11月5日,bZX协议报告遭遇黑客攻击。攻击者窃取了受影响智能合约中的代币。在对攻击交易进行初步分析后,我们怀疑此次攻击是由于开发者的私钥泄露所致。
攻击过程
攻击过程大致简单。通过调用特权函数 transferOwnership 将受影响智能合约的所有权转移给一个新的合约,例如 0x0acc0e5faa09cb1976237c3a9af3d3d4b2f35fa5。然后,新的合约所有者可以将已授权给该智能合约的所有代币转移到任意地址。
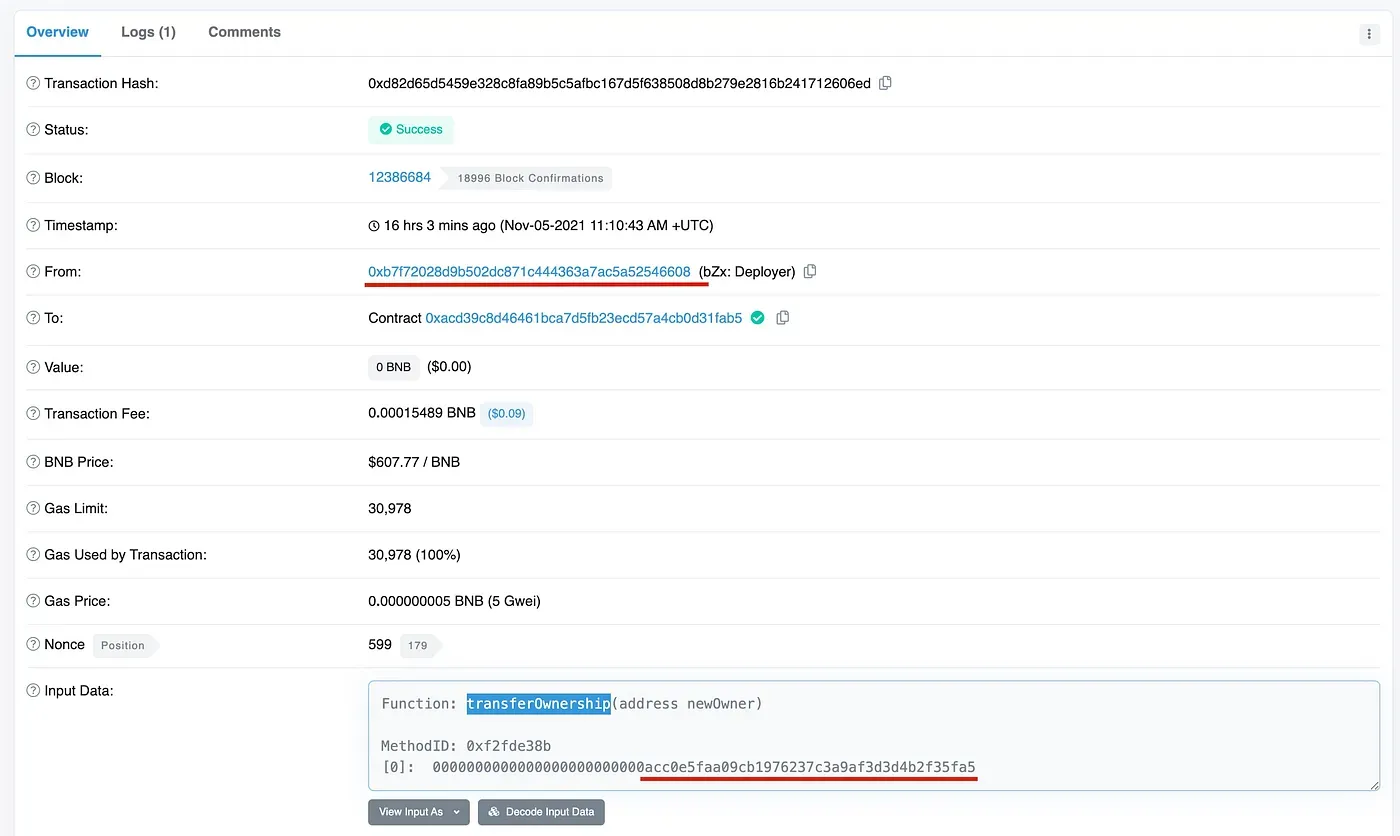
请注意,特权函数 transferOwnership 只能由智能合约的当前所有者调用。事实上,我们发现调用此函数的地址是 0xb7f72028d9b502dc871c444363a7ac5a52546608,这是受影响智能合约的创建者。
我们无法确切知道合约创建者将所有权转移给其他地址的确切原因。然而,我们怀疑这是由于开发者的私钥泄露(或被盗)所致。
结论
总而言之,DApp私钥的安全性对于应用程序的安全性至关重要,特别是对于那些未使用DAO的项目。我们建议项目方可以采用一些新技术,如机密计算和MPC来保护私钥。
关于BlockSec
BlockSec 是一家开创性的区块链安全公司,由一群全球顶尖的安全专家于2021年创立。公司致力于提升新兴Web3世界的安全性和可用性,以促进其大规模采用。为此,BlockSec 提供智能合约和EVM链安全审计服务,用于安全开发和主动阻止威胁的Phalcon平台,用于资金追踪和调查的MetaSleuth平台,以及供Web3开发者在加密世界高效冲浪的MetaSuites扩展。
至今,公司已服务于MetaMask、Uniswap Foundation、Compound、Forta和PancakeSwap等300多家知名客户,并从Matrix Partners、Vitalbridge Capital和Fenbushi Capital等知名投资机构的两轮融资中获得了数千万美元。
官方Twitter账号:https://twitter.com/BlockSecTeam




