5月8日,Peckshield 报告了 RariCapital 的一起安全事件。经过仔细调查,我们发现这是一种价格操纵攻击(间接操纵),在我们发表的论文中已有描述:DeFiRanger: Detecting Price Manipulation Attacks on DeFi Applications。在论文中,我们重点关注检测 DeFi 应用上的两种新型攻击,包括直接和间接价格操纵攻击。前者是指攻击者通过攻击易受攻击的 DeFi 应用,在同一个 DEX 中执行非预期的交易来直接操纵 DEX 中的代币价格。后者是指攻击者间接操纵易受攻击的 DeFi 应用的代币价格。此次安全事件就是一次间接价格操纵攻击的例子。
根本原因
我们分析了攻击的根本原因,发现不安全的价差依赖是导致问题的原因。具体来说,Rari 的 LP 代币价格依赖于 Rari 持有的 ibEth(以太币)LP 代币的价值。不幸的是,ibEth LP 代币的价格可以通过攻击者调用 ibEth 的 work 函数来操纵。
攻击者持有的 Rari 代币价值 = Rari 中的以太币储备 * Rari 代币数量/Rari 代币总供应量
Rari 持有的 ibEth 代币价值 = ibEth 中的以太币储备 * ibEth 代币数量/ibEth 代币总供应量
Rari 中的以太币储备受到 Rari 持有的 ibEth 代币价值的影响,而 ibEth 代币的价值可以通过攻击者(通过调用 work 函数)增加 ibEth 中的以太币储备来操纵。
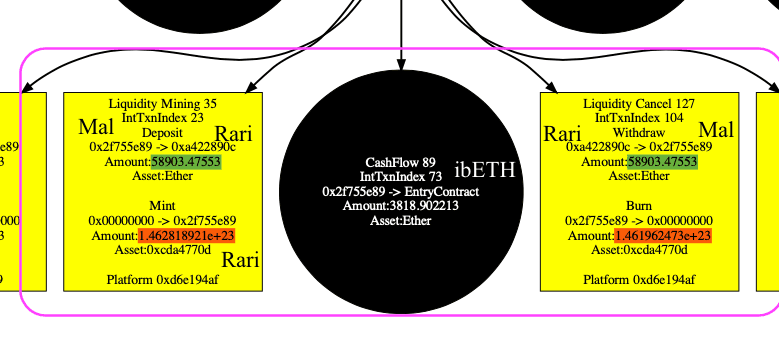
