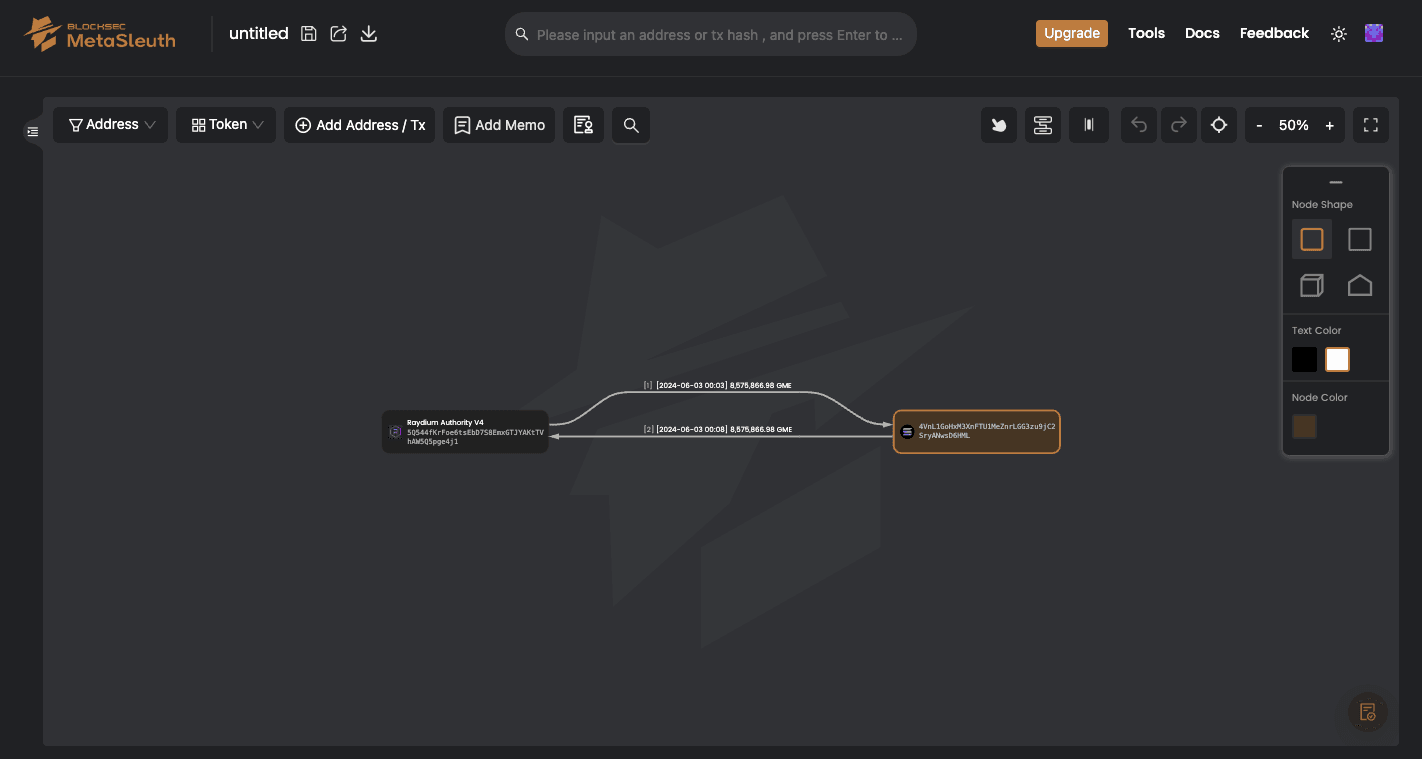
我们可以看到画布当前显示两条记录。
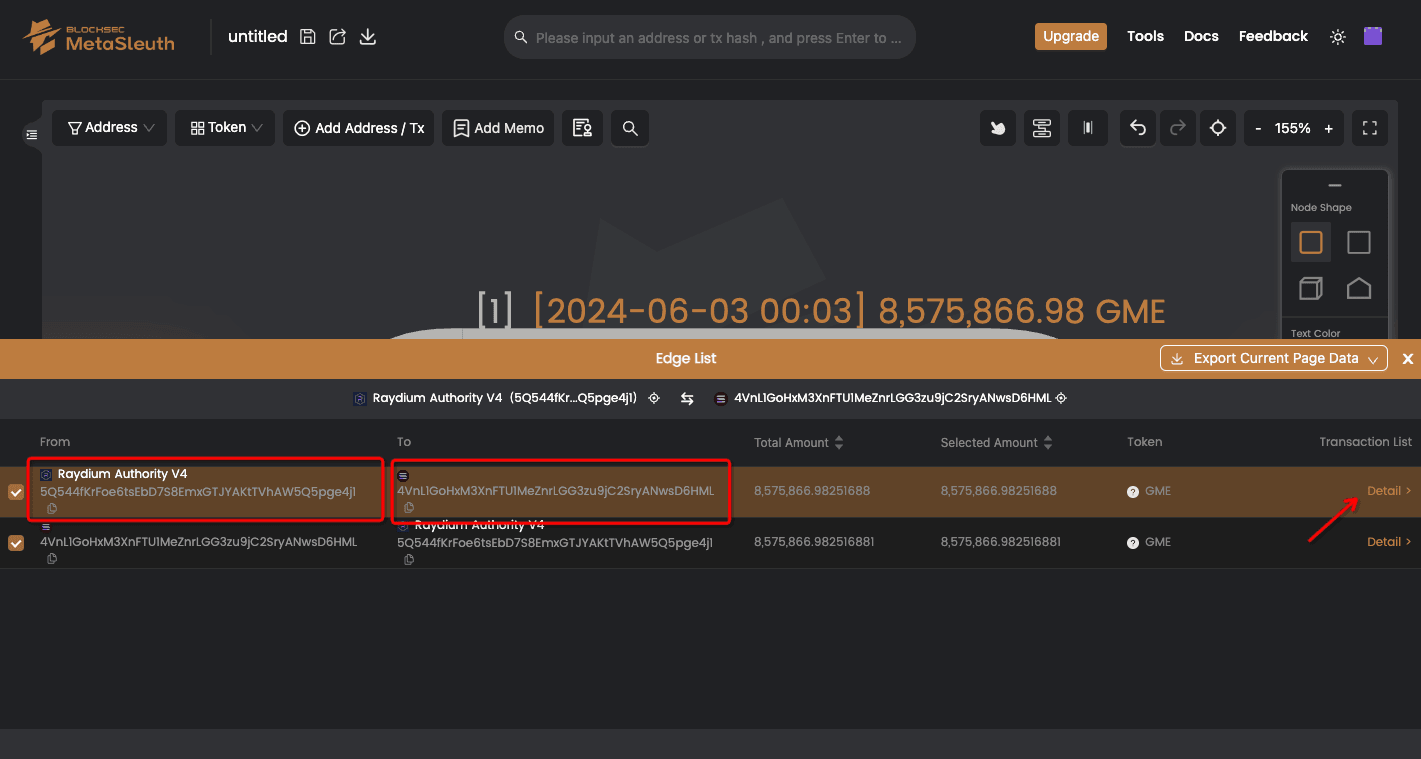
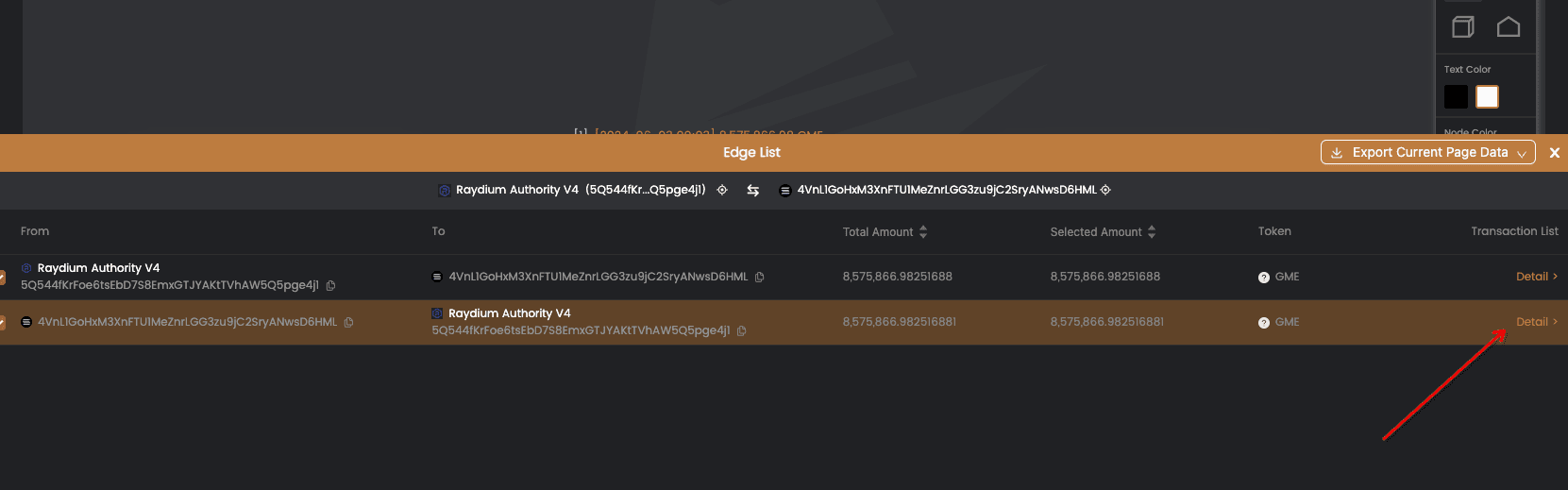
如前所述,边代表汇总的代币转账。我们可以点击边来查看更详细的信息。 在边列表中,我们可以看到节点之间的所有代币转账。由于显示的是汇总代币,我们可以点击“Details”展开以查看更多信息。
