VEE Finance 发布了一份关于近期安全事件的报告。报告中称,主要原因是“Vee Finance 预言机价格操纵和预言机价格获取未处理小数,导致了互换前预期的滑点检查未能生效。”
“事故的主要原因是在创建杠杆交易订单过程中,预言机只使用了 Pangolin 池的价格作为价格反馈源,而池价格的波动幅度超过了 3%。预言机刷新了价格,导致攻击者操纵了 Pangolin 池的价格。Vee Finance 预言机价格操纵和预言机价格获取未处理小数,导致了互换前预期的滑点检查未能生效。” — 引用自 VEE Finance 发布的研究报告。
然而,经过我们仔细调查,我们发现事实可能并非如此。真正的原因是攻击者创建了一个假的 ctokenB 并将其传递给合约。由于 ctokenB 由攻击者控制,它可以返回任意的底层代币,用于计算代币价格。这是攻击的真正根本原因。
整个过程
有一个名为 createOrderERC20ToERC20 的外部函数,任何用户都可以调用它来创建一个代币兑换,使用通过将抵押品放入合约获得的 ctoken。ctoken 包含一个代表真实代币的底层代币。
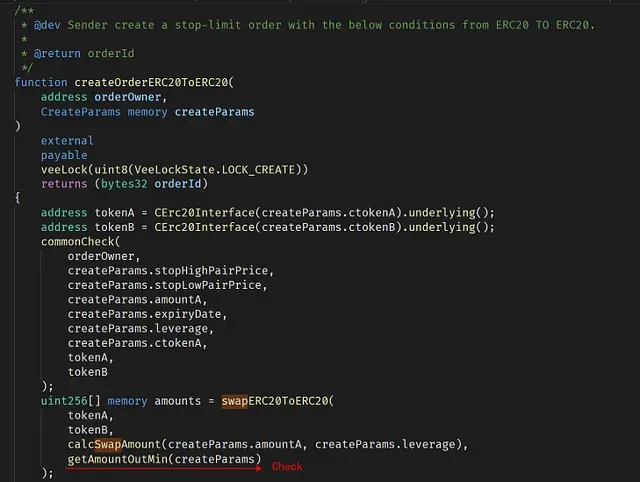
在正常情况下,调用 createOrderERC20ToERC20 来交易一对代币时,dapp 需要确保交易不会造成任何损失(否则 dapp 会亏钱)。这一点通过调用 getAmountOutMin 函数来强制执行。
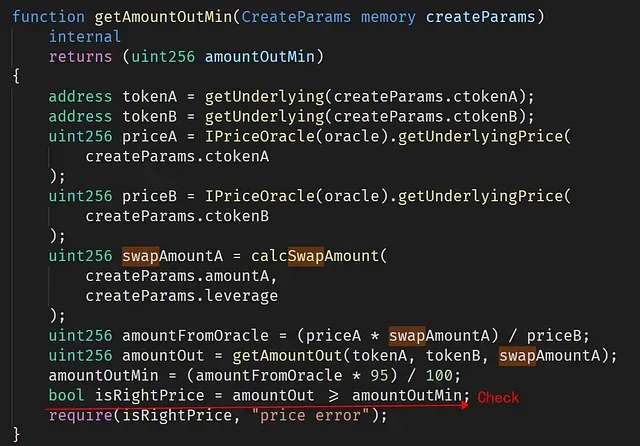
假设我们将 0.95 ETH 放入 dapp 并获得一个价值 0.5 ETH 的 ctoken(超额抵押)。然后我们可以使用 3 倍杠杆,让 dapp 代表用户交易 1.5 ETH 以换取另一种代币(例如 tokenX)。在这种情况下,为了防止损失,dapp 需要确保交易的 tokenX 的价值不能低于 0.95 * 1.5 ETH(否则 dapp 有亏损的风险)。dapp 利用外部价格预言机来计算 ETH 和 tokenX 的价值。
然而,createOrderERC20ToERC20 函数不验证传入的 ctokenB。因此,攻击者可以实现自己的合约作为 ctokenB 并将其馈送给 createOrderERC20ToERC20 函数。结果是,这个假的 ctokenB 在被调用 createOrderERC20ToERC20 和 getAmountOutMin 时可以返回 LINK(0x5947bb275c521040051d82396192181b413227a3)作为底层代币,但在被调用 IPriceOracle(oracle).getUnderlyingPrice(createParams.ctokenB) 时却返回 BTC 作为底层代币。因此,它可以绕过 isRightPrice 检查——因为用于计算价格的代币是 BTC(而不是 LINK)。这可以通过 priceB 的返回值 0x15e1549d1216fe9fc032e7c00000(443783124870000000000000000000000)得到确认。这是 BTC 的价格。
结论
总而言之,攻击者利用了 ctokenB 检查的缺失。由于 ctokenB 不是一个受信任的代币,因此 ctokenB 返回的底层代币是不可信的。然而,在此次攻击中,价格预言机并未受到损害。
经验教训
使 DeFi 项目安全绝非易事。除了代码审计,我们认为社区应该采取积极主动的方法来监控项目状态,并在攻击发生前进行拦截。
关于 BlockSec
BlockSec 是一家开创性的区块链安全公司,成立于 2021 年,由一群全球杰出的安全专家创立。公司致力于提升新兴 Web3 世界的安全性和可用性,以促进其大规模采用。为此,BlockSec 提供智能合约和 EVM 链安全审计服务,用于安全开发和主动威胁拦截的Phalcon平台,用于资金追踪和调查的MetaSleuth平台,以及用于 Web3 构建者高效冲浪加密世界的MetaSuites扩展。
迄今为止,公司已服务超过 300 家尊贵客户,如 MetaMask、Uniswap Foundation、Compound、Forta 和 PancakeSwap,并在两轮融资中从 Matrix Partners、Vitalbridge Capital 和 Fenbushi Capital 等知名投资者那里获得了数千万美元的资金。
官方 Twitter 账号:https://twitter.com/BlockSecTeam




