我们很高兴发布 Rustle —— BlockSec 为 NEAR 社区提供的首个自动化审计工具。
Rustle 具有以下优点:
- Rustle 目前可以检测 NEAR 合约中 20 多种类型的漏洞。请参阅“检测器”部分获取完整的检测器列表。
- Rustle 易于使用。我们提供了详细的安装命令和教程。此外,我们还为用户准备了 Docker,以便快速上手。
- Rustle 非常快速,大多数 NEAR 合约分析可以在 3 分钟内完成。
- Rustle 用户友好,报告格式支持 CSV 和 JSON。我们还提供了一个脚本,帮助您将结果导入 Notion。
检测器
Rustle 可以检测的所有漏洞。详细文档可在此处找到。
| 检测器 ID | 描述 | 严重程度 |
|---|---|---|
| unhandled-promise | 检测未处理的 Promise | 高 |
| non-private-callback | 回调函数缺少 #[private] 宏 | 高 |
| reentrancy | 查找易受重入攻击的函数 | 高 |
| unsafe-math | 算术运算缺少溢出检查 | 高 |
| self-transfer | 缺少发送方 != 接收方的检查 | 高 |
| incorrect-json-type | 参数或返回值中使用错误的类型 | 高 |
| div-before-mul | 由于操作顺序不正确导致的精度损失 | 中 |
| round | 未指定 ceil 或 floor 的四舍五入 | 中 |
| lock-callback | 回调函数中的 panic 可能导致合约被锁定 | 中 |
| yocto-attach | 特权函数中缺少 assert_one_yocto | 中 |
| prepaid-gas | ft_transfer_call 中缺少预付费 gas 检查 | 低 |
| non-callback-private | 在非回调函数中使用 #[private] 宏 | 低 |
| unused-ret | 函数结果未被使用或检查 | 低 |
| upgrade-func | 合约中没有升级函数 | 低 |
| tautology | 条件分支中使用重言式 | 低 |
| inconsistency | 使用相似但略有不同的符号 | 低 |
| timestamp | 查找所有时间戳的使用 | 信息 |
| complex-loop | 查找所有具有复杂逻辑的循环,可能导致 DoS | 信息 |
| ext-call | 查找所有跨合约调用 | 信息 |
| promise-result | 查找所有 promise 结果的使用 | 信息 |