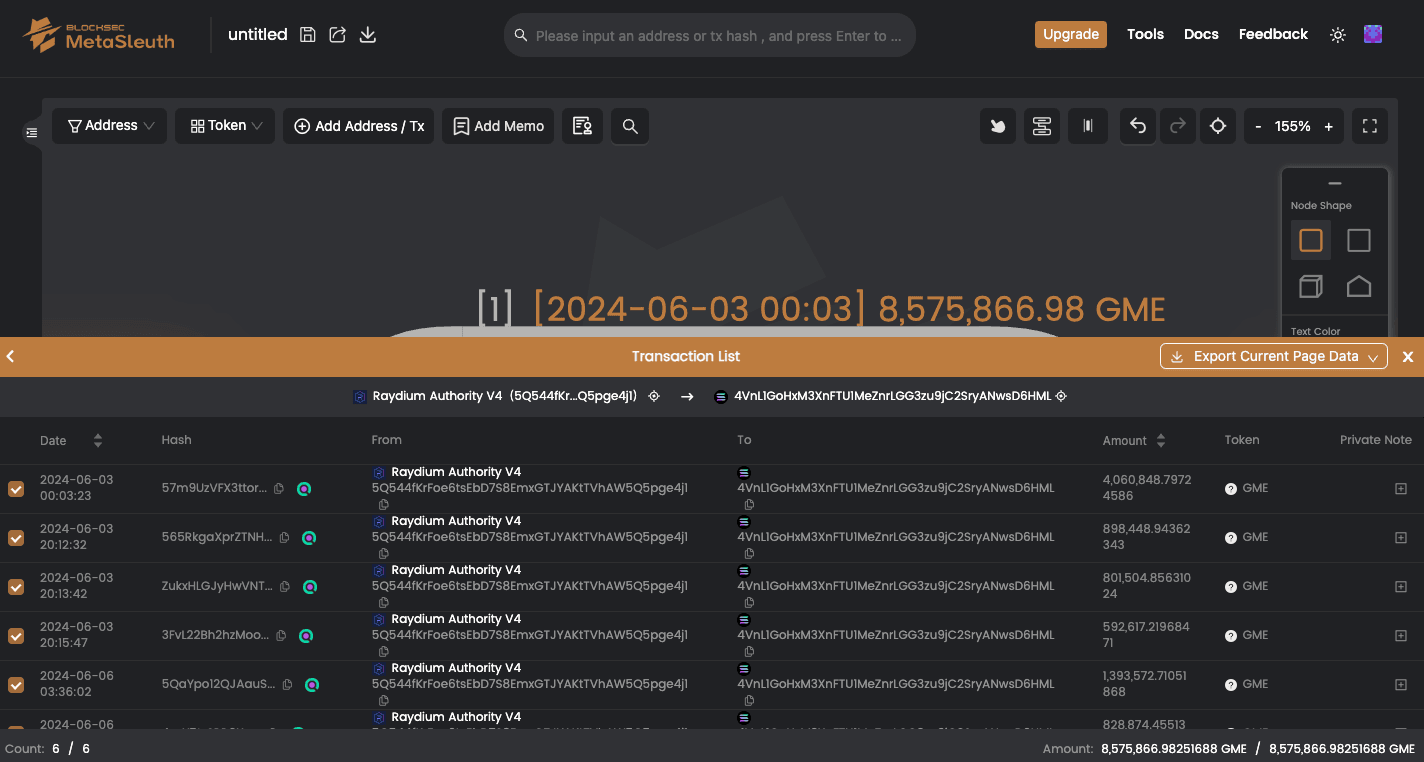
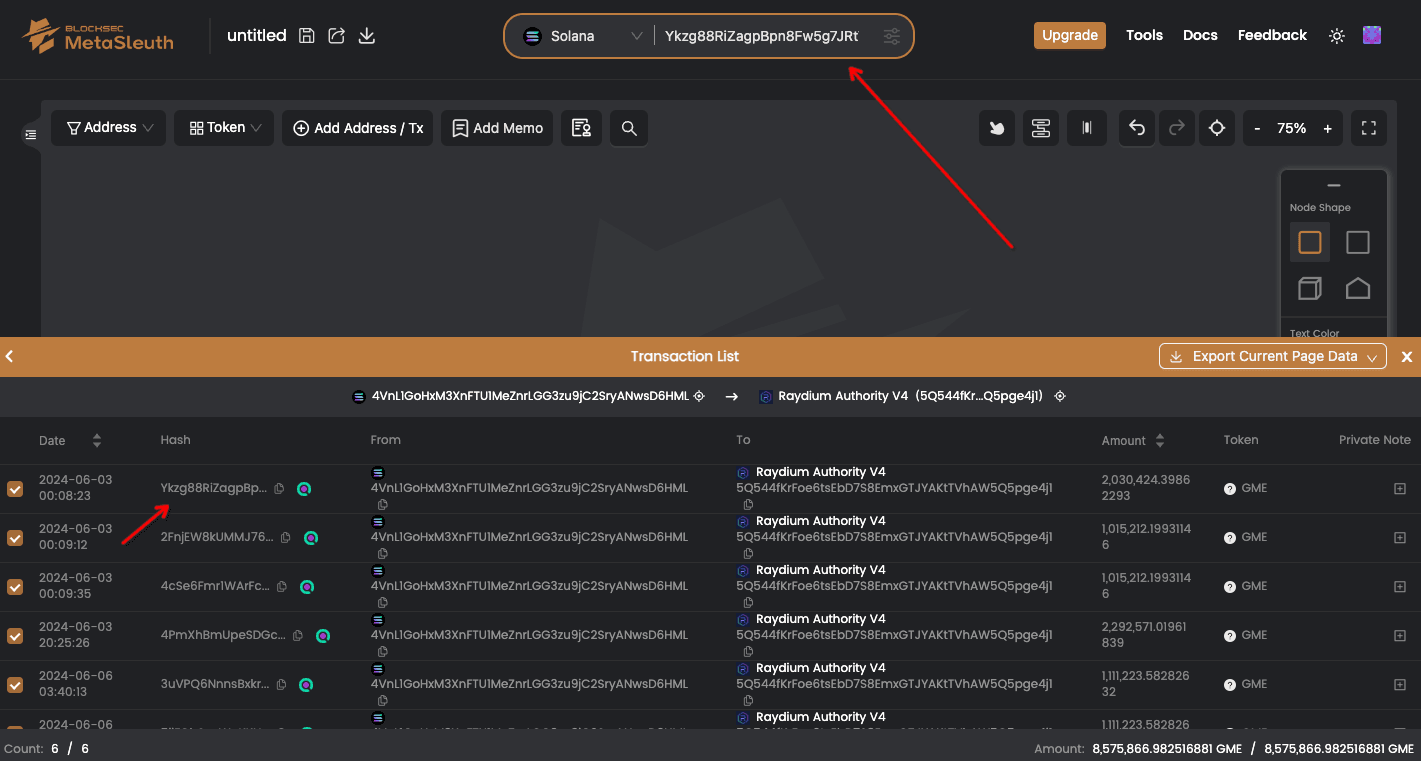
此外,您可以将交易哈希粘贴到上面的搜索栏中以查看交易详情。
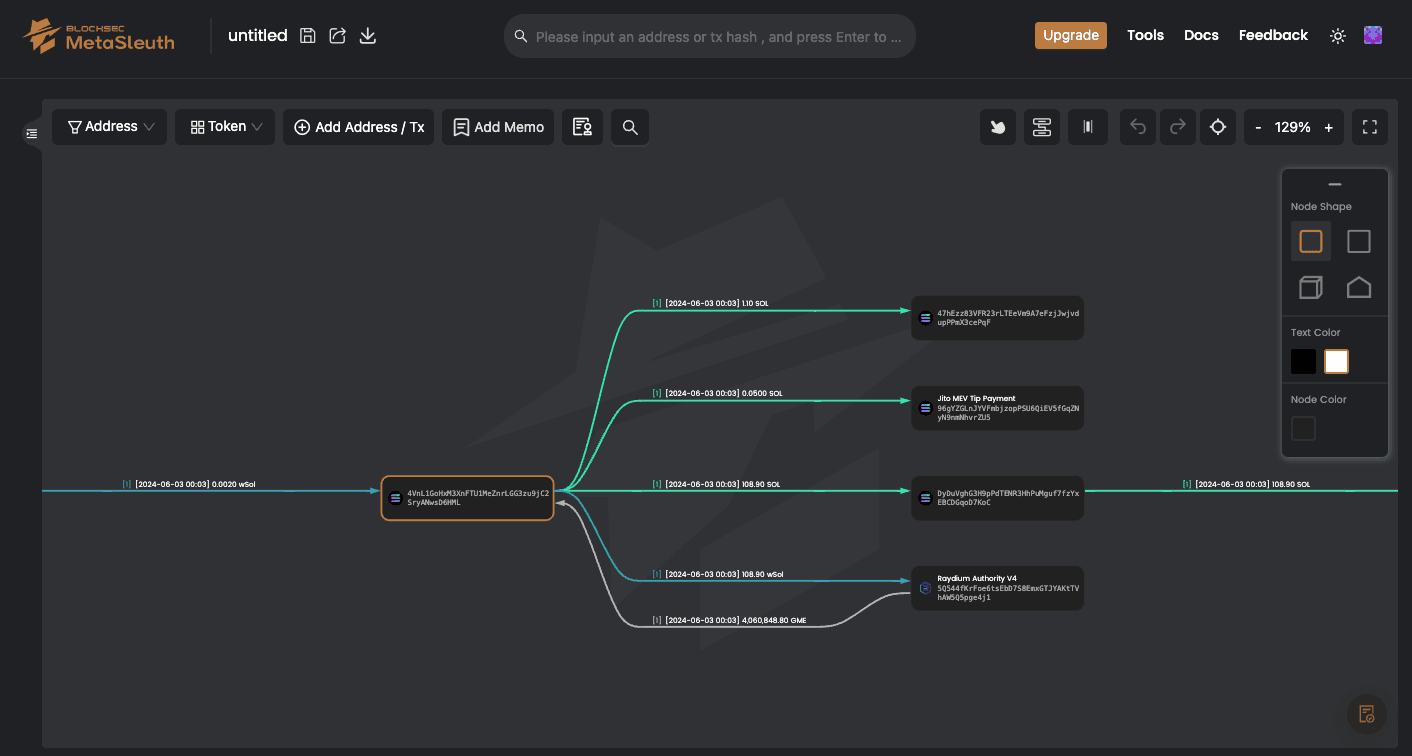
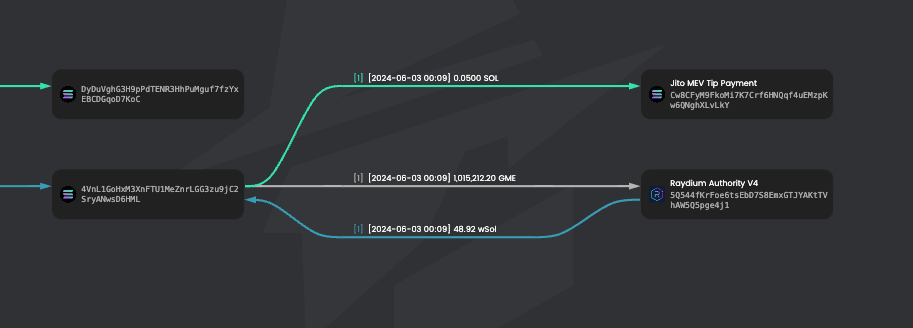
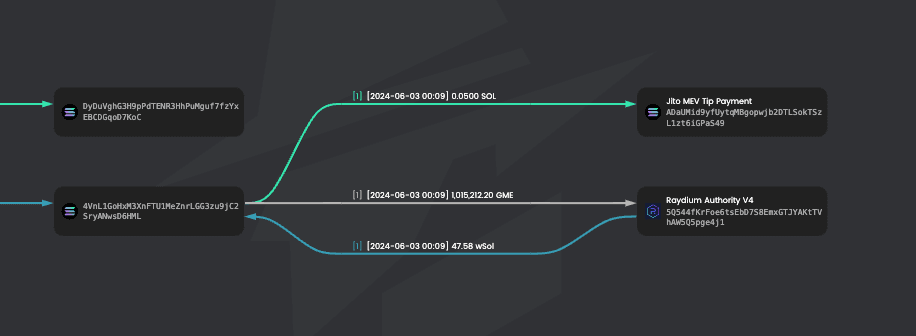
