7月21日,我们的DeFiRanger系统报告了几笔可疑交易。经过人工分析,我们确认这些交易是针对Sanshu Inu的攻击。具体来说,Sanshu Inu的Memstake合约通过滥用“通缩”机制受到了攻击。 接下来,我们将使用多笔攻击交易来阐述攻击过程。
攻击流程
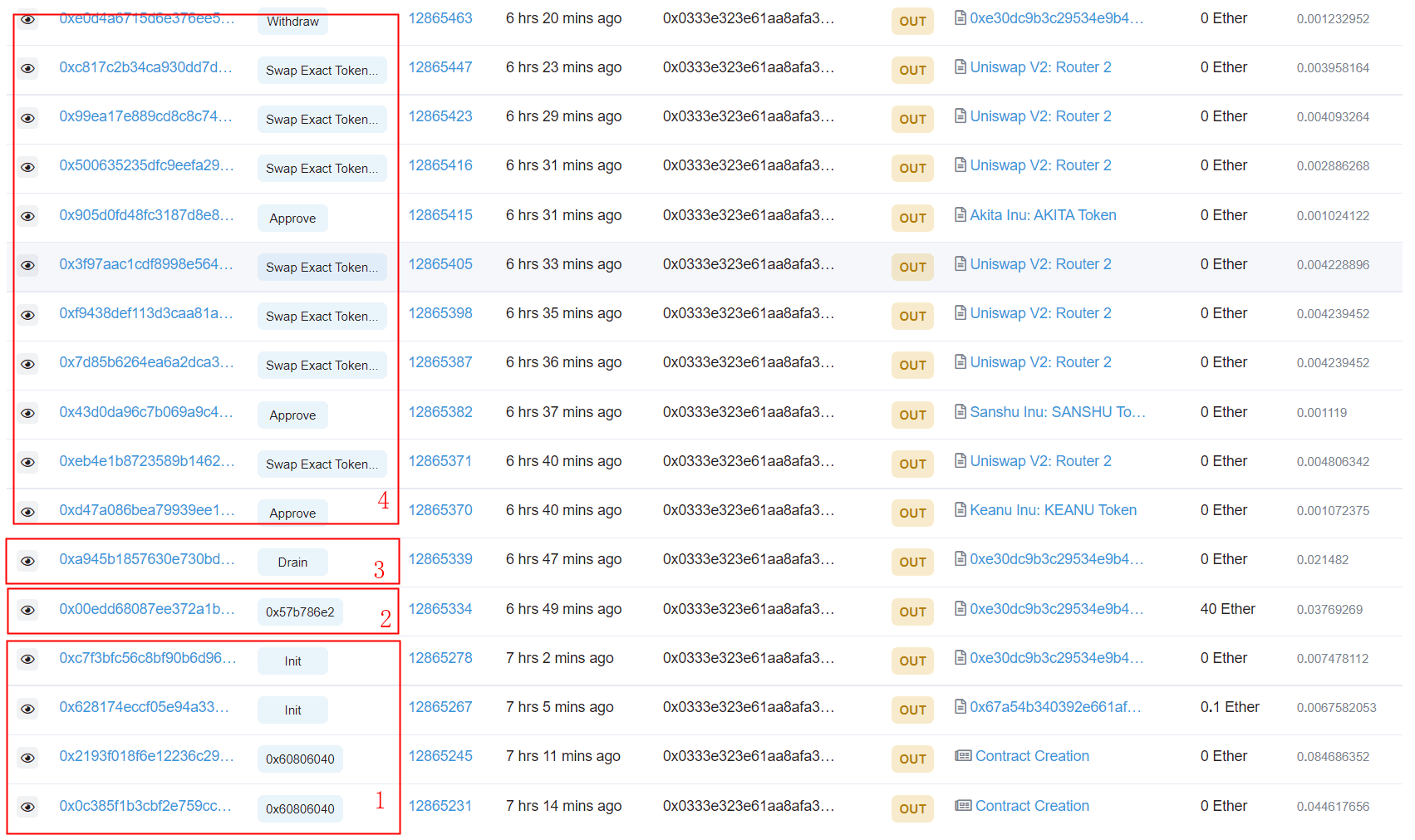
下图列出了攻击者 (0x333) 发起的一些交易。
攻击包含四个步骤,其中最关键的是第二步,它利用了ERC20代币的通缩机制来操纵Memstake智能合约的奖励计算。
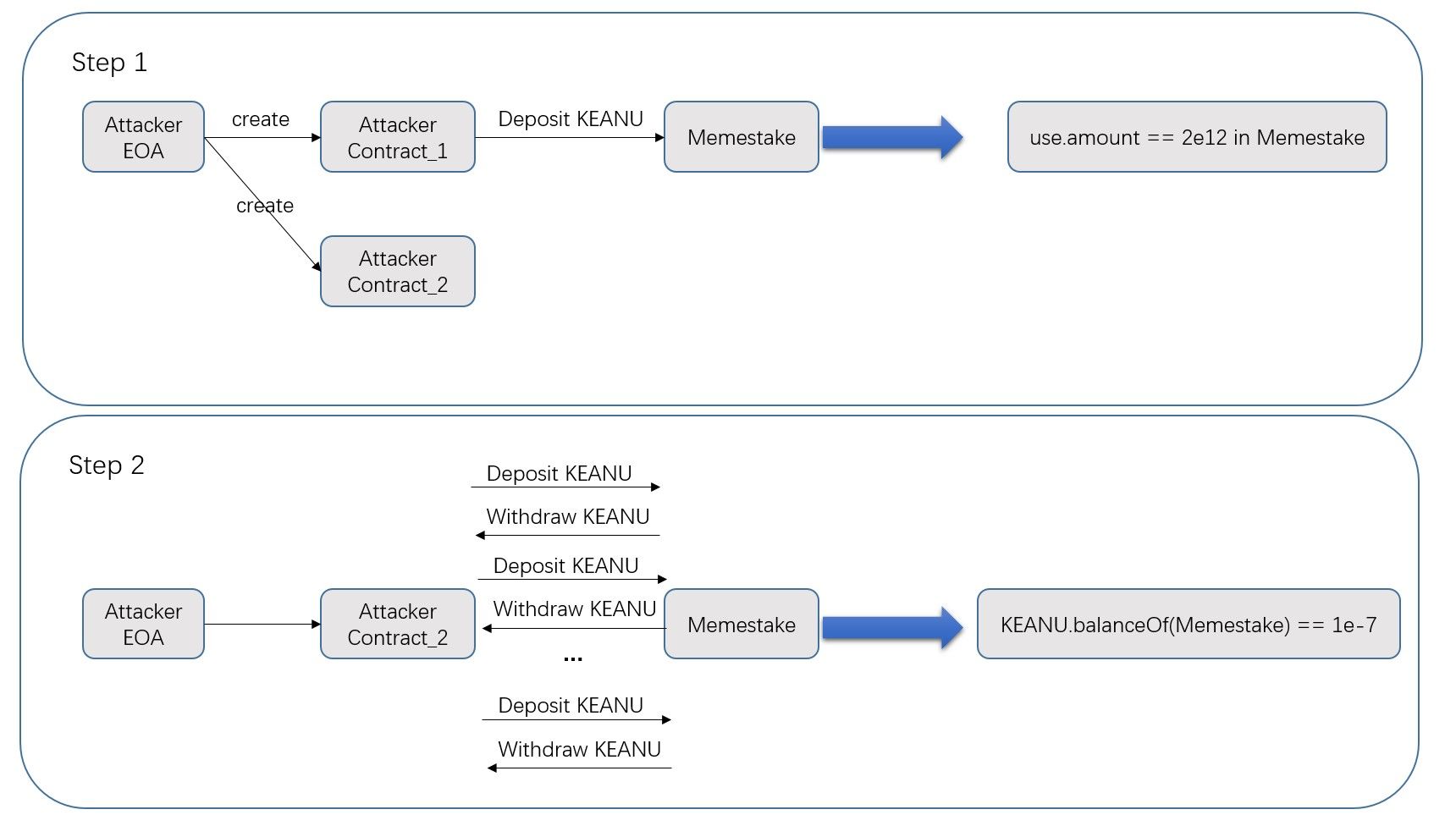
-
