2023年:
Web3领域发生了一起重大的黑客攻击事件,Euler Finance遭到了入侵,导致近2亿美元的资产损失,这是当年经济影响最严重的事件。
最常见的攻击向量源于业务逻辑漏洞,共有15起此类事件,每起事件都造成了超过8万美元的损失,其中包括对Euler Finance和Platypus的著名黑客攻击。
精度损失(Precision loss)成为一种新型的被利用漏洞,KyberSwap事件由于在tick计算过程中出现精度损失,导致约4600万美元的损失。
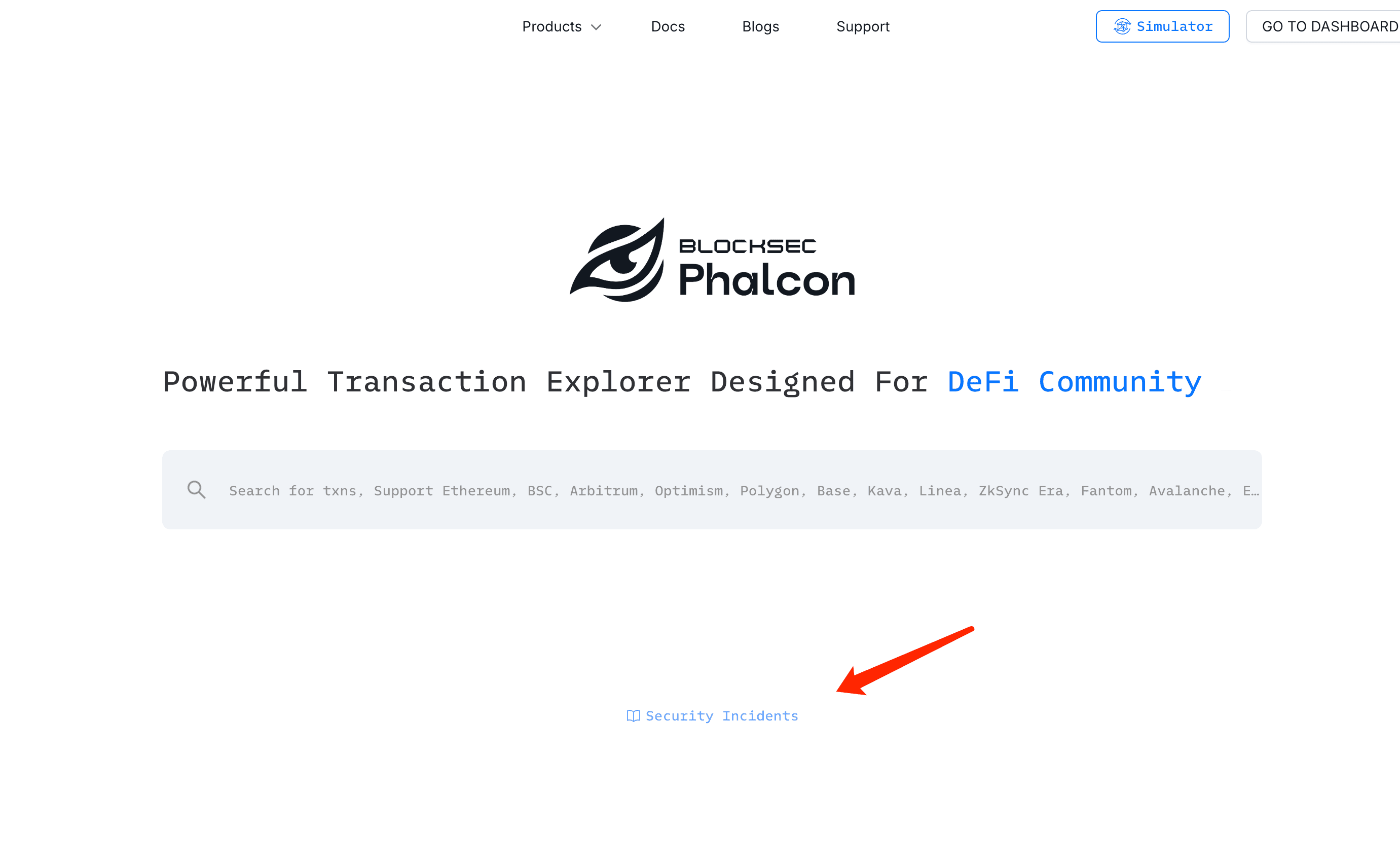
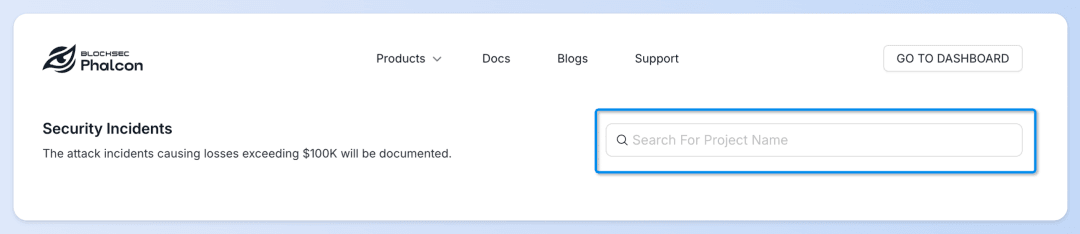
随着Web3生态系统的持续快速扩张,巨额利润的诱惑导致黑客攻击事件增加。为了应对这种情况,Phalcon推出了一个“安全事件”仪表板,允许用户系统地跟踪最新的安全事件。
您可以点击此处访问该仪表板,或访问我们网站的首页,然后选择“探索交易”来找到此仪表板。
