2022年9月16日,我们发现一些攻击者通过重放EthereumPoW(又称PoW链)的PoS链消息(即calldata)成功窃取了大量ETHW。 此次漏洞利用的根本原因是PoW链上的Omni桥使用了旧的chainId,未能正确验证跨链消息的实际chainId。
我们立即联系了EthereumPoW的官方团队。 该团队积极表示愿意采取行动,并且他们也尝试与Omni Bridge沟通。
That's why we asked the other day...
— EthereumPoW (ETHW) Official (@EthereumPoW) September 18, 2022
A message from the core -https://t.co/aemIaDFXvP
And a tweet to clarify - https://t.co/9bCKm0sugK
Thanks Blocksec, they were the 1st to pinpoint the issue.
Thanks the core and eip155, for protecting ETHW community.#safu #security https://t.co/htlLXQlTT7
然而,随着越来越多的攻击被观察到,我们认为应该将风险通知公众,并于2022年9月18日发布了警报。
由于目前仍存在对这些攻击的一些误解,例如认为是重放交易而非消息。在本报告中,我们希望提供详细的分析来澄清这一点。
攻击分析
以下是一个利用交易的示例:
- 以太坊上的PoS交易:https://etherscan.io/tx/0xbddb0cc8bc9949321e1748f03503ed1a20dd618fbf0a51dc5734c975b1f8bdf5
- (利用) EthereumPow上的PoW交易: https://www.oklink.com/en/ethw/tx/0x9c072551861ce384203516f4d705176a2d2e262d5b571d853467425f1a861fb4
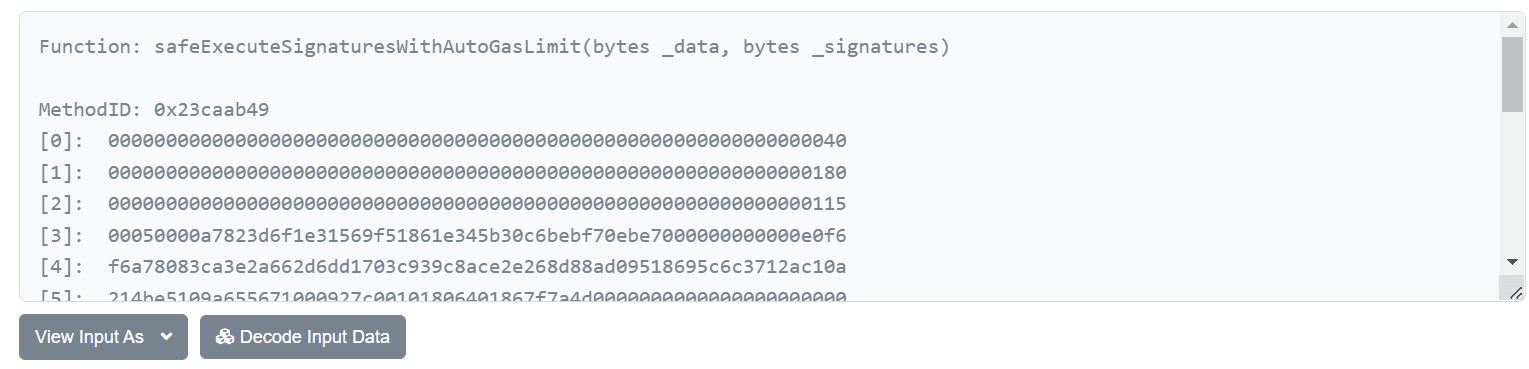
请注意,这两笔交易是不同的,然而,这两笔交易的calldata(或输入数据)是完全相同的:
0x23caab4900000000000000000000000000000000000000000000000000000000000000400000000000000000000000000000000000000000000000000000000000000180000000000000000000000000000000000000000000000000000000000000011500050000a7823d6f1e31569f51861e345b30c6bebf70ebe7000000000000e0f6f6a78083ca3e2a662d6dd1703c939c8ace2e268d88ad09518695c6c3712ac10a214be5109a655671000927c00101806401867f7a4d000000000000000000000000c02aaa39b223fe8d0a0e5c4f27ead9083c756cc2000000000000000000000000a6439ca0fcba1d0f80df0be6a17220fed9c9038a0000000000000000000000000000000000000000000000ad78ebc5ac62000000000000000000000000000000000000000000000000000000000000000000080000000000000000000000000000000000000000000000000000000000000001482faed2da812d2e5cced3c12b3baeb1a522dc67700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000105041c1b1c1c981df6cdaf073d55b78d7f0c7e2b421a569bff677a9464d