0x.1 前言
2021年11月15日,我们的内部监控系统在BSC上检测到可疑的闪电贷交易。 经过调查,我们发现这是一起针对Nerve Bridge的攻击,包括fUSDT和UST的MetaPools。
截至本文撰写之时,攻击者已耗尽Nerve质押池中fUSDT和UST的流动性,并获利900 BNB。
令人惊讶的是,我们发现易受攻击的代码是从Saddle.Finance分叉而来的,而Saddle.Finance的代码已经在2021年11月6日导致Synapse Bridge损失了8亿美元。 具体来说,该漏洞的根本原因在于不同库中计算代币兑换金额的实现不一致。
然而,并不存在任何公开的报告来分析这次安全事件。 因此,在本博客中,我们旨在提供一个全面的分析,包括项目的机制、漏洞和攻击。
0x2. 背景
0x2.1 什么是MetaPool?
基本上,Curve提供了两种类型的稳定币兑换池,即标准稳定币兑换池(Standard StableSwap Pool)和MetaPool。前者是一个完全的AMM,用于创建不同稳定币之间的跨市场交易 [1]。这是最常用的池类型,例如Curve.3pool,它由DAI、USDC和USDT组成。然而,这种池无法隔离稳定币之间的风险,可能导致LP提供者遭受巨大损失。
因此,提出了MetaPool来解决这个问题。
正如Curve所言 [2],“它允许一个单一的代币与另一个(基础)池中的所有代币进行兑换,而不会稀释其流动性”。它本质上是稳定币与标准稳定币兑换池(由其他几种稳定币组成)的LP代币之间的兑换池。在我们的上下文中,我们将这两种类型的稳定币称为池稳定币和底层稳定币。
例如,本次事件的一个受害者正是fUSDT与Nerve.3pool的LP代币(包括BUSD、USD和USDC)的MetaPool,这个池的结构本质上是[fUSDT, LP代币(BUSD, USD, USDC)]。因此,fUSDT是池稳定币,而BUSD、USD和USDC是底层稳定币。
0x2.2 易受攻击代码的来源