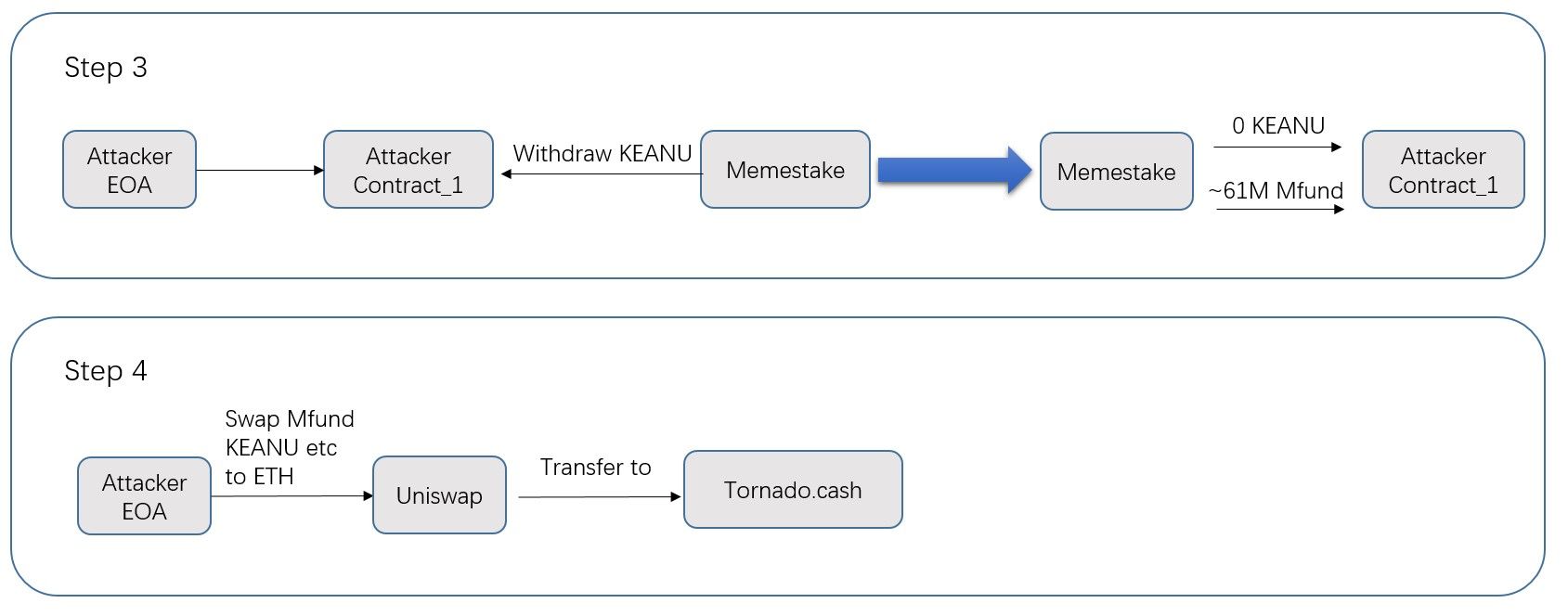
步骤2(操纵):攻击者首先通过闪电贷(Towards A First Step to Understand Flash Loan and Its Applications in DeFi Ecosystem (SBC 2021))从uniswapV2借入大量KEANU代币,然后使用在步骤1中创建的第二个智能合约将代币存入/提取Memestake。由于KEANU具有通缩机制,每次交易会销毁2%的代币,因此实际存入Memestake的代币数量小于Memestake合约维护的