深入了解2023年的黑客攻击及其利用方式
您可能会问:Mixin Network事件不是2023年最大的黑客攻击吗?
确实,那次事件非常严重,但我们的列表侧重于由漏洞利用导致的黑客攻击。由于Rug Pull、私钥管理不善和其他因素造成的损失未包含在我们的统计数据中。
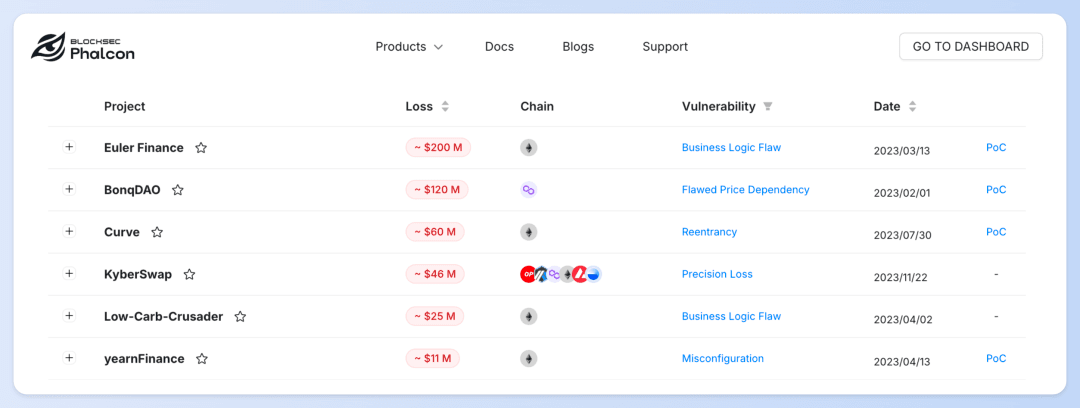
在Phalcon的“安全事件”仪表板中,我们汇总了2023年近70起由漏洞利用导致的黑客攻击事件,每起事件的损失均超过10万美元。
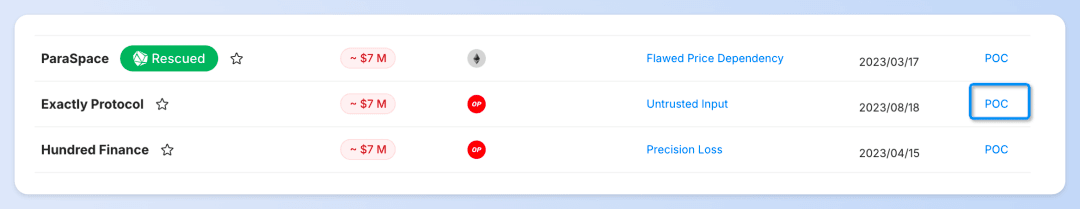
以Exactly Protocol事件为例:
您可以了解资产损失、攻击发生的区块链以及攻击时间等基本信息。
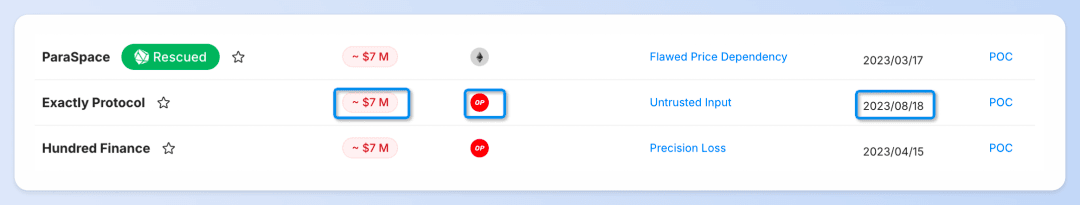