使用我们的系统 DefiRanger,我们轻松地恢复了图中所示的 DeFi 语义。在流动性挖矿(存入以太币获取 LP 代币)和流动性取消(取出 LP 代币获取以太币)中,LP 代币的数量(用红色圆圈表示)与相同的以太币数量(用绿色背景表示)是不同的。
攻击过程
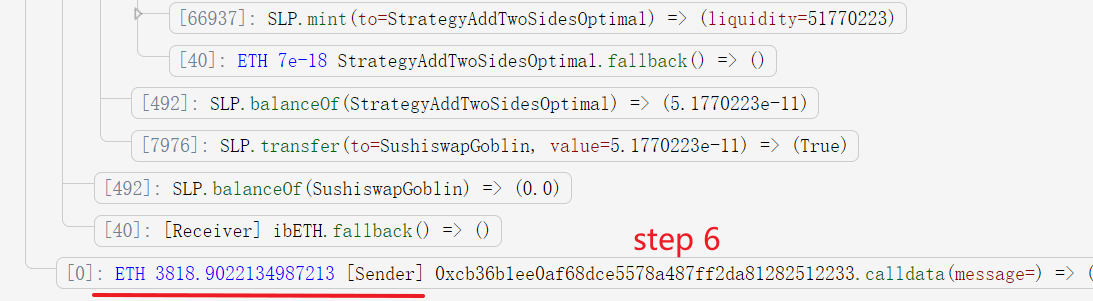
攻击过程如下所示。
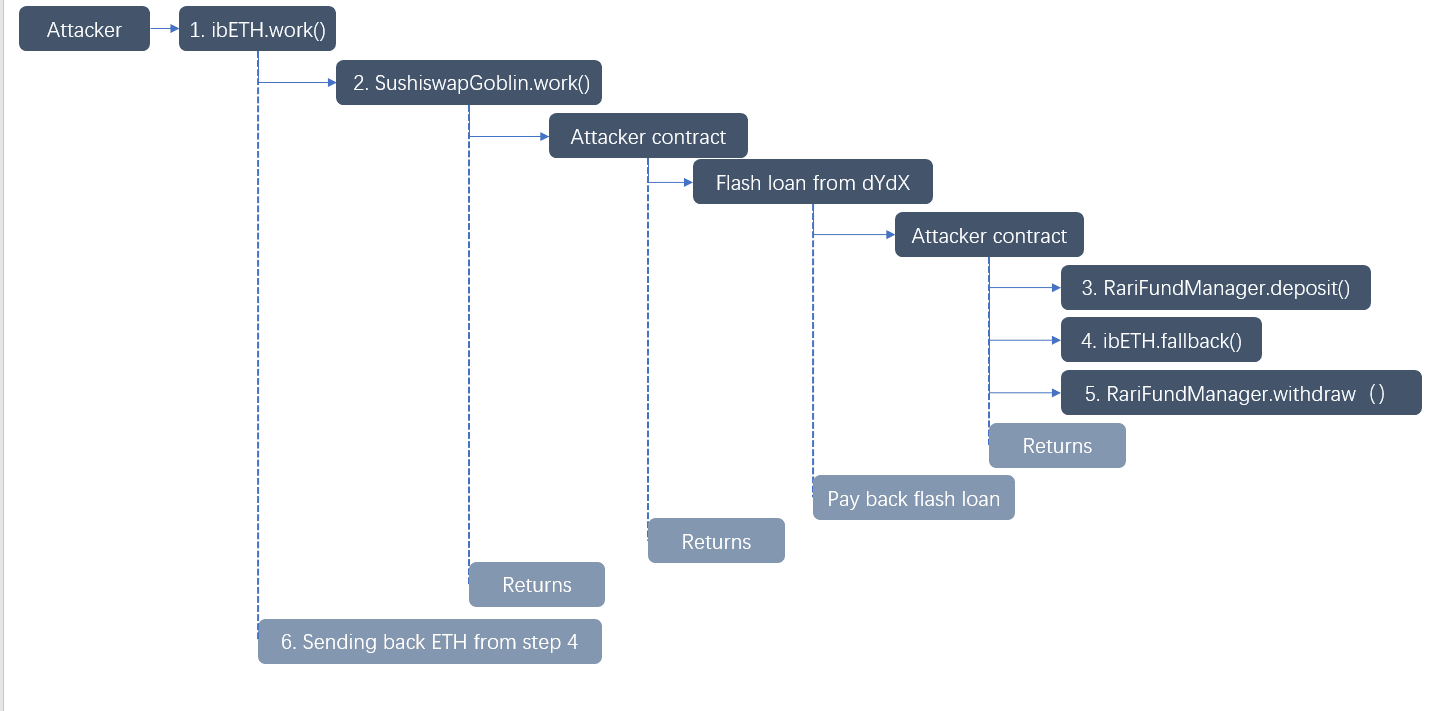
- 攻击者调用 ibEth 的
work函数。 - 该函数调用
SushiswapGoblin.work函数,后者进一步调用攻击者控制的合约(0x2f755e8980f0c2e81681d82cccd1a4bd5b4d5d46)。
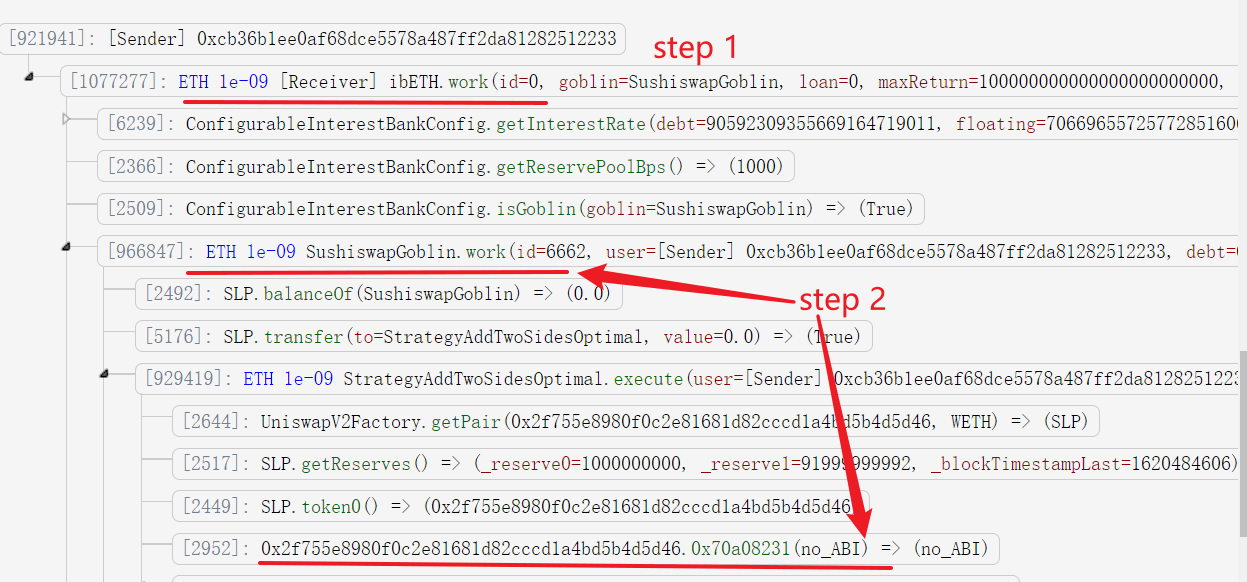
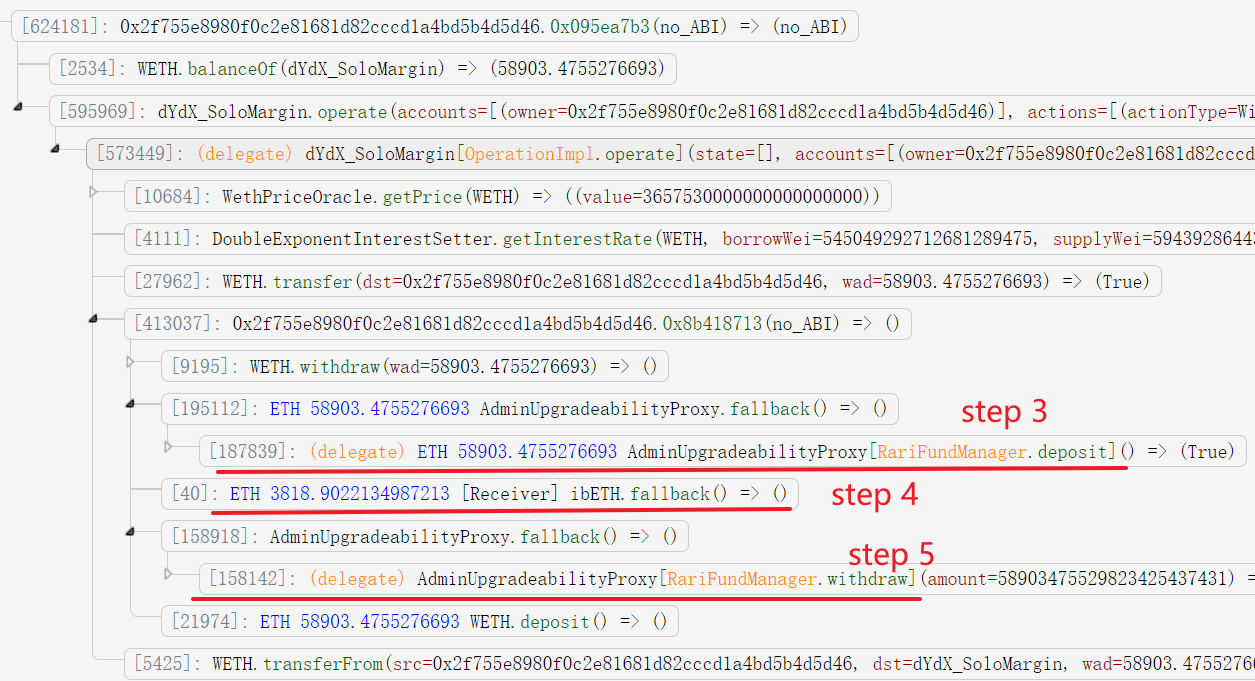
- 该合约首先将 58903.4755276693 以太币(从闪电贷借入)存入 Rari,并获得 Rari 的 LP 代币(146281892117489076580650)。
- 攻击者向 ibEth 存入 3818.9022134987213 以太币。这是关键一步,它将提高 ibEth LP 代币的价格(而不影响其总供应量)。这进一步影响了 Rari LP 代币的价格。这是因为 Rari 池中总的以太币储备因其持有的 ibEth LP 代币价格的上涨而增加。请注意,攻击者无法通过增加流动性来操纵 Rari 或 ibEth 的代币价格,因为这样做也会增加代币的总供应量。