Curve的MetaPool是用Vyper实现的。为了支持Solidity的开发,Saddle.Finance的开发团队用Solidity重写了代码。作为本次漏洞的最初来源,它已经被 Synapse 和 Nerve 分叉并采用。11月6日,Synapse遭到攻击。
MetaPool中的大约820万美元资金被提取,但由于攻击者犯了一个“愚蠢”的错误,实际上并没有损失任何资金 [3]。
在此之后,Saddle.Finance采取了紧急行动,通过暂停所有MetaPool合约来保障其资金安全。然而,Nerve Bridge并未采取任何行动,这不可避免地导致了这次安全事件。
相关的合约地址如下:
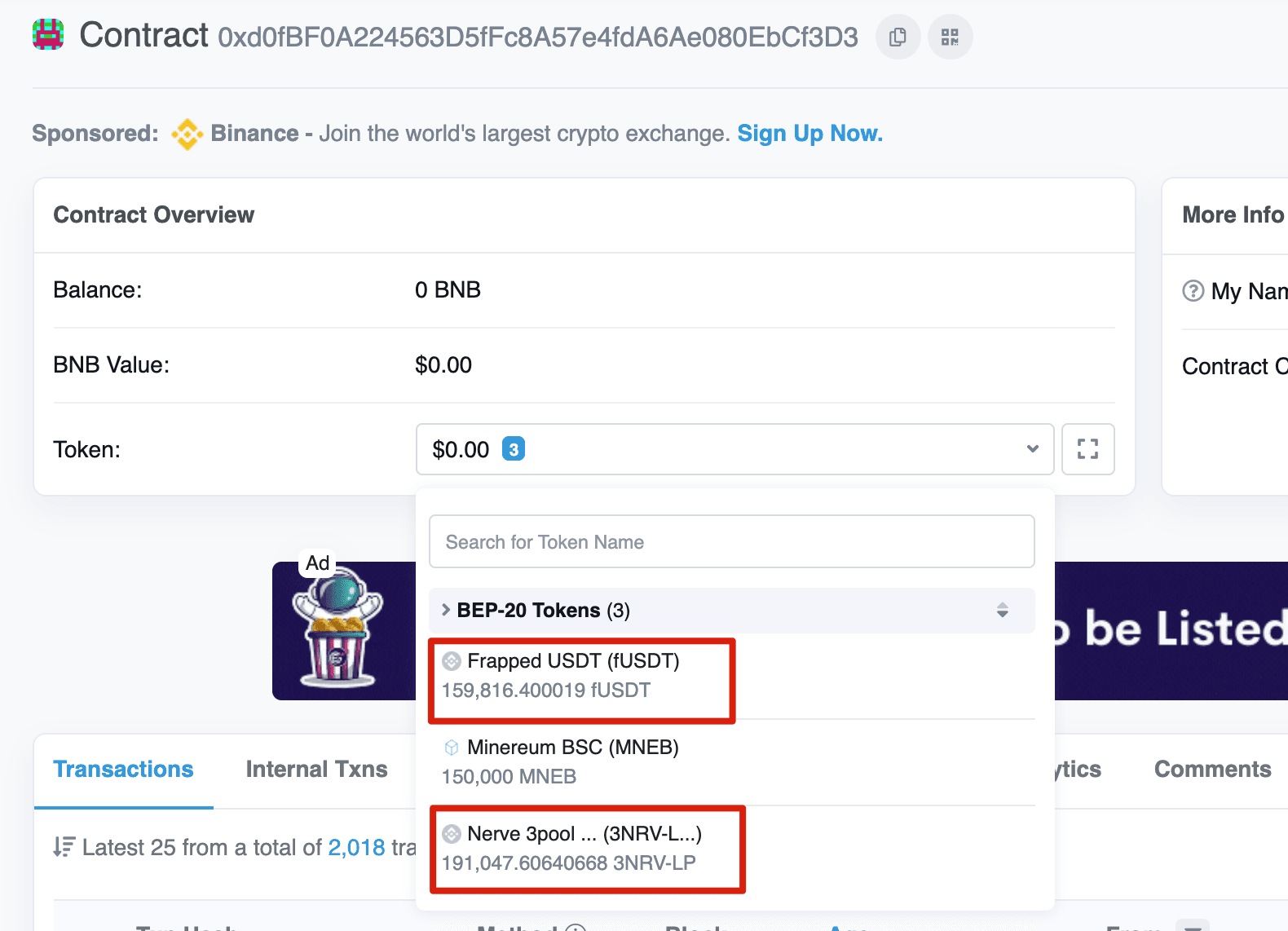
- MetaSwap: 0xd0fBF0A224563D5fFc8A57e4fdA6Ae080EbCf3D3
- SwapUtils: 0x02338Ee742ddCDe44488640F4edf1Aa947E670E7
0x3. 漏洞分析