我们还展示了每起事件被利用的漏洞类型,并提供一个点击链接以进行深入的根本原因分析。这些分析由我们专业的安全专家提供,他们始终致力于在安全事件发生后,及时为社区提供关键见解。
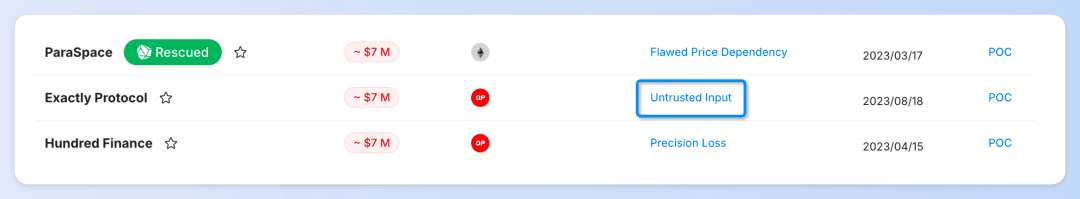
此外,本部分还包括由我们的合作伙伴DeFiHackLabs编译的PoC(概念证明)代码。
您可以使用Phalcon Fork来调试安全事件的PoC(概念证明)代码,并与社区共享PoC代码和交易。
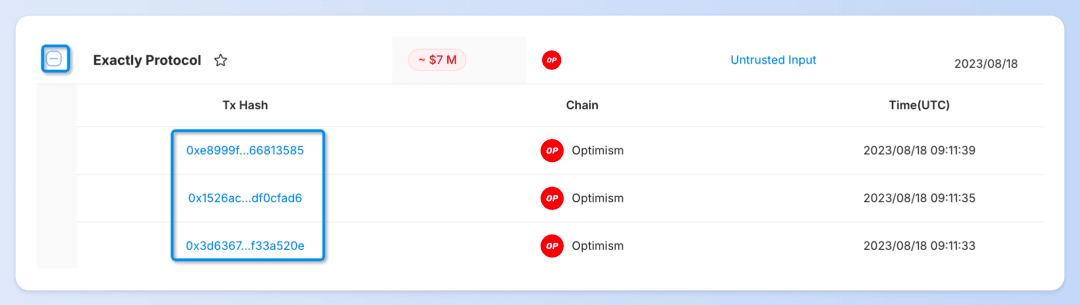
点击协议名称旁边的➕即可展开并查看每笔具体的攻击交易。 只需点击交易哈希,您就可以通过Phalcon Explorer查看交易的资金流、余额变化和调用流程。
信息 ➔ 洞察
📌 想了解与特定协议相关的攻击事件?
👉 在搜索框中输入**[协议名称]**即可立即获得结果。
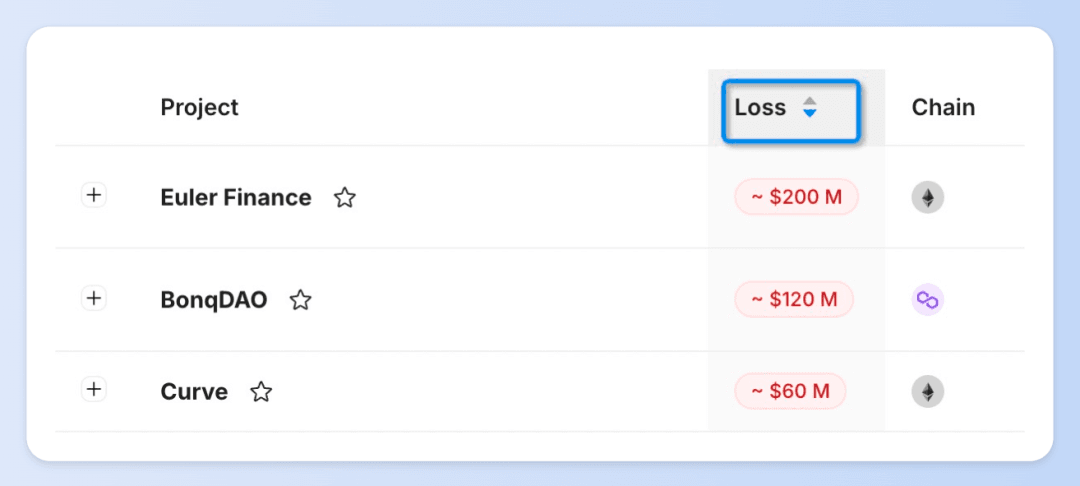
📌 对2023年最严重的攻击事件感到好奇?
