我们内部分析工具于 4 月 5 日在 Tether Gold 合约 中发现了一个漏洞,该漏洞允许攻击者将任何人的 XAUt(Tether Gold)代币转移到预定义地址。该团队收到了我们的报告,并表示他们已在内部定位到此问题。今天我们发现该问题已被修复,并想在此分享详细信息。此外,我们将说明如何使用 Phalcon Fork 开发和调试此漏洞的 PoC。
0x0. 漏洞
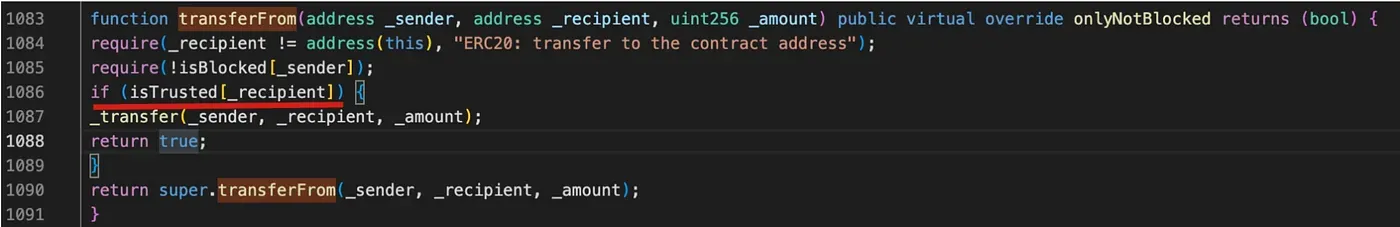
在 合约 的 transferFrom 函数中,任何人都可以调用此函数将其他用户的代币转移到由代币所有者定义的受信任的接收地址。虽然此漏洞不能直接用于将代币转移到攻击者账户,但攻击者仍然可以将池中的代币转移,以操纵池(例如 WETH-XAUt 池)中的代币价格来获利。
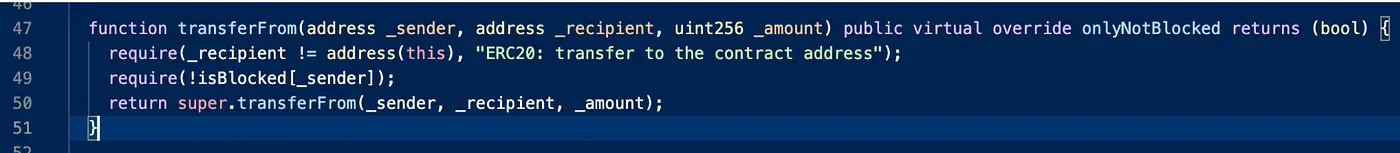
此漏洞的修复非常简单,如下所示。
0x1. 如何利用漏洞
要编写和调试 PoC,我们可以为此目的使用 Phalcon Fork。首先,我们可以在漏洞修补之前创建一个 Fork。我在通过 Fork API 创建 Fork 时使用了块高 17038763。