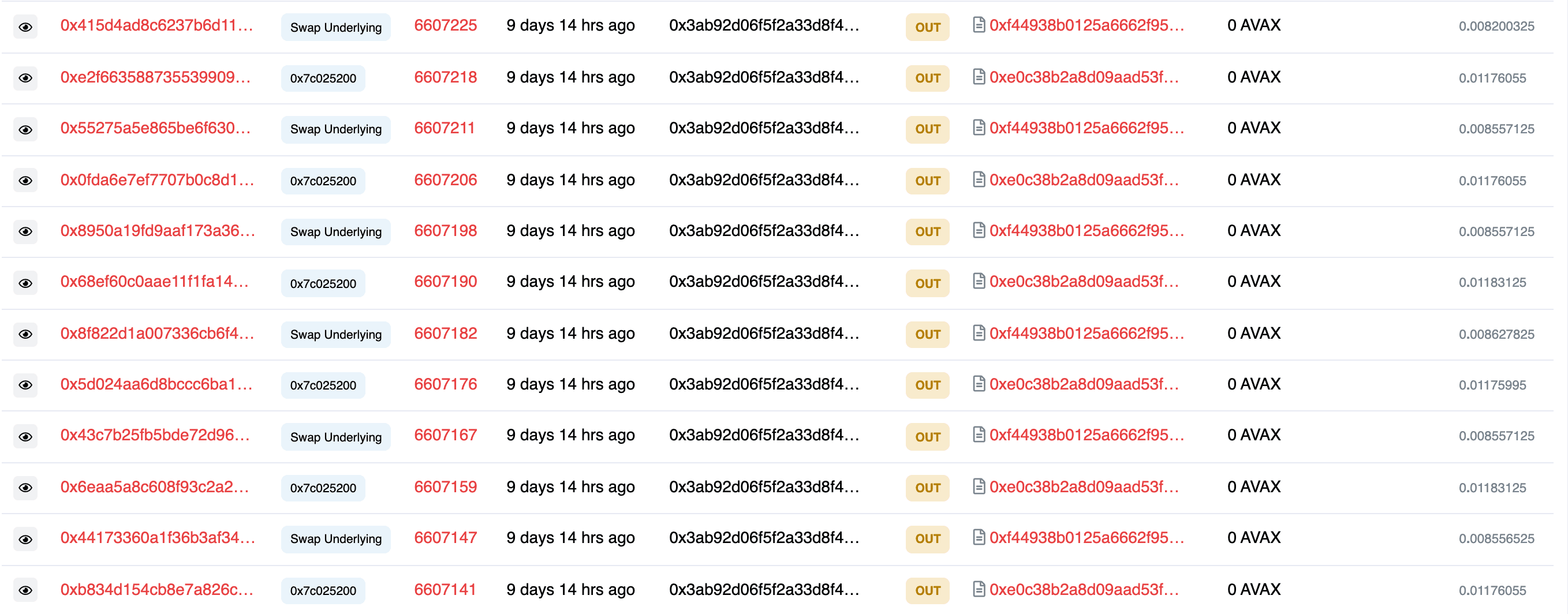
在MetaPool中,有两个重要函数,即swap和swapUnderlying。具体来说,前者用于兑换LP代币和池稳定币,后者用于兑换池稳定币和底层稳定币。
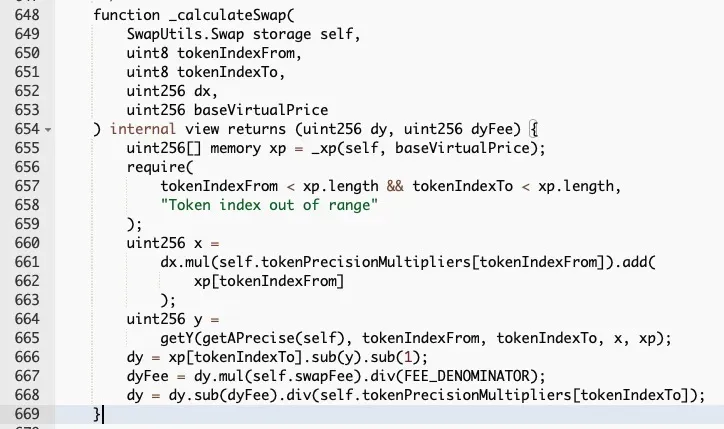
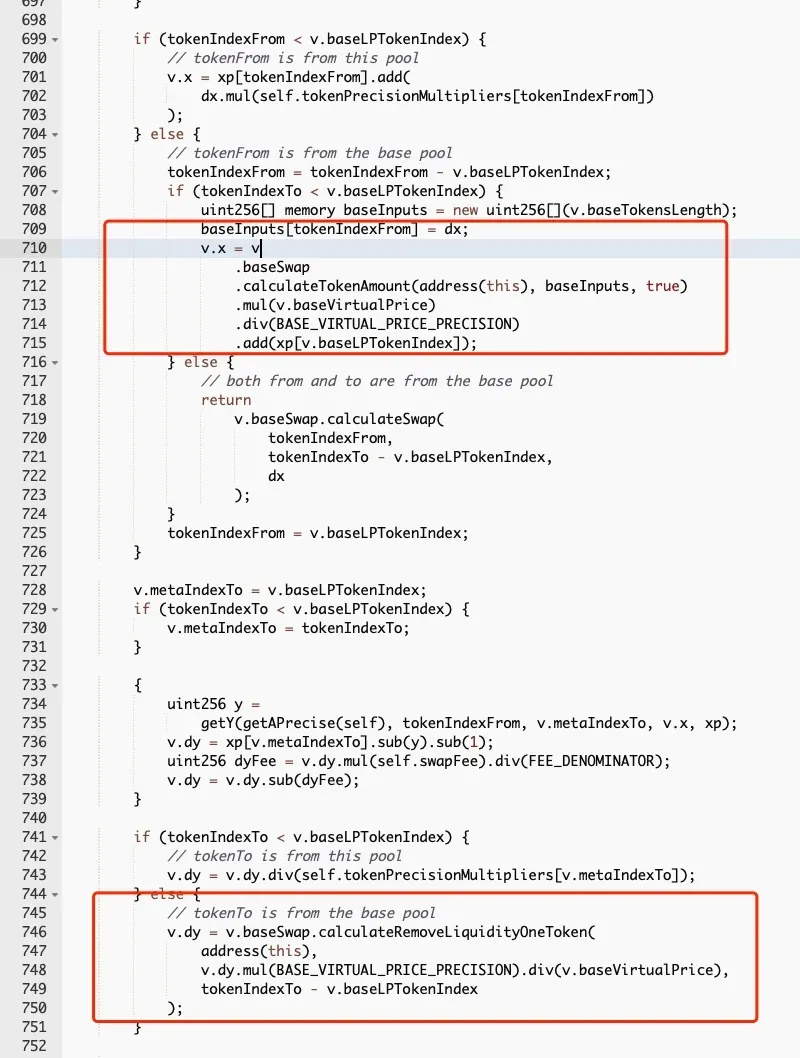
然而,这两个函数的实现是不一致的。如上两图所示。红色矩形框中的代码片段用于通过衡量LP代币的“虚拟价格”(随着更多费用进入而从基准值1开始增加)来调整LP代币的价值。而swap函数忽略了虚拟价格的影响,这意味着LP代币的价值将被低估。换句话说,可以兑换出更多的LP代币。
因此,可以通过先用相应的LP代币收回底层稳定币的流动性,然后调用swapUnderlying函数来兑换池稳定币,从而可能获得更多的池稳定币。
0x4. 攻击分析
我们将以示例交易为例来说明攻击。