👉 选择**[损失 - 降序]**可以快速识别损失最重大的安全事件。
📌 对2023年攻击事件的趋势感兴趣?
👉 选择**[日期 - 升序]**可以跟踪攻击频率和方法在全年是如何演变的。

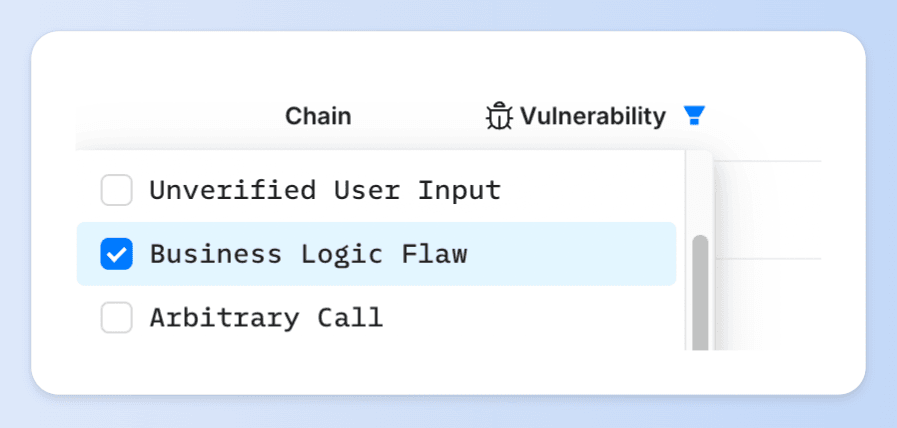
📌 正在寻找由特定类型漏洞引起的攻击事件?
👉 使用过滤器选择**[漏洞类型]**即可快速定位相关事件。
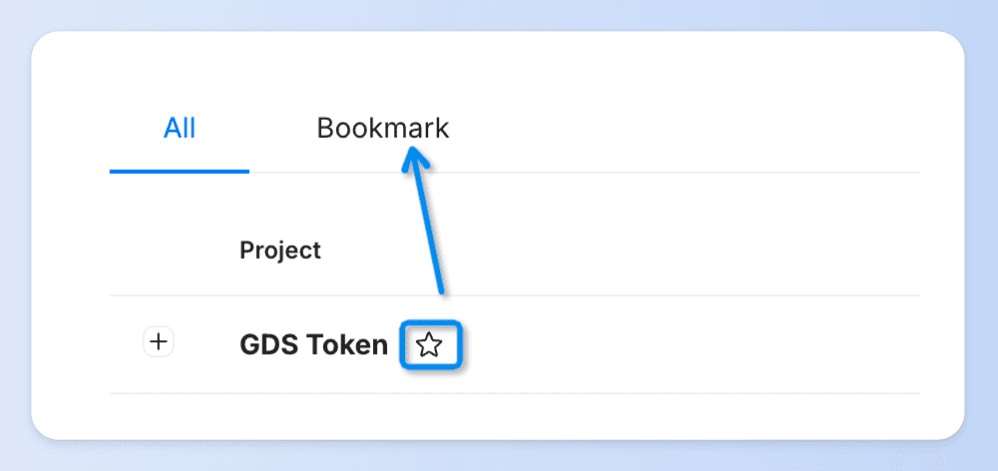
📌 如果您想比较和分析多起攻击事件
👉 点击⭐️即可收藏该事件,方便日后参考。
立即开始探索
Phalcon的“安全事件”仪表板不仅为普通用户提供Web3安全信息,还为安全研究人员和开发人员提供了一个学习和回顾的平台。通过分析实际的攻击技术并了解黑客如何利用漏洞,他们可以更好地识别和加固其系统中的潜在薄弱环节。
我们将持续更新数据,确保您能够获取最新的黑客攻击事件信息和见解。
立即探索Phalcon的“安全事件”仪表板,加入我们,共同构建一个更安全的Web3世界。



