关于 Ronin Bridge 黑客事件
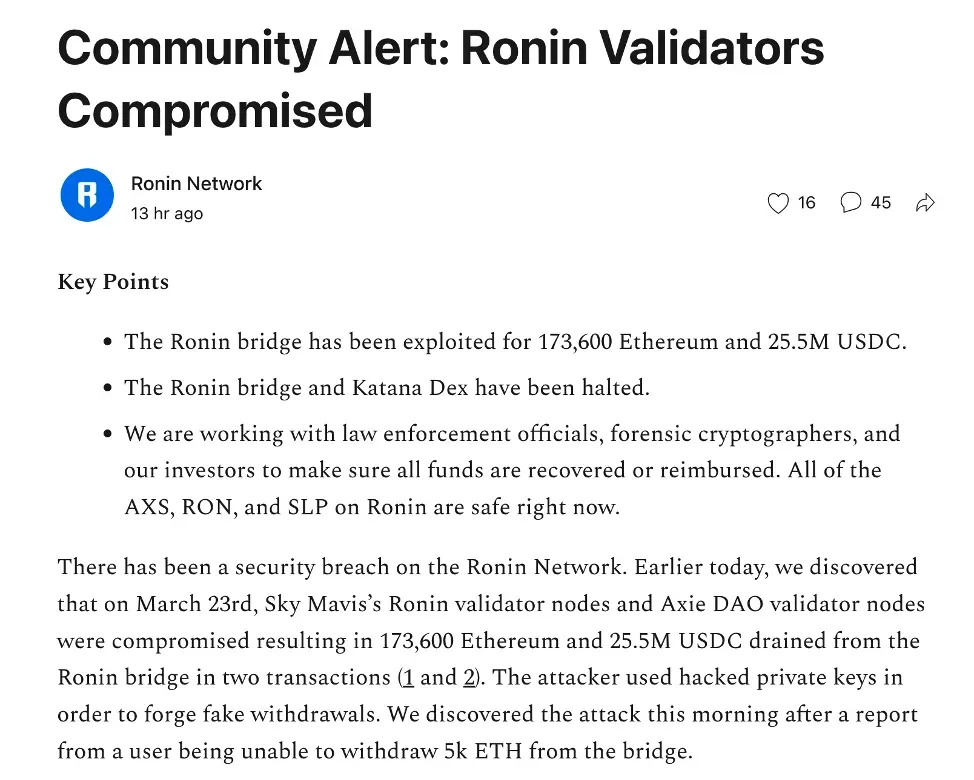
2022 年 3 月 29 日,Ronin Network 发布官方公告,警示社区 Ronin Bridge 的安全事件。具体而言,攻击者通过攻破 Ronin 验证者节点获取了私钥,并通过两次攻击交易从 Ronin Bridge 盗取了 173,600 ETH 和 25,500,000 USDC。
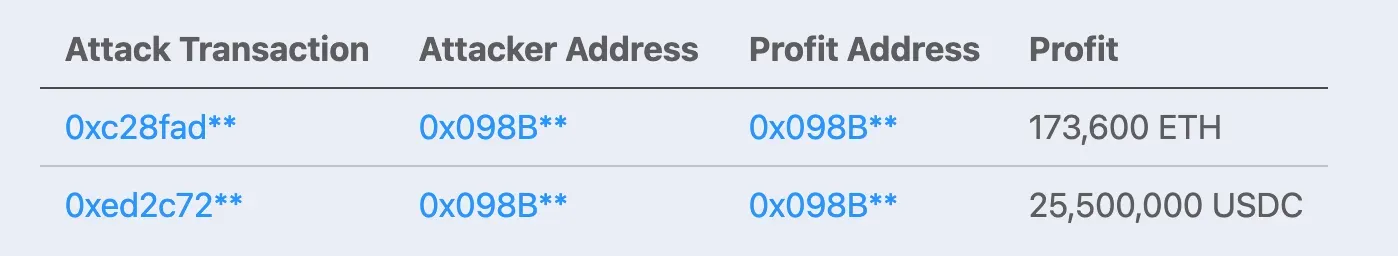
两次交易的详情如下:
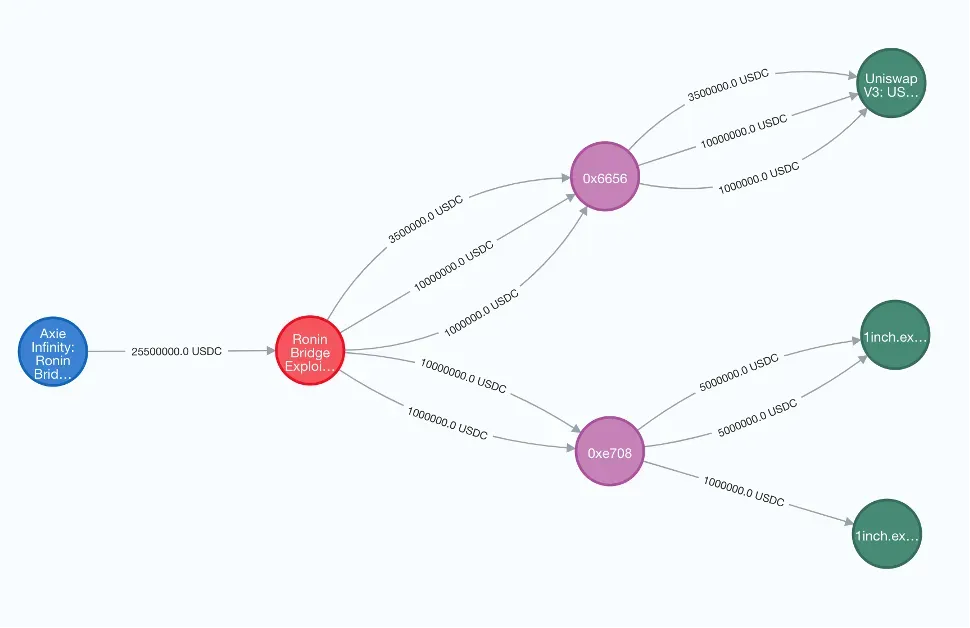
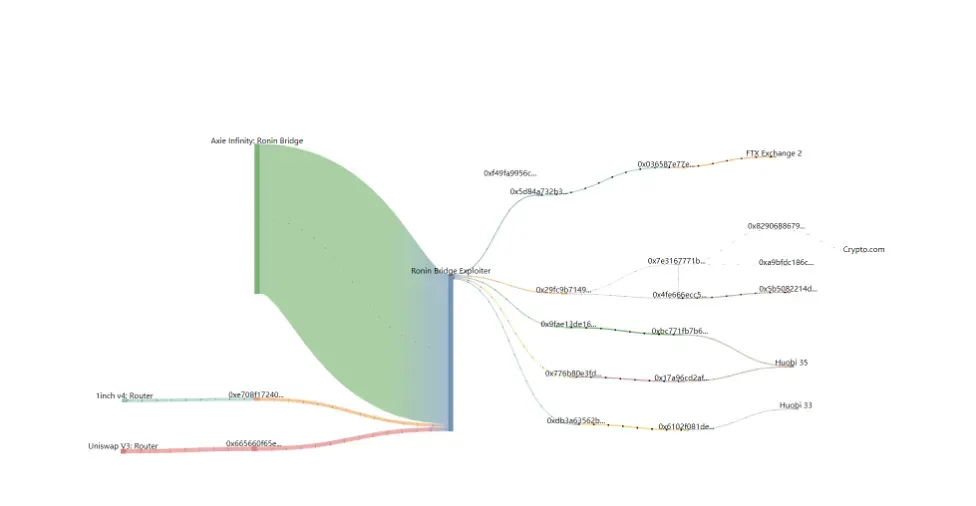
追踪被盗资金
攻击者在获利后立即将被盗的 USDC 兑换成 ETH。具体来说,被盗的 USDC 被转移到 Uniswap 和 1inch,并使用了两个中间节点,即 0x6656 和 0xe708,来进行来回兑换。兑换完成后,所有被盗资金都变成了 ETH。
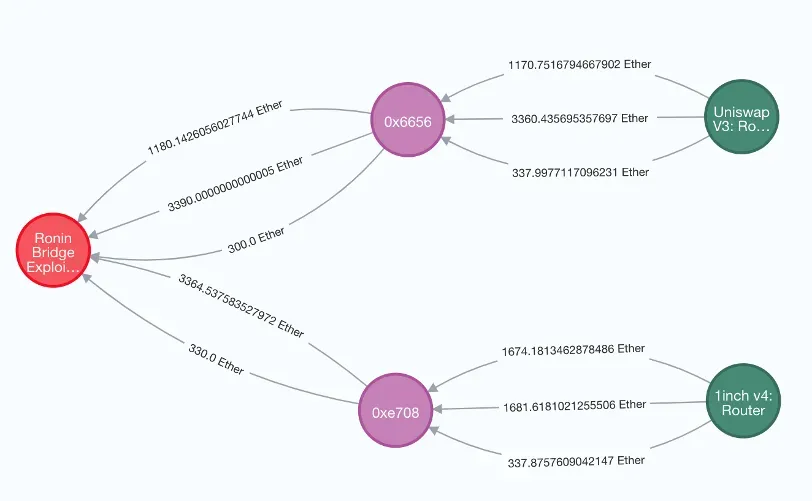