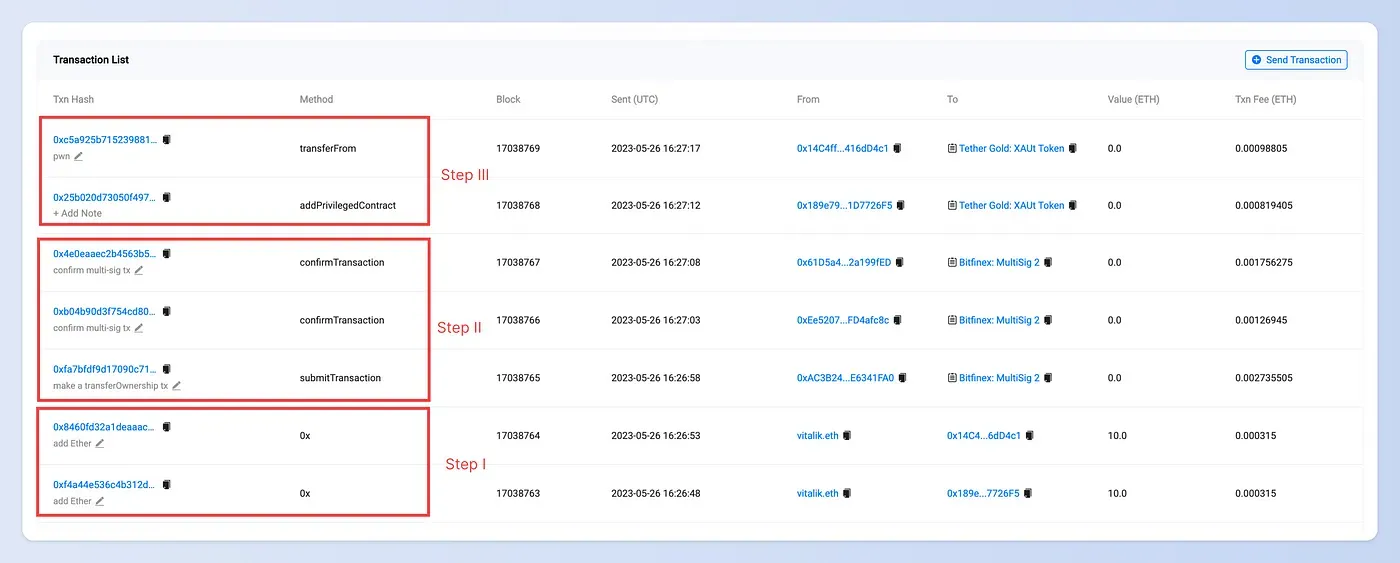
步骤 I:准备足够的 Ether
第一步是为攻击者准备足够的 Ether 用于支付 gas 费。如果账户中没有 Ether,将发出从 vitalik.eth 发送 Ether 的交易。
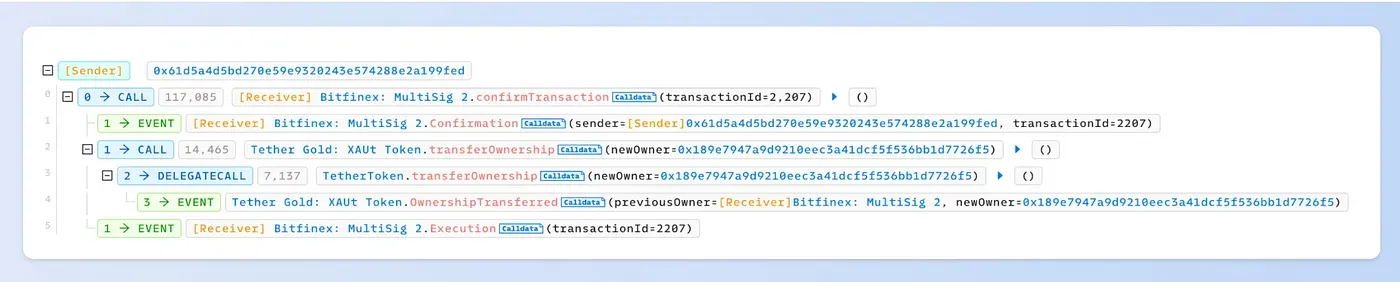
步骤 II:转移 Tether Gold 合约的所有权
Tether Gold 合约的所有者是一个多签钱包(0xC6CDE7C39eB2f0F0095F41570af89eFC2C1Ea828)。要将所有权转移给攻击者,我们需要提交一个多签交易,然后确认该交易。
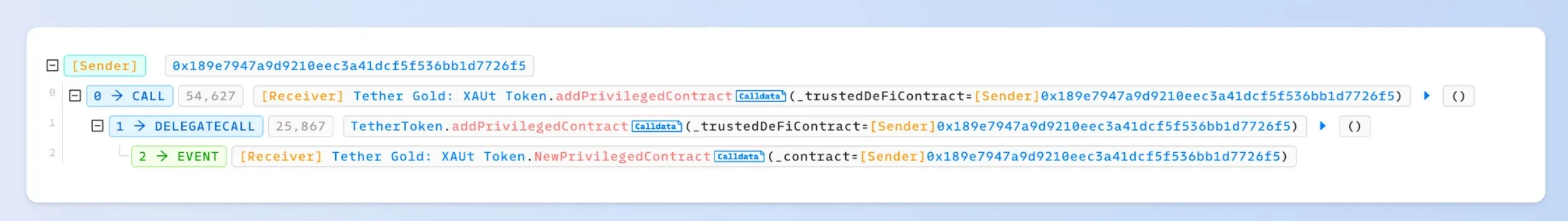
步骤 III:向 Tether Gold 合约添加一个特权账户
我们添加了一个新账户 0x189e7947a9d9210eec3a41dcf5f536bb1d7726f5 作为特权账户。然后,我们调用 transferFrom 函数,将 XAUt 代币从受害者转移到特权账户。
0x2. PoC
请在此 GitHub 上找到 PoC:




