案件背景
10月23日UTC下午2点,SHAR代币戏剧性地首次亮相,从0.00056美元的开盘价飙升至0.05986美元,市值在一小时内从零飙升至6000万美元,增长近100倍。在接下来的几个小时里,出现了一些关于SHAR团队的负面消息,指控他们参与了KOL操纵。随后,SHAR的价格在接下来的三个小时内跌至0.02393美元。尽管有负面消息,许多用户认为这不会对项目产生重大影响,因为一些知名的KOL继续购买该代币,并对SHAR的未来表示乐观。从晚上6点到8点,代币价格逐渐回升至0.042美元。
10月23日UTC晚上9点26分,一个由地址CHj3发起的交易将500,000,000 SHAR(接近总供应量的50%)兑换成19,619 WSOL,几乎耗尽了流动性池。此次兑换导致SHAR价格暴跌至0.0013美元,市值降至300万美元,这一切都发生在一分钟之内。SHAR币持有者遭受了“拉地毯”式的欺诈。
MetaSleuth上的资金流向分析
通过MetaSleuth,我们可以清晰地追踪此次“拉地毯”事件中的资金流向,并发现一些有价值的线索。此前在10月20日至10月22日之间,此次“拉地毯”事件的肇事者(控制地址CHj3的实体)从四个交易所(Binance 2 2595 SOL,KuCoin 950 SOL,MEXC 1 580 SOL 和 OKX 1 1920 SOL)提取了总计6045 SOL,并将其分配到14个地址。这14个地址均由肇事者控制,旨在人为抬高SHAR价格并积累大量SHAR以便最终抛售。下面是这四个交易所到14个地址的资金流向图。
10月23日UTC下午2点,在SHAR上线后的两分钟内,这14个地址将其持有的所有SOL兑换成SHAR,向流动性池注入了大量资金,并迅速推高了SHAR的价格。以下是一些购买SHAR的兑换交易示例(交易哈希):Q81H,4Jxa,5q5n,3xvB。在获得SHAR后的半小时内,肇事者将这14个地址持有的所有SHAR转移到其控制下的另外104个地址,进一步分散了代币。下图显示了14个地址中4个地址的SHAR资产流向图。
这种分散策略使得链上似乎没有单一地址持有大量SHAR,这有助于减少外界对SHAR资产安全性的担忧。然而,通过对资金流向的分析,可以清楚地看出,尽管大量SHAR被分散到众多地址,但它们最终都由同一实体(肇事者)控制。肇事者保留了随时出售所有这些SHAR代币并耗尽池子潜在价值的能力,表明SHAR存在重大的安全风险。
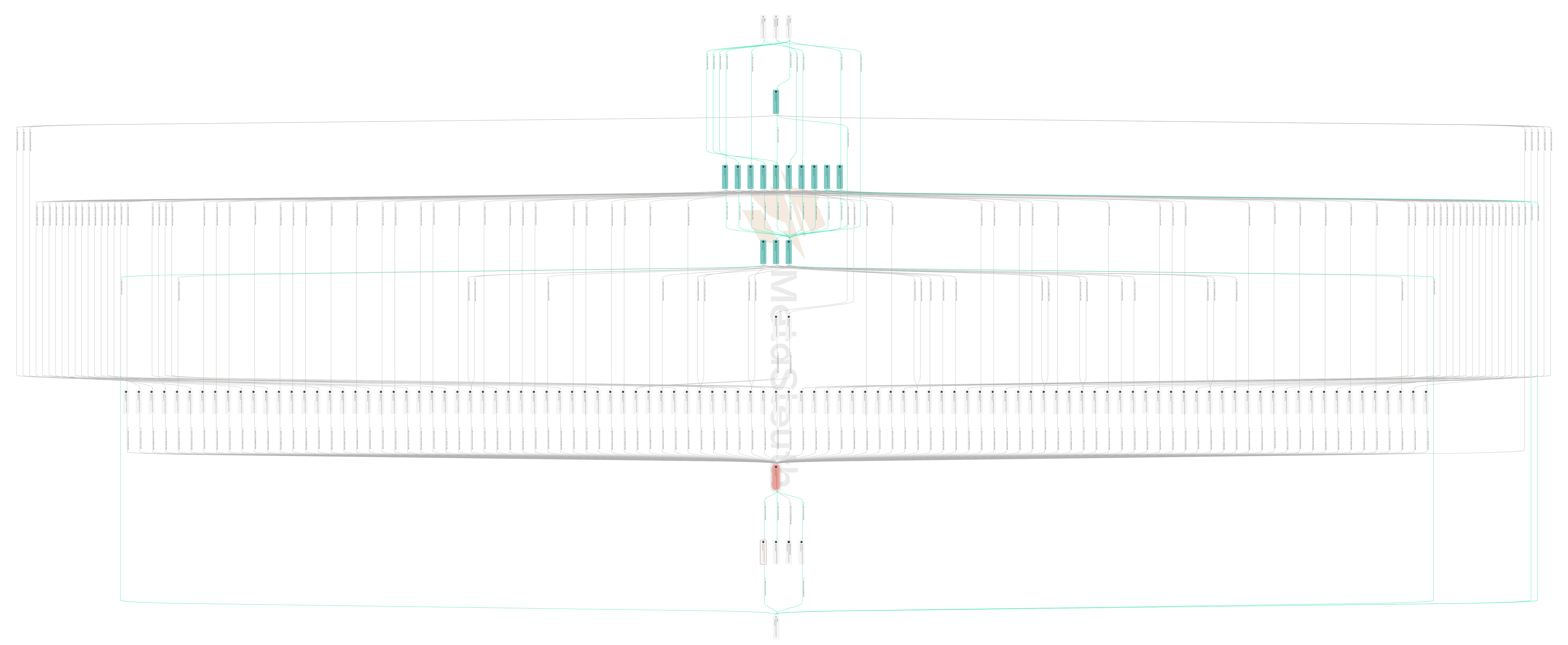
最后,随着SHAR价格的上涨,肇事者抓住了其认为的合适时机。10月23日晚上9点25分,肇事者同时将所有受其控制的104个地址中的SHAR代币转移并整合到地址CHj3。一分钟后,CHj3地址发起了一笔交易,一次性抛售了累积的500,000,000 SHAR代币。流动性池几乎被完全掏空SOL,肇事者获得了19,619 SOL代币,价值约420万美元。10月23日晚上9点26分,所有仍持有SHAR的用户都成为了这次抛售的受害者,他们持有的SHAR价值在一分钟内跌至原值的十分之一。下图显示了SHAR代币从104个地址中的52个地址整合到CHj3地址,然后被抛售到池子的过程。
为了追踪肇事者如何将非法所得变现,我们继续追踪这19,619 SOL的去向。这19,619 SOL在CHj3地址停留了近一周,直到10月29日UTC下午4点21分,肇事者发起了两笔交易ajqYwt和3uD6Ys,将其中的6,000 SOL转移到其控制的另一个地址J7aV。在接下来的20分钟内,肇事者通过另外两笔交易5STJND和3z6C72将这6,000 SOL存入OKX交易所。随后,在晚上7点52分,另外5,000 SOL被转出到地址J1wF,并且这些SOL也在晚上7点53分被发送到OKX交易所。然后在11月4日至11月10日之间,肇事者逐步将CHj3地址中剩余的8,600 SOL兑换成USDC和USDT。我们在此列出所有兑换交易:2rGGMf,5cWJte,4AE6z7,5HovYa,4Da6zR,5P9rmx,5AAHn1,5nm1Xy,Mn3Rxa。截至撰稿时(11月14日UTC上午8:30),通过兑换获得的141万USDC和16.8万USDT仍保留在CHj3地址。CHj3地址仍持有约19 SOL代币,尚未兑换。这是这19,619 SOL非法所得的当前处置情况。下图展示了左侧的兑换交易和右侧的OKX存款。
相关地址和交易
负责抛售的地址:CHj3vHyMhF6DF3VkwhzgK833o7uvsN7CrPVyUdmbFo5E。
早期积累500,000,000 SHAR的14个地址:
- E78TudQEcPwqiwnJ5HYEjJzogKPVAHGcLx7YRonxMuU3
- 5Cyg8Y4jEKKgna8Pf4xVXWLtNRZmJQksU23p1GyKnToU
- EzHJnPZ83RKvXzGDZLtfgoEBWoVjLEetMHFos2XcES6g
- 5rXZD1pZjJqSLCNRSxhn3MQLvRQUQB5nDD1Gf8nNXjT3
- 5MMdwsfXXcZNpK95mHFTtYz8K7JQ3JcboRNAimH61suC
- DZnhX2VG7LKLvfB747DgAmahGBdARevBfeTM4K1p1Rz7
- BnCFNcGHh6pMZXgHUHJi4a82Vfo2Xtcw818b9FNMU49P
- 75fXUzEqjNeBtqhXzjAbVKa84AcfnvG59nMUnvb3SXUx
- DEGdacTknp6BSYQc6fhJdfq9dZNZM3T4NBTSt8jnkygA
- H6x6k37wSe7ZBUct4eHyHn6W1o2TTXfAy2z9WyvUNLpZ
- Bhx3ZqViaRA4ZbXapro4VakYuS5bwhu2rc4cS8Dog1cy
- RSaAciLFtxDVtBH3awdnrjrDmcGUQBjYTon2FPRpCJG
- 3UtiQzi1HGH7sEg28T1sZpeQPLAb4m6Hive2cW6CV9XR
- 86DrFintdQt5w7jyJjobFQ5hVU63rbneYnDfkqC9xAbL
将非法所得存入OKX1 (5VCwKtCXgCJ6kit5FybXjvriW3xELsFDhYrPSqtJNmcD) 的交易:
- 5STJNDbQBMbigzHf6mzCrtiM6s8QJjpQazzu5j7zC61uBB46V9NkumCw8UwWHXg7YxpomAFN664PnxHYMAU353q2
- 3z6C72fm6VVGdkFW3VcpjTccq725ZuVWpcZJv3GM3DBp3D3oLVjq2nyaRDhNZbmG95fi9cTTZfZ8bT22rdXjdEfR
- 64wMUp3VFz7pxZEpZak9uXAPfbEMBDiTWUGZLgECLn8fSMPexuR5ifRqJTSTpe98ELzRG676Pfe9xoXmG9DreiG1
资金流向概览
由肇事者控制的104个分散SHAR的地址、他们为抛售从四个交易所收集SOL的交易以及其他详细的资金流向,都可以在MetaSleuth中进行探索。立即探索更多细节,发现有价值的线索: https://metasleuth.io/result/solana/CHj3vHyMhF6DF3VkwhzgK833o7uvsN7CrPVyUdmbFo5E?source=5e4fca36-208b-4714-afb3-0800d5355323