3 月 28 日,攻击者开始转移 ETH。截至 3 月 30 日,攻击者已从攻击地址转移出 6,250 ETH 到交易所,其中包括分别转移到 FTX 的 1,220 ETH、转移到 Huobi 的 3750 ETH 和转移到 Crypto.com 的 1 ETH。
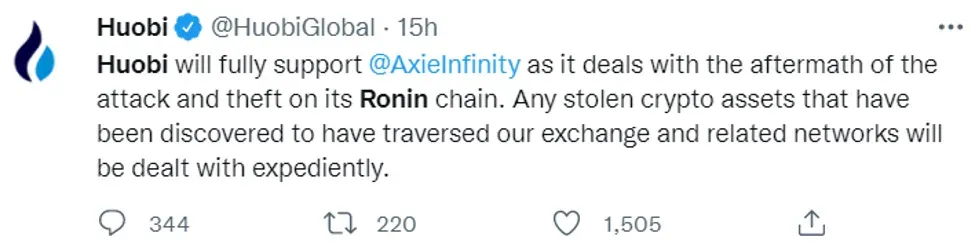
好消息是,这些交易所愿意协助项目方追回被盗资金。

结论
截至撰写本文时,攻击地址仍持有约 175,913 ETH,而有 1,279 ETH 正在转移中。我们将持续监测被盗资金的追踪情况,并及时与社区分享我们的发现。
其他数据
攻击者已获取 182,162.86 ETH。其中,173,600 ETH 直接来自项目盗窃,8,562.86 ETH 来自被盗的 USDC。
- 初始资金:1.0569 ETH 来自 Binance
- 被盗 ETH:173,600 ETH
- 从被盗 USDC 兑换的 ETH:8,562.86 ETH(4869.18508653411 到 Uniswap,3693.6752093176137 到 1inch)
- 已转移:6,250 ETH
参考
https://roninblockchain.substack.com/p/community-alert-ronin-validators?s=w
关于 BlockSec
BlockSec 是一家开创性的区块链安全公司,由一群全球知名的安全专家于 2021 年创立。公司致力于提升新兴 Web3 世界的安全性和可用性,以促进其大规模采用。为此,BlockSec 提供智能合约和 EVM 链 安全审计 服务,用于安全开发和主动威胁拦截的 Phalcon 平台,用于资金追踪和调查的 MetaSleuth 平台,以及供 Web3 构建者在加密世界高效冲浪的 MetaSuites 扩展。
迄今为止,公司已为 MetaMask、Uniswap Foundation、Compound、Forta 和 PancakeSwap 等 300 多家尊贵客户提供服务,并在两轮融资中从 Matrix Partners、Vitalbridge Capital 和 Fenbushi Capital 等知名投资者那里获得了数千万美元的投资。
官方 Twitter 账号:https://twitter.com/BlockSecTeam