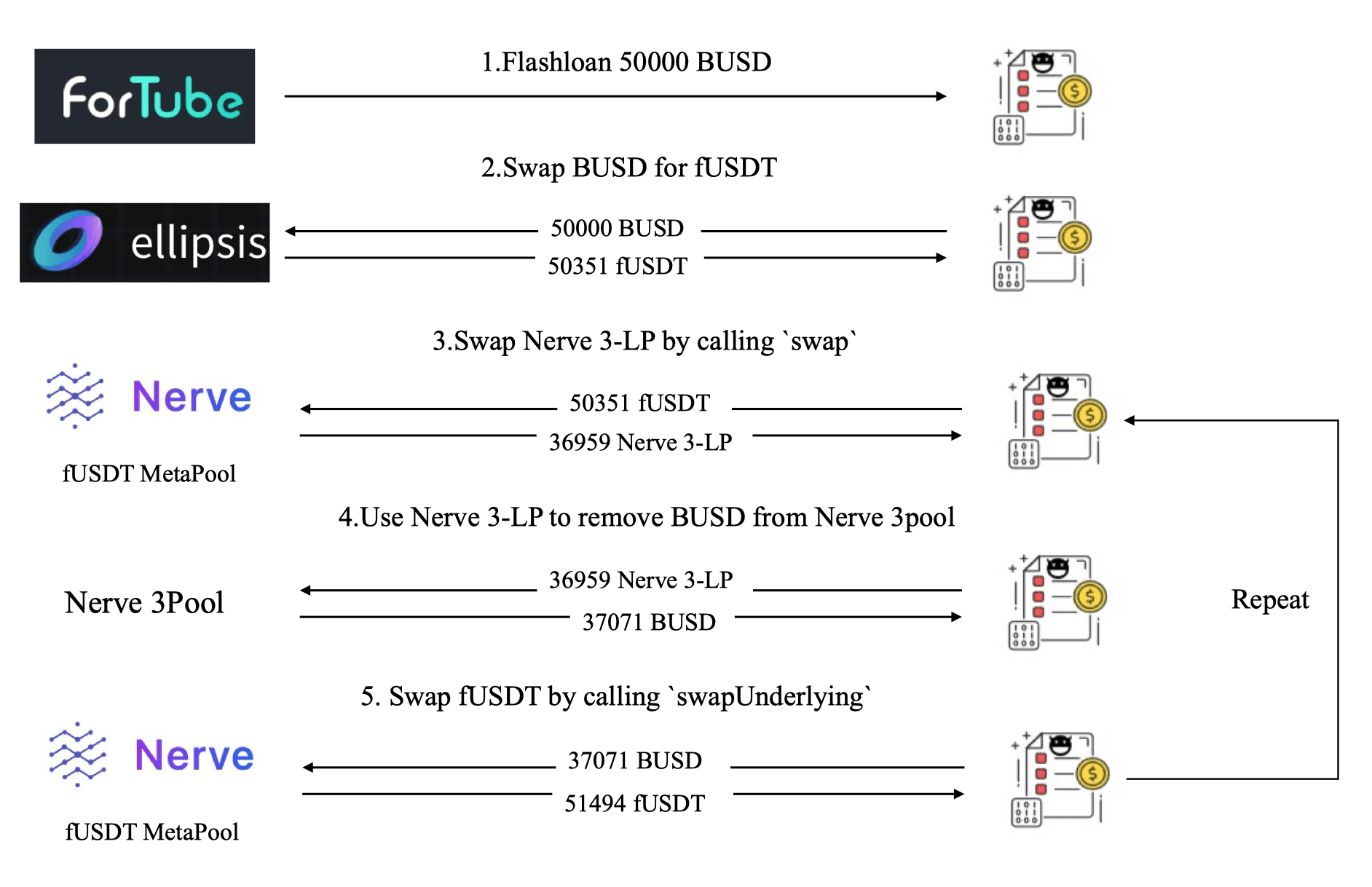
图6显示攻击者采取了以下五个步骤来发动攻击:
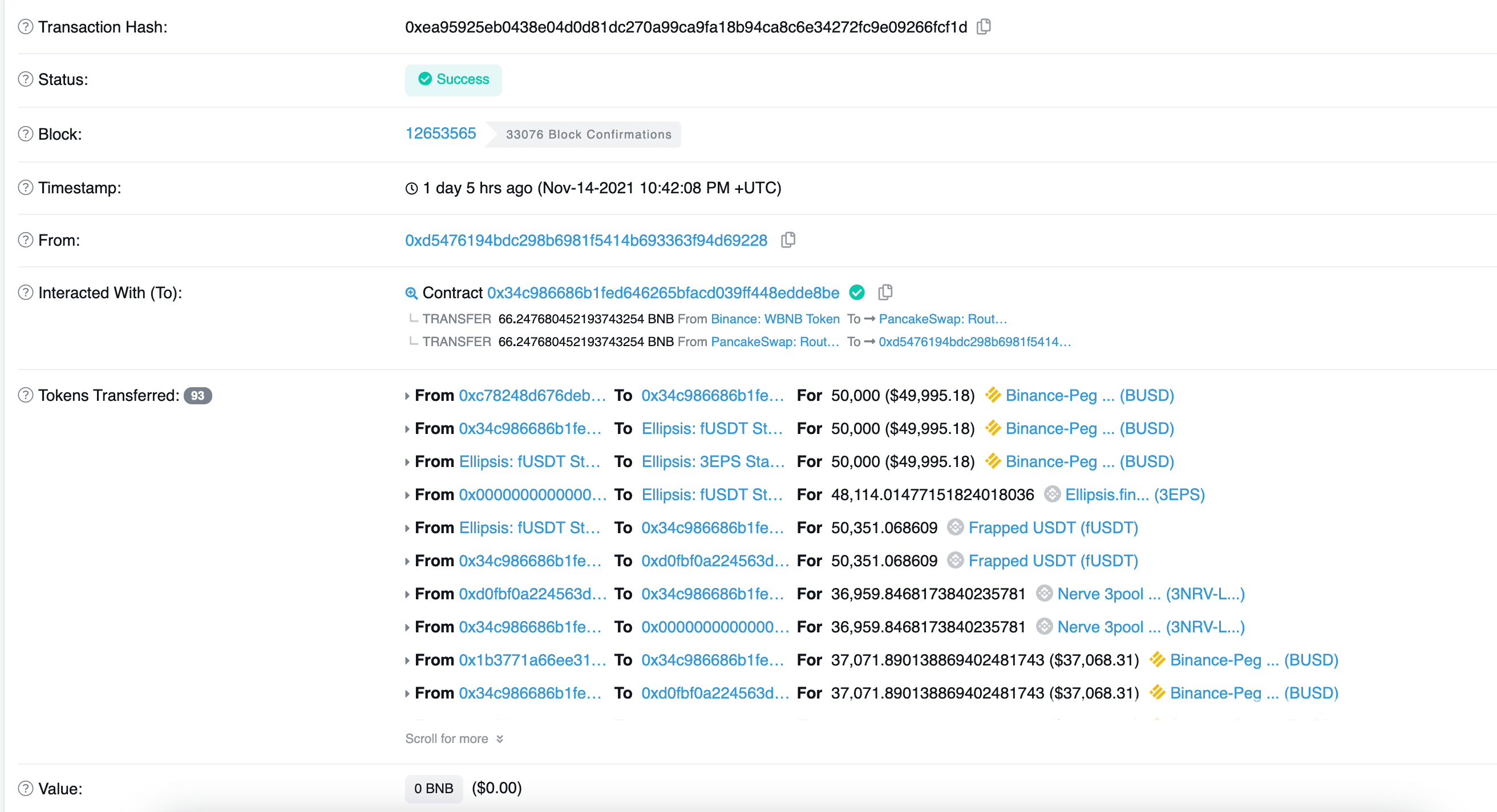
- 步骤1:从Fortube通过闪电贷借入50,000 BUSD。
- 步骤2:从Ellipsis将50,000 BUSD兑换为50,351 fUSDT。
- 步骤3:调用MetaSwap的
swap函数,以较大的滑点将50,351 fUSDT兑换为36,959 Nerve 3-LP。 - 步骤4:调用Nerve.3pool的
removeLiquidityOneCoin函数,使用LP代币(上一步骤中收到)移除BUSD流动性,即37,071 BUSD。 - 步骤5:调用MetaSwap的
swapUnderlying函数,将BUSD兑换为fUSDT,收到51,494 fUSDT。
攻击者重复执行上述五个步骤(约200多笔交易),耗尽了MetaPool的流动性,最终获利900 BNB。
有趣的是,攻击者采用了与Synapse事件中相同的攻击方式,这种方式并非实现目标的优化方式。或者,可以通过更有效的方式发动攻击,例如,应用优化的参数在一笔交易中耗尽流动性。结果表明,攻击者可能并未完全理解这个漏洞的根本原因。
参考
[1] https://curve.fi/files/stableswap-paper.pdf
[2] https://resources.curve.fi/lp/depositing/depositing-into-a-metapool/
[3] https://synapseprotocol.medium.com/11-06-2021-post-mortem-of-synapse-metapool-exploit-3003b4df4ef4
致谢:Hailin Wang, Lei Wu, Yajin Zhou @BlockSec
Twitter: https://twitter.com/BlockSecTeam