1d5203672d7b5a3d6af658d14ebc11c26f2547fd0aed01750cca58753a0a79b297bad8a62a71eb6b7ac2099611604eff316e7fe733e9981c1b3890cb04ff9d43612e6f2687227f0226cfa27e4b6cd96a10865e04aa9e0f369dda7548771a094f69bf0a9fa6c27257e22d2b1bbb84beb52ad3966592037b328d352fce375a1fa75cb3fbfd18166f4177a19ad2cc74ce67da68f5ce17b857e6382c3ebf20f76482534135f426f4a74222daa07d9f401cb8baca4339ecd44e285df0e0cb88447a31d08b673cecc67d22c7e6e0ce5afd2ac9439c5a8b68f05077b850cdfdfb79cdaefc5b103bb693609440000000000000000000000000000000000000000000000000000这仅仅是调用safeExecuteSignaturesWithAutoGasLimit函数的输入数据。
显然,攻击者(0x82fae)首先通过Gnosis链的Omni桥转移了200 WETH,然后又在PoW链上重放了相同的消息,从而获得了额外的200 ETHW。 这样做,PoW链上部署的桥合约的余额可能会被耗尽。
漏洞分析
在分析了Omni桥的源代码后,我们发现其中确实存在验证chainId的逻辑。
function _isDestinationChainIdValid(uint256 _chainId) internal returns (bool res) {
return _chainId == sourceChainId();
}不幸的是,此合约中使用的已验证chainId来自名为unitStorage的存储中的值:
/**
* Internal function for retrieving chain id for the source network
* @return chain id for the current network
*/
function sourceChainId() public view returns (uint256) {
return uintStorage[SOURCE_CHAIN_ID];
}它不是通过EIP-1344提出的CHAINID操作码获取的实际chainId。 这可能是因为代码相当老旧(使用了Solidity 0.4.24)。 直到PoW链分叉之前,这段代码一直运行良好。
总之,此次利用的根本原因是ETHW链上的Omni桥使用了旧的chainId,未能正确验证跨链消息的实际chainId。 此外,其他协议也可能存在类似的问题。
影响
直接影响是攻击者可以窃取大量ETHW(以及桥在PoW链上拥有的其他代币),并在某些市场上(例如一些中心化交易所)进行交易。 这样做,ETHW的价格可能会因流动性增加而受到影响。 因此,用户/投资者在PoW链上交易这些代币时应保持谨慎。
结论
Solidity开发者在处理由合约本身维护的chainId时,应给予特别关注。
关于BlockSec
BlockSec是一家开创性的区块链安全公司,成立于2021年,由一群全球知名的安全专家创立。公司致力于增强新兴Web3世界的安全性和可用性,以促进其大规模采用。为此,BlockSec提供智能合约和EVM链安全审计服务,Phalcon平台用于安全开发和主动威胁拦截,MetaSleuth平台用于资金追踪和调查,以及MetaDock扩展,为Web3构建者在加密世界中高效冲浪。
迄今为止,公司已为MetaMask、Uniswap Foundation、Compound、Forta和PancakeSwap等300多家知名客户提供服务,并在两轮融资中获得了来自Matrix Partners、Vitalbridge Capital和Fenbushi Capital等知名投资者的数千万美元投资。
官方Twitter账号:https://twitter.com/BlockSecTeam