| transfer | 查找所有转账操作 | 信息 |
如何使用
我们使用 Rustle 分析了一个流行的 NEAR 合约(例如 LiNEAR)。命令已在 Ubuntu 20.04 LTS 中进行测试。
-
准备要让 Rustle 分析的 NEAR 合约。
git clone https://github.com/linear-protocol/LiNEAR.git ~/near-repo/LiNEAR -
通过运行
./rustle开始分析。./rustle -t ~/near-repo/LiNEAR ~/near-repo/LiNEAR/contracts/linear
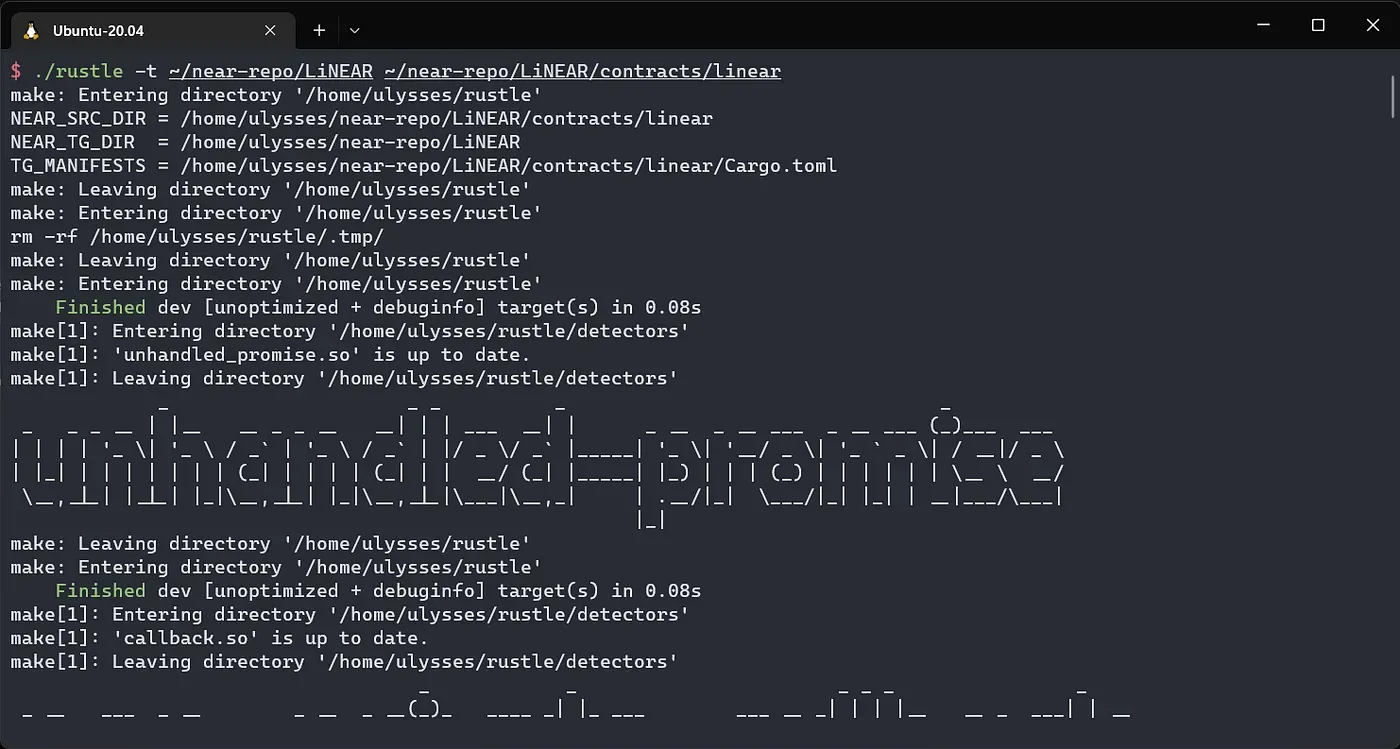
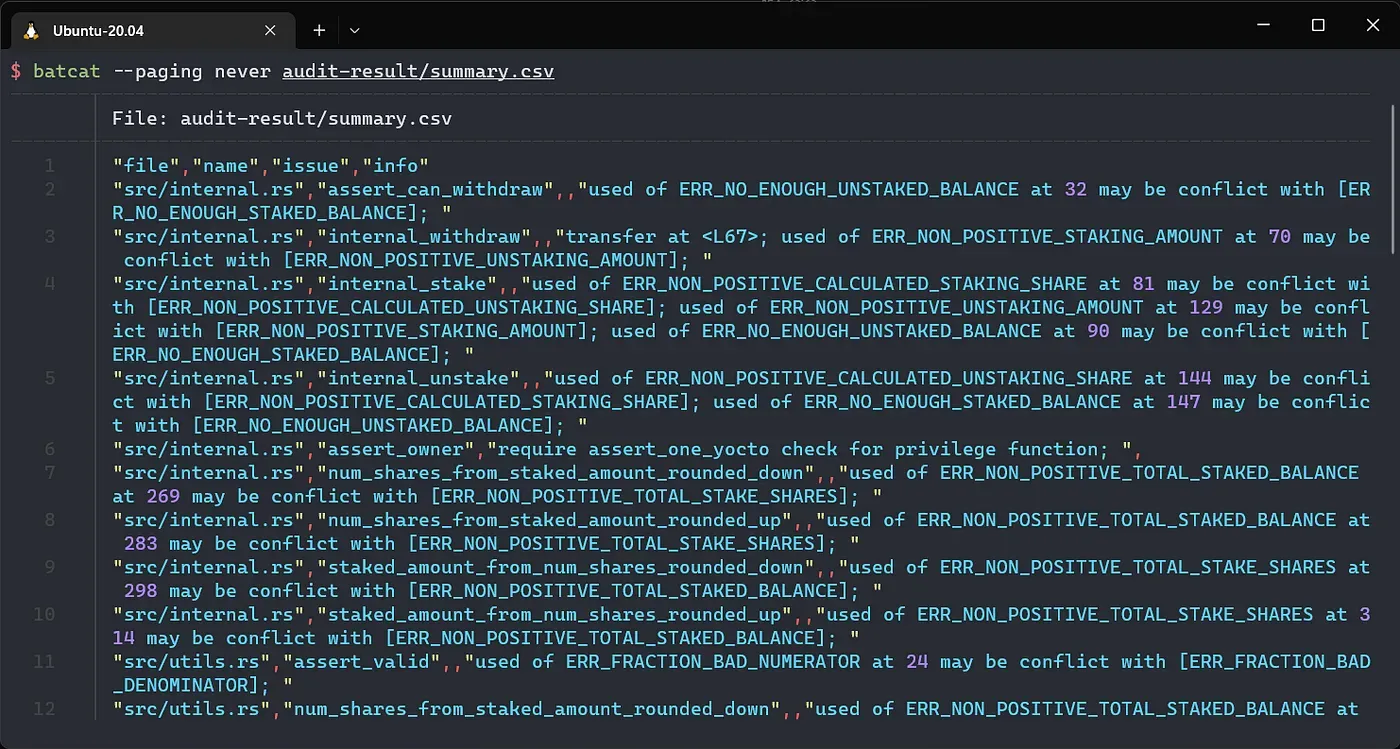
- 在
audit-result/summary.csv中检查报告
- 您可以指定要使用的检测器或严重性组。
./rustle -h 查看详细信息。
示例:
./rustle -t ~/near-repo/LiNEAR ~/near-repo/LiNEAR/contracts/linear -d high,medium,complex-loop
额外说明
Rustle 可用于开发过程,以迭代方式扫描 NEAR 智能合约。这可以节省大量手动工作并减轻部分潜在问题。但是,复杂逻辑或与语义相关的问题仍然是 Rustle 的局限性。定位复杂的语义问题需要 BlockSec 的专家进行全面细致的审查。请联系我们进行审计服务。
也欢迎提交 Issue 和 Pull Request。
关于 BlockSec
BlockSec 是一家开创性的区块链安全公司,由一群享誉全球的安全专家于 2021 年创立。公司致力于提高新兴 Web3 世界的安全性和可用性,以促进其大规模采用。为此,BlockSec 提供智能合约和 EVM 链安全审计服务、用于安全开发和主动威胁拦截的 Phalcon 平台、用于资金追踪和调查的 MetaSleuth 平台,以及用于 Web3 构建者在加密世界中高效冲浪的 MetaSuites 扩展。
迄今为止,公司已为 MetaMask、Uniswap Foundation、Compound、Forta 和 PancakeSwap 等 300 多家知名客户提供服务,并在两轮融资中从 Matrix Partners、Vitalbridge Capital 和 Fenbushi Capital 等知名投资者处获得了数千万美元的投资。
官方 Twitter 账号:https://twitter.com/BlockSecTeam