- 攻击者提取以太币。由于 Rari 代币的价格更高,攻击者可以使用更少的 Rari LP 代币(146196247321127203315331 而不是 146281892117489076580650)来获得相同数量的以太币以偿还闪电贷。
- 攻击者在
work函数结束时获得归还的以太币。
总结
总而言之,RariCapital 面临的安全漏洞 starkly 提醒我们,DeFi 应用面临着复杂的威胁。通过巧妙的利用策略,攻击者实施了间接价格操纵攻击。此次事件揭示了智能合约中使用不安全价格依赖的关键漏洞。此次攻击凸显了 DeFi 项目迫切需要采用像 DeFiRanger 这样强大的检测系统,以防范威胁日益壮大的 DeFi 生态系统的完整性和安全性的直接和间接操纵策略。
关于 BlockSec
BlockSec 是一家开创性的区块链安全公司,由一群全球杰出的安全专家于 2021 年创立。公司致力于提升新兴 Web3 世界的安全性和可用性,以促进其大规模采用。为此,BlockSec 提供智能合约和 EVM 链安全审计服务,用于安全开发和主动阻止威胁的 Phalcon 平台,用于资金追踪和调查的 MetaSleuth 平台,以及供 Web3 构建者在加密世界高效冲浪的 MetaDock 扩展。
迄今为止,该公司已为 MetaMask、Uniswap Foundation、Compound、Forta 和 PancakeSwap 等 300 多家知名客户提供服务,并在两轮融资中从 Matrix Partners、Vitalbridge Capital 和 Fenbushi Capital 等卓越的投资者那里获得了数千万美元的投资。
官方 Twitter 账号:https://twitter.com/BlockSecTeam