user.amount值。攻击者重复此过程,使Memestake中的KEANU代币数量减少到很小的数值(1e-07)。参见交易 0x00ed 和下图。
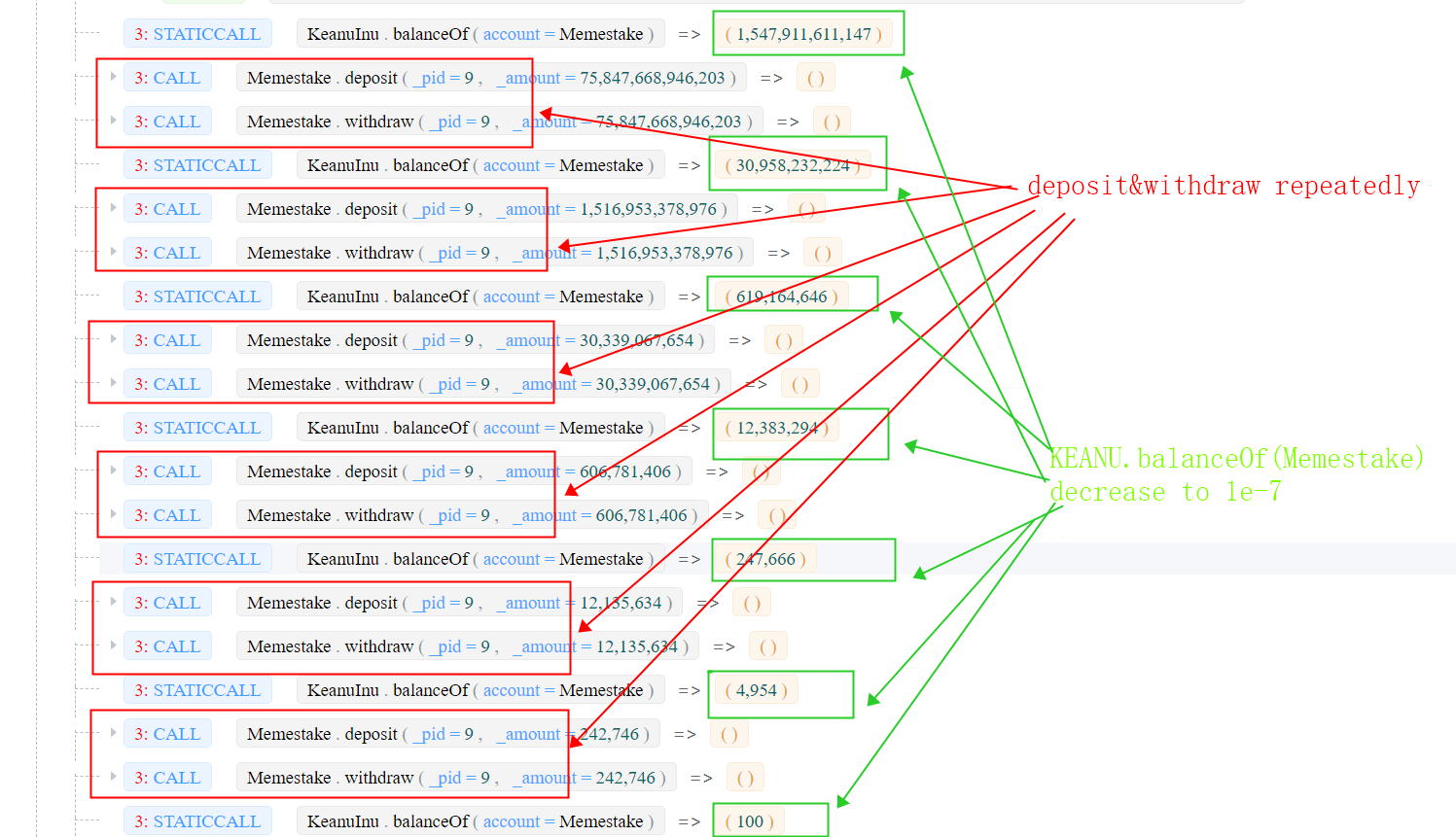
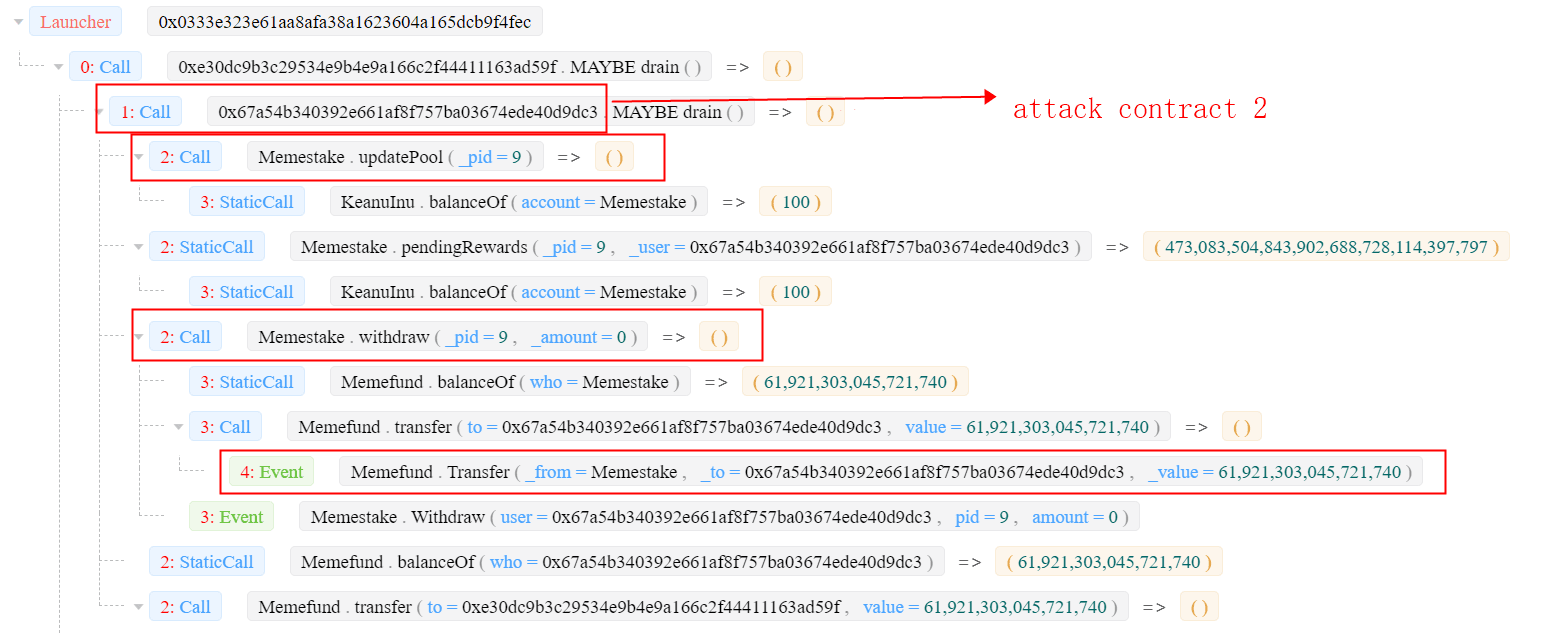
- 步骤3(获利):攻击者调用
Memestake.updatePool()来更新accMfundPerShare。此值取决于KEANU代币的数量(在第二步中被操纵)。然后,攻击者获得了大量的Mfund(约61M)。 有关更多详细信息,请参见交易 0xa945。