我们可以看到,在 00:03,108.90 WSOL 兑换了 4,060,848.79724586 GME。 接下来,我们需要确定这些 GME 以多少价格售出。点击第二条边,然后点击“Details”。
注意左下角,在 [2024-06-03 00:08:23]、[2024-06-03 00:09:12] 和 [2024-06-03 00:09:35] 时,分别售出了 2,030,424.39862293、1,015,212.19931146 和 1,015,212.19931146 GME,总计 4,060,848.797 GME。
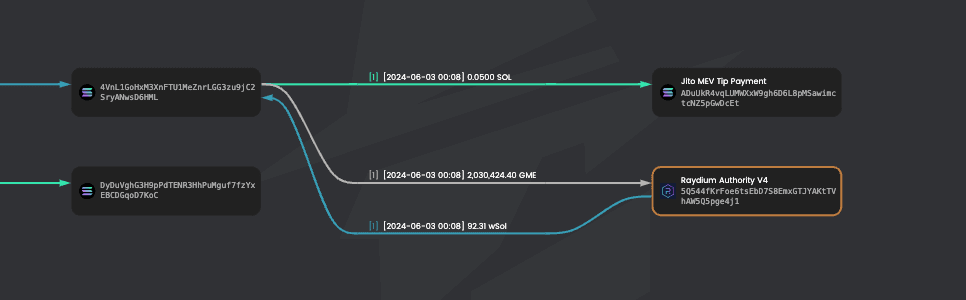
此时,将交易哈希粘贴到上面的搜索栏中,即可查看收到的 wSol 数量:92.31 wSol、48.92 wSol 和 47.58 wSol,总计 188.81 wSol。 在短短 5 分钟内,利润为 (188.81 - 108.90) * 166 = 13,265.06。
通过运用这些方法和技术,您可以利用 MetaSleuth 对 Solana 生态系统内的项目和钱包进行深入调查,监控 Smart Money 的投资活动,并做出更明智的投资选择。无论您是初学者投资者还是经验丰富的分析师,MetaSleuth 都可以作为探索和理解 Solana 生态系统的强大工具。
订阅并享受 10% 折扣
注册 MetaSleuth 时,请使用 BLOCKSEC 作为邀请码,即可享受订阅 10% 的折扣。
https://metasleuth.io/?invite-code=BLOCKSEC
关于 MetaSleuth
MetaSleuth 是由 BlockSec 开发的一个综合平台,旨在帮助用户有效追踪和调查所有加密货币活动。借助 MetaSleuth,用户可以轻松追踪资金、可视化资金流、监控实时资金动向、保存重要信息,并通过与他人分享其发现来协作。目前,我们支持 13 条不同的区块链,包括比特币 (BTC)、以太坊 (ETH)、波场 (TRX)、Polygon (MATIC) 等。 网站:https://metasleuth.io/ Twitter:@MetaSleuth @MetaSleuth 电报:https://t.me/MetaSleuthTeam