- 步骤4(兑换为WETH):攻击者将Mfund和KEANU兑换为WETH,并通过Tornado.Cash洗钱。攻击者获得了55.9484578158357 ETH的利润。
杂项
有趣的是,攻击的第二/第三步与Flashbots有关。第二步用38 ETH购买KEANU(0x00ed)。此交易受到了沙盒攻击(通过Flashbots)——这使得攻击者本人成为了沙盒攻击的受害者。第三步(0xa945)在uniswap上出售Mfund,这产生了一个套利机会,被Flashbots的搜索者捕捉到。
关于BlockSec
BlockSec是一家开创性的区块链安全公司,由一群全球知名的安全专家于2021年创立。公司致力于提升新兴Web3世界的安全性和可用性,以促进其大规模采用。为此,BlockSec提供智能合约和EVM链安全审计服务,用于安全开发和主动阻断威胁的Phalcon平台,用于资金追踪和调查的MetaSleuth平台,以及供Web3开发者在加密世界高效冲浪的MetaDock扩展。
迄今为止,公司已服务超过300家尊贵客户,如MetaMask、Uniswap Foundation、Compound、Forta和PancakeSwap,并在两轮融资中从Matrix Partners、Vitalbridge Capital和Fenbushi Capital等知名投资者那里获得了数千万美元的投资。
官方Twitter账号:https://twitter.com/BlockSecTeam




